From SEH Overwrite with Egg Hunter to Get a Shell - Rodolpho Concurde
Show transcript [en]
welcome aboard at my talking i'm glad for this view for all my talk is called the throne i see the variety with iggy hunter to get a show my name is concordia but you can call me by my nicky name hodox i read about me i'm penetration tester instructor id consultant information security throughout 30 years certified ethical hacker basic council already gave it taxes to hack in the box psychopath security conference murderer lucas that confronted him village inside skull guys besides attendance etc about 129 magazine about stackable flowing painters magazine about to cover you from frozen to get a shower pronunciation right at the shell here i leave here my liquid in profile by my name my email for who wants to
take out some doubts after this presentation you can write to me on my editing profile my or my email our agenda we are learning about sc8 instructed exception handler buffer flow we have a park impossible learning see the variety charting jump aggie hunter medic characters reverse shell and you have a questions
exceptional hunter reception 100 is a chunk of the code from inside of an application which have the objective to handle any exceptions that can occur during exception of a software receptor look like with here we have tried to catch when the flow of execution passing dry execute some code this of course some exception should jump to catch and catch execute some specific code where exceptional code conception is an expected event an error that occurs in a running system or program where exception occurs the program's normal flow of execution is interactive it is important that the application can handle the exception or error to continue running normally the address of the exception holder are stored on the stack
the windows operation system has a forehander that gets any exception that is not handled by the program so so the window sensor has your own accepts handler when windows handles reception in a application you usually see message program has encountered a problem it needs to close
the sc8 works in a chain and they are localized in the end of a stack in the classic birth overflow vanilla the exploit of writes the return address without worrying about the world writing more in stack but with the se8 of rights technique it's possible to be taken more space for the shell code in order to have exploit more stable so here we can see that the sc80 works in a chain we have here next s8 recording passing to next state recording passing to nexus 380 recording in the office chain buffer flow buffer flow is a normally where a program while writing data to a buffer overall the buffers boundaries and the variety to set the memory location
mighty beam will be based placing the memory which locates a large amount of the data and dynamic a stacking based allocated unlimited or fixed size of the data such as data from account variables or functions here we have a left major in the right images inactivates we have a label 4 with 11 a's right imagine have variable 4 is 150 eighths as we can see when we in like in writing menu we have overwrite the resistability character a in the variety in end of stack because sc8 is localized in end of stacking we override the c82 now we have a park the attacking machine will use the kylian 3200 20.3 and the level sources that review usd
file sharing web 7.2 running on windows xp service packet 3 here we have him i like to find a load of enable software i'll make it available on my linkedin profile the link for this slide for who want to download the enable software you can find the available software linking on this lines that will became available money including profile
okay
now we have this we have received a park
let's see the video park
let's open the vulnerable software easy file sharing web server is running on part 80 open the moodle debugger click menu file attached
choose the vulnerable software by clicking attach
the softest parts clicking button run for running the vulnerable software
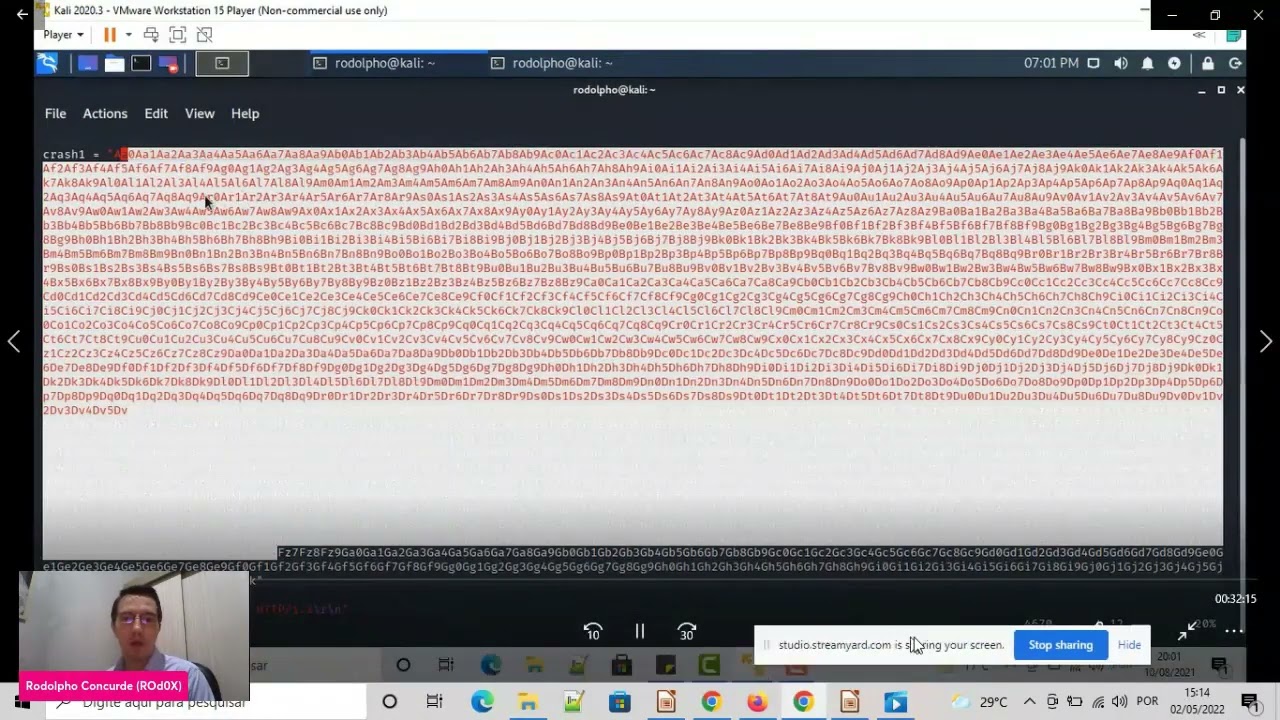
now let's open the exploit code in kali linux vi is collector the exploited code this is the exploit code is writing in python we have very procrastinate with a lot amount of characters we will save the select amount of characters against the target software
the target we have a payload equals method getting plus question for labor class world will send them within the right amount of characters local writing valuable questions against the tag type party 80. this roth amount of characters was generated by 2.8 uh again separate amount of characters was in eighty by two pancreatic is localized before the metasploit framework it tools exploited you should type panel create dash ld link 5000 5000 and we have here out amount of characters you must copy sort the amount of characters and paste in your variable question exploit the code
to the paste in variable questions in exploit code
so we will send a lot amount of characters against the tag team at the getty in party eight let's save the exploited code in the same title name of exploit the code is correct on two prime pi saying that x center guess the vulnerable software the flow of execution is top tier acceleration we have it click menu view sc8 chain and we have here a value of the sc 100 this value we have do a lot amount of characters with this value we need to find the office 30 of the se hundred we need to find our office set of 300. find office set we use a two parent of a set part of set
space dash l link 5000 dash q dash q and the value of a c hundred 46 35
46 35 66 46
6 66 46 when we found off 35 out 65 offset 5.65 is of 75 300 we need to ah entity of the office 30 in exploit code so now we have it we have variable crash world character a multiplied by office 34.61 plus b multiplied by 4 plus c multiplied by 4 plus 90. 90 means noop is no prison do nothing no means no patience because do nothing so we will feel will say against the target we're saying against the target 5 5.61 character a and there's real variety after we will variety the sc 100 with character b character c again we'll write sc 100 with character b character see
let's restart the movie debugger clicking button run resize the mood of the burger running the money the burger run the vanilla softimage
sandy executes the exploited code the pythonxconnect tree executes the exploit code sending the payload we have a flow flow of execution stock t acceleration minute view sc8 chain and now we have in c hundred forty two forty two forty two forty three forty three forty right button follow address in stack and we have pointer to nexus 300 bpb ac 100 cc ccc we as we can see we get a contour of a 600 so we get a contour of a c hundred we have b b b b in pointer to next is recorded
you get a controversy hundred let's open the exploit code now we need to find the ax instruction an instruction pop-up return for this we need to type in command bar exclamation mark sc 100 sch8 exclamation mona sch click menu view log and we have here all the first 20 points i show here for my point is open sc 80 dash detect let's learn more about it let's learn more about sc pop-up return
now we need to find immunity or instruction pop-up return this instruction will actually image below make a return to the pointer to next we activate the recording the pointer to next create recorded variety with a jump to our show called to get a versus shell so let's understand this imagine when expressing flow of execution is stop in acts violation flow of execution stopped in explanation after it's handled by c80 because associated this is the exception hundred of the windows in korean sc 800 we are variety with pop-up return so from of execution is passing coin ts800 and will execute the box box and return it in eternity we will return the pointer to nexus c80 recording that he
pointed to nexus 380 was override with he jumped to show called it's a short jump so flow of execution is a core explanation so your variety created your variety greatest 300 pop-up return so we'll execute box pop and return it here return it will follow out in point to the next s8 recording pointer to necessary to record will execute one short jumping and we will jump for our show code to get a mercy show for this now we need to we need to find it i sushi pop-pop return
open the local c programs file immunity emulator debugger and then we have a log of the c80 point text a c8 point text we need to find the instruction pop-up return without secure mechanisms without we need to find it a pop-up return without security mechanisms we use it either stem 0103 fe 1003 fc and we have here pci popping the i return as we can see we you we will use to hear about pci pdi return with secure mechanisms asadi asdis files repair files save se8 as files as files we use this address 1003 pci for pdi return without security mechanisms
so we need to create the inaugural code available sc80 with address fe-03010 is our address for pop-up return 1003 fe we need to type and like view architecture 86 you should you should we must type in like fv03010 and now we need to find the x instruction jump shot i should instruction jump chart because we will make pop-up return and you use the return file jump shot in short jump you make a charge jump to our show code for before finding i'll be called to find short example users we need to create it we need to create available any se8 with 1999 6 and b06 is up code for short jump as we can see in as michelle
you should type you must type jump short 8 and we have code in b06 if b06 is our code if i jump short need to add the eb06 in our exploit code we have labeled nsc8 1990 xeb x06 variable sc8 fe 03010 pop up return and then now we have available crash one character aimed private by officiate plus nsc80 plus s8 plus 90. that's our noobs
save the exploit code
the restart the model debugger restart the moodle debugger click button run to start to run the vulnerable shaft immunity debugger again
execute that sprite code
we have act violation click menu view sc8 chain and then now we have the ic hundred the edits for pop-up returning shorty jump click button right bottom phone and using stacking and then we have here in s300 i i ended for a pop-up return he pointed to next i see he recorded ash 1990 looping eb 060 be our shortage jump we have here get the control of the c hundred and the variety of c hundreds pop-pop attorney the variety i see hundreds with you try to jump
click if you write a button go to expression and type identify pop-up return 100 and do we have a key 10-0 i just have pop-pop return puppy see eye-popping the eye return pick your right bottom puppy ci bracket punch toggle to put the bracket pointed puppy breaking point is to stop the flow of execution this means that the flow of execution is stopping pci press 50 f7 to pass flop execution and the clicking button run and the flow of execution is stopped by pci pass the flow of execution f7 f7 f7 and do we turn it through our loops we'll return so an open loop is any jump shot we have here a b06 the visual six hour
jump shot pass nope nope f7 f7 pass jump short for f7 and the follow out in loops we have here our loops in this place of these loops we will put our shell called together shell but i know that this is isn't enough space we don't have enough space to put our shell code here so again in this place of these loops we should put our shell code together shell but i know that is we don't have enough space to put our code here for this we use a technique called aggie hunter we use a technique called the egg hunter as we can see we have here our loops but even being a lot amount of space this isn't
enough space for our show code we don't have enough space for our show code we need to use a technique called aggie hunter let's learn more about technique called ali hunter
we know that we have a little space threshold code for this we will use a technique called any hunter aggie hunter is a small piece of scale code which search for a 12-bit space which the attacker was not able to feeding the available buffer space for this make use of this little space official called the aggie hunter to have direct execution of the flow to shall call the bigger so as we can understand here the ali hunter is a small piece of shell code as we can see image below small piece official code that will have directors for a bigger space where in this bigger space we can put our shell code into the diversity shell
so we must type in command by exclamation mark help egg and here we can see this comedy very common the egg these options for the comedy egg we have the four value is root wood is a default label that will you use it after we use it later default label would and you should type extra mesh extra mesh to find the eddie hunter eddie hunter again a small piece of shell code as we can see here we must copy we write the bottom copy clippy board the whole i copied the small piece of the shell called the pcrx price code the small piece of the shell called called the incentive will hit the reactors for a
bigger space where in this bigger space we can put our shell code together versus shell
let's open our exploit code edit paste in our sprite code our id hunter write the bottom and paste selection now we have here our little piece of shell code called aggie hunter and we have variable crash world character aim to play the ball for searching
character aimed about facility plus any sc 80 i tried to jump in plus sc8 i pop up with 30 plus 90 plus eggy hunter plus 90 that is our noobs
and we have here payload 2 equals bad shines
we have a character in question character aimed by facility or variety se8 if you pop up return override nsca to visuality jumping plus 90 loops plus 800 plus 90 or loops and the payload true equals medical spanish highs we will send these characters since zero one zero two zero three and etcetera up f against the target for fine belly shy let's learn more about what is betty shares
now we need to search for betty characters depending on the application type of vulnerability and the protocols use it may be certain characters which are considered bad and did not and should not be used in your buffer or shell code one example of many characters is a zero zero this character is considered badly because a new byte is also used to terminate the three cooperation it's used to get our buffer whenever which did no byte appeals so we'll send it you said against the type this all these characters since they know of fff with objective if it caused some you call some error in this software we want to change the zero zero because we
already know that zero zero is so many characters again zero zeros are many characters but we need to know if there is always many characters for this we will say the player will say the audacity targeting this character 010203 etc up f3 first if question errors
try this put here payout 2 equals better shines you send this bad shots against the tag and we have here payload user agent
[Music] but after we put in parallel to our shell code to get the mercy shell save the exploit code
restart the debugger
click the button run run the vulnerable software debugger again find the pop-up return address if you write a button go to expression find it pop ci put a bracket quality puppy psi right a button break punch toggle to stop flow of execution copy ci
execute our trade code python exchange [Music] five send the payload
pause the vlog of the question we have here actual violation press shift f7 to pass the acceleration pass f7 to pass accumulation after clicking press f9 or click button run
four of the execution stops import pci best proposition f7 f7 f7 returning fellow auction loops f7 jump charge f7 loops f7 and here we have our aggie hunter these this instructions is our aggie hunter it's our audi hunter let's put a breakpoint in scans right button scans breakpoints toggle to stop the flow of the execution is scanned
clicking button
whatever [Music] flow of execution stopped in scans let's see the value in scans right button in the x right button is history dx following dunk we have here who choose this the full labor of the country indicates after the solution will come in our shell code in this case our bench shines but it has to put our shell code together with shell pacific 7 jump to the ipf7 and here we have our bench side z10203.505.60709
0 a 0 b 0c and etc up ff
we have all this bad size since 0 1 up f c 0 up ff
we have the bad size c01 up ff as we can see we don't have a more air hole we don't have more air because we have here all these values into zero l up f this indicates that just zero zero is a better characteristic for our software for our software just zero zero is a better character and we don't have my others many characters beyond zero zero so now we can we will generate our shell code together with shell to generate our shall code it without zero zero just without zero zero so we started the monarch debugger
the start of the movie
[Music] go to express to find a pop-up return put the backing point poppy ci to write the button breakpoints toggle put a back point to pci
open the exploit code and then we here we have a shell code erase this odd shell code to cope to base of neutral code first generator shall call do you use a tool called mscf we know
we use a tool called msf window for generating our shell code you should type you must type msfvino
python degenerate payload for file python and in this
in this message we know we generate a shell cody avoiding a better characters zero zero generate our shall call divided by character zero zero let's erase this old shell cody to paste our initial code
we have here we will crash one character empty plied by offsets plus nsc80 are short jump plus s8 our pop-pop return plus 90 multiplied by 5vr loops plus 800 plus 90 our noobs and below payload 2 equals birth buffy is our birth is our shell code and here we have payload equals other agency
shell
is our shell code so let's copy our shell code and paste in our exploit code
copy i shall code
edit paste in our exploit code this show code will generate biomass vino to get a reverse shell
let's save the exploit code
let's save our sprite code
and let's execute msf metasploit at the equipment sprite with msf console the messy f console to the equity automatic sprite to lision.555 to get a connected back
type use much handler search payload windows shell reverse tcp
windows shell reverse tcp search ali host
look how i be
search any part to listen on part 4 4 4 4. and then security execute meta sprite command x sprite to listen comedy sprite now let's execute our exploit code pythonxcollector6
and we have absolution bypass acceleration if shifty f7 shift f7 to pass ax violation
and after press f9 to go f9 click button run and stop the flow of execution pci passport ci puppy guy returning f777 press loops if f7 pass jumper short with f7 and then we have the our aggie hunter we have our aggie hood put the part in scans right the button in scans bracket punch toggle put back parking scans click button run flow of the execution we stopped in scans let's see the content in scans right button in registering the x right button resisting the x following them and we have here a default label root the four label root this indicates that after root will come in our shell code after root will come our shell code
write importantly the x following them and here we have here our root
pass scans which with f7
f7 f7 pass jump pdi with f7 pass the mpdi with f7 and we have here our show code the adc d974
this is a the same value of our shall cody in our exploit code we have in our expert code in our shell called dna dc d974 this is our shell code you know is executing in our vulnerable soft social code executing of enable software click button run button run to to pass the executive flow of execution button run
and we have him at the sprite we got a shell we got a shell metasploit you can type net user to cd users using hotdogs and administrator you can type it to ipconfig tv to see the ip of victim we have here ip of victim this is everyone this is a video part of how you can write on exploit code using a technique se8 variety with egg hunter in this slides we have here step by step of how you can write your express calls using a technique se8 a variety of any hunter for who want to see again i'll became available my linkedin profile the link for these slides i'll make available managers and provide
link for this inside receipt everyone now i open for the questions thank you very much
you





