Down the Rabbit Hole: A Tour into the Dark Web
Show transcript [en]
Hello everyone, hope you are all well and healthy. My name is Konstantina Koukou, I'm a lead security engineer in checkpoint software technologies and an evangelist in the company. Together now we're going to take a deep dive into the dark web, understand what is right there and hope you enjoy. Let's go. So the agenda is that we look into the architecture, how the Dark Web operates, what are the components, what is the protocol, what can we found, what can someone purchase through Dark Web. We'll explain a little more about the transaction and use the use of blockchain technology as well as the syndicates and collaborations that exist in Dark Web. There is a saying by the poet Carl Sandburg that life is like an
onion, you peel off layer by layer and sometimes you will. And we can say that this pretty much also applies to Thor and Dark Web, unfortunately. But let's take it from the beginning. I want to give you some feedback and history actually of how the Dark Web and this thing started from the beginning. Actually, TOR started to be a project in the 80s, a project of the US Navy laboratory project. The main goal was to develop an internal channel that was completely secure, confidential, and nobody could break it, no matter if he was able to monitor the traffic through the network. There were three masterminds behind this: Mike Reed, Paul Shiverson and David Golshag. The goal was, as
we said, complete anonymity and privacy for the user. The answer was to create and deploy the first prototype, the first research design of the ONION routing. And actually, the operation was, what was happening is trying to encrypt the communication in each and every hope of the path. And this is actually how pretty much the onion routing works. And until 2004, the project remained in the hands of US Navy. but it was late 2004, that became an open project. The US Navy decided to give it back to the community. First of all, because they needed also to hide their own traces in the dark web, the intelligence members action into the dark web. And this is how it is right
now. It's operated by the community. And we also find that big organizations that promote freedom of speech globally are also supporting financially the Tor project. Let's see some very basic stuff and what's the difference between working in a common browser rather than working in the Tor browser in the dark web. First of all, on the left you can see a web page result from the Google search and this is how the engine gives us the well-known websites, also called as index sites. On the regular web, most people we know that are aiming for publicity, they want people to reach their site, to get their attention and maybe monetize the visits. But on the other hand, When we are talking about dark web, probably this is
the complete contrary situation. First of all, we know that in order to register a new website in the regular internet, we need to take into a standard procedure, register domain and we go through even without noticing through some standard organizations that are monitoring the activity. While on the other side, I can open a new site on the Onion site on the dark web in a matter of seconds. No one asks for what I upload, how I upload and who am I that starts a business over there. And actually, if I don't decide to give someone the Onion site my address, nobody can reach me or it would be pretty random if it gets to my website. So, I generate it to myself and
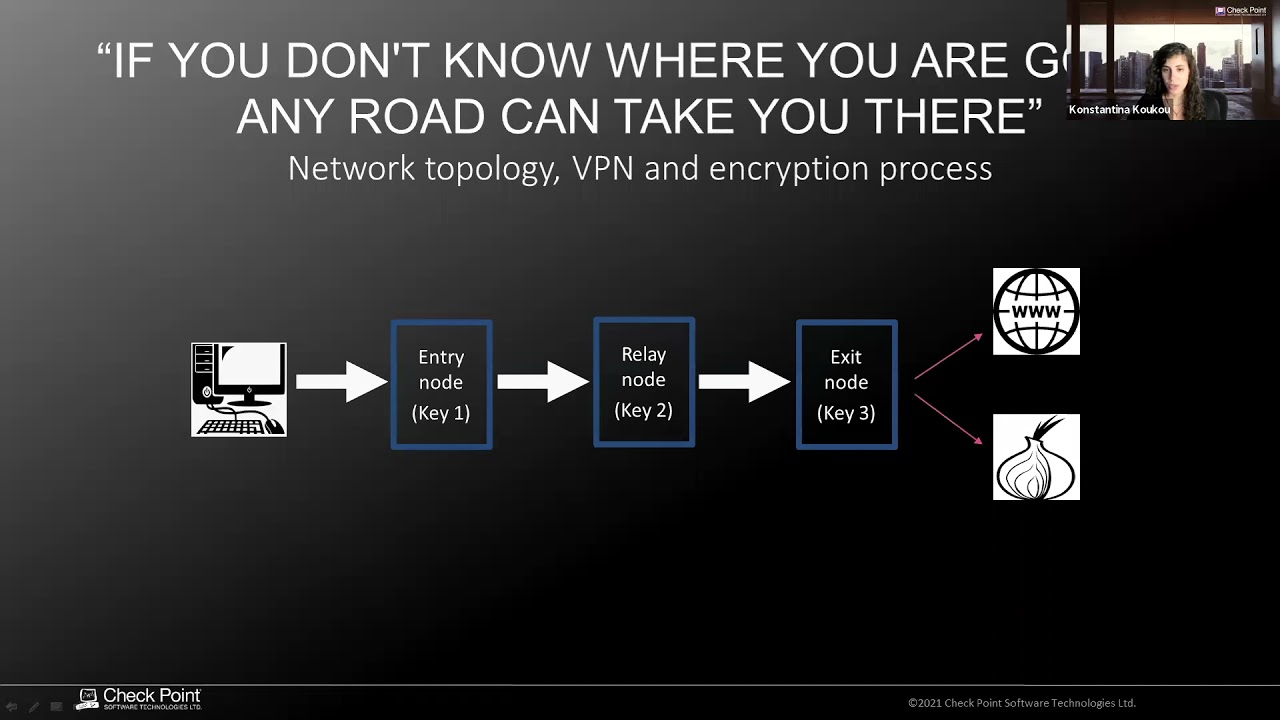
there is no notification for two people that can get to my site. So, this is probably, I want to show you the typical connection, how it's done using the ONION protocol. And you can go through the website, download the package, which is pretty much like a VPN and also containing the web browser that exists in the bundle. and we have the user that gets into the network. The first hop we call it an entry node, then goes through an intermediate node or a relay node and then in the third path, the third point in the path is called exit node which is the one that gets me into my final destination. Pretty much all this flow is
what we call the Torch circuit. Once we connect into this network, we are actually part of it and we contribute to the network in a secure way. In order now to establish a communication into the network, the host first needs to set the Torch circuit as we discussed. So this is established by the three hoops that get me to the destination. They are responsible for receiving and sending my packets from and to the destination. And now we have to say that this path can get me either to a legit well-known website of the regular internet or as well of course can drive me to an onion site into the dark web. All this circuit remains active per web
session and this is because it's needed to be private and not be permanent for a lot of time. And there's actually another mechanism that randomly resets the Torr circuit every 10 minutes in order to delete any traceability. The idea now is that every node has to know very little about the next hop into the network and of course very little about the final destination. It's only the exit node that gets the information of the final destination and we will explain. So the host actually creates three private public key pairs that are shared among the three parts of this communication. First, the packet is encrypted by using the packet by using encrypted three times with the key of the entry,
relay and exit node. And each time that this packet travels through the path, I see that for example the node 2 takes out the K1, it decrypts the packet with its own private key and then it knows where to pass the packet to the next hop. So the exit node again takes out the K2, decrypts the packet and as soon as also decrypts K3, it knows that it has to forward the packet to the final destination. Now, by default, the traffic is regularly unencrypted, meaning that the exit node knows always information about the destination, but it's not the node that knows the source. So we protect the user and the privacy itself. On the other
hand, when we go to the entry node, the entry node knows about the user but has no idea about the exit node or the final destination. The relay node stands in the middle so neither the user nor the destination knows. Now, I want you to think about how strategic, viable and vulnerable the last X node is, meaning that it's a node that gets all the information, sometimes unencrypted. And when you act like yourself, like an exit node in the network, for example, the policy, sorry, police departments or inspection organizations can see that kind of strange activity or strange transactions are coming from your IP address. So you have to protect yourself. But on the other hand, you have access to a lot of information. So all in all, it
has a quite important role in the circuit, the exit node. And if one decides to act like an exit node, it better use a guide that is over there in order to do it securely. Now, I want to now go into the rabbit hole, as we said, because we want to see what's actually in there and what someone can do when it's navigating the dark web. First of all, we will start with the more legit stuff. For example, corporations that we know that are also deciding to operate in the dark web, for example, like Facebook. An incentive to do that, for example, would be to show that Facebook cares for the privacy, although we know that it's not the case sometimes. But we see also media pages
like BBC and New York Times that have also their site up there. The reason for that is that they want to promote good investigation and freedom of speech and they want to reach a lot of information that exists into the dark web. But also we see that intelligence agencies like CIA also have a point of presence in the dark web. And this is the reason probably because they want to be open to any whistleblowers that they want to contact them and provide them a secure way to do so and protect them. Now we'll go into the marketplaces and marketplaces like you know it in the regular internet. It could be for example eBay or Amazon WS and there are hidden marketplaces that allows you
actually to buy stolen accounts. These there are accounts for example that you can buy from Netflix account PayPal accounts. information that have been acquired through breaches and the owner of these breaches, the hacker, is trying to get rid of them. So it's selling them through the marketplace in very nice prices. On the other hand, we know the dark side. Let's go into that, but very briefly. Of course, someone can use the dark web in order to buy to buy drugs. This is one of the most used way. Guns is the other very frequent reason someone is using dark web. But also we see that it is feasible for someone to buy American citizenship and generally IDs. And this is quite interesting because sometimes we
find that there is actually someone that's handling is handling those, for example, for a USA citizenship, you can see that someone makes the payment, is expecting the passport and someone in there is a serious inside job that seems that it's for sure handling fake official citizenship documentation. But sometimes like we also have checking checkpoint ourselves, it happens that, for example, we We communicated with the dealer of corona vaccine and you never get back. So it's not something that you get for sure. Another service you can get from there is a hacking as a service. It's something that you don't do yourself. You don't buy anything like an exploitation kit, but you order an attack, you
order a DDoS, you order an Instagram hack, a Facebook hack, or there's something interesting here, destroy somebody's life. I don't know how it's doable, but anyway. And we can see also that there are serious discounts on the event of the coronavirus. Another one is a mystery box, very creepy one. It's very trendy on the dark web. Someone, the buyer, sends you a box that you have no idea what's in there. And most frequently it's about creepy stuff. So not interesting, but it's trendy. And let's go about, discuss a little bit about how this the marketplaces are operating. We can see that they are caring a lot about customer satisfaction, although we say that we never, for example, know who is the buyer and we never
reveal the seller. Marketplaces act as intermediates. However, they want to be like loyal entities into the transaction. And what they are doing is that the moment that someone makes the payment, The seller is not paid until the buyer gets the product on his hand and confirms that everything was as expected. So they ensure that the customer satisfaction is up to a level in order to continue the operation. An interesting now question that you may have is what kind, what type of population lies under the dark web? What are the users of the dark web? And the truth is that we can find everyone. You can find someone that are even from criminals to hackers, children that
have curiosity, but we can see even parties that have legitimate interest. For example, we talk about, of course, NSA, CIA, that of course are tracking activities and getting a lot of data and petabytes of data from the dark web. but it's also media researchers and journalists that are looking for information that exists there, as well as some companies from the financial sector that want to look into what's happening there. A nice reading that I would recommend to you is from Jamie Bartlett. He's a journalist himself and he has written several books, including The Dark Net, describing How he experienced all these activities he has done in the investigation into the dark web and what are the conflicts that he personally failed when he
had to go really, really deep into the dark web in order to achieve his investigation goals. Now about the transaction themselves, of course, the communication we discussed is encrypted end-to-end, but now we need also to consider the transaction, how the payments are secured, which is a very, very important subject. Up to some years ago, there were actually some platforms. One of them was the goods transfer, the web money or the Liberty Reserve that acted again as proxies for the payments. They were able to do any kind of transaction, lend you money, do the transaction for you without many approvals. only by giving a simple email. But it happened that those platforms have been taken down due to, of
course, as you can understand, some activities that became traceable by the authorities. So it was about time to find something new to replace those platforms and be the way to ensure the anonymity in the years to come. Bitcoin at that point was in the field, was already there. It was more of a technological vision without having an actual use case. And it was the right time that it started to be used by criminals and people that tried to keep their anonymity. However, there is a slight disadvantage here because although we know that there are private wallets, there are hashes, there is no disclosure of information about the transaction itself, However, if you go now to blockchain.com, you'll see that without
even logging, you'll see that there is information about the wallet ID, the private ID. And somehow, if someone traces that and finds a pattern and looks into all the information, maybe there are slight chances, but there is maybe the possibility that can lead the transaction to a specific wallet and person, and then we would lose the anonymity. So now comes another method, it's called the bit mixing service. What someone can do through the service is again use it as a proxy and say that "okay I want you to carry over this transaction and I want you to do it for example in the time frame of one week" and then the service starts little by little doing
the transactions. and also he can choose, of course, it's always using its own private wallet and it's using an algorithm for the transaction and that ensures better anonymity than even the Bitcoin. Last, and I will try to conclude because I have used more of the time that was assigned, I want to talk about the people that operate in the dark web. Because I see that not in our field, but generally we know there is a misconception about the hikers. It's one with a hoodie in the dark room working on its own, while what actually is there, it's quite the opposite. We see that there are a lot of hacking organizations nowadays, you call it, they have names. It's actually, we're talking about literally companies that operate
the hacking activities. For example, we see here that these are the masterminds of the Zeus malware. It was one of the most favored, and I think still it is, banking malwares, banking trojans that managed to get a lot of millions from millions of of users by, of course, infecting the workstation and being able to take the username and the password. And sometimes they were even able, of course, to bypass the two-factor authentication and complete transaction of very big amount of money. And I want you to have into your mind that when we're talking about this corporations and hacking corporations they actually have the structure of a regular company We can see there is the kingpin,
it's like we call the CEO in our world. It's someone that controls the whole business. But it's also the developers that are developing the malware. They are the server guys that are taking care of the servers, the uptime in order to be able to spread and deliver the malware. They are the QA managers, they are the people, the managing directors, they are the ones that are taking care of the hacking campaigns and making them successful. And of course, there's also an operations, money operations manager that takes care of the financial stuff. And now with that, I would like to take you into the light to find a way out of this dark world. And to sum up, I
would like to say that if at some point this presentation raised your curiosity about trying things yourself, I think that you better do it with safety. So I have to give you some hints. First of all, you have to disable the JavaScript auto updates. This prevents the execution of potential exploits on the browser. We suggest always to use your own VM, not expose your host machine over there. You should use a very strong nickname, something that you have never used in the regular internet, something that needs to be unique. and could never be traced back to your true identity. And last but not least, you should pretty much become familiar with the jargon and the slang in order to be able to communicate
with those people. And with that, I would like to thank you and hope you enjoy the rest of the conference. Bye.





