September 2015 Lab - Password Cracking
Show original YouTube description
Show transcript [en]
all right I didn't get started on 50 after so um for any of you guys that are going to be actually doing a lab this is a QR code and a shortcut to the branch that has all the relevant information if you do not appear to access i also have 10 flash drives with that stuff hold on so i can give you one of these each drop that information as all the hatches so we're going to talk about Patrick cracking and we're going to do a quick lab I'll talk very briefly before kind of such you guys up to the lab but you guys could go i'll be walking around i can help you out with the lab and then
i'll do a quick briefing at the end to kind of say like what we did fix this problem before read into that my name is John viola I run a group called slopes of the information security which is at least a portion of the crowd the night out so then we have John branches it isn't this a security class or skin it's an undergrad okay pull their meeting for one range Bobby Lynn don't work that software blend them how he has created a sh so we're right great yeah record earlier that um so anyways so mine except the alignments doesn't infosec i also worked right down the road I my contact information via Daniel squad the
first of all what is a hash there's anyone who can when briefly explain what hashes kind of says it up there with the back and say if anyone can explain quickly briefly what was a hash no okay no one's in the mood to participate tonight I see so the best way that has ever been explained in the is a pictographic blender so it's kind of something where you put it in a blender you blend it up and then you get some sort of commotion need some sort of drink or whatever out of it but you can't take that end product and go back to the same website and put in it right then you're just going to have this kind
of mush that's essentially the point of passion they used to coach a core functions essentially modulo and it's meant to be of one way there's a lot more but that's one example so example the passion functions are so it's essentially division and you take care of enter this so to learn for example that we five sha-1 263 Jake 256 before going to or newer shopper each chain 256 they're actually just ratified in August by mist st something 202 but anyways so there's there's a lot of changes going on this feeling with the new economic shake is actually a really interesting because it allows a very block with length using sponge functions so essentially allows you have a hash of
any length you want from one bite to infinity so if it's is a cutie six pit you see length there and there are other Santa's thanks like I me five and shut two and things like that but the moping about shape and about Kitsch act which is what it's based off of is that allows that meant that very cool so then we'll call it both your hashing algorithms there are hashing algorithms and then there were secure hashing algorithms and your app hashing algorithms have three main characteristics and then there's one what point to make about Stevie guys ever see square so if speed is obviously extremely important when it comes to hashing both both internet you sometimes
wanted to be fast and sometimes you want to tweet slow enough talk about that a little bit later but there are also three other primary characteristics preimage resistance collision resistance and second preimage resistance you can kind of read what these are sure you guys are familiar with that kind of notation but preemption resistance do you think we're trying to keep the bottom so end of the message Jason he flashing a key algorithm so like I v5 a shower and a shirt all your result let me know cause this is to accept we can talk about this offline or have any questions I just want to give you kind of like a foundation for what the
difference between I just a general hashing algorithm and securing matching algorithm for same time okay so there's a whole different uses for hashes so a shack is that they going to see message authentication fingerprints use a lot hash algorithms are used for integrity checking so ppi to use a lot digital signatures and they're checking that's what verification so we're in focus tonight on the specific implementation of passion which is patrick reputation so feed as I much before it's a little bit of a fix point too so on whatever you're doing a penetration tester when you're trying to crack passwords you kind of want here you're using what you can just speed this up you want to be
able to hash as many times per second as possible so you can make more attempts you can do a bigger brute force you can fly more entropy things like that ways that you can paralyze it by include GPUs a6 of fpgas a lot of people just use GPUs because they're kind of all temper because you can play video games and you can take that take that same box a craftsman's with it but they do big a six in fpgas which are like specifically made for this one purpose I don't see her here tonight but a friend of mine and a bunch of a 64 Bitcoin mining and those translate very well into this because before my name is essentially
dispassion multiplies and looking for specific awkward so the way that these work is through paralyzation so the GPUs essentially have a lot of the ability to run the same instructions on a large amount of information at the same time so if you so if you a small set so I found this interesting so if you a small set of passwords to crack and you try to crack it on the GPU group it'll actually run a slower than if you have a large amount of passwords because it can't take advantage of the peridot zation as well there are some downsides the GPUs in general I'm wear a six and fpgas are a little bit more hopeful like a lot of
GPUs don't have certain opcodes like a rip rocky over tape which is used on international rhythm so they essentially have to perform I think it's three instructions versus one instructional makin a sec so there are benefits do go to a sick route but a lot of people just end up going on the GPU rock then those are those ever sign of its or what you're trying to defend if you have your store people's passwords are a way to verify somebody's password you want it to be as slow as possible um within within reason as far as performance goes so that if it were to get exfiltrated at some point there it would be tougher for
them to extract the actual passwords for instance if they're just going to someone just does md5 and you don't fold it there are free computed rainbow tables available that do like all all characters help them to bear with simple like one through eight yeah i'm going to talk about that later okay but assault and just quickly assault is a way to make the hash it's supposed to make that has unique so you take a pseudo-random bit of information and append prepend it to a password so that it can't be pre computed so even if your password is literally the lowercase password you penned a unique salt to it it's not only unique output hash so you can't free
compute that's it you had to do it at the time whatever you want treat that the salt and there was also peppers the collectible um so if I for grabbing a recent news and what do you guys have heard about Ashley medicine look like everybody if you haven't heard about it I don't know where you've been so the interesting thing about this so they use the interpret 12 rounds and is kind of to give a good cuz i think the great comparison oh the different hashing algorithms in addition to the technical details here so people were working on cracking the bcrypt 12 wrong password and they got about four thousand facets crack monique and those are essentially
like the password ABC 123 there there were literally one character passwords like those ones are getting crack there and then there's mp5 tokens which a little bit more than just a password but they were able to crack a living million of them in 10 days so just keeping comparison there four thousand and one week 11 million in 10 days an institution returns on the 55 says wii u bar down to seven days it probably still be like not really i want to details about that if you're interested others also last time LastPass breach where they use a PB katie of two which we'll talk about that later but as a way of strengthening the passport by is
actually hatched they say she did 105,000 time so they did it five thousand times I let end you on the client 100,000 pounds of their servers before they sorted so effectively 105,000 and then other one thing might be clear with Xbox Live Raptor flex you know these things are happening all upon this is something that's important to know about it actually does happen it can affect your users because of password reuse so a lot of these people will use whatever ABC 123 for their password and Ashley Madison and it will use the exact same username exact same password on you know they're younger now so that is pretty much it I'm going to do a quick trip to
the lab and I'll talk too much and I'll talk at the end of the lab about some of the things that we can do to finish this to yourself talk more about salt pepper sleepy kitty of tues some other hey srp stuff so quick ensure to the lab what is its scope so the scope of this is essentially database web application stop dumps not necessarily operating system stuff so if you were to expo like a Sam file or something for windows box you're going to get different algorithms like ntlm llm hashes are ancient you know and ntlm hashes and then you can get various you know on Linux there are various choices on how you store your
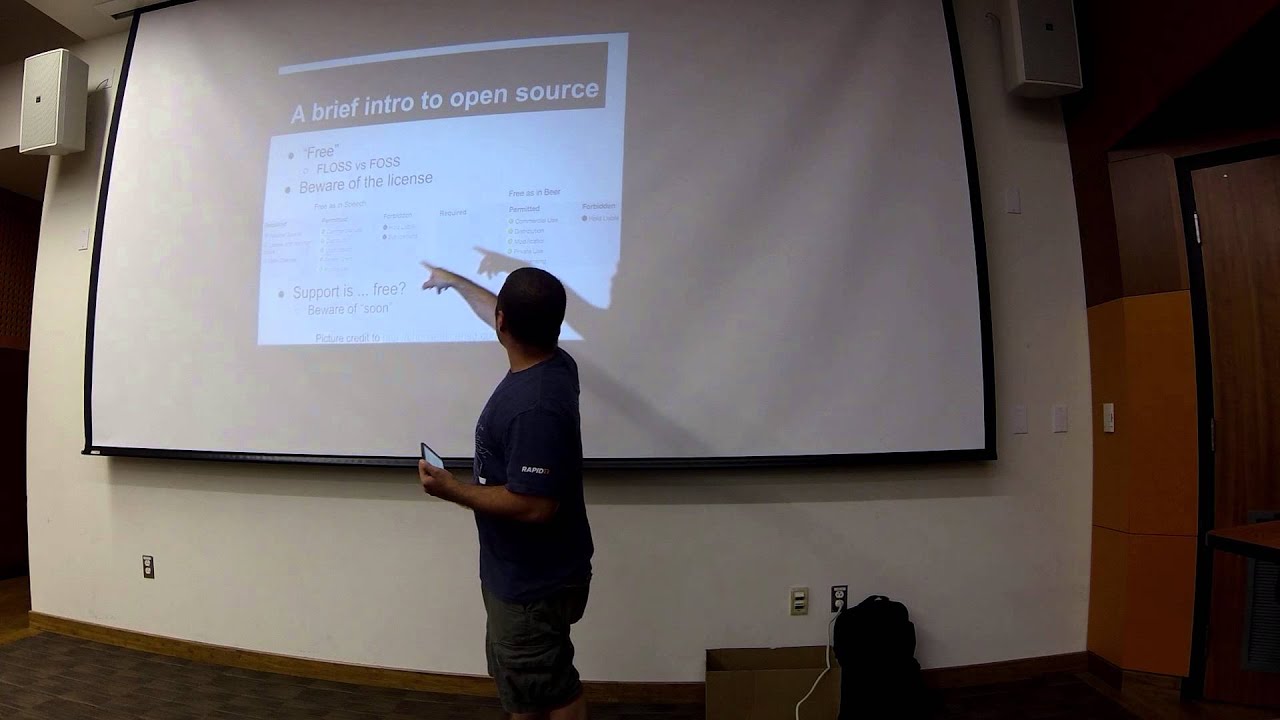
passwords including fuel efficient des or shot whatever people are quick things more about the tools that we're going to use the night so a brief intro to open source won't talk too much about this but there's floss versus boss free libre open source software versus free open-source software so these are essentially two different two different licenses from open source and usually they differ a lot so like what's required and this one was created here is nothing but freeze receipts you have requirements if you're going to read um so anyways kind of just to be wherever license if you're going to be reusing quote from somebody make sure you know what the requirements are they put in
some cases if you use code like with uh I think it's GPL like you're required to leave that open source and available to public and other ones like em I tease i think i forget allow you to bring it in college but if you're writing a product or something another thing that's interesting is support is like a free and open-source way so which can we be aware of that so they were soon on this example about it perfectly illustrates how I feel about open source so I can go to the next slide there we go so this is the split side with dr. maintenance on the new observers on July 11 2013 they'll be up soon so that's kind of the
thing that you'll see a lot of times when you work with it before software it's just some guy working on it in his personal time you don't know what soon actually means this screen shot was taken like four days ago and it's gonna be back up soon okay you'll also find a lot of working pages and plates and really interesting things that you won't find with enterprise software so depending on your use case you know you might want to take that into account so for instance this club is closed forever The Magus reasonably cydia 44 what makes unavailable all of these are legitimate you should be patrick racking websites there's your fiction is not secure in
this one is gender with the bug on and they are going to inform we're seeing you all there debugging pretty nice for us but this is the kind of stuff that you see whenever you deal with open source software I'm not not to say that open source software isn't great just just beware of using it or using code and how much you can depend on it for I availability so there are a couple options for lab and after this we're going to get goin so there are three main options there's beginner intervening in the competition the main difference is here is the beginner so the hats were different for all of them beginner has download section in the
readme its list a bunch different tools that you can use it also has step-by-step with available hints so if we going to read means the very serene meeting there's on hints folder and his folder literally told you command by command what to do to practice passwords intermediates a little bit different it's different hashes or different passwords it also has it downloads but that's more vague steps so if you want to kinda like pull around or you've done this before you want to touch on how good you are at it if I'm going to go to intermediate and for those of you that are experienced password crackers there is also a competition where i'll be giving away something probably a book a
penetration is my book or two and so that is available for download now but so i'm just going to go on in a limb and say like if you want to use that as your whatever like just do it if you think if you think you can do you think you can win the competition using that i'll let you i'll let you guide the in order to win something for the competition you have to crack eighty percent or more so the first person to crack maybe percent and can submit some sort of proof to me that they did it and what time they did it they will get the first reward and the second award is how much of it can
you crack so how far into it can you get you can crack it a hundred percent then the first cry one hundred percent will get it I doubt what you're gonna do that to do things sure if you share the prize I'm not prize for everybody but yeah you want a big things like three people or something and try to be accomplished that's fine honestly if you've never done this before I think just looking at the beginner look at the hints and step by step they aren't perfect it'll get you most of the way there if you do find anything wrong with it any steps broken links anything like that let me know when those primary things to know is if
you're going to be looking at this on github make sure you're looking at the branch make sure you're looking at my password cracking branches and I have emerged that in the master yet so all the links will be broken if you don't get master so there's a little drop top it says branch master you click the doctor the drop down on github and there's an option for passive cracking 2015 09 24 anyone much accessible competition photo no okay no one is nice sorry so I'm going to do a quick them up and then I'm going to finish up the couple's life that I have so this is actually a quarter turn on Brian period for his do a few cracked ribs this is
two gpus in it it's at his house and we're sitting about it into it and you see the ring around kuta Nash cap right there good a half cat 64 what do you guys have questions about how to choose the GPUs with hash cat one clarification there is that hash cat is cpu-based you have to use Lucy on has passed hashmap or could have cat to use the GPUs and then on match the addition anything to use that GFX whatever to make sure it goes to the discrete favorite so what this is going to do this is going to work on the dump one for beginners is the sha-1 you guys didn't plan it out
this is job one I unsalted and then you'll see they specify what they quickly use and 100 of Sean and this is an interesting gph entertain 65 so with some what do you got you can create a lot of heat so sometimes you don't want to overheat it so their damn ability to have a minute so I'm going to run this real quick
alright so i think is it shooting a lot yeah so let it run for a couple seconds pause it and then show the status so you can see there's a lot more options a lot more information here then you guys are saying hashtag for instance and time cut off your in the there we go so you can see kind of like here's where we recover to iterate recovered 59.8 1% and you can see the sea of the total gpus is 1929 killa hashes per second so that's 1 15 million a second so you can get really up there with these boxes um you get into the billions of these boxes is depending on you you'll notice like this
GPU is a hold of this to use because that one's a little but we never stick works I'm very kind of what you can do with these tools of you if you keep angry you get crack this thing all over to take your graphic dump 18 minutes a menos at 91 and 94 yeah yeah so for anyone over one hundred percent in the eighth minute so I got something really helpful um so and then there's where I've covered couple quick points and then we're out of here alright so I'm I think that this mom so how do we defend so the big thing matters work goes into the hash so a lot of people don't understand this
but actually I Rosa give me five shot one two three there are men they're not necessarily benefit password storage they're used for passionate storage pretty much everywhere that I know about they're not meant they weren't designed the store password even s script which so you guys got your computer is it designed to store password it's designed to derive key to a little bit different um but so we get begin event by using better algorithms we're essentially the fact over if I'm on early about slowing things down making it more resource intensive a different ways so chonburi with the shape allows you to very well put that kind of person curveball anybody trying to crack the passwords
I'm Mary Hart yes hashing is really interesting is that thing the folder that are decrypted s script they essentially so they exploit weaknesses in GPU cracking so that they're still very secure defensive but they're almost equal on a GP crackers heavy seat music you can't really make use of the paralyzation it's like that it and uses the interview just little fish in it there's a lot of things like that inner corners memories you can't have to have babies large amounts of memory it really makes it more expensive to run the Kraken here as well because there are physical different physical constraints about GPU pipelines vs vs memory verses like to hear pop other interesting things srp iterating fotos de que those
ones you won't run to as much iterative photos to page video asian of the bgp it's our piece if you look at the paint yay-hey no gotta give you an idea like what that is it's really an interesting field though I love details on this foot if you want my summary mine suggested i would say it be crypt I recently was looking to beat the perceptor and i found out that those extra some really interesting boundary attacks against a script that lowers the amount of memory is required like that feature doesn't have those problems bigger piece aesthetic porque memory allocation so i know there's also there's better implementation just not this algorithm by my implant is a pkt of
two is it sensor possibly Eurasian function version two but in summer gets just do the same thing over over so you talked earlier around from one last passage 105,000 iterations that kinky asian is just do it over and over and over and all you're doing is increasing the amount of resources takes to get to the end result so x minus one password hundred thousand times in order for me to compare to make sure that the ticket is the right password i'm going to have to detach it on and offline so the doctor can have the hash treat cancer hundred thousand times so you can make that be any number that's hopeful it's almost like a song so assault here if
you kind of talked about this a little bit earlier but it's meant to be looking global TV set of information that you can append prepend to a password to make it globally unique so even if it is literally password you add almost how we do in the beginning of it hash it and you get something different anymore just a hash password and that's typically stored in a database in that a password table where you have almost literally salt pullin password hash Patrick you have to Apollo the solvent password and they use them whenever they're comparing to me you get input from the user you have you can vary against the half Oh pepper it feel the difference so
pepper important cover is to prevent if there's a sequel injection vulnerability and it's someone they would have dumped that path that table they don't keep that local unique set of information in that table and that's all this was a different matter is the location where is effectively the same thing so so in the same table is the password pepper is typically in the code or something and it's more global mean you need an individual unique so you can say like you know XYZ companies you have a pepper and it's you implement that effort for all your passwords so you'd say it would look something like hash salt coolin password and then you have have that
same pepper that use or any other that's word yes um so I always know i mean so that's that's generally a good suggestion I haven't seen very much implementation it seems like it was listen to explore them together yeah
yeah yeah yeah so so it's to prevent people from being able to creep you they need to be another mission that's the point that it's actually the only point of folks and peppers is to to resist free computation or offline computation so they come I can't go home and they work on whatever they have a half will Sultan any other questions is that's all I got that's for contact information then its genteel all that's up for justice john viola TV goodbye that's all I got so thank you very much because I believe that materials out there for a while so if you wanna play