PowerShell Is Dead – Epic Learnings
Show transcript [en]
so thanks for coming to our talk on PowerShell is dead epic learnings so we're going to talk about Gundy ribbon introduction my name is Brandon this is good talky - a little bit about what is PowerShell and when people say what is PowerShell all the different key components of PowerShell and whether it is or is not dead we're going to talk a little bit by the evolution of posture - which is a command control framework written purely in PowerShell by myself and other members and attitude we're then going to talk a bit about EDR some of the history and challenges we face on the offensive side as well as some of the stuff on the defensive side and then
a couple of teacher predictions and hindsight and you know it's already industries going perspective so Who am I so my name's Ben Turner I had at the net read red team so I have direct oversight of all the red team engagements that happen I do get involved from time to time BAFTA tended to step away a little bit now you just to kind of have oversight of all the engagements I am a crest see shafts and TTL and happened for me is done some Red Team Training and that we've delivered a steel confer last couple of years also done some workshops on red teaming and supply as well I've done a few talks as well in
the past if you want to check them out put a few links there and also the lead developer of Cauchy - which we'll talk a little later about other than your eyes the relays the end towards were gonna be so long so I decided to keep me in short and sharp and then I saw Ben's I found a bit of Padme note when I see a picture to me but basically I'm a pencil scooting Sultanate natured one of the red team leads to have multiple red team leads to cut out offensive engagements for intelligence red teaming against large banks and insurers and things in UK and also you may have noticed we were called team spy series also we attend
the year become CTF every year so bit sad that it's the last year this year we've had first place last couple years and gotta hope for the trio this year but some good write-ups if any of you are interested in CTF some quite good challenges we quite like going out there as a team and challenging ourselves so if you want to take a notice from the links we will make the slides available for everyone a bit later on slideshare.net so you can grabbing repeating chances ooh we've gotta get going I just want to reference a few tools and books that we kind of use on a daily basis from our an offensive perspective I'm not going to
point out the more because we'll make the slides available but first let's hacker which is a bit like process explorer is one that I use pretty much my daily basis is going to be a couple of screenshots with this in it's got a couple of good features above process Explorer things like you can receive tokens and the threads and you can manipulate those within protis hacker itself and it got some quite good new points from a dotnet perspective which later we do quite a lot on the process migration injection when we didn't read to you and being able to sort of see the pages in memory is a really great way for us to know whether things are
happening or not happening so the M map is a great way for us to do that and that's all available from sysinternals also cff Explorer for NT core that's another really good application I have on my windows book so any DLL any executable you can right click open with if explorer you can see all of the binding output all the hex you can see the exports and then in a DLL you can patch them on the fly so it's a really good tool like we use quite regularly when we do this or reversing and I'm coming and another one if you're not familiar is property cap and property change so from a writing perspective if
you've got a soft proxy this allows you to use any of your tools that sort of your sign against your target so even things like graphical so like our DP or telnet again sort of mainframes that kind of thing you can do all this by using property chains and pops you cap another couple of books that I just wanted to reference as well so I've been pen testing me quite a few years but I wanted to kind of get a bit of a lower level knowledge of the Windows API tools and tokens and handles and how this all works windows internal part one and so I recently got on them so halfway through it I think it's a really good reference
book it kind of dives into some quite low level knowledge but kind of starts to click a few pieces into place for me when I'm actually sort of doing things like process migration and stuff like that so I think it's a great way to learn also the red team and blue team build menu so I think the more we can know about the defensive side the better we can do a pensive offensive work for our clients so we know how they think and how they were we can work around them and talk about avoidance techniques which we'll talk about a little bit later in this talk and also the hackers playbook I don't like that one
mainly because pushy too is in there so I took with that this year so that sort of crooks of the tool is is what is PowerShell and is it dead I think when a lot of people say how shells dead a lot of its come down from like I guess the elites of the offensive world started to move our business or C sharp and dotnet and but when people say is powerful dead I think you've got to think about it in many different ways so do they mean just directly the PowerShell executable so if you see this running on a box you know is that malicious is that what they say is dead so you can no longer run
standalone powerful executables on the windows host because they're blocking you know is that why it's dead is it actually the system got management dalmatian dll so that's the crooks behind PowerShell so parish register wrapper for this DLL so is it when they say PowerShell is dead that they mean that and now because you've got other techniques from EDR that can detect anything that's loaded into that process that they can now monitor for this so is it that that they think it's dead or is it the folder so that the folder that the executable is launched from so if you move the boulder from there to sort of C temp does that mean now you've got
free rein again to run things like PowerShell as long as you call it something else and also since the introduction of even four and five a lot more advanced security features have been implemented in perishable things like transcript logging script block logging a mess on integration which allows AV vendors now to scan palatal and all of those one-liners that was a lot a lot of the ways that people getting around it and practice began around it was basically you've got direct access to memory she can get script load into memory without getting scammed by 81st so is it that PowerShell v2 that doesn't have any of these are fine and powerful and five is dead so I
just want to talk put those key concepts into your mind and we'll talk a little about this brings us onto toward the evolution of pushy to so pushy to is a command control framework M it was clearly written in PowerShell to start with from a completely client-side and server-side perspective so you install it on the windows box you target windows in distribution its lately developed into sort of - from a server side we'll talk a little bit about that in a sec but it was mainly written I guess from my perspective just because I want to do an achromatic you'll pretty much work I wanted to understand how you get a command from over here to talk through a proxy
through the internet 3 we directors back to your host and make it all work make it all secure I guess it's not about a dream of 60 lines of code they're just basically a netcat reverse shell into what it is now which is probably tens of thousands of lines of code with sort of multiple people helping develop it and it's actually quite a good framework and a lot of people think that because it's got bachi - it probably doesn't do any justice it's just a PowerShell door XE frame where actually it's a lot more about now in the evolution so we've been going at it for about four years in terms of writing and developing Posse -
it was first developed in power sharp and server-side and client-side in December we release version - we had a C sharp fury it looked a little bit like Armitage in COBOL there's a lot of right-click get system right click get screenshot that kind of feature what I ended up was being more a pain in the ass to the eyes because you have to sort of maintain two faults of the project every time you make an update to the command line part yeah they do we part and it was just a bit of a mess and but it was a good learning experience I think we learned a lot from it and when you're really an operator you really
hard asset you just want command line you just want to know what you type in and what you get back you don't have to be waiting the GUI sort of propagate waiting for sort of things to appear if you do something like online you instantly get the output back and that's what we found was most useful when you really hard at it from an operator perspective we are also introducing like a posse to slack channel and in October of 2017 we actually release the reflectively allow so this is those who don't know it's actually loading manage code which is basically what power shop is into an unmanaged code space Steven Huey did kind of all the crooks of the
word behind it and we just kind of use that curry to build into pots so what that meant now is if you are running in a partial that exit process you can migrate out of that into any of the processes owned by that user and that means then from a detection and perspective they have to get a little bit cleverer on how they starts texting things and this is where the system got knowledge Meishan gmail starts to come in we also released sharp socks at the tail end of 2017 just after deer become so a guy called Rob Mazen so that allowed us to basically have a complete stocked proxy through proxy - that allows you to do
things like our dps before it is very much command line driven so you can load PowerShell scripts or anything that's on the host itself the shop so you can deploy that it will all be done by HTTP HTTP beatings all encrypted and basic can be running an RDP session to their domain controller through a compromised host so that was a really big open up for us from a party - perspective and also in 2017 we migrated over to Python so from a c2 server perspective it was a lot more I guess easy to implement because a lot of us as offensive guys want to be on Linux because you kind of know what you're doing on the command
line so we're on the c2 server side to be able to be used on a Linux side and not just a window so we moved over to Python very much the client in the implant site is still PowerShell driven but from a see to serve Richmond it's more manageable and you can move it over different different platforms as well 2018 actually decided you some documentation so to use them to make you never had any documentation really so if it was about time and we also released a Python in plan so now what was actually originally only power shut up has now gone to Python and now you can get a Python implants so actually you can get
over a shell back by on a Mac and things laughs so we've been doing engagements where the cobalt doesn't seem to do Mac Empire the yre one does a little bit out there that we could get hands on and actually you know make our own so we kind of introduced this with an pushing to as well now and then in 2019 which we'll talk about at the end is basically a shopping plan so getting getting up with a cool kid who decided to show up in plant Christmas over my Christmas holiday store looking better today than right a sharp implant which we'll talk about and also not that you probably want to use it or you think you have any
clients that have 2003 in XP the c-sharp version does actually work on that as well it's just quite amazing from our perspective there's also this crossing that would it wasn't so this is what the CTU servant looked like you have an implant Handler and a server and you basically get the implants on the right and on the left you see the output that's very simple you open a Windows box this is again the 2016 release so you have like almost have split-screen one on the right showed you implies communal on the lap side you're out there and you get logging logging was the kind of key important part about all of this the reason why we made it was because
everything you do need to be logged from an app from a defensive perspective so that when we go to the client and say we didn't list against your stain they can then learn to work with that and kind of make their detection and put them in place to what we actually did and timings are really quite important so if you don't track your logs accordingly then obviously you're giving it false data to the client which isn't helpful for them when they're trying to track back through all their logs of all their different systems and actually play back this is more of a purple team exercise so again back in 2016 what did PowerShell look like when you had
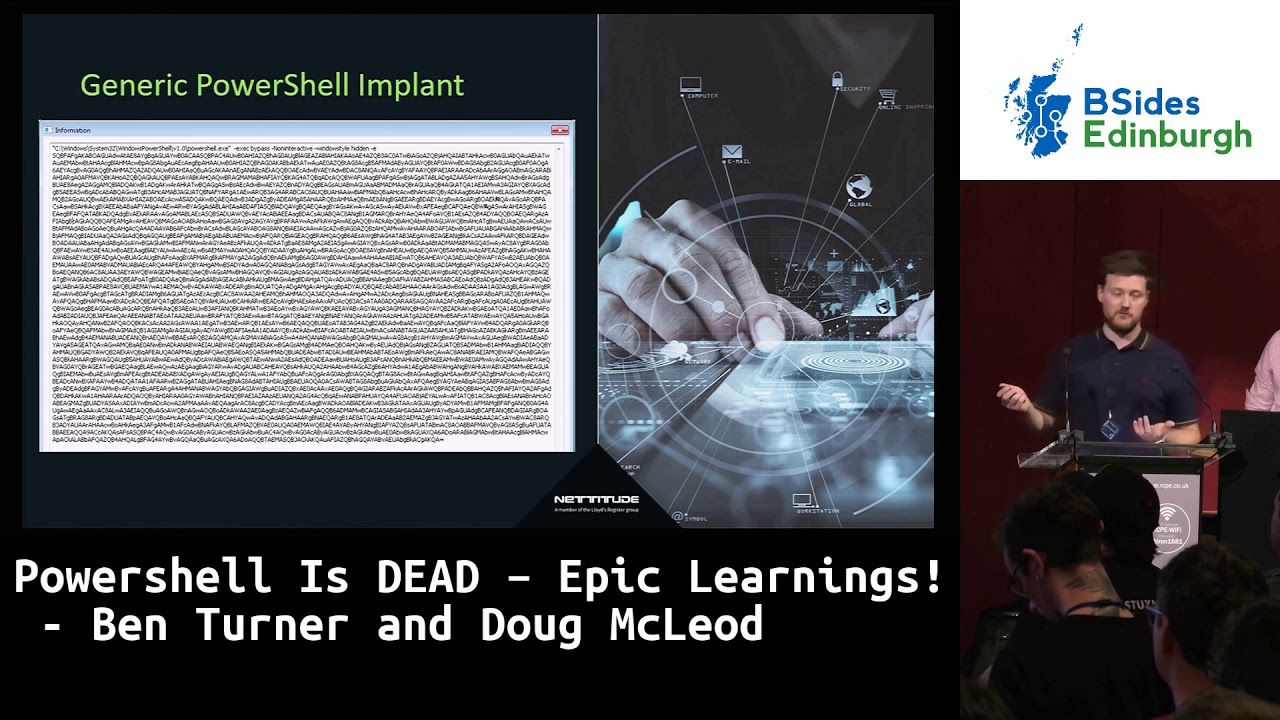
compromised a host so I've been hoping to see what's wrong with this but quite simply there's a PowerShell one-liner running there so our process running this is the malicious situ running on any host so this is how you would have found quashy - back in 2016 so if from a defensive perspective they knew that was something they've been compromised they knew the power of running what do we do to try and find out a little bit more information is the command line arguments so anything with a - e flag is generally malicious mostly malicious and while that is just the basics for encoded blob of data so this is what it looks like a lot of data no legitimate
process is really running things like this nowadays and what that means as well because it's basic C forms we know is only encoded you can reverse that and you can quite happily you get the basically the drop or the potty to implant back in its raw state so you can see the commanding control framework so it's sort of beaconing - you can see the crypto that it's using and see all of the data from The Dropper perspective and what that meant was when - the EDR soar timeline came along was if you do a quick search across your entire estate the process named PowerShell basically you can find all their own plans so from a defense perspective one's easy arcane
thing we've kind of had it with that game because this is how easy it was kind of find where we that's entire estate once they've got the good visibility of all our em points and then they can dive into any one of these to see the command-line arguments reverse those command-line arguments know where we're beating to and block those beacons back we're out that's how quick it can be and the defensive perspective to stop an attack if they're anything like PowerShell as long as you've got the right things on the host like EDR so I guess at this point the approach was more block powershell on all endpoints don't let PowerShell one that's the fix that's easy happy days
winner only I'll have signed PowerShell scripts so you know they're not gonna be signed so what if they can get them in in any way they can be ran because process what did they can get around that then they can only run sign powerful scripts so it's a winner I guess the modern approach now is actually not by it's more upgrade to partial pi which has greater visibility so that the attackers in let them run those one-liners and then detect them on so in sort of mid stages there at app so you can actually see what they go in after and what they're looking for on your estate so things like a MSI integration with a B so that's now
powershell version 5 the transcript logging module login script pod login so if you run watch you - in PowerShell 5 you will see every command that's ever ran so that's the kind of visibility have with all these extra features in PowerShell 5 having said all of this back in 2018 by RDS and really great research and according to fire IAB 233 have been basically compromising lots of different aerospace industries across 2018 is matching really good bloggers if you're interested so posse team has been noted to be used this is the literally the PowerShell version as well so this is the very original PowerShell Dropper not the Python server which has got a little better not the reflective DLL
they are literally using the powers on one-liners compromised countries sorry organizations across the world and it's suspected attribution is around as well so if you want to take it's quite an interesting just through articles it brings me on sort of the.net assembly so what is the PowerShell executable exactly so basically what that is is that as I said before is a wrapper for the.net automation DLL and what you'll see if you look into a process hacker or process Explorer and you look at a powershell binaries running you'll see these two tabs don't necessarily performance well I'll show you is this loaded the CLR inside of that process and in this version its PowerShell booting tools are at this CL are version
two which is in effect PowerShell version two if you look at the modules load its these are all the deals are loaded with in that process you'll see the management automation that has always loaded within a process that's running motion you can't get around that carbon is done some quite good work on how you could maybe manipulate that but it's not trivial at all so anything that's running power tool or anything in unmanaged world or partial will always have the system that might have an automation DLL and that's a great way for detecting it so this is when we introduced the reflectively allow about from the Steven hero stuff so that basically is loading the dotnet version
to CL are inside of unmanaged code so a managed code is basically you know the C world instead of the c-sharp world and so and again this is this is code the Steven tiers didn't work on it's loading the version to the CLR so well that is what that does as well if you're running on a host that has version 2 and version 4 which is quite common except for version 10 now which is actually a remove support for dotnet b2 it allows you to basically remove all the a MSI integration or the transcript logging script but log in because you're loading version 2 of the CLR not version full so these are kind of things you can do on a
host if you know they've got both of the versions run the downgrade attack all the common scripts like power of you were always great tools out there that you want to use are all written version 2 so there's no point in loading the vision for the CLR so this is quite you know how simple it can be to code this up into a reflective DLL and also an app domain so an app domain is in the dotnet world is where they store all the binaries in a simple app domain so it keeps it all consolidated into one up to Maine you can have multiple app domains into it inside of a process but initiative since we keep them all
consolidated into one because that means you can garbage collect them at the end does it remove the whole abdomen and then we want to do is basically load the app the main so in the reflective the allow for boshy too and we have two options you can either load the vision for the version two obviously a large depending on what you want to do so the vision to all just be loaded directly or the vision for tribalism for if assume you're you looking for is an available little fallback division to so what that means now is if you take a look at this process listing can anyone tell me where what she too is hidden in
here well actually it's really difficult at this point there's no way of knowing which process we are in there's no power shoulder XE process room so this makes it a little bit more difficult for the defenders so if you find us inside the network unless they've got some really cool things like system on or EDR on the endpoints they can actually see the process is loaded so take tune Sh executables one's a legitimate one are ones that we've migrated partially to it gives its full command of control over the end point the only subtle difference is ones about the system that management automation DLL loaded one hasn't that's the only way of telling whether this
process is malicious or not from a positive perspective another way is also whether it's gone abdomen so known SH process should have an app domain load it's not a dotnet binary it's a sea binary written from Microsoft there's no good reason why I should have the dotnet app domain loaded and there's just a good way of telling basically it's been compromised but again you need to have all these tools on the endpoint to ever see this if you've got nothing rollback and just basic idea on an endpoint there's no way of knowing at this point whether you've been compromised in a network or not however again with the likes of EDR providing they've got things like tracing in taining enabled
or carbon black you can make a go right tell me across my entire stay where the systems at management automation DLL is been loaded inside of a running process if you do that again you will find every process that we're running in again you probably gonna have a lot of other process like legitimately like PowerShell so you need to start excluding things like PowerShell because at this point you're not looking for that you're looking for anything is loading outside of PowerShell and this is the kind of response that you'll get so you've now noticed across your estate that there's four processes running that shouldn't have the systems on that don't man or making yeah are loaded
another sort of upset consideration that we kind of moved along in the timeline of gosh t2 is ad site and assembly load so a lot of processes sorry a lot of good PowerShell scripts that people write you add type and there's a good reason for that they do it so they they show you the cow so they're not just putting a big blob of basics before and then doing assembly load but actually showing you the code and then you you know you compiling it on the fly however from an upset perspective if you're running this inside a posse to inside a save an SH process and you do add type on your PowerShell script all that's
doing as you can see here it's quite small but it's actually running CFC which is a command line compiler for c-sharp it's compiling that bit of code on the fly and then it's dropping things to disk like temperature C files and dropping a dll to this so all this is happening and it's in a flash of a second you won't even notice it when operationally you'll just think hey it's worked great carry on however if they've got things what T Neum and they're looking out for things like dot c SC dot TMP got DLL this is again another way that you can get the call so making sure that you can put all of your scripts to bet so basically
compiled code using assembly loads is the way to go so these are how the things that we've got to adapt to our surrounding depending on the type of client that we're going after another thing that's quite interesting is the assembly load so assembly loads what obviously the way you should be going however MSI is starting to have integration within now so XP ends uh some work around the early release of this for Microsoft so Microsoft are looking to put basically msi into anything that's loaded from an assembly load perspective and this is basically an early release as we're just checking out his growth and when they actually release the code and whether we can get
out of it a lot of this is basically built into your process though so a lot of the msi and hooking and things like that the reason why it's an issue is because in your process and Dougal talked a little bit about that so of the ins next phase of the EDR and next in very much for those on the back does actually stain upon tension onto gravity time and so easy are basically sensor agent deployed two end points that then send a lot of information back about behavior what's happening on the system is who saw much more a know about what's going on in the system much more sense of what's going on oh nice process
fifteen so when I word document or a macro runs that executes a been lunches W scripts on a shell command and then then load something an executor or vowel I'll be in an ace-high Dark Age free and we'll see if it's all about looks like but basically it does everything so much more visibility some of the example vendors you probably already seen carbon black where you can search for the system management automation do think that silence lumison Symantec endpoint protection so end point detection before before you dr came along the blue team ken ahead in the sound end of the noise gone looking for fun quite Ben's mansion in there with PowerShell one-liners and but bringing in dr end but i'm when i'm
breaking into an organization that opposes lesson you can see what's there been a better group on when i get on the horse and a CER that's pretty much me do you not want I don't want to be an environment in dr for someone could have a balance among a lot more about what's actually going on a lot of the things were actually did more painting a so-called going back in time almost like game hacking for some upper so avoidance first and foremost I have got a number of TTP that I know is usable for also converter and thousand five red teams but actually and intelligence to indicate what level of three actor you're supposed to be
simulating and then you go and pull the same tension TTP severe so one one engagement we're on and carbon black detected us or we're migrating the SPC goes to for sideburn connections through same renders very nice so we don't have an unsigned binary connects notes that's a signature of our carbon black and so we're trying to hide in there we use WMI to propel the horse so about more advanced not just one ancestor mental and cameras are on there you may be monitoring for and dropping files as estimate Heather obsessed them so that your your Haven on the news you can see them so if you talking assistance songs in 2007 you will see it without changing the
settings for that lets our detection and probably the students exercise from them carbon black does what it says it's positive but really when we went back and looked and said you know gods go back against this organization how are we going to go against them and carbon black tar number signatures and a number of pieces of did another place pet names especially materials one might attack three months another one they all keep then and that's what students analysis with but actually just read the [ __ ] burning it's actually given away epiphany students as an attacker so we can test and see exactly what's going on and buy a lot defective copra good that we've got suspicious
SVC Hostgator and processes and hadn't system files high profile with WMI instead some of the more obvious anxious publicly to go by so things like susta Mentos my object line in undetected but co-creating fulfillment of the America to take it so can we go back then how do we do it not getting detected so we're already loading up in the fashion email that wouldn't open so we can migrate and outlook it's not on a watchlist who know down the reflective about function so basically been insane work world had SDC posters of Palin and I was actually launching CSC to compile some of our parasol structure named execute we can bypass on by just reflects of the motor
functions but you start marking causal system in hiding most all these things find alternate methods to query the system so testamento for example the period is one lap and lean persistence so within review the works best to see what is working for us written for start-up time and he said make an appointment with his thoughts defense by junction holders with phone hijacking and we can start to do what template so the word center the tempo actually ones is no trusted location to any man who pay into that will ultimately one of the things on England's work so it is not to bypass somebody's in India time some of them and then lastly need is some people in
my part in black so it was the point on all the end point actually in several state doesn't so we can be very stealthy what or methods again and quickly find a way to s3 and then new data desire belong in be and a place that they have moved as a relative whatsoever and I'm never not taking a truck we will go attain iam cycle definition so and that's what God has working for system management automation dealer with friends talking a lot about but it's not working for these process last names and then if you looked at number one here it says not doing a hash checksum or digital check on any of the process in the location you can see in
point to why that's actually bad you can play PowerShell or any of our implants or covet that name and it will bypass the spinner Allah just completely bypasses when you know what's going on is much better I am so again treachery patents Britain and and again none of this is new this is universe since 2009 pretty F students talking over here in another blog post it's a normal stuff they see to implementation and Porsches and Porsches we also got migrate path past when we run search pool called post on suspended state it's going to use and reflective DLL injection and to that and then it's going to get up hitting type of post Peter and ice exactly what we see here
approach will explode and I'll launch in search for post and again if you look and say something like process hacker or who says it's cooler than this year the parent has explorer so kind of tracked where thanks it's been going from we look back at our example where you can see a word doc is you've got worked in a matter of abuse cracked and then lunch in your binary well I thinking Shrek check potential and thinking what I actually got learned from when we're jumping in fixed water we're removing our tradition to that path to actually pulled out and again just it sure while we're doing this we're still actually even the same IOC so we're on the CLR
for the process amount of automation and sailed are important there's no running and that this is a some of the code that's actually and a DLL but if people with the Porsche it's open-source you can look at the code that the DLL are obviously compiles to you town or a start-up in full eggs and help you attribute list and inside that we've then got pods where the process which allows us to basically specify this fifth parent that we want to come from and actually it's taken from stack or book law if you look there and so again this is carbon black unless bypasses carbon black or like threats carbon black and to thanking where it came from
so a now and side Explorer Thor exit as a SBC votes in this example it's not it's not working out when it's actually came from it is messing so as a defender when you found out that your your workstation to look at it see what's going on your forensics you make master spit you make mess of actions are then happened that's what we're looking to do we're looking for play and with what II D are on the host but we get ready so often by parcel so there are methods for detecting and paint sleeping tarnish a bra a blogger exact months ago and this is using event tracing for windows so at the very top you've got
the header field and that contains process ID that's actually a payment process for anything that burst so Kinect has a task which is I'm giving here you can see that the hitting process ID and Sebu 92 for actually matches the header length record in red but when you actually split one what actually happens as a process ID and then as force X 5/3 and if you look at the header it's 9 to 24 so they should always match and they don't so it's been split so now we can start to write lyrics for that as well [Music] and are better at rectory process arguments with them then one scene what about this no and so inside a process
you've got the pair process environment block and that tells you a lot about what's actually inside our processes got a lot of information do not process one of the things it's got is RTL user process parameters or the process parameters which is got another structure what you can do parse and then say that's the command link and so the way we can abuse this is basically we can create a process that's suspended disco an argument so we can have like command prompt and launch in stages just a string and then we identified by the player base with antique really process information but in parse the pipe using that structure pasta the command-line arguments and then you can overwrite the
command-line arguments with whatever we want using very precise memories we're going to patch it in there many policies on suspended state don't want to resume it what I actually get stacked off is what was there just as you are about to resume what the command-line arguments were well what's actually recorded by Wendell is is what happens when it was created when it was in a suspended state so you cannot fake argument to the start and then then you're Bill arguments or object pronoun suspended so we put this on a lot of parsing to fill in some of the things like porch that's open source kill them with God's not open-sourcing only customers get this year when you do
find a couple good examples online and cobalt rates caught us with art here as well as a statement we're using this 15 EXPN also brought a blog post Oh example per click on type C and C++ art to do the same thing and then the one I like the best is fuzzy 6 Swamp Thing which is a c-sharp implementation and we're just going to do a quick example what that looks like for or at least unpack first so I thought it what's one thing think is going to launch command prompt it's going to echo out Hello Sailor as fake arguments and then it's going to have real arguments off below B sides so what we see you can exit pops is hold on
these sides is equal to-- so that's what's actually executed what a public nsaids process after we actually see the command line says although sailor because it's tracking what was done at their national stage know what was done when it would resume so again you can correct things then you're probably thanking her sorry I jumped ahead there and so for this bet there's a warning so certain certain process explorers and composers work from certain tiles are actually go and read the tab that you've updated so if you don't modify it or once you've modified it zoom there's going to be the the real arguments it can be reached and have a swampthing actor does something look cool so when
it's a actress is suspended with a fake arguments then it changes the arguments and then resumes it then changes in fake ones against the only one people's along to look afterwards doesn't see anything and if you're thinking why and why are you doing this and the real answer is partial one - for example or all that - would just disappear you can make it look you can make it look like whatever you want so the still launch powershell you may get caught for that but all that all that extra stuff thorne same with these extra additional education methods and then lateral movement and lateral movement sometimes when you break into one post in you're moving to another
you've actually trying to remove attribution - how do you go and you might have tails into them punting on to some URLs to just minimize that people this instance of is in one and hit that away you're still actually in order to settle and constructor so if we can say that SC will run but they don't see the computer name then great they don't move over when so inside user land you've got your processes so you've got a user process and this is all can happen one process but as one Pitkin illustrator maybe not perfect either you've got a user process it called virtual our cakes which then calls it W allocate virtual memory and then that talks or through
such calls to the caramel and that's where your actions then actually carry though so all the windows api calls have people through that but this is where it gets like old-school gaming as and when you're talking about cookin so he can is really manipulate in the logic flaw off and something's going on and then being able to enter set that and make modifications to it so another quick example of that as just like you should deal with some c-sharp code on it but when you put the red thought there that's a great point that's actually injecting CCS in terminate at one thing and that's not one like hot patch in our token because you're actually and
manipulating the way that that floss which is a really quite easy example but if we if we look at what you are is actually doing it and when you go from virtual archaic 2zw allocate memory and we're we've got I have it up there so I have the trampoline it's going to happen enter the space where that actually is it's a jompa dress so you've got a jump people so the job tables updated by VR and and then they control that so anything that's come throughout they can no check it is good or bad if it's malicious or not and then pass on to Carol that's good and terminate that is bad but there is a problem here and you
can see what that is but really it's all happen in the New Zealand it's not happen in the kernel so actually all the stuff doing all the modifications are done they're done in your process so they inject in the DLN and then redirect them to the functions that they put there and your process so from our perspective we can pretty much say what the [ __ ] you did in my house as my process I will not process you can implement those therefore so what we can actually do is repack memory to remove jump to the original code so again it's all SNR or one process so we can do whatever we want with that we can update
the import address table to point to in the correct function so we can create a stop to carry out the south skills and then jump to that stop and that does it instead and you know I agree to remove some of the libraries in Indy LLC is injective in and so I've got a quick demo of what that looks like just because that probably sends about wizardry and it certainly does to me some things too but it's not actually that much that much code and that that much work so this a lot of them was creating a DLL that pitched and two variables but also to say thanks to rob Madison for the help with this but it's
got a couple bumps in it takes two variables and put some basic math on and give you an output so the first run off that there this is just in c-sharp we're just gonna create a class that's gonna load that the DLL so you can see okay and it's going to curve the yellow function hook of a function and then we're going to call it in the main we're gonna get ten and eleven as two numbers it's going to do some basic math on that and it's going to output a result when we click play so yeah we got a result 122 it comes out and actually if we run a mobile pain 222 or keep going out it's
just static math so you do that quick test but now what we're going to do is we're going to hook that function and memories we're going to load that then hook it and we're going to redirect it to our one function this is basically exactly what you PR are doing and we're going to control the floor for the data for the function so then we can do whatever we want with those numbers we're gonna do some different math and just add them together and add sexta to that result will end up in 83 but we quickly look at what that looks like we create a class and then you end up with three or one function so just like a
similar function tips to two integers it's going to write out the entities that human so again it's just a sure that we come forward and then at the very bottom of that function we've got the Tonchi plus value plus 62 which is where we're doing our own math on it and then we're going to go and what exactly where that as in memory and just before we've got some additional DLL unforce here of which is going to be probably called the windows api calls in so we've got things like lord lively and hip hop address he liked the and rape process now if that's actually that API calls we need to do this hey we're
then going to jump back up to the meaning we're gonna look at how this actually plays over an award too lightly finishing end and this is and the pickable function so this is the initial one we did earlier on the earlier one we're then going to identify where that as in memory hey you think it a [ __ ] address then go work at the offset of where that as versus where our code is in memory and then we're going to use right process learning to then update and memory where the place is jumping so as I showed you that jump instruction the sale before well we're just going to overwrite the jump instruction so we get
the base value and if possible one put is going for a jump and then that's gonna Dan jump I will put and then we're gonna click play and then we're going to reset it back to initial one so what we should see when we quite play this time is the value is a it's been hooked we'll see how a math function VAR e to convert with 83 and then we'll see our math function bar it comes out with one two two after that's being unhooked again I really the take home from this is just how easy it was to manipulate this in memory and that's exactly what you dr did and it's exactly what we're doing to
unhook ER which means a really good one like people expiain recently on hooking things like silence from incisor process we've done a lot of work if you look through some of nature's watch and see people at tom wilson are putting other things that turn on Victor went on paper we a lot of power when people are actually using this and user process space and till it gives us a lot of control so and just some naughty are it's not a silver bullet people tend to think as any quickly deploy it for all of your endpoints it does give incredible visibility to the routine highly recommend as a complementary piece and that's the key is a
complementary piece to the defensive strategy it shouldn't be solely relied on and then it does not replace good people with experience that's still the best thing you can have and sage a team and Savior security teams and then it's always going to be a catenary scheme they're always going to do something we're always going to do something they're always going to put a person new security mechanism we're going to look to get by it yeah it just brings it back to I guess the reason why we're here today and it is powershell dead and this is my attempt as no is not name that's scottish for no i think but if you do think marital is doing i guess it does
depend on the environment you going after so it depends on the sophistication at the endpoint it depends on if they've got EDR they've got system on deploy a difficult a knee and what kind of login a monitor and they've got on there and going how you're sending in the payload there's a lot of sort of common scripts and evasion sorry and security of client is now looking for the word power shoulder XE so it does depend on how your weapon or something and delivery into an organization so whether you use power soul or not but if you do think power drill is dead we're kind of get in with the crowd and we made it a c-sharp from
time i'm not going to go too much into town about it but just going to give you a quick if you wanna have a go play at home so once you set up pushy too it's just quite a trivial install links machine you'll see these two bits of code which is basically the sharp and plans in version for the CLR we haven't backboard it to to because all the common lighting so that we need is generally in for and there's a quick way of getting this going so if you're on any any windows box once you know has visibility of the positive server you can run it with this void funk as the entry point so that's the entry point to
start the DLL so that should just kick you off the shell and if you wanna you can migrate to something like search protocol hosts just to prove that you're not actually in c-sharp binary you in an unmanaged process so what does that look again from a defensive perspective so we're in search protocol host as we just migrated to how can we tell now that it's actually a malicious binary and again not PowerShell and it's actually purely just c-sharp so again it will have an app domain that we saw before so very similar it will also hello something called the CLR DLL and the MS core he got the allow these are the two I guess signature
libraries now that got loaded so it's not the system top management though or Mason dealer however there's a lot of other legitimate bindings out there across your estates that will be running things like the CLR lots of applications even things like silence of running so based on net the program on link also have tie-ins to m/s Corey install the CLR so although you can do the similar thing like looking at the system de management automation deal out from a c-sharp perspective it's a lot harder because this is a lot more prevalent across your estate so it's not quite as simple and one of the things I guess I wanted to say as well about the C shop implant is
so everything would based on PowerShell originally so just it with policy our shell is a command prompt so it has things like changed working directory print working directory echo things like copy all those things on a C top in one isn't native so we had actually build or line to the core implant so that's why a lot of like common features and things that weren't there by default we had to build all these one of the things that we've actually done which is using dotnet reflection is allow you to load though any binary so then if you're familiar with cobalt strike and it's assembly and actually assembly fit function this is a similar concept on
that so any of the sort of ghost pack executables or dll's that you can get out there from on the community to use offensively on your items and later you can load into policy too so get one of these processes running go and compile your own dotnet library and you can load it like this using load load module and then the executable or DLL and then do run X C or D alone so here's a quick example so there's two options when actually in windy allow you have to give it the namespace name and the and the map and the class name and then plus the names of us again and I'm a couple about
why and then the method so if you're running if they allow you have to give it a method because it doesn't of an entry point if you're running an XE you don't have to give it an entry point so you'd have to give it a method because it has a default entry point of main so what does that look like under the hood so basically what we do is once you load an assembly it uses assembly load like we talked about earlier basics to a blob and load it back into the run space and you can see it which was shown in a sec and then if you're running an axial go away and run basically invoke which is
the entry point of main so any means if you give it an argument and Scott an argument parser it'll be in there so you can just give it up in Haiti I'll show you all the help and but with the DLL function you need to get actually give it some specific method that you call them in any parameters or arguments that you want to pass to that as well it allows it to be fully extensible so you can go and write any c-sharp application and use it rather see chomping client based on its dotnet for above basically so it's really quite powerful with my trip sort of like the default it only gives you the crooks of an implant all
thumbs or blade download the basic features but you can now go away and create your own sort cordia levels and own process migration methods anything you want over an in.net and allows it's probably usable within the implant I'm just to show you a bit of an upset consideration again when you load something like seatbelt and the assembly name is called CL you will actually see it I'm at now so just speeding up now yeah you'll see seatbelt in the assembly at the main so just things to be to be aware of last slide now it's just been a future prediction so we've said already is a bit of an over reliance on EDR on the endpoints a lot of people are
focusing on all the tertiary assets and probably not enough on their core systems with a critical data you know all the customer data so I can I move to 0 just networks MFA we believe machine learning so I think a lot of people are going to invest a lot more time into the people in process you can really get a handle all your processes and how they sort of administer systems an attacker isn't gonna knows that the know those so from the behavioral analysis perspective you are to know if something is being administered in a different way and no that's an anomaly and potentially start an incident I think see two frameworks going to move back to the sort of C++
base so dotnet premiers PowerShell we're going to start probably going back to sort the course C libraries things like dropping executables onto disk rather than actually running things lot more low bus and Lowell bins and so they were great at a time but they're a finite list so if you're actually dropping things like msbuild or CSC and running them so in a malicious way they're going to know about the maintaining things that can pick up all those really quickly so if you're running things outside of that and they're not like if you get signatures to check in something like an arbitrary execute ones or host sounds really naughty but actually probably gets around a lot of these
superior powers but permit oh we've got time for I think but I'm going to be time I guess there's going to leave you with find a job that you enjoy doing you never work a day in your life the final key note is in track one as well I believe this when starting now sorry we have run over the slides are there if you want no and thanks very much you