Learning Lessons & Imparting Wisdom of Past NSA IAM/IEM and IA-CMM Processes
Show transcript [en]
besides DC would like to thank all of our sponsors and a special thank you to all of our speakers volunteers and organizers for making 2018 a success this is an officially affecting impacting my employer so this is a presentation I gave last year and what it is is a whole bunch of lessons I've learned over the last 35 40 years about why we're so insecure and how we're not fixing it so please this is from me and not my employer Wow humor I love it okay so I've been been doing this for years okay so my first tack was actually a some of you've heard this story basically was when a premise computer or I was playing a game on it
they put their first game on it I don't like losing so I modified the Star Trek game so I ended up with extra dilithium crystals yes and then I started winning and they kept on wondering why I was winning every time and then I showed them and then they made me responsible for security of that machine so and that's pretty much how my career the first system on the Internet the mainframe blah blah so I have a lot of history doing this and dealing with all the crazy things and the interesting thing about it back in the 70s it was hey the computers having a problem in the late 80s right after the DDoS it was
WOW it was there a warm on a network is that what's causing problem now we actually have people that know have a vocabulary to discuss some of these problems so what this is is actually a two-hour I'm gonna go through real quick so history of security and privacy measuring organizations process people technology and beyond sorry you'll have to go to besides Delaware to see my presentation on how to hack a job in a career okay so have you ever heard this guy will swear okay do alien guy because he what he did was he has his document from 1967 anybody born before 1967 you are oh I told you this so majorly so he did a
presentation on security and privacy he was really forward-thinking and when he said is look security privacy we have to deal with at the same time we'll notice as we're discussing how privacy was removed over time for expedience and also he dealt with distributed systems here's the distributive the system you see look look he looked at by the way which I do I have a laser no laser I mean I have a torch for ya I'm doing well but I don't have a laser okay so person's watching me hi people at home I'm moving so take a look at the user if you can see this identification authorization and subtle modifications of software has that changed okay let's
see hardware failure to connect the proper connection cross cross coupled with other networks has that changed okay look at the three threats the maintenance man the systems programmer in the operator has that changed it hasn't and then we have the hardware in the software because there's going to be failures and user identity and access control has that changed this is a long problem that we have not solved and one day one of you or maybe us together we're gonna end up solving it but honestly it's very very frustrating because they're going through a lot again Lee put that down I go any lower could be under here's the interesting part there was this this guy
he would thought it had heard in New York City about these people doing freaking which is hacking phones and he said hey I want to do this movie he went to a bunch of people including the Department of Defense and other people and asked around guess who he found 17 years later that friend Willis where so he discussed all these issues all these issues which by the way you could map each of those issues and two issues within were gates okay so they put out this wonderful movie well this is during the the administration of Ronald Reagan Ronald Reagan during the start talks said hey can we stop the conversation right now with his generals and admirals and stuff
in the room and he said I watched this movie and he started telling the story of the movie and he said get back to me within six months and tell us if we are potentially compromisable well actually yes that's why this was created pretty scary and huh so there we go so over time they want to formalize it here's the formalization of how to secure the networks based on that movie the ideas that actually had to take place the the thought process is to address all of that okay by the way do you have you guys ever seen one of those of a couple copies of the whole suite at home it's it's interesting from a
archival standpoint to see that again we're still dealing with exactly the same problems then as we are now except now we have these very expensive products that only solve 25 or small percentages of this stuff okay so when we started creating these we realized that we needed we needed to remove privacy because it was too complex to add to the thought process so we ended up with these different certification eventually certification accreditation models in each of those models we had related to infoset COMSEC IAS and misuse of information personnel administration systems this look like has anybody done any assessments just look like assessments NIST 800 series yeah it's that's actually a more mature version of
this so these are all interrelated disciplines we've tried to address again the same problems from back here
so what's happened is all the groups across the top have been contributing to creating these standards great stuff great documentation and adding documentation along the way these were all documents that are available or they're historic or current in the public space all different types of guidance from the certification and accreditation standpoint they're trying to identify the risks from that first page from that graphic what are the safeguards how do we stop the attacker coming in how do I modify information denial and author unauthorized use right this is what we deal with every day on an offense or offense is this is what we're abusing and this is what we're dealing with for risk management because
risk management came from the pretty much the insurance side how do I see the same thing happen again and again and figure out what the what the risk is one of the big challenges of this risk assessment model is people that are doing it may not actually understand what the risk is a little story I was doing an assessment for a government organization and I was told that this server in this room did not mean an assessment because it was in the room and nobody could get to it and I said no really so let's talk about what some of the problems are and he described it and described he says fight but it's in this
locker room and you have to sign in and everything and I pointed to the computer cable I said so what's going through here isn't that like an entrance do you have access to this and he just was very angry with me and it took about two weeks for me to come back and actually finish this assessment but honestly people have expectations that a cable goes through the wall or I have wireless access that nobody can intercept it anyway which by the way goes back to that first slide okay this is the current process we've dealt with again furnace and everything else for CNAs privacy really is included with it yes we've added some PII issues but we
haven't talked about the real long-term issues and by the way this didn't has anybody ever lost their data okay well here's here's a good question have you ever lost your fingerprint data okay are you a threat now because you can't use this for two-factor authentication have you lost any jobs that you know of because you can't do that we don't know at this point how about your face having your genetic material that becomes a whole other issue if somebody has your genetic material maybe your kids and or whatever your family whatever good angle is a job just because that genetic material has been lost and somebody's gonna use it for insurance or advertising or whatever they use it for
okay again we've been focused on security but not actually dealing with it by the way the the interesting part about why this is a problem is if I take something there's something lost over here and the wall deals with that the wall doesn't deal with duplicating this duplicating this and then using it for other uses and it's really really frustrating for me because well you know people have my face out there and resolutions that they shouldn't and things like that let's see so one of the challenges of the early days is everybody had their own assessment model every single organization and by the way I didn't include all the lack of commercial space assessments and audits it took them a
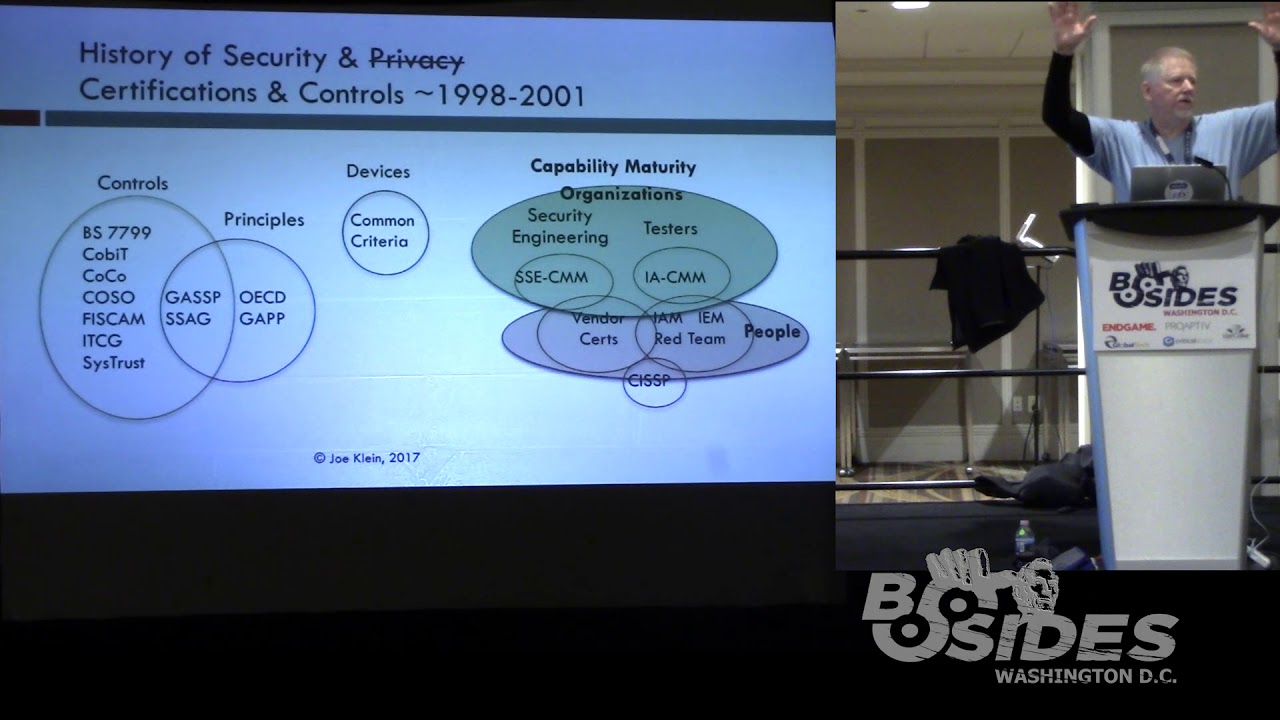
while to actually get in front of that here's all the certifications between 98 and 2001 each one if you were in the business at that time and you were just looking at controls your organization depending on your organization may have to go through five different audits or eight different audits and assessments and and capability models from different organizations but nobody had a way of actually thinking about how to pull them together okay and by the way some of you were still going through this fist cam versus a FISMA assessment different thing oh yeah by the way people were certified too that's what our certificates are that's what red team's can be certified CSS Peas you know
whatever the certification process is by the way there are now more certifications and finally I was picking on somebody at a conference eight years ago and I said look please if you're gonna make a certification use the letters E and Q so I can say that I have the certifications from A to Z well yes we now have certifications at our q and z so one of the interesting processes we're actually going back to rethinking was the process of a maturity model has anybody heard about the maturity model for threat intelligence this is to deal with some companies don't have the infrastructure the people the processes the management support of the legal support to be able to provide a
mature organization to be able to even deal with threat intelligence right now threat intelligence for those communities are turned it off turn it off turn it off turn it off not hey is there somebody using this in my infrastructure and can I see if that's actually communicating with a command-and-control and can I understand which systems were actually compromised by that oh yes or you're not even using the threat intelligence you're just getting and paying for it which when I've done some assessments and talk to customers over the years there are a lot of them that don't even they're paying for service or not actually using especially to the fullest so here are the categories from one to five zero is
basically not even performed how many organizations do you see don't even perform this okay couple all voting machines they perform them voting machines no seriously have it automobiles up until recently okay so we have performed information so essentially it's a base the big challenge about this performed this way is whoever's working for that has to be a superhero or unicorn because this is why people need unicorns because it requires so much work it requires so much knowledge they usually after you've done it a couple times you've burned out then you have plane and tract welded well-defined quantitative analysis this is where threat intelligence becomes real important a lot of high-end products become important connecting your infrastructure and quantitative
improvements this is where we actually want to get we want to basically see that something happened in their network and we can actually change it via a smart person within a few minutes or some machine learning stuff because I got bored of seeing it happen all the time and I make it change automatically okay this is where we are again we left this because it was a hard for people in the 90s and early 2000s let's see there we go and if you want these slides I'll send them out and sorry they're so small I the room was only supposed to have like 60 people in it when I presented this so I made sure this why the screen was the
right size and a resolution or everything else so if you look at the red this is the most level of waste the level one again the heroic effort on the design how many people did early cloud stuff okay you're doing heroic work just to figure out how to secure it and did you get all the information you needed to secure it adequately no most of us don't when we get into a new technology okay and then basic project management does somebody actually have a project management are they actually creating metrics around it again when you're especially in the cloud I mean how did you how did you actually have a metrics around how many people logged in how
often they logged into they log in at night and I logged in a day none of that existed in the early days of cloud even up to C 2008 2000 2009 when I was implementing cloud for some people processes are there validated processes for the cloud one interesting question are you allowed to actually connect into your cloud providers processes as feedback anybody able to do that right now how about DNS enumeration of your networks because they're using DNS and not scanning your networks can you get access to that stuff or DDoS again these are processes as you mature you'll get a lot more information and towards the top is pretty much productivity and quality this is where
we want to become secure and secure by the way that took some time wait a second there you go um yeah that was my fancy stuff so has anybody heard of system security engineering okay just put out a wonderful document this whole concept was killed in the late 80s Early 90s why we had devices that had blinky lights on them and because they blinked they must be secure and we ended up buying more of those blinky lights we've now come to the conclusion that the blinky lights haven't protected us very well this is the processes that were recommended originally the nist team under dr. Ron Ross has done a wonderful job expanding this and bringing this to
the future now here's the issue how many of your organization's have a system security engineer ignoring projects all those hands holy schnikeys they're by the way for the people at home maybe you were raising your hand and nobody here was so if you can see the blue the green and the reddish pink thing the hardest thing for most organizations to get security going is dealing with the organizational process and teaching the project managers because honestly when it comes down to the engineers to figure out how to do monitoring things like that we've got it nailed the real maturity comes in working through towards the right-hand side of this process okay and again this is another
matrix I have a link to this so to simplify this whole process and I say came up with this thing called the I am ie and what they did was they said hey we create a process to number one identify how to do an assessment and it dealt with all the process stuff you know are you doing a backup how do you know you're doing it backup okay can you scan you retrieve one file for me oops your backup software is not working oh there's a log here that says it hasn't been working for a year awesome okay again we don't do that very often the second way is the evaluation we were scanning we're doing some
lightweight penetration testing third is actually a red team love red team's so this was the process by the way this was defunded and it's gone some of the documentation still floating around there's some duct there's some software but it was meant as a formalization of the process to strengthen the organization's processes people technology and policies so that you could actually have a mature infrastructure currently I'm not seeing a lot of processes from the auditing community from the assessment community to be I do this besides the compliance stuff this was the planned time and by the way you'll see this in this was early this was late 90s you'll see a lot of these ideas included with most of
your auditors assessments and pen testers processes so this is a very sound process to go through let's see like as an example I like what the NSA was doing here with this workshop what they did was they asked a really interesting question they would get a group of people together and they would have different experiences within the organization and it would ask ask a question they said what is the most important products you have the data in the organization and you'd write it up on the board and then you'd score it based on how many people thought it was the most important and at the same time the city people in the corner the security people and the
auditors would sit quietly and then they would come back and actually discuss with the criticality of most of these things were do you know what the usually the the lowest priority of the most organizations were email because nobody needs email right because nobody saves things oh by the way the reason I wasn't able to get access because I can't access my email to get this light so ok my case I failed ok but that was usually the lowest from priority standpoint so if you want to look this up there's some information about here this what they then ended up doing and say what is a system what is a system at this point it's not
just a computer it's a bunch of data that's being processed does anybody look at the system end to end who's the consumer and who's the producer especially long chains of these the systems the supply chain of data a lot of people don't look at that I was looking at one assessment at time and found out that they had a really good supply chain except for one thing they couldn't afford certificates so the supply chain in and out the organization was all via email non-encrypted ok this included PII information this included pretty much everything health care information was pretty pretty amazing you can't find those unless you actually do an end and from a consumer process ok
so one of the things I did was after you got the assessment completed and you define what the categories are you would then say well those systems were part of these organizations you would then classify medium high low things like this to identify them and that was the process you did prior to doing the physical assessment you did this risk assessment by the way this process works for all these systems not just a bank not just a federal agency this particular InfoSec methodology can work with pretty much any infrastructure which is pretty cool so then they have the activity they go through the process let's see I'm gonna go with quick this is okay they had that
ìiím when it was a hands-on the nice thing about the IEM for those that have never run an assessment go learn about it it talks about why you're doing different things how to do a scan what type of scan what you're looking for things like that so you've got the process yeah one of the other things that we found to be successful is that the process with the customer you know what are you doing this is wacky make sure you have legal and scope you know nothing worse than starting the assessment against a cloud infrastructure that part of that cloud is owned by somebody else very inconvenient okay create rules of engagement create scoping questions by
the way if you're starting up an assessment this is the perfect scoping questions to ask okay you do an end brief a lot of organizations gave up the in brief process which is here's what we're here to do can you bring all the important people in or the the most important person in that the supporter of making this happen is funding it know by the way put the people in the same room that we're to be working with so we can meet them and you can say hey these are the people we're working with this is why we're doing it a lot of organizations will do assessments without doing that and then you don't get the right information and
there's usually pushback it makes it real hard and that post assessment which is actually creating lists of things this is this hasn't changed in years this is exactly the same assessment stuff we do every time except a lot of organizations don't like network sniffing where we learn from network sniffing bad configurations and routing routing people are never wrong okay I love reading people I'm a routing person yes the other thing we find out is protocols that aren't encrypting things okay so that's something that becomes really useful there are tools in the market there's some broken figurations that will do this for you and snore and sericata but these are things you definitely want to look at
and password compliance how many people are using two-factor today here a little trick on the two-factor you can buy these little USB things are relatively cheap and you can actually use them at home what a concept okay this one just happens to be you the key because I got a stack of them from a conference but considered taking a look at it so when we actually have risk do we ever see assessments from a risk standpoint mapping it back to what we found this is the crown jewels here's what we found and by the way it was not only the crown rules but the data coming in and the data coming out the authentication things like that here's
what we we can use again NIST is recommending something similar to this others have in this process and c-cups you then map all this to say you know how secure the criminal records like in this case criminal records warrants blah blah blah by the way this is just an analogy from somebody else this is this particular set of slides about a criminal organization it's not mine and then going down and saying here's all the CDs that are actually matched to this particular thing we have things like nessa so we'll do parts of these but sometimes unless you map it correctly you can actually say that this vulnerability actually impacts these three systems so this is Welner
abilities the one we want to get rid of in all these three systems here was the coolest thing for the IEM once you actually found the risk and you took the vulnerabilities you created a table with the highest stuff on the upper left-hand corner and the lowest and lower right-hand corner and that gave you the ability to work with the customer and say everything in red you need to finish quickly everything in yellow you want to take care of the things in green if there's three of these together they become yellow or potentially red deal with this this way allowed people to actually go through this process there's a finished high level risk of one system
and it becomes lower to the road towards right all the way customers understand this they don't understand law the current deliverables that we're giving sadly oh my god I got through this quickly sorry so so again going back to me going back done okay going back to this still haven't solved it we now know it's there we have a process that we may end up testing to see if it exists every year we really need to go to infrastructure we're on a real-time basis that we're seeing risks to our important things happen from a defense standpoint also I'm sorry what's the definition of insanity doing the same thing again and again expecting different results I think it's time for
us to stop the insanity see wasn't that perfect to stop the insanity and start thinking differently is there a method that's out there that succeeds oh by the way if you were to learn the method that's succeeded for you for eight or nine years and you're a bank or your federal agency that didn't want to actually be compromised would you turn around and polish it there are organizations that have never been hacked based on some of those technologies and no most of the time it's not just a blinky like things so start asking people so what is your especially when you're in conferences like this so how well have you done on securing this or securing that or if
your red team's any red team people and they all ran away that's awesome if you have red team people you'll get you get three types of red team people which it they're all brilliant and they're special ways that's sorry that actually sounded pretty bad sorry those at home they have experienced on actually how to hack systems and a lot of times what you get is you get people that can go in and get the target you're done four hours and you're done and have a nice day write the report okay you have people that take a little bit while and then you have places when you do assessments you don't get in they've stopped everything so they turn
around they come back and say hey we don't just want you to test this we want you to test this much now and they can't get it then they say you know go this far and they don't get in those are the people we need to figure out where they are so we can learn some tricks from them oh and by the way four pen testers the hardest thing we have is to go and do a pen test last year and find out that they fixed nothing over the year if you look at a lot of the commercial organizations that's what we hear all the time hey wow they never got funded for this year but next year they're
gonna get funded to fix these problems and what do you think most of the fix of the problems are not good engineering but blinky lights so he gets it gets really really frustrating doing this and yes I've been a pen tester and I succeeded there was a few times I didn't succeed no way yes somebody actually figured it out so that was that was pretty cool any questions sorry this was the last minute I usually do a lot more preparation and rant than everything else and she's trying to follow me he knows he has to get up every once in a while which is really fun so if I run around the room will you just kidding
any questions again sorry this was the last minute type ranty thing oh and by the way here's a good question how many are testing the IOT devices and their organizations how about the heating system that's in the building that has a computer attached to it they call them boilers they go boom if things happen how many people have checked they're important I don't know transportation device products those are becoming critical oh by the way I got a new car and you know what the first thing it did when I pulled into the garage it tried to access my wife I know okay think about that for your organizations are your people connecting their cars and their other technology or to your
critical networks okay so things are changing oh by the way very soon we're gonna have devices for extra memory we already have implants at Bluetooth we already have Coquille implants at Bluetooth are they accessing your networks we're not looking at those kind of things today we're also not looking at different frequencies that there are now tools that are in the open source they're used by hands that are used by the biological community the physics community there's lots of other things that we need to be looking at to figure out all are we protecting ourselves so any questions well I ranted and nobody ran away not too many people so thank you [Applause]





