From Vulnerability to CTF
Show original YouTube description
Show transcript [en]
I want to introduce to you Ron Bose lead researcher at rapid7 and for the next session he's going to tell us about from vulnerability to CTF
hello everyone um thank you all for coming this is the first talk I've done to a live audience in like three years so my only Quest is laugh I make jokes because that way I feel like there's actually people around I've been talking to a webcam for years and it's been awful so yeah thanks all for coming this talk is basically going to start off with me talking about myself and uh but what my background is what I've done what I do now stuff like that then we'll talk about ctfs capture flight challenges I've worked on ctfs in a bunch of different contexts over the years and I think a lot of them are there's a lot of good things about ctfs
that we can really learn from then the kind of point of the talk is I want to talk about vulnerabilities I want to go over I think five or six or seven vulnerabilities that either I found or I've known about I've turned the CTF challenges that's where I talk about the process of how I do that and I think bones are cool and I want to talk about them for an hour and that's what we're gonna do another thing I want to say about what we learned just to wrap it all up so who am I I am Ron Bose as our empty Santa my rapid7 I'm a lasikiri researcher which is the fancy wave
saying I'm a uh I write blogs and recommends playing stuff my handle everywhere is Yago xa6 uh Yago from Shakespeare Othello nx86 from the CPU you can find me on GitHub on Twitter on Steam on pretty much every platform I do that there Elias so I want to share with my family first just you know let you get to know me um I have a husband who doesn't like his picture public and I we have two birds together they're both green cheek conures gcc's and because they're gccs we named them playing a shark so flying on the left we've had for about two years and sharp is brand new we hired for we have him for like a
month Spock squawk thank you uh they love joining my video calls and stuff at work it's a lot of fun they're here are the little troublemakers if I just want to show them off every CTF I make has them in there in some way now so at the level open source development and uh I kind of got my starts doing like researchy stuff working on edmap and Brandon who's in the front row being able to end up together back in like 20 2009 2010 and he dragged me a tour trying to do a talk in like 2011 and I got to talk about nmap and that was kind of cool my first big talk these days I work on the medisp flight
before time I research vulnerability stuff like that I'll talk about that more I've written tools for like hash extension attacks um yeah I do lots of Open Source work I've done a DNS Factor DNS tattoo so you might have heard of uh my last three jobs it turns out they're all kind of the same thing uh 2013 I moved to the States from Canada to work on to work at Google um I would we would do among other things reviewing our own products finding bugs in Google stuff and then disclosing those bugs to the product teams and they would fix some stuff very much like internal then I jump to counter hack which is uh
run by let's go this is sort of a affiliate ascends in that counter hack we would do pen testing for customers which meant finding vulnerabilities and customer software and then setting up to the customers and what's really cool about counter hack is we would also do ctfs which I'll talk about soon and the vulnerabilities from customers would feed the ctfs as like ideas for challenges which it talks about and then the the trouble people had or the things people applying on the sea of challenges with feedback into our pen test business so it's a really nice two-way street and that's okay gave me idea for this talk and then about I guess in April this
year I started working at rapid7 so I'm very very new there and representative I do all the same things I take software I find bugs and stuff but now I just released it to public I can talk about it I write Vlogs I play plugins um attackerkb.com is where we post a lot of our write-ups it's a really cool site in my opinion as an employee but also we do really deep Dives on uh vulnerabilities it's a it's one of you okay look at things it's a pretty cool site in terms of CTF um going back to like 2009 or so I've been playing ctfs a large use for skull space which was our um hacker space in
Winnipeg by hometown and later on the I did Defcon CTF with stratum or her uh some of the folks from that from that team are here somewhere so yes is a player for a long long time and then I gotta started doing ctfs as a Creator so I make the Beats High San Francisco CTF along with uh Brendan and Daniel and some others um my previous job we made that were CTF which is like it's a paid thing concerns again me and Daniel work on that together and then Holly heck challenge 20 holiday hack challenge is a free thing that that sounds and kind of how to do every year and that's a huge video
game CTF which we're really proud of again me and Daniel worked on that I should mention I'm gonna put this I LinkedIn slides on the last slide so you'll be able to get there if you want them I should mention what is a CTF uh CTF is a capture the flag challenge basically if you don't know there's multiple different kinds I don't get into like a nitty-gritty things but they're very short versions that players solve security related challenges for points sometimes we just give them a question answer sometimes they attack each other's like infrastructure either way it's security challenges or points and see if you have time tracks I love the ctfs most CTS probably all of them
so I want to show off a little bit of History because I think it's kind of cool the first CTF I did as a player was called stripe CTF in the 2010 apparently and one big takeaway from that CTF was the final challenge was a hash extension vulnerability at the time I'd never heard of hash extension ever and the concept of it just blew my mind and there's no tools for it there was white papers but no like easy to follow documentation so I read the white papers I wrote code I hated it it was really hard I'm not very good at reading academic stuff but I got through it and managed to write a proof
of concept exploit for md5 shot one shot two days six Etc I made a tool called hash extender and I wrote some Vlogs and that's now like the best known tool for it so I can really thank CTF for getting the idea to do that I learned something I'd never learned before uh the photos on the right are from a 2013 CTF called plaid CTF I just put them there because like the story the kid in the bottom right hiding behind the brace acting boxes the name Ethan he's my buddies kid and he came with a cape on and I said why do you have a cable on Ethan and he says I'm a dinosaur
I was like can turkey with that so I think about 7 A.M after working all night on the top right I had to keep on I don't remember why I thought it was a good idea but it was also a dinosaur so in 2010 as a as a hacker space me and skull space worked on quality hack challenge 2010 uh that was back when Daniel was an intern there and we won and Ed wrote like you guys totally rocked you did awesome you're making cool stuff happen and that was in March 2020 2011. so it took three months to pick winners which pretty much is how we always do it um what's cool though about this is that
2011 it told me how good I did and then in 2017 I was working for him so I'm really proud that I was able to kind of turn doing ctfs especially doing them for like Ed into part of my career and that's like one of the reasons I like talking about this is because like CTS has done so much for me that I think it's really cool to talk about um this is the first idea of I wrote this is my playing notes I actually dug through my pile of notebooks I found this and I wrote notes for how I want to make a CTF and I don't want to read all these you're welcome to download the
slides later and read them but the funny thing is I rented these I'm thinking oh yeah I made this challenge again and again and again there's a few things I really like making challenges out of and as far back as 2011 I was still doing it but the first big CTF I did was B-side San Francisco and I'm almost done talking to myself I promise um the story behind this was I was out I met Reed Lowden who's somewhere at this conference I don't think he's in the room and we we went out for lunch or something when I was in San Francisco visiting but he said hey you don't make ctfs do you want to do rctf and I was like sure and
we did it and I recorded Brandon and Daniel and others to help make the CTF and it ended up being like fairly successful and we've been doing it for five years now and each year is better than the last so we do that every spring I think we're doing this one in April so it's really cool to uh see we get to do a big CTF and I'm really happy that that besides San Francisco sorry gives me the the time and Trust read basically says to us like make a CTF let me know what you need and then it goes off and we do our own thing for six months can we make a CTF it's pretty
cool so let's talk about why ctfs are valuable I think I've touched on this a lot already but I feel like I should do more than just talk about vulnerabilities although I like talking about vulnerabilities so this is the best open open licensed image I could find this sort of from a easy Google search to say kind of like people learn a little bit of what they read and a lot of what they do and then even more of what they teach so ctfs are hands-on experience for things that people don't typically get hands-on experience doing but not everyone especially if people are younger or new in their careers are privileged enough to like be able to hack things like I've
been able to as a pen tester or as a researcher or whatever so like being able to teach people things and let them actually do and get Hands-On work is super super valuable and Bug bounties these days kind of fill that role too but not gonna talk about those also with CTS write-ups are very much encouraged and that's where teachings where it comes in for Holiday hack challenge we would do we would value evaluate People based on their write-ups not based on what they actually did we would have a hundred people finish here to a thousand people I don't know the numbers but a lot of people finish it and then would write out submissions of their Solutions and
we would pick the ones that are our favorite technically and our favorite creatively so this is just an example I found not just from Googling around he and like he runs into the travel log I believe and it's really cool that people will then take the things they learn and share with others and like for myself I would always wrap some of my CTF challenges as an author and as a doer and I think it's really good to like really really learn things well I think it's funny you were talking about as laundering and that no one told me I can't use this word but it feels a little bit weird but basically as a pen tester we often do work for
customers and they often have really cool bugs in their software that we can't talk about because they're customers but feeding those bugs into like what's the core of this bug there's nothing to do with a customer but that we can teach people as a lesson so that when they see this bug they'll find it so I'll talk about some of those after what's actually really funny about these is oftentimes bugs you find your real stuff are too simple or too silly to really be bugs you see in ctfs people look and go look there's no way that would be a real bug it's just too silly but a lot of real bugs are that silly
this is kind of a weirder concept when I was young I had a couple slides about this I removed because I thought it was just too much talk about myself there's already too much talking to myself when I was young I did a lot of video game hacking a 2017-18 or when I was 17 18 19 I got really into Blitzer games and regrow cheats and stuff for Starcraft and and Warcraft 2 and Warcraft 3 and stuff and like reverse engineering how those games worked and how the logins worked and how their profiles work they have their anti-cheat work and stuff I learned a lot as like a 17 18 19 year old and you that those those systems don't exist
anymore they only use the same logins anymore so being able to share those with others and say like here's where I learned how to do this here's where I cut my teeth here's what I thought was interesting and being able to wrap it up into a challenge is really cool um so I feel like I'm kind of honoring the vulnerabilities by showing people kind of how they worked we'll talk about a couple of those so now I want to talk about vulnerabilities this is kind of meat of the talk and I think I have about six or so vulnerabilities I want to talk about and we're gonna go pretty quick but on each one I have links to write-ups about them
I have links to the source code I've got a couple live challenges ready to go if they don't mess up if I do mess them up I still have slides with screenshots so the first vulnerability I want to talk about is CV 2020 1388 uh this was a this is the first thing I worked on at the rapid seven and I'm just going to click on my analysis to show off if you want to read this I have a lot a lot a lot of detail about how it works including assembly and clean proof of concept like I wrote a lot about this but I'll give you the sort of 50 000 foot view if you're interested in seeing
more that's cool if you can't read the terminal text at the bottom that's just a screenshot from the page I just showed you so you're absolutely welcome to just read it yourself basically fi's big-ip device was vulnerable to a uh authentication bypass and that's a pretty common vulnerability class because it's really easy to mess up Authentication so the way the authentication works currently even like to this day um basically there's the F5 server I I do it a size two different servers but really there's two Services running on one server the first the first service is a reverse property the reverse proxy would do some types authentication not others and then there's a backend that runs on
localhost and that does a different type of authentication but not the others so like whether you're using a password versus whether you use a token are handled by different Services which is a really strange way of doing things I'm sure it's historical reasons ultimately but what happens then if you applicate with a token so you'll see at the bottom I send the X5 xf5 off token equals blah blah blah um if you're thinking with a token the reverse proxy sees a token and says I only had I don't know how to tokens that's not my thing I'm gonna forward this onto the back end so when the back end receives it it goes is there a token yes okay I'm gonna get
this token and if it's wrong I push back if it's right I accept it sort of simple the back end does the off the second pass authentication there's more than two there's like three or four different paths it's just ludicrous but the second way is if you say using password as an authorization header if the proxy sees using password the proxy goes oh this is my job I should validate these and they use a pen module so it uses the Linux authentication mechanisms to validate the two same password by itself and if they're correct it removes the Usain password and then forwards at the back end in the back end receives something with no authentication it goes
oh this must be already authenticated and accepts it which makes no sense but that's how it's done so if the back end gets something with no token and no authentication it accepts it as valid which that's bad so it turns out and I didn't know this this is this was new to me there is an HTTP header called connection which I was aware of which usually has the values of keep alive or close keep alive means keep the connection open and close means don't but turns out there's a third value for it which basically says a list of headers the name of the header to be removed so you can tell a proxy to remove a
header while proxying so now what you have is the same scenario except now you send the X5 off token as a connection header the uh the reverse proxy gets this authentication it says is there a token yes there is so I'm going to forward this step back end then approaching his mod proxy says oh hey I'm supposed to remove this token so remove the token and it forwards it and then you win the back end things are authenticated and there's a endpoint that you can't really see probably but it's called TM slash utilitarsh bash bash bash which takes the command to run so you guys run ID and it tells you root so this is like remote route just by
removing a header and I thought that's a pretty cool vulnerability to like learn from because like this whole connection header thing I had no idea I spent like a week trying to find the actual core issue of this vulnerability and couldn't figure out why it worked until I read the Horizon 3 Zone who discloses it until they write Horizon 3's exposure and they mentioned the connection header and I was like oh today I learned so I made a challenge for B-side San Francisco 2022 which was two months ago give or take um called refreshing and I posted a source to all these things if you want to see these challenges we open source all of our
B-side challenges so you're absolutely welcome to see how we wrote them but um basically I wrote a web application firewall reverse proxy that if I saw it if I saw Quarry string with any illegal any weird characters it was at a security header and say this is a dangerous request and then on the actual server it would check for the header and say if this header is here alert alert alert this is bad so I made a so I made this Challenge and if the user can remove the header then they could uh they could run close they could uh pass reversal in this case do a very obvious controversial attack so basically the solution to it was just
to curl and then set that header and I thought that was a really cool way of teaching because I've never heard this before I think anyone who solved that challenge probably learned something because I mean some people I'm sure I know that but I sure didn't so Sutter's rfcs have weird edge cases I think Brandon's really good for that he'll he'll dig into like file formats like the zip or raw format or something and look for like weird ways of hiding data so it's like it's a cool type of challenge to like look at specs and make a challenge based on them so that's the first issue I want to talk about um the second one and that's okay by three
for the price of one thing and I do want to do these ones live-ish um I have screenshots if they don't work but I could I could go test a little bit live so this is where holiday hack challenge 2020 which me and Daniel worked on and this was our two polling Birds you see there's a bird that's calling cell phone um and I can confirm owning a bird they love being on my head so the artist it was a good rendition of what burden would do so basically if you haven't played holy hack challenge it's like a game you hop around this virtual world there's talks there's music there's this is a whole game which my old company counter heck
Adele can confirm they put so much time every money into making this free game just because our boss Ed just loves the Christmas challenges and it's really really cool that we do this for the community like I'm I'm a very cynical person who comes to advertising and I think this is a super cool thing that does hands does it doesn't have to but anyway uh one of the things was to open the door of a room and we have our called terminal challenges in this game and the terminal challenges will give you like a little console like this and the consoles will let you run commands and do stuff and this is like a legitimate URL you could use this later
if you do use it there's a username parameter that you should change to something else because somebody else uses the same username it'll kick you out which is kind of funny that's Daniel's Fault by the way um anyway you're given this terminal one saying like please reverse engineer this encryption to open the door now something I believe strongly in is that reversing should be easy as easy as possible and often it means taking the dumbest thing that might work so the three different challenges the first one is the door in another lesson for making CTS is pins so like I don't just give a challenge I do you look at a screen it wants a password you roll your eyes the
passwords probably start right in the binary give those kind of hints to people I think are very valuable because you don't want people floundering them like doing guesses so if you're into the wrong thing it's just gonna time out Ctrl c yeah so if you just run strings on door typing is hard if you run strings on door you get a bunch of strings and one of them is the password like I could use a guess for the path password yep the password is open the door so it's a very simple challenge but you wouldn't believe how many times during an actual assessment of reallocation that that's worked where I've just run like strings in the binary and got to
the password a private key something other it's something that everyone should try like if you're gonna reverse a binary if you just take out my binary or an exe file does if you run the Linux Strings program on it you might just find something and maybe you don't you might get interesting information I do I think strings L is helpful to get less junk n sorry I know how to do this I'm a professional that just gives you only longer strings and like seeing what libraries are important stuff like that is really valuable I should also mention I can't talk in detail about the source of these ones because these are from like contests but like if you were to Google these
things you would realize this is written rust and knowing this written rust does like tell you things about the application I think the more interesting one of these was the lights let me go into lab folder because I agree right in here so if you were in the lights binary it says you wonder how to turn the lights on if only had some kind of hint that it says config file loaded so and select file is decrypted and that's kind of the big hint is that there's a config file and this was a very very close surrogate of a vulnerability I actually found in some customer software so if you look at the config file
it's got some fields are encrypted and prefixed with e dollar sign and some that aren't you'll notice when you run the program it says welcome back elf technician so it reads the config file and it writes the terminal this one I'm going to edit it and just replace L technician with the password to do I told you I'm an expert I know I know what I'm doing all right and then run it again I messed up there we go so now this is welcome back computer turn lights on now this was like an oddly common thing I found in local applications that have encrypted config files is that it's very common for config files to have some
plain text and some encrypted fields and there's been several times where I've just swapped the fields so we decrypt something and then shows it to me usually it's a name it could be other things this actually worked on multiple different pen tests I've done which is kind of kind of cool the third one's a bit too complicated to actually like do live but I do have slides so this was the first one second one okay so I want so this one was based on a point of sale uh term uh desktop application that I was working on a long long time ago and this application was password protected but I could view the file but
the file was encrypted and It Was Written in Visual Basic I believe so I really didn't want to like reverse engineer it and figure out how to encrypt the file so instead I uh we mess with it I forget how it came out but you're interested to leave the config file and when I delete the config file it prompted me and I can actually show that what that looks like so I'll just Catholic a big file just so you see what it looks like so it's got an encrypted password in it just like before if I remove the vending machines.json file and run vending machines it would config files missing please create a new one please enter the name
wrong please send the password password doesn't matter and then if you look at the fake file now remove it wrong password doesn't matter it doesn't matter it's not remove it this time if you can it it encrypts the new values and what we turned out is that if I encrypted a whole bunch of A's a whole bunch of B's a whole bunch of C's Etc it would eventually uh have patterns so if you look at encrypting a whole bunch of A's and this is very very similar to real vulnerability and we get 9V T blah blah 9bt every eight or so character is it would repeat and then if I encrypt another string like say all B's
it would be eight different characters but it was still repeat if I encrypted like 16 a 16 B's or so you would see the first half sustainment the second half difference so I do always do my rent to like some sort of a weird crypto thing and I asked Brandon and said like what am I looking at and he said it's a poly alphabetic substitution Cipher what that actually means is like I could build a lookup table I can try like I could do eight A's eight B's eight C's eight D's Etc figure out what they encrypt to and then build a lookup table that would just go backwards and like there's a much easier way to do
that but that was the hard way and it worked the problem is this is a GUI app I was working on decided to do each one by hand and like get it pop-up box and it was brutally slow but I was able to encrypt a whole config file using that so that was pretty cool so I really wanted to like Implement these things as CTF challenges because like I read these in the real world and I thought they were really cool and wanted to like show them off crypto attacks can be really easy to implement in a CTF challenge because what encrypt is doing is very obvious it's keeping data confidential or it's keeping data
um it's keeping Integrity of data so like attacker can change your attacker can read it kind of thing the problem with crypto challenges is often hard to make them interesting so I think making it kind of like a game really kind of interesting but it's often kind of hard to make these fun but I think these ones were interesting to like figure out the other problem is that sometimes these are two they seem too dumb like people look at our CTF and go no one would ever actually do this when you got it from a real piece of software so next I want to talk about this one's interesting because this was a vulnerability in a diable 2 server
and I want to say 2000 6 2005 when I was quite a bit younger um a guy I know at the time his name was evil cheese living in the UK basically spent a summary versus using Diablo 2 server and finding duplication bugs and back in those days if you could duplicate the item like a stone Jordan which if you ever played this game you probably recognize you can make like 10 20 of selling one these days you can make apparently 35 cents so that's you know economy but basically he found a bug that he exploited and do full of items and made a bunch of money and then it got fixed but I could not find any information I
actually like I found on web on the on the archive I found someone talking about a similar dupe by the same guy but I cannot find the Duke that he told me about as possible nobody's ever talked about it which is fine it's also possible I completely forget the details I get it completely wrong because this is from a long time ago but I think I got this reasonably close to accurate so basically the way Diablo 2 worked was on the right you have the equipment screen the equipment is um in an array basically your helmet I'm making this up a little bit but your helmet might be one your left weapon might be two your
armors three your ms4 it doesn't matter what's interesting though is like when you sell something it would sell from a certain position so you sell your hat it would say a muscle item number one if you're selling your mace number two and so on the thing is there's this weird weird index zero slots that was used as a temporary buffer or so my memory kills me where it would copy the item to that slot and then sell it but there's nothing stopping you from selling directly out of slot zero so what you could do is sell item zero buy it back sell it buy it back sell buyback and get multiple copies the same item
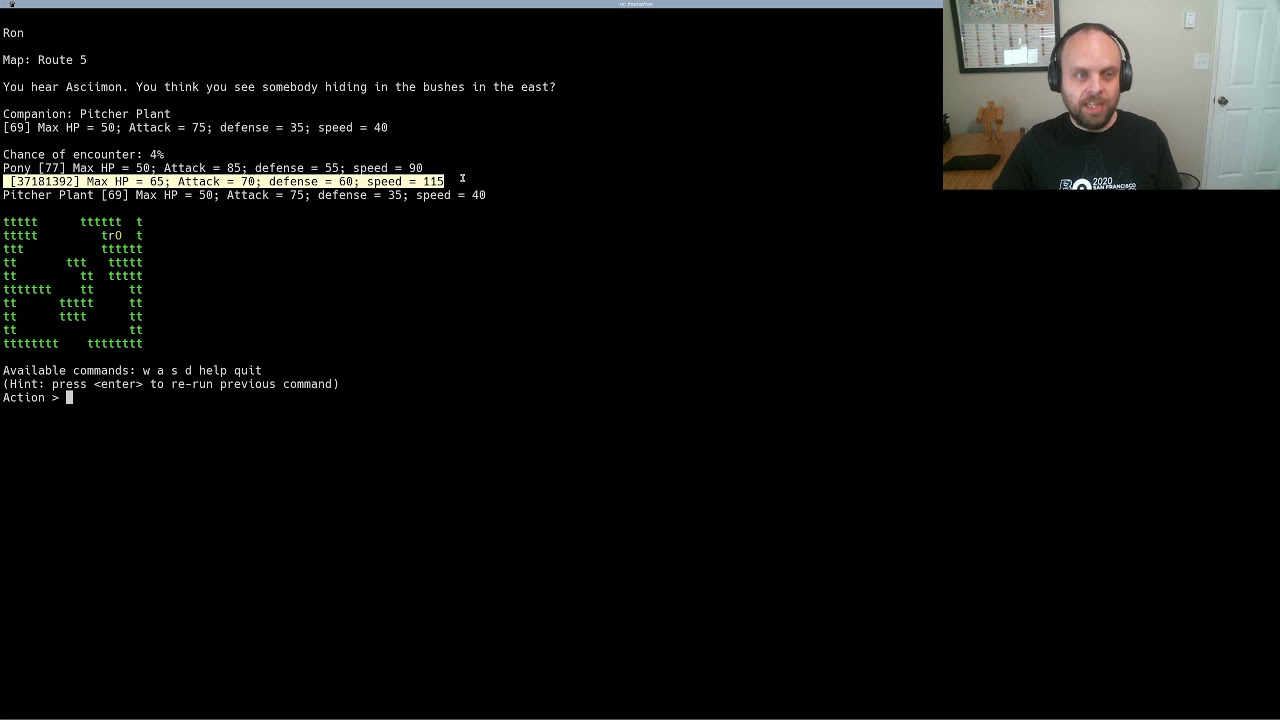
and like this is my memory of how the bug worked and maybe it's wrong but if that's right it's an interesting bug several challenges based on that called beast fight bees being like BS above like Diablo it's my pun you'll notice that the refreshing challenge was the F5 bug B's fights at Diablo bug I I make funny names so this one I actually have handy and I don't know if it's gonna work out that well but I do have screenshots if it doesn't but this is a game I wrote I've edited the source code bit to make this like easier to show off but it was like it was like a little text-based Adventure game you would like
uh netcat to a port it will give you all this stuff um it has commands you want help when I was when I was young these games are all the rage you know adventure and Zork and all that stuff but basically the way the bug actually worked and I'll show you the code for it in a bit you have an inventory so I have blueprints grass Shield pictures of cats I have like 50 things that you can have and I spent a lot of time making a very simple challenge but if you look at your inventory so you remember this um I have a grass sealed so I can equip the glass Shield like so and now I've got your Garcia
equipped okay I need equip my shield by Shield and so on so I can make as many as I want but that's cool why do we care and the thing I should mentioned first was like There's different areas in the game there's a street for example so I can move to the street and then from the street I can go to convenience store move one they used to be like right in the counters I turned those off just so we went the have to deal with it so you're at the convenience store you can buy a thing called flag.txt for a lot of money more money they would ever hope they have if you actually play the
game which is not true because I hacked it to have lots of money so I can show you that but that's besides the point what you can basically do is unequip your Shield and you come Shield then sell the item I'll just sell one sell one and so on so it's really simple you just like on your cup sale on your cup sale on your cup sale on your cup sale and you make tons of money game money not real life money in this case and then you get it's like say when you buy the flag um there's a command to describe things I forget what it is because yeah it's hard inventory describe describe number four
and then we'll give you the description of like so like it's a simple enough challenge but to me it kind of like captured the same sort of thing that this vulnerability had um this is gonna be yeah you've seen that already so this is the actual code for it and the source code is as usual linked so you could just look at the source code yourself if you want but um basically and this is a vulnerability type that I've seen a lot in real software where it checks if something is null says if not weapon it does something but then when you equip it it doesn't set it all it sets if like the false it's really common when people
store data in ways that weren't thought out well enough to like use two different pieces of unrelated data like whether it's knowledge equipped I mix them up that's kind of a state machine problem since I think I've seen lots and I thought I'd invented and it made a cool challenge you've seen all these screenshots already you've seen all that yeah so like it kind of honors this bug that I sort of remember from being a kid which I thought was really cool because like a cool person in my mind disclose it to me and now I'm telling all of you about it but it doesn't matter because this is like 20 years ago so next I want to talk about
this was a bug called we gave it a name it's called WebEx web exec so me and my former co-worker Jeffrey Junkin who's not here but he should be by me Daniel and Jeff worked together for quite a long time we were doing a pen test at a client site and what they asked us for was here's our secure laptop image can you get system on it and we said we could try so we spent some time on it and we eventually figured out that there's there's a Windows service that can be overwritten and it was Cisco WebEx and you can override it with arbitrary exe file because their permissions were bad and then start the
service as a user and get a system that was a nice easy vulnerability to exploit everything but the customer was using a weightlifting software so we just replaced the exe file it didn't work it would flag it as a uh most as a changed file and tell us it wouldn't load so that sucks how do we make this work so like at the client site I was like I wonder what this WebEx updated service is that's a strange one so I like I run strings on it you know I said earlier run strings on things I saw that it ran like create process as user which means it funds other processes and like that's interesting what's what's
this one and it turns out it's fun whatever you tell to so if you just start the service normally um SC that's Windows service control manager SE start WebEx service and you set the fourth parameter to ndxe file and the second parameter just software update it would just run that thing as system just like okay you want to run kelp we'll run kelp it's basically suited with no password excuse me I don't know why you work like that but it worked and it worked great so we were able to like run run a program as root anything we wanted or as system anything we wanted and that gave the ability to run like I'm interpreter payload or whatever it
was something would have gone uncut and because of how I read it it wasn't caught by whitelisting so that was really neat so you're able to like do that actually I think we use it to run Powershell and then Powershell around our code something like that I don't remember so like we report to the customer and said like can we like tell people about this and they said sure that's fine we don't care so we got permission so we went home and we we wrote a report for the customer and we sent it and we were documenting this vulnerability when Jeff says can't you access the service manager remotely so I'm like huh so then I read
SC backsized backslash my P address and then and then like start WebEx service sure enough it worked um suddenly we had like an authenticated sort of remote vulnerability it was really cool we gave a name because of the first vulnerability we found so we call it web exec yeah like WebEx but exec and like we did a pretty detailed blog about it I linked everything like I said because I think it's you know lots of things to read afterwards this is on my blog so like I wrote that I did like a high level write up it's all disclosure thing it's what I do now for a living but this is like doing it as a pandester as like we found the
thing on a engagement so we said it to Cisco they fixed it they sent me the fix I said this fix doesn't work as can you bypassed they published it we bypassed it they fixed it again blah blah it eventually got fixed right on like the third try so that was it uh we also wrote a message module for it and this is like my first ever met play module before I worked for Rapid seven we just recently published our first post worker representative essay module so basically runs you get a username password and it runs code a little bit like SMB um exact or whatever it's called My Brain just turned off but basically like
LPS exact that's the one it's only p is exactly except not um so at the core the whole problem here was bad Windows service permissions I mean badly design software yeah but bad service permissions as well so arbitrary users shouldn't be able to start service locally or remotely only system should start the service so I was like hang on I can wear a bad Window Service so I wrote that window service I did not link this because we never deployed it the readme says it says tricky to deploy run this manually after an error blah blah blah that was not good so we tried to get the staple and thankfully in testing Windows service manager really doesn't
like being a CTF Target you have to give people using a password for the Windows machine they have to not abuse the Usain password um it's really easy adopted by accident it's impossible to debug errors sometimes Windows service manager says like ah so like if you get really difficult and thankfully we never deployed it we did make a similar challenge for networks I think Daniel actually got to work but it's our lady of level that only like one person per game gets to it so that it kind of works for that but it never worked for us so oh that's a really cool service but it just didn't work so like it turns out some platforms suck
for ctfs like Windows SMB stuff is really really bad it's easy to do now service it it's easy to do like break things in the cloud stuff has similar problems if you're hosting on like if you're relying on cloud-based challenges which we do for b-sides um it can be really tricky because the Google Amazon whoever might detect ivity and break your service also it's really easy to like mess up configurations and like blah blah blah see ya more balance so like I obviously started with bell knit as like my my target I think I have two or three more bones and I have 22 minutes so I think we're doing pretty good so this goes back again to like 1999
2000 and this is when I was first learning how to do like versus engineering hacking I I joined like a group called uh Vol Legends VL who like I learned a lot of stuff from as like like game hacking they wrote a bunch of like cheats for Starcraft that they kept private and they could do a lot of cool stuff like stack buildings and Crush buildings and like they wrote AIS that would like make the units do things it's all really cool stuff and I really want to learn as like a 18 year old so when you open up Starcraft and click on Battle Nets a bunch of stuff happens um it connects to balance servers it it
says like hey I'm I'm from this local from this country I'm running this version um it does a bunch of stuff like that the first thing it doesn't major though it'll check the the um the main program files the exe file and the dll files to make sure I haven't been tampered with and we'll talk about that that's what this is based on a bit of validation product key and make sure it's not used it does a bunch of weird maths that I bet you haven't looked at it now would make more sense back then I didn't understand it we call it decoding the CD key I don't know what does but I bet you I can figure out now
and then there's a password hash the password hashing we call broken Shaw button because of Shaw one but not they made mistakes implementing it so like I personally reversed all these things as like a brand new person and I learned a lot about it but I wrote like some of my old docs and other Docs that you can take a look at if you want but the cool part was the version check it was called check revision basically when you logged in you would send the battle that like hey I'd like to log in please I'm from this country blah blah it would say sure we're gonna send you a dll file like a literal
window dealer file that we want you to loaded memory and then execute so you would just download the L file over plain text load the memory and execute it that's terrible now but that's how we how we've done it like 1997. so the deal file will get a formula that was hard coded and it would always change like each time you do this it'll be different but the formula would look like this the first lines the second one is more realistic but the first line is a demonstration a equals five b equals 10 equals fifteen and then a equals a plus s blah blah it would send you that formula and I was like what's this doing like I had no idea
and like what I learned from reversing and from like just testing was it would take each bite in the main dll files and the XE file set s to that byte and then run this formula so take whatever a was starting at five and add s to it and then do all this math it would do that for every byte in the file first by second by Third byte four byte in the files on the operating system and based on what you sent it it would know what version you're on and be able to send you patches or whatever so we reverse that that that's all out there it's easy to find but sometimes I
forget when like 2005 they changed it they changed their thing called lockdown and I reverse all of lockdown and something else I know did too and I can't find any of it running a sock I have a Wiki this is my Wiki right here oops can I click on things this is my Wiki I have a bunch of links all 404 I have uh source code it has it's not implemented um RJ who's a little friend of mine said we fully intend to update this in 2007 so like all the work I did this is completely lost to the void I did find one source that talked about it which is um a white paper style but it's a guy I
know called skywing he works unless I take to work at Microsoft that was a long time ago but he kind of documented this whole thing and it's really interesting but all the work I did is just gone I know you happen to it it's really sad like I wish I've been on GitHub or something but in 2007 didn't exist it's not really sad that I couldn't find this to show off but what lockdown did that was different was instead of fingerprinting the files on disk you know fingerprinted files in memory and we use a bunch of anti-debugging tricks to make it harder so the nice thing about doing it in memory is that when you check something memory
uh debug breakpoints and things like that will change the checksum so it's a much more complicated thing to actually bypass several challenge based on that called secure asset manager uh secure asset managers from beside in San Francisco 2021 as usual the source is linked basically you can't go a service it sends you a string that's not unlike that that the challenge thing you saw you do what checks out my memory based on that and then send the checks on back so it does the exact same thing um yeah debugging breakpoints stuff like that will change the response that makes it really hard a lot of people think they got it solved and it doesn't work
it turns out because they were using the bugger and it broke so yeah I think I implemented all the stuff I found tricky about reversing it without anything that was actually the code that was the first thing I reversed and I hacked and I really want to shadow people and I've done the same challenge in like three or four different iterations where I try to do like the challenge I remember having with this and then doing it again so like I thought it was really cool I learned from this I want others too as well so this is the last vulnerability and it's by far my favorite one so you probably heard Pokemon I think
Brian's playing it as we speak and there was a vulnerability in Pokemon Red back in the old days and it was called the old man glitch and the way it worked was you would go to a cutscene where the old man the character in the game would um show you how to work a Pokeball which you throw at things is minor setting I really play these and then he would with he would just wander off to a place I think civilian island or something and he would go you go waiting like on the right there and then you would run to a Pokemon that doesn't exist missing though or others but what's going on here
oh this was an old old issue that like everyone can play Pokemon on Game Boy I knew about and it's probably old man glitch so basically happening because when you talk to the old man your name like if I name my character Ron or whatever your name is replaced with old man temporarily so they can like show you how to play the problem is this is this is from like when's Game Boy like 1995 I don't know it's in the 90s anyway and it didn't start your name somewhere because there's no like Heap there's no way like temporary store your memory so it would copy your name to someone that's not currently being used which
was the encounter data table which means that next time you have an encounter if a table is never reset it would just have an encounter based on your name rather than what you're supposed to and as a result you can have all kinds of broken encounters uh you could based on your name you could change the level the type of Pokemon the IVs and EVs and uh Pokey things Brandon's cringing about my poke knowledge uh Cinnabar Island not Cerulean so yeah basically it stores it stores your name in 800 data so basically so whatever's in memory this is the use after free ultimately is what is really known as um it copies anything memory and then
uses it for the wrong kind of thing so I'm in the game based on this on the left is the original Pokemon on the right is my map um there's an example putting way way way way way too much work to a challenge let's see if I can zoom this right Zoom so this is enough I made this is Google Docs so I basically made this map and I would export this to a CSV file and then load it into the game and it was really complicated but it actually worked really well so I could just design map in Google Docs that was neat it's like in like modify them out like if I put Patrice in like
with treason and if I make if I export this and Run the game it will have trees there now um so I made all this I also made um a list of Pokemons so this is the actual Pokemon names um sorry uh game freak if I'm battling copyrights but like Bulbasaur Ivysaur Venusaur Charmander I got all these from the wiki but then for copyright reasons and because for human reasons we changed them all my husband actually did all this work he changed like um Bulbasaur to plant frog and Venusaur to climb dinosaur and so on and so on and so on if you play Pokemon you know how much work you put into this it's 152
technically because of busy no and like he put so much work into that I put so much work in this map and then I celebrated a game that was vulnerable so here's what the game looks like when you actually play it I'm gonna be run the actual vulnerability a bit too hard to show off but I will show you the x24 in a bit so I'm gonna choose plan frog with my starter we have artwork wait a little better small it can also be fire lizard not to be confused as Char Charmeleon whatever I'm not Pokey guy there's also a small vulnerability in this which doesn't really matter where you can choose any Pokemon so you could do fire you could do
missing missing no I think dot which is just like this is an Easter egg this is not actually useful but you're getting missing though so once you start the game you get to walk around the game world um the goal of this game and it says it somewhere is if you can collect all 151 Pokemon which is in this list or see all 151 Pokemon then you'll get a flag basically it just occurred to me completely randomly that the professor is actually based on the Jack from b-sides uh Jack Daniel Professor Jack which is kind of funny I just said that's a joke but kind of works here we have the whole world you just have a
spreadsheet it's all all the names and all the locations and all the encounters are all done there's there's uh fights all the map of the fights is based on the actual Pokemon map like it's all way too much work according to this there's also um uh I forget what the command is there's hidden commands it's this really complicated game for reversing and for uh playing now the actual vulnerability in this let's see if I can find my slides uh talked about that talked about that oh yeah use that for free there we go so it's basically is it way too small I use after free in the uh capture thing or if you capture a uh
Pokemon and then free it you end up with a pointer to uninitialize memory and you could by using a game changer change your name to be put into memory which is like a weird Heap attack um the actual doesn't really matter I did a very detailed uh video about it which is linked right here but I also wrote an exploit for it that I can show off which I this is a one second Brew of delay but you can see how it wanders around it's gonna take forever to do anything let's go 0.3 seconds so it I also used to hit those hidden teleport commands um it knows how to do fights it knows how to do all this all right like I said
I spent a lot of time on this everything is doing this for a reason that's a name changer I'm not gonna make you watch this in that speed I think 0.0 for was what I was gonna test it basically this just it uses the encounter table vulnerability to use your name to overwrite the encounter table and be able to encounter things you should be able to counter basically um you'll see that the encounter table has high as an encounter which is not valid in addition to the uh other names it probably won't finish my time my Talk's done but it will eventually log all 151 Pokemons and then win the game um yeah so this is not identical to
vulnerability but I think it captures the feeling like I think the whole like using your name use after free all those kinds of things are kind of captured and like this is by far the intelligence I'm most proud of because I put tons of work into it but like there's a lot of Futurama similar to or something like that similar to people legally sing from that use a lot you know still not to say legally in my talk so similar to what technique is taking from is similar to a legalisting from similar typically existing from but anyway so that's that vulnerability and that's kind of the uh the last part of my talk um I said there's one side that's a
conclusion because I felt like if I said nothing else it would be kind of too soon basically there's there's some bugs that we find that are very teachable moments um the F5 vulnerability where I learned about headers and stuff like that are very well teachable moments some bugs you find that you can't talk about because they're in customer stuff but you do want to talk about you can often find ways to get around that and do like challenges based on those um some bugs are too hard to implement like I wasn't going to implemented Diablo 2 server but I could make a server that that behave like the able to server and some burgers some bugs just
don't work we talked about WebEx that's pretty much it um there's a tiny around the bottom there where you can get this these slides um the QR code will take you there I promise um my reference haven't worked at hackerkb.com I seriously think that Dr be the coolest thing I've ever worked on I get to just write detailed stuff about vulnerabilities and my co-workers can confirm this we just like spend days researching a vulnerability and writing about it I think it's really cool my blog which I mostly released for ctfs now and my email addresses so I don't know when I have to be out of here but I might have a couple minutes for questions I'm totally have two
minutes anyone wants to know how the uh oh we're at the number 32 so this will never finish 33. thanks everyone coming and have a good rest of your biggest