Craig Williams - Ransomware Evolved

Show original YouTube description
Show transcript [en]
hello all right can you guys hear me okay so I guess I'll just dive right in here I don't even know what that is but that's sketchy as [ __ ] so my name is Craig Williams I run the talus outreach team I've been doing computer security for a bit now and what I'm here to talk to you today about is ransomware I know very few of you have seen ransomware heard of it so I've got a few intro slides just to cover the topic very quickly oh yeah first off to give you an idea of what Tallis's so a lot of people think talus was like an acquisition that Cisco made the reality was cisco effectively had
three separate threat research teams they had the iron ports a cop's team the cisco track team and the source fire VRT you know effectively all we did was just shove everybody underneath the source fire VR T's management team you know for those of you have been in the security business for a long time you know you seen layoffs and stuff happens and that's always unfortunate but in our case that really worked out well because each team had its own individual goal right the IronPort team obviously was web and email the source fire team was IPs and the Cisco track team was just threat or e in it so it really worked out well we ended up with a giant organization with
even more capabilities than ever before I think right now we're like a 270 researchers and we're hiring in Europe that's what we're here give you an idea how much data we have we basically have more data than anyone else it's how we see things more quickly and so without that said I'll just dive right in so you know what's the big deal with ransomware why is this such a big threat you know think about how much money people made off a compromised user ten years ago you know what was a single account worth right maybe a couple of dollars and now if I compromised a single machine it's worth you know three hundred five hundred dollars if I ransom off an
entire hospital's database it's worth you know twenty thousand dollars if I ransom off say Sony Pictures database who knows what it would have been worth right so the reality is ransomware is basically the highest profit margin business right now for bad guys and as a result we're not only seeing more people move towards it we're seeing the adversaries get more and more efficient at it and that's basically what the talk is about today to look at what we're seeing what trends were seeing and some of the new things that were some I got a really high level I really have to ask this is anybody here not heard of ransomware okay great has anybody here been affected by ransomware
or have a direct family member who has I've got one honest person in the room so most people have been affected by ransomware connected with somebody it basically looks like this you know you end up doing something stupid you click on an email attachment you go to a website and maybe you turn off your ad blocker has anybody noticed the new fancy trends with the websites with the ad blockers where they say hey you know because we have a dirty ad stream and you're running an ad blocker you can now no longer view our website right like who's doing that now Forbes wired all the other websites remember when Forbes did it the very first day they did it they compromised a
researcher that's the reality we live in and so this happens to everyone even if you have savvy users it doesn't matter right you're gonna have somebody who forgets to patch a browser plug-in and you're gonna get compromised so how many people in here thought ransomware was new how many people in here thought ransomware had been around for the last two or three years alone so believe it or not ransomware dates back to 1986 the very first piece of ransomware was the Aged trojan written by a absolutely crazy guy if you want to read a really interesting thing on a go read his Wikipedia article the guy wrote like on the side of a bag like so-and-so is
attempting to murder me and then try to go through customs that like Heathrow and thought it was gonna be okay they ended up getting arrested and found criminally insane he didn't get charged but it was the first time it happened it was a really interesting story and well believe it or not his thing was he tried to sit to ransom the people on an AIDS mailing list like literal the disease AIDS so that he could donate the money to AIDS research yeah just a weird aside so back in 1989 that happened I was spread by diskette he actually mailed physical diskettes out to the mailing list and charted about 200 bucks a person now here was his problem back
then you had to actually physically mail money or do a wire transfer right now what's great about that you know easy easy to trace no problem right and so it never really caught on he had this great and innovative idea as a bad guy but he was you know crazy and it didn't work out now unfortunately with the advent of torn Bitcoin we had a unique new phenomena right now we had a way that not only could you deploy your ransomware but you could control it and you could also take payment and it was effectively untraceable right as soon as that happen that's when we started to see the influx of ransomware and we started to see new people move towards
it and people trying out new and innovative techniques to make the ransomware more and more effective I mean come on how many people in here have heard of a any company on the planet who wrote a crypto library without a bug right like it doesn't happen right and so this is where we see adventures in ransomware and the security industry I saw some other examples right you know these are some of the older ransomware probably everyone's heard of cryptolocker and crypto wall most people probably heard of locky now so one of the things I wanted to talk about I guess we'll leave this one up so think about the concept of ransomware for a second right like literally in the
physical world ransomware be the equivalent of you coming home you're part but it's been emptied there's a note on the door they said hey you know you go ahead and wire transfer me your you know send me like a couple hundred Bitcoin and I'll send you back all your furniture I promise you know it's it's gonna be sometime later but I'll get around to it right Bitcoin wallet ID like no one would fall for that that's insane so why do people pay the ransom for ransomware does anybody have any ideas think about back when this started to happen you know what did we see in the papers does anybody remember the New York Times article where the the poor victim hit
the Bitcoin exchange on the wrong day and didn't quite have enough Bitcoin but like the benevolent Robin Hood of the ransomware world went ahead and gave him their files back anyway story after story like that where people got their files back basically built this sense of trust and cryptolocker right and so what happened was we had these people trusting these ransomware it's basically thinking they were all trustworthy now the reality is if you're in the security industry you know that's not true not only are they not trustworthy intentionally but a lot of them are trust with just due to bugs and so regardless people still pay so a lot of times we see ransomware around a temporal
campaign this would probably be one of the primary vectors from ransomware right now the Windows 10 update campaign went out by email it actually looked I mean it looked pretty [ __ ] bad but everybody fell for it I'll be honest right like look at this you got utf-8 encoding errors all over the place they misspelled Microsoft like Jesus and then like they don't even get the right antivirus like how hard is it to look up Windows Defender for [ __ ] sake it would take two seconds lots of mistakes but anyhow they throw this ransomware together tens of thousands of people fall for this right and we're here at Cisco looking over email Corp it's just like WTF like what
are we supposed to do so if you ran this you'd immediately be hit with CTP Locker so now think about this right like with cryptolocker had a cryptolocker build their reputation years of paying the ransom right so with CTP Locker well that's different why would I trust it right and so CTP Locker has a free sample system you know kind of like a drug dealer I guess it's so if you click on this this little button it would list out your files and it would say okay I've got ten thousand your files you can have three here the three I've chosen to return to you and you get those files back proving the decryption process works because that's
the reality right at Cisco we've seen countless samples that pretend to be ransomware but they're not they just wipe your [ __ ] and are like hey give us some money like that's that's where we're headed right think about how much easier that is that right than functional encryption and decryption software you know as CS student could write it anyone can write it but this is how they prove that they're real of course if you load it up you know we detect it blah blah blah this is what the record does so this is the one I wanted to talk about that I found the most fascinating out of all the ransomware we've looked at all year
so we're stuck with this problem right like how do you know to cross the piece of ransomware and what a ransomware authors do about it and so this particular piece of ransomware what does it look like does anybody recognize this looks just like cryptolocker v2 right it's visually identical to the GUI you know talks about it being RSA encrypted it's a little bit different turns out it's the first piece of knockoff ransomware it's actually Tesla crypt I wanted to show you a demo let's hope it works and I don't knock the HDMI cable out since apparently it's kind of iffy can you guys see this rules can you guys see this or do I need a full screen
in but you in the back and I see hands can you see it you should have full screen it okay great so just to prove you know what this is so here's a my valuable data so my valuable data says pan's earnings are [ __ ] future bookings are down let's crush them so my secret plans since this is my personal VM I have pictures of my daughter on here right data that's very valuable to me like if this got stolen I might pay for it right there's my kid being a goofball right I better show you both of them so don't get in trouble there's my other kid in her Halloween outfit right if I
lost these my wife I would be in trouble especially with as much as I travel like what do you mean you lost all the baby pictures but let's say I'm not savvy right I get one of those emails one of those temporaly emails and it said hey you've been waiting around for Deadpool for a long time well you know what I've got a cut from the studio doesn't have all the special effects in but it's you know the new Deadpool - it's awesome if you install this codec you can watch it right now and I'm like sweet click on run me and I'll go watch me some Deadpool and of course the first I can
always think benign software doesn't generally delete the Installer Ida Pro is like the only other one so immediately this pops up now what jumps out at you what's unusual about this so the first thing is the tell-tale ransomware screen kind of the trifecta is you'll see the ransomware screen pop up you'll see the ransomware wallpaper pop up and then you'll see the handy dandy icon on the desktop pop up now what's great about this is they actually label it cryptolocker version 3 that's really abnormal most ransomware doesn't go hi I'm Bob's ransomware and so immediately our detection research team looked into this and we're like hey we've taken apart cryptolocker version two three and four
we've got like 80 page white papers on each one and this doesn't look anything like it you know like we did the diff we looked through the binary is completely took it apart there's like no code overlap it's like 10% which is like the Microsoft core libraries and so immediately we're like literally this is the first piece of knockoff ransomware they're impersonating cryptolocker right why build your reputation as a ransomware author when you can steal it right I mean if you're a thief steal it right why not yeah and so uh you know let's let's look here just to proof so if we look at my my super secret plans it's now you know high entropy garbage
probably encrypted and not compressed we could pop up in one of the JPEGs and if you guys know anything about JPEGs you'll notice the JPEG header is gone there's no tags there's no length values it's just garbage and again high entropy garbage which probably means it's not compressed it's blown away or randomized or encrypted not naturally you know when detection research took this apart the first thing they looked at was the encryption algorithm right cryptolocker like most I don't want to use the word successful but like most clever ransomware they don't use symmetric encryption right they use asymmetric encryption now what's the downside of asymmetric encryption you know you have to have a server that it can talk to to
do that exchange right so you have to be online so the test the crypto there's probably dude agreed I mean this isn't stupidity right they actually have functional symmetric encryption they're not idiots but probably dude agreed and then want to pop offline boxes they said hey let's make the algorithm symmetric when the ransomware screen pops up the user will they'll pay they'll plug into the internet and we can get the money now of course detection research like sees this and they start frothing at the mouth like what do you mean they use symmetric because what that means is the same key in memory as the key that can be used to decrypt the files and so
Cisco was the first company to release the Tesla crypt decrypter thanks windows go ahead let me run that you that great like it lets me run the malware with no warning but it's like whoa Tesla crib decrypter watch out so it's asking me if I'd like to terminate Tesla crypt like alright then what I'd like to delete The Dropper I don't know why I'm on you made that a separate box oh my god go ahead and decrypt the files but keep me the sample Thanks and then what I like to decrypt the files sure and did I want to get backup no way let's let's live live right and so what it's doing right now is it's
going through memory and extracting the key and it's going through the drive and looking for every single encrypted file now have you ever played it the first version of this it was way faster because it only did version 1 or sorry version 2 we now support all versions now we'll get to why in a second so you'll notice now some of my pictures have reappeared here's Katie eating her sandwich let's see if my secret plans have decrypted who would they have nobody tell anybody my secret plans and so I've effectively recovered all my data and I hadn't paid a single thing so the reason I showed you that is two reasons number one this is how the
security industry wins when we release this we were the very first company to release a decrypt of for Tesla crypt the second we did that no one had to pay ever again this post that we did for this file was the most popular blog post cisco has ever published it was more popular than the john chambers executive leadership handover when you google tesla crypt i think we're the number one hit still and so what happened was basically we drew first blood we pointed out like hey well these guys can write ransomware apparently they don't get crypto right like for whatever reason they're capable of writing good encryption decryption software but they clearly don't understand encryption algorithms and
they're clearly making poor choices and it was a pretty much the best thing ever immediately when we did that well they put out a new version about six to twelve months later Thank You Persky I think beat us to it Kapoor skee released a Decrypter kudos to them you know fight the good fight and then six to twelve months later their host another version an independent researcher released another decryption tool so effectively what we did over a period of about 18 to 24 months was watch them spend [ __ ] tons of time and money developing in this ransomware and immediately destroying their ability to profit from it right this is what it's all about this is what
the security issues about and this is what's important to tell us is that when we do these things we give back we release them open source so that people can extend it other people can add to it and together we can actually stop the bad guys right it's not about taking down one server it's not about blocking one sample it's about making it too expensive for the actors to continue their business model I mean think about how much money and revenue they spent developing this ransomware right that was a significant effort I mean think about how much money a company spends developing encryption and decryption software and we're talking hundreds of thousands of dollars and we just
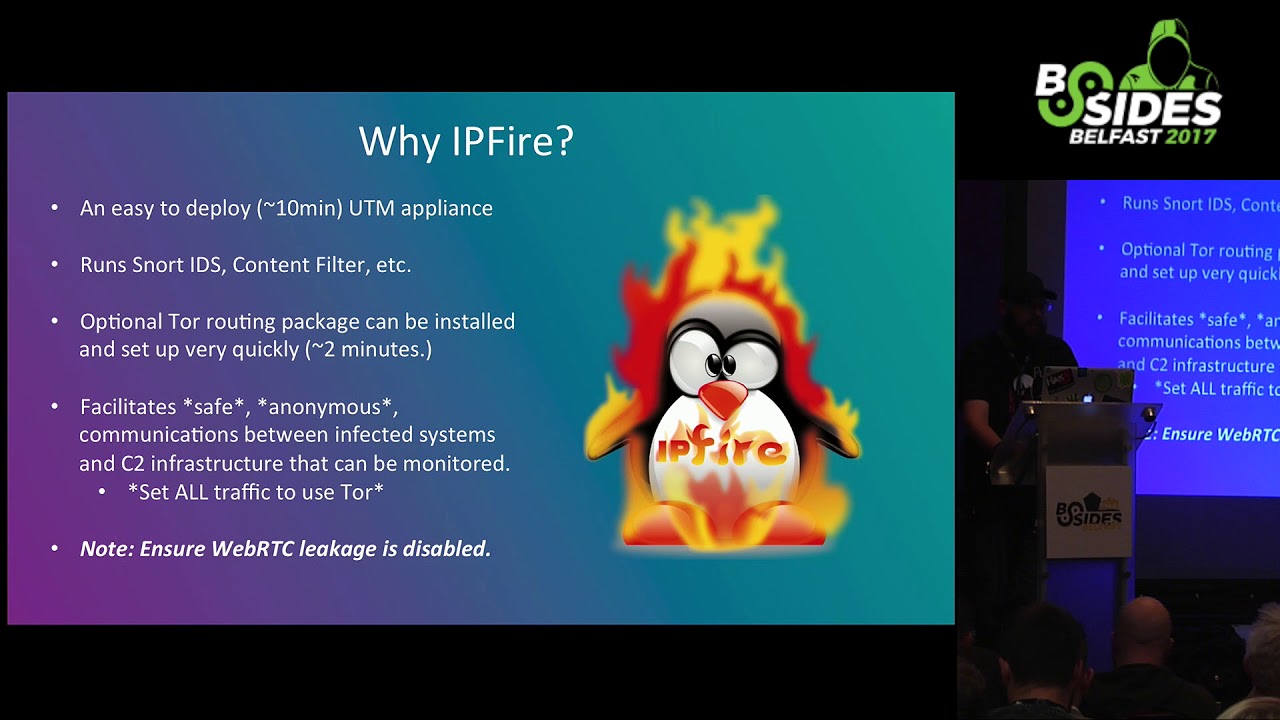
destroyed that for them and so that's that's really what we're all about it's housed and that's what we enjoy doing and so I wanted to walk you through Tesla trip to show you an example of how the industry winds together all right so with that said well what have we looked at as a primary vector so far email right everybody knows about email probably fewer people know about malbert izing has anybody in here heard of malvert izing before okay about two-thirds of the room so we'll give a quick high-level so malvert izing is basically taking advantage of the Internet's ad exchange to propagate malware the advantage with malbert izing is that unlike email the user doesn't
necessarily have to do anything stupid you can be hit by malvert izing by simply going to a major news website at Cisco we've been looking at malvert izing for years and literally I'm completely serious when I tell you this there is no clean Ad Exchange on the Internet there is not one there are some that are better Google for example is very good but it is not completely clean if you view a website that has ads you're at risk from Albert izing so to dive right in you know a lot of people think the internet ad agencies are all one thing they're not there are different companies they're different components and they all you know how to put this
perspective my vegan tech lead made this slide and I always include because I like it the fact that he's a vegan this hate for the ad agencies are like eat a cow I just enjoy the irony but this is what it really looks like you know when you go to a website like cnn.com you're actually connecting to hundreds of sites this is a completely benign graph by the way this is nothing sneaky this is the way it's supposed to work has anybody heard of Outbrain down here does anybody remember the attack the Syrian electronic army made against the news websites a few years ago remember they hacked a little little-known website called Outbrain their control panel so our brain is the
technology that says hey you've read this article would you like to read this other article now luckily for us the Syrian electronic army was only using it to push propaganda but they easily could have used it to push malvert izing and so it's things like that that attackers take advantage of and we're talking anything from like compromising one of these servers to paying for a legitimate ad and having a redirect embedded in the ad you know anything and everything so to simplify it a little bit this is basically what it looks like you'll have a user go to the website the website will redirect you to an ad server and that ad server may direct you to a
benign ad right that's your great day you went to a web site you saw the web site you saw your ad they got one one thousandth of a penny everybody wins right now unfortunately some days it doesn't work like that some days you go to the web site you get redirected the ad server you go to a partner and that partner unfortunately links you to a server that's got a malicious link on it and then you go to an exploit kit landing page this is probably the highest risk to users on the internet that we can see right now we're seeing about 20 billion threats a day blocked and malvert izing is by far our number
one so let me give you a real world example of this we're gonna talk about the angler exploit kit has anybody in here heard of the angler exploit kit before it's about half so the angular exploit kit is about the highest profit exploit kit we've ever seen it caught our attention and I guess it would be like 2014 so for those of you don't know probably the most well-known exploit kit was a ponch's exploit kit you know the black hole exploit kit was very well known and widespread and it was used worldwide what happened was basically it was too famous for its own good right when everyone's using this exploit kid and it's making you know tens of
thousands of dollars every week of course it pops up as number one in law enforcement radar and so international law enforcement came together and said enough zijn uh fanned they all decided to get together and go after this guy they got him he was actually finally sentenced a couple months ago to several years in prison he'd sat in prison for years awaiting sentencing and so the problem was at the time people thought that was great right it sounds great like catch the bad guy put him away but what happens when you have a demand that's hundreds of thousands of dollars and all of a sudden the supply goes down overnight do you think people just say hey I don't want
to make that money let's leave it on the table so immediately overnight we saw dozens of new exploit kits surface things like nuclear and neutrino angler all vying to be that number one and so you know we watched it for a little bit and I think in the annual security report last year we basically declared angler the winner of the exploit kid arms race it was able to not only out-innovate the competition but what other people had a great idea they would steal that idea incorporate it as their own you know and you know like malware and like we saw a Tesla crypt there's no honor among thieves there's no patents for good ideas for
malware you know they think of it they'll move to it I give you a solid example of that would be when the Fiesta exploit kit used Silverlight as an attack vector for the first time until that point no exploit kid had ever used Silverlight as an attack vector well immediately the angler authors saw that and were like wow they basically found an antivirus bypass I think we'll use that too and so they started using it within a couple of days so we started looking at angler and we take a look at limestone networks in Dallas Texas because it's geographically close to where my team resides and it was hosting you know slightly over 50% now you'll
notice that's near in Germany was around 50% we had some smaller spikes until about December of last year and Engler was very very tightly controlled as the browned January of this year got a little bit looser and then went dark and we'll talk about that in a second but to give you an idea of why this one was so interesting has anybody not heard a virus total so virus total is basically the antivirus clearinghouse for the industry it was a company called his systems at Google bot like in 2008 or 9 effectively every antivirus company in the industry uses it when you upload a file I don't get scanned by I think it's like 40 or 50
antivirus engines and it'll tell you what they detected it as it's a really cool tool unfortunately when you upload angular samples virustotal doesn't detect it we had a detection rate of 6% and of that 6 percent most were detected by less than 10 engines which you know when there's 40 or 50 engines it's an appallingly low rate and the reason it was so low was because the samples are encrypted right if you've ever written like IPS signatures or claimed 80 signatures you know you need something to tag on well if it's been encrypted it's gonna look like super high entropy data and there's simply nothing there and so that's the reason it was so hard
to detect from a network perspective it also had several evasions they had things like dynamic dns domain shadowing that made it hard to detect if you've never heard of the main shadowing effectively what it is it's a technique of registering tens of thousands of subdomains using what we believe is fish credentials for domain registrar and so you know they're basically hijacking the reputation of the base registrar's domain and just you know having like a 26 character randomized subdomain and they rotate through tens of thousands of those every few minutes anybody guess why that's a problem just think about how simplistic web blocking technology works you know there's a lot of the really really cheaper stuff use multiple
detection engines know they just use a whitelist and a blacklist well if you use a whitelist and blacklist you can't easily rotate in and out tens of thousands of entries every two to five minutes you just overload the device they also used you know adversary own to everything so give an idea how this worked this is a real example they targeted things like this pretty frequently this is the Fergus Falls Journal if you went to the Fergus Falls journals and you were unfortunate enough to go to the obituaries section you'd be redirected to Sense and Sensibility which would quickly redirect you to an explicate landing page usually dropping cryptolocker version three does anybody realize how [ __ ] up
this is like why do you think they're targeting obituary pages what age group could they be targeting that use Internet Explorer and don't patch ever right they're targeting your parents the targeting my parents right these people have thought this through this isn't careless this is very precise every piece of angler is very carefully designed to not only compromise that specific age group in that group of users but to do so in a way that's very difficult to trace so to give you an idea of what they targeted these do still while they did still target a little bit of Silverlight for primarily flash and Internet Explorer if you didn't use Internet Explorer you didn't have to worry about angler but the thing
was if you saw the malvert Iseman and you were not running IE or you were not vulnerable you would never see the exploit so your antivirus engine would never say hey that sites bad and report it you'd simply never know it was there and the way that they did that was through a very very careful and deliberate architecture so when you went from the Fergus Falls Journal you would be redirected to what we called the proxy server which is effectively limestone networks now I want to be clear here limestone networks as a victim in this these accounts that were they were made for the hosting the boxes were all fraudulent they would come in overnight
they would make up some identities they would use stolen credit cards and they would get hundreds of machines and these weren't done in a row they were scattered out very cleverly so they were very difficult to detect and so for limestone not only are they losing time and the you know racking the boxes powering the boxes but they're also getting hit with tens of thousands of dollars of charge backs right as soon as the credit card company comes back and says hey these are stolen so limestone is very helpful the proxy server would then you know direct the user over to the exploit kit server almost always in the Netherlands over port anyone using SSL anybody know why
they like the Netherlands it's the same reason the Pirate Bay likes the Netherlands right they have very very strict data privacy laws you can't just go say hey that box is evil you should take it down that doesn't work if the exploit kit server interrogated the browser and found out that they were vulnerable it would then send down an exploit over a port 81 encrypted to the proxy server which would then feed it to the user exploiting them to the user and of course would look like limestone networks was attacking them and so if the user reported it and said hey this box is hosting malware well limestone networks would say oh thanks for telling
us well one racket immediately unfortunately there's a health monitoring server every 60 seconds the health monitoring server is pinging the proxy server saying are you up the second it's down you know just like cutting the head off a Hydra it would rotate in a new one which would then take over and so you have an effective downtime of 30 seconds for taking down a server that's intelligent architecture but also gather logs from the axe blicket server and wipe them every 24 hours anybody hazard a guess is why they would do that you know what's an IE exploit worth right these people by O'Day they use that a if they're not having success with their exploits well they're gonna
go take their money and they're gonna go invest a new exploit maybe they know today maybe they don't but if they're having stuff that doesn't work they've got at least rotate and of course you know the entire time there's yet another server the master server which is of course fetching the logs from all the Status servers keep in mind this is a collapsed 3d model there are hundreds of these hundreds of these dozens of these and dozens of these massive massive network so of course we partnered with our good buddies at level three they're the group that helped us with SSH psychos and some other research this is what it actually looked like so this is
the actual health check notice they're using the URL as a password you know nice randomized string if you didn't know that string of course you wouldn't be able to get the health check but if you knew it it would return 204 and you'd know immediately o2a four okay that means you're up and running and ready to pone users had another password down here to get the log files that would allow you to not only fetch the log files but call delete on the log files effectively covering your tracks and over here is a nice helpful redirection this one is to world scream in the Netherlands both streams really funny I called world stream and said hey you
know you're hosting the angular exploit kit you're compromising our users I blocked you from Cisco customers but you really need to take down that box they're like okay well you know Dutch privacy laws let me look into it and I'll call you back so the next day they called me and they said hey I just wanted to let you know we were able to contact the owner of that machine and they assured us that you were right it was compromised but they've actually resolved the issue and it's fine I mean well we're watching them continue to redirect users to exploit Kipling any pages so it's a problem with dealing with these different servers in different countries no I forgot to
mention this part was in the Netherlands this part was usually in Russia or the Ukraine a proxy servers are almost always in the United States anybody want to guess why that is makes it hard for law enforcement right they're intentionally spreading it out to make it more difficult so because we had all these log files and because we had all the data on it for the first time ever we were actually able to calculate out if you know the explicate continues to operate in the manner that we observed it well how much money are they making just from ransomware and so from a single proxy at limestone they would get 90,000 victims a day of those 90,000
victims ten percent would be served an exploit of that ten percent forty percent would be compromised 60 percent wouldn't maybe due to it being like a heap sprain it wasn't reliable maybe they had antivirus maybe it was just you know a bad day who knows of that forty percent 62 percent were delivered ransomware so 38 percent were delivered different malware more often than not but depth which is a click-fraud type malware that we believe the angular authors also wrote but that's another talk so just from the ransomware payload if you used the FTC's estimate of 2.9 percent people pay the ransom we low-balled the price of Bitcoin to 300 dollars it was around 500 I think it
collapsed a little bit though in the last major Bitcoin thing crashed and the number of redirection servers we saw there may approximately 34 million dollars off of ransomware just from the limestone networks portion now if you remember back at the beginning I showed you there was almost the equal portion of Hetzler so conservatively about sixty million dollars from ransomware remember there's 38% at each server that's click fraud but dead most likely so they're making significantly higher than sixty million dollars a year just off ransomware from this one exploit kid this is the problem we face so we dug into it a little bit further how many people in here have ever heard this statement that
ransomware does not affect Russian language users yeah it's a common fact that's really not common if you've read up any on their white papers they actually use undocumented windows API is to determine this and so you know we were doing this research we were able to tie a lot of stuff together so you know I mentioned the DEP earlier this is some of the hosting history and so we were able to tie the hosting history up adapt to the hosting of angular and yeah I forgot the important one and the the lurk Trojan this is the best clicker ever and so what happened was there was a Trojan called the lurk banking Trojan and I'm like most stuff it actually
focused on Russian and Ukrainian banks turns out that was not the best idea for them effectively but what happened was the people behind the the lurk banking Trojan were suddenly arrested well it's funny the second they were arrested several botnets disappeared including angler Droid X and locky largely disappeared now this isn't to say that anguish gone you know I want to make that very clear we're talking about something that's worth you know well over a hundred million dollars a year potentially if you include all its profit margins it's gonna come back somebody has that source code it's just a matter of when but it's great to think that right now it's actually dead due to
their carelessness now I wanted to talk to you real quick about the brand newest stuff we're seeing has anyone in here heard of the Sam Sam ransomware so okay not many people that's surprising so up until now all ransomware required a user to propagate right like we saw with the temporal base ransomware where they would take advantage of something like the Windows 10 update or they would take advantage of something like a movie or the Chilean earthquakes or the Ecuador earthquakes or whatever you know it required a person to click on that email attachment like malvert izing right it required a person to go to a website write it they didn't have to make a
mistake necessarily but they had to go to a website with an unpatched browser and they could be compromised with Sam Sam they actually changed that model now what's interesting about this is Sam Sam had the clever idea of using network vectors and I ransomware payload it was actually not that advanced Sam Sam used the off-the-shelf Jack's boss it's a pen testing tool kit for JBoss servers with a nine year old and a 7 year old CDE who has a nine year old web server facing the internet that hasn't been patched that's terrifying but it turns out millions and millions of people and so what happened was Sam Sann basically would scan the internet looking for these nine and seven year
old CVS and it would then attack them and it would use Jack's boss to install a backdoor once that backdoor was installed they would poke around for some unknown period of time and then install ransomware on various boxes on the network now it was interesting about this is throughout the entire ordeal they had a lot of really weird behaviors so not only were they using off-the-shelf payloads and backdoors which is really weird right because that makes it easy to detect but so they were doing things like this where they're selling like bundles of keys that's really weird up until now every piece of ransomware has been like you pay X dollars for a computer well Sam Sam decided to go for
like the Costco bundle model I don't know if that works over here is there like a Costco here you got you're gonna help me out or just shake your beard thing yeah so like basically they're saying if you buy all your keys at once I'll sell you 20 keys for the price of 15 that's bizarre as hell right like somebody who runs a network that has valuable data they don't want 7/8 of their data they need all their data they would pay for all their data it's just weird because they're not targeting people without deep pockets they're targeting you know mostly hospitals in America and Europe so that was weird the other thing that we noticed was that as the ransom went
on they increased the demand from one Bitcoin to one and a half Bitcoin per machine and then 2/3 Bitcoin per machine I think the Washington Post even had somebody saying for per machine so you know they're potentially losing for Bitcoin per machine times several machines per bundle that's thousands and thousands and thousands of dollars that's really weird for a ransomware to author to leave that amount of money on the table so with this led us to conclude is that basically they had no idea what this data was worth like they have no idea personally I think they were completely new to this right they didn't write their own payload they didn't write their own backdoor they don't have any
idea what they're doing from a monetary perspective it's just a mistake after mistake after mistake so it was interesting about this that regardless it was incredibly effective they didn't need a person right they could scan the internet they could find these vulnerable machines and install these backdoors and then at their leisure go back through and say hey is this network with ransoming and so the first time we saw this was in December of 2015 targeting the gaming industry in the United States and it was a very very limited attack right very very small number of victims and early 2016 we saw it explode and for whatever reason the attackers targeted the US healthcare industry now I think this may have been
like a psychological twist right like if you target one you know vector 1 vertical all at once well everyone in that vertical can kind of come forward and it's not that bad it's super hackers right no one can defend against super hackers despite the fact that they're using a 10 year old vulnerability what to make matters worse and what really bugged me about this was every single victim was like we've never been breached before this is the first time this has ever happened and I can assure you no data's leaked out we saw those press releases time and time again does anybody think that kind of thing is true when you have a 10 year old
vulnerability not very likely obviously I can't state anything solid one way or the other but of course you know being in Townsend with our mission as on our poster of pissing off the bad guys which sorry I'm now supposed to say forcing bad guys to innovate we worked with Cisco IR and Cisco IR had a customer who came forward and said hey I've heard of these Tallis guys please share our data with them so that they can do something to help us and we had a incredible discovery it turned out that the authors behind Sam Sam would take up to 74 days to actually install the ransomware yeah it's insane and so immediately we're like wait we
have 74 days to like save the victims you know that ass fire at the scanners and so we started scanning the entire Internet we found approximately 3.2 million vulnerable servers running on normal web ports all right so these are 3.2 million servers that are running nine Harrold web server code and seven year-old web server code these are not unimportant businesses these are embassies aerospace engineering companies schools hospitals these are businesses that you would expect to have better security postures the problem with this is I don't aggress too much but if you watch Rob Joyce's talk from usenix where he talks about how the NSA targets companies the entire point of his talk is the way that the NSA is so successful
is that they know the network better than the customer knows it this is exactly how Sam Sam worked they knew they'd found a ten year old servers pointed at the internet that the victim had no idea was there and so they then would compromise that server and use it to move laterally for like 70 days so of course we decided that's not going to happen we want to literally take the money out of the bad guys pocket and so we looked for servers that were already back doored because again Jack's boss is an off-the-shelf payload it's super easy to fingerprint and so on port 80 we found over two hundred and two thousand 173 we then of course we're like oh wait
what people ran on non-standard ports and we spent another 1,600 and so we basically took I don't know half of my team half of our interdiction team and said hey here's thousands of IPs find someone for every single one and fix it and so for about three weeks we did that and we literally took thousands of dollars out of the authors of Sam Sam's hands now this was the bigger problem as we started working with these victims we found out that for the first time ever it wasn't getting one actor off a machine the average number of actors on these machines were four there was one box that had over a hundred and eighty actors on it and keep in mind all
over the news we'd been hearing this has never happened before all your data is safe yeah I obviously we don't know one way or the other but we do know that it was incredibly disturbing there was a unbelievable amount of elementary school software that was targeted it's possible they were the next vertical so we worked with faut they'd actually developed the patch prior to a scanning and we're in the middle of deploying it so it was really advantageous for everybody involved but again you know my point here is that this wasn't super hacker this was some dude who just had an idea and decided why don't I take a well-known network vector off the shelf out of a tool
similar to something like Metasploit and just add a ransomware payload anybody could have done this and this was incredibly effective and the problem now is that the author has tens of thousands of dollars if not hundreds of thousands of dollars from all the hospitals that they hit and so when they come back they're going to actually have the funding to have hired proper developers similar to the authors behind angler and so I think it's something that the security industry as a whole needs to keep an eye on you know we definitely are so that's all I had to talk about today you guys want to follow along you can go to our website it's got all our
white papers they've given you like the 90 second overview of like the 80 page white paper we announced all our stuff on our Twitter any questions comments
all right well thanks for your time [Applause]