BSidesIA 2017 Track2: Want to break JavaScript and APIs in web apps? – Andrew Freeborn
Show transcript [en]
everybody on my Andy Freeborn acting all the things and today we're going to talk about breaking JavaScript and he is and without the new hotness so no we're not all about me now as you know just I to drop over up Gina pentester at Pacific and so a lot of pain cooking and a lot of dank memes much kind of one best for but also tested security and web apps and mobile apps and all kinds of security in both web app mobile testing and as well as a client and skated memories I love a different kind of CPU architectures and gain the dank memes you know current paper is a ebook Kermit so I kind of keeps it going and who
doesn't love that so today you know kind of a little bit of agenda I you know cut-up out the y at the top and kind of looking if we're going to talk about and why even motivations with this kind of talk and then tools to identify and I break the all the things not all the things but may thinks and then I'm going to take a break if we have tools to break stuff and we're going to do a demo so hopefully that works out but we'll see how that goes so why as you can see here on the picture there's a lot of colors here for JavaScript and basically and just within the corporate or even
small business environment yes of the Julian kinds of jQuery angular mustache that them you know like all the things you know work very well for a specific use case that business may use it for but how often are we evaluating that specific version of jQuery is saying oh we're on 1.6 we should really be on the next version for variety reasons the dumper says well I pots money time and say well because security we should so as you can see from the CD that our codes a ton of different varieties of JavaScript frameworks in use today and it's only going to get worse as you know the response cool new thing to play with and develop it and then using production
and trying to keep on top of that so as security people we need to make sure that we're aware of this new burgeoning format of incorporating different versions of javascript in the environment in production and how we're aware of these kind of frameworks and making sure that we know that you know we do our best to really be aware kind of that the ball rolling of being updating secure but really really no reason with a javascript is a problem because it's evil so the bane of Oliver Oh bane of our existence so you know really with what type of developers on assessments is an oz version of jQuery and mustache and they say why we
outdated let me state because security but really it's a problem that not only that we face in our organization but any kind of place where you find a highly deployed product you're going to have a lot of people looking putting miles on that and if that actor is trying to exploit that it just adds a fight that wants WordPress and how to happen or are they update and keep on top of their platform to make sure that they're secure and so commonly you're going to see you know always feel of lovis porn abilities we see all this version of jQuery it's not really a high you know high risk to the organization but scum a
low risk oh now we see a low-risk can say a the lab kind of information but again that's how low risk and OEM we see all these different of vulnerabilities well when we're seeing lots of different vulnerabilities somebody can be very clever and chain all those things and use all horn abilities to help make an exploitation so like an Airbnb here in this article you see that all these were low vulnerabilities but chained together this compromise air baby so yeah this businessman safe well it's a low-risk what's hit that wears cannot really wear too much about it though but it's not nothing Flores perform abilities you could become in a higher situation and be compromised so we should be aware
that yeah we can accept this risk but we need to make sure that we're aware that the more things we accept the more risk we're at and so not only are we seeing JavaScript use a lot we're also seeing HP is use a lot so that's great for a developer has great to have api is to have a lot of cross compatibility between platforms to share the data naturally what businesses want to do is consume and use and have it via readily available tell people to use and consume be you know invested in their platform so a common platform for you guys of you know it's currently start out to rest and so if I am saying
firmly management company or say I'm event company that uses we're blade management data I can get data from one vendors tool and then they're from another person's tool and then combine that these anarchy is but if yeah I is again our software and has their own challenges unfortunately with API is its kind of seeing as like a habit they the question as far as how do we make sure that each Isaac here and who is snapping it and making sure it is secure me would say it guys up I hope it works okay I hope it's secure but it's not rly amateur part of is a carrier scary testing methodology to make sure that we're just hammering that each time
because you're were kind of shaking down as possible a little hanging fruit and it different and that as much as possible to make sure we're giving you know our my biggest sure it's secure you through a third party or Charlie developed API and interest something enough the ol odds team they're working on a new 20 top 10 for 2017 as you can see for a pen is under protective ad is so now for first time we're seeing API is specifically called out as a problem that you know we need to make sure the top 10 problem that were just you know we're seeing the apartment we're not way testing very thoroughly so again making sure AP is or you know a thing that
we're going to test and break and manipulate and see if it you know behaves as it should and with the results that we want so the best way to do a little hacking is with chrome and really you know chrome and firefox developer tools are crazy awesome it was up look more about that and retired jas it's a platform as well and then note security and think again two great tools will cover in postman an API developer tool mostly and a vertebral venerable virtually you know purpose so you know well today's load centers in 45 years now and so he's in barfi know in this use case is still very valid and you know a vital part of anybody's tool a
tool set so again with chrome and firefox you know we come as we saw and brass talk that chrome has a large share of the market and so developers hobbies forget you know compatibility with chrome and firefox and sometimes the internet explorer sometimes but in with both firefox and with chrome they bundle in the baseline version of elephants and so these other tools are agree to have you know a lot of the bugging capabilities introspection wasting manipulate and resend and just basically wreak havoc with any website you know as a common use early to say i'll check them an email but the tests or either Bible tool is that if i'm on engagement or am at a client site this is a great
tool because it's not come come we saw as like a threat or a way to compromise website but you know as a kind of that hurdle of knowledge and acceptance of you know you see developer tools against them to make sure you know we're also doing our job and it's a lot of places available from google I'm sure Firefox's tool to walk through the tools and how they work and understand how you'd be debugging and respecting and I really get to know it to be you know a bad works will set and then why is it easy a test for a variety issues being quickly and use of death rules I can see headers I can see all kinds of
methods I can do a lot of different things and validate security and see if like the base that bare basics are being done like are we enabling cookies or reason ssl only so a lot mullet lalaine and fruit can quickly be identified without busting out verb or these are kind of tools I'm getting used to help we'll hang a fruit so just being with these tools themselves we accomplished a great deal of testing so what testing for example we have if we usually schools we can quickly see the source code for all these JavaScript files CSS and timers like that so developers are a lot of fun they'll leave comments don't do a lot of things that necessarily you
know don't worry impact the users experience but a lot of our tax was behind sorry sight jira ticket numbers or people's names or when it was change or what for mobility was addressed or comma doubt source code that doesn't you know you know I'll stick it out later but let over for whatever reason so I can see and the top part here we can see all the in the routes that this angular app is going to use or the model controller type of application all the routes so we can see you right there in the first one administration so we're going to stay up off the bat can see the administrative portal that you know he
you know is it off is it have any kind of burnable is associated with that and the bottom we see a comet a link to a scoreboard that's interesting but again here the problem is that doesn't need to be in the code for the source or the source code let's take it out does no harm to us at all it's only gives the attack for more information to our internal working processes names for social engineering any kind of mariya tactics that we see as a low threat but chained together can be you know exploit exploit 80 so when we do look at the source what the time it's not last words like three John normally long lines of texting it's
painful look but speaking we will help us is pretty print become the strong braces we get on the right a much better and easier to read version of the source code that you know formatted very nicely for us and helps us quickly you know review the source code for everyone to look for and you know from our point of view for doing source for analysis or whatever we're going to be doing we can have a much better view of the source code so i highly recommend if you can look at the source dude pretty print always so for attacker focus tools and information gathering I too i like to call i use is our retired ijs so
returned at jf has been around for a while it really text of affordable JavaScript libraries were a lot no packages as a free it's available direct at github and wrigley update has a javascript in packages age so you know mustache and so we see the maintainer to go through there and say up version 1.5 in ALB horrible to this thing you know upgrade to where the package you know says to use and a lot of times with this tool and others will be a specific of disclosures of articles and the specific reason why that library is learnable let's say sequel injection or deny on service or regex exploit its all using this is very easy to use it's a pretty
versatile
yeah you can now use it in the bar situations you can use it as scary package.json file or even either to skin you know you can also have it as an extension in chrome and firefox so as you're browsing web site if you had that extension installed automatically to be scraping like through the console and a lot to the console the say oh this version of jQuery has this horn Billy
as been filling up there so you know ways the easy grads are through the extensions so just like surfing through the website you can quickly see oh yeah it's a parade but in our version related to also check is a standalone on through the command line that's been stripped of JSON file we got all your packages in our library version to see a sequel eyes or sanitize and it's very helpful of powerful and three easy use and I wanted it through our thought that Amber we both had attentions for retire when they do active and passive scanning also do more checks for that as well but for the four / depar as a per license but for
zap it's a free extension and it's pretty powerful and here we can see example of what retired at jas will show as a browser extension you'll see we have you know all the englert files are in jquery are you know that version 1.5 point 11 of angular is portable at that point of time you know as bright house where from you the test origin report saying oh yeah town this version of angular at that place why is horrible kind of what they assess the risk to be and be very helpful for screenshots of reports in quickly identifying said Albert light let's go a new version and help relieve these issues but the more in-depth will always and retire is to
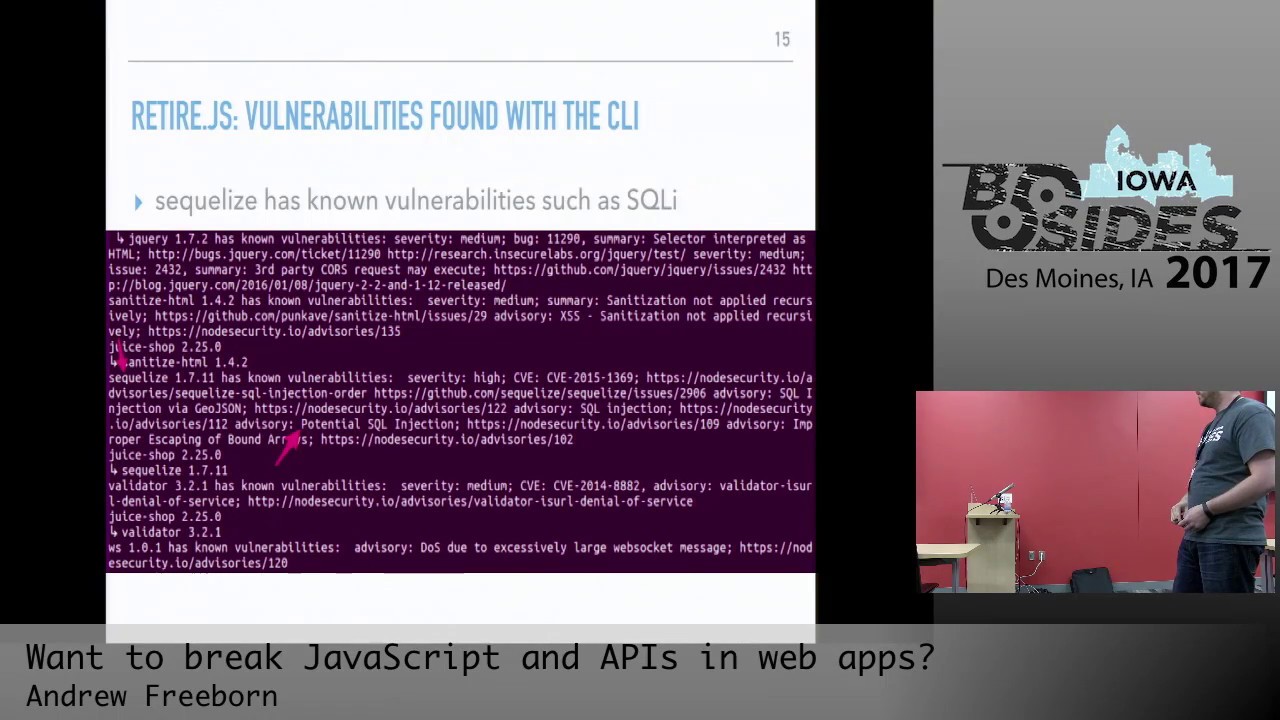
the command line so let me see here using the command line getting an episode JSON file we can see that you know through this wall attacks equalise 1.7 point 11 has potential sequel injection problems so again you can see like the note security to IO advisory linking to that version of civilized and the problem associated with that library and also calling out to more tools the operate basically is the same way you know basically excuse me the first one is a note security platform project from a lift and actually I don't see here I make dark excuse my fingers he helps maintain this project air base in Iowa and you know maintains I kind advisories
it's a lot of tools like our retire and I think and SP of course well reference no security advisories and kind of like people you know additional crowd source version you know crowdsourced pilot or e of information again it's a it's game set direct reducing the JSON files and uh d no packages as well and think it's pretty cool to think you can basically go to the website and say I want to scan this public github repo solo scan anything from JavaScript Ruby Java and it kind of hateful of the juggling a lot of things and so could see the bottom there with this sinks can from this anonymous github repository we see that the commits that was scanned the
nonverbal is associated with this form will pass steps are causing problems with this project and the pin sees all the kind of libraries associate with this so quickly XP or for free you know if we have a public or private private you get as well the free tier a quick assessment of delays associated with your project
the next school is hook man now applause man is a great tool for developer and QA people as well so first man is primarily used with ap is and assessing that and I kind of be my team tool used to share testing and scenarios and do validation testing but forestry people like me it's also a great tool because we make sure helpers are doomed they should be doing so from here for postman I can quickly provoke try break ap is i can say that query and thankless teammate and say this is what I did you know find out sick or whatever the case may be and also not sick instead of validation I can quickly share that information with
a dirty member and that like oh yeah guys suck early gotta do this kind of thing or oh yeah a version of 2.7 of Python get out of 10 so you know bridge of using Python 3 that's a different debate so you know another free tool and you know soap UI is a great tool as well you know let's kind of get around for a while but postman it's not the first you saying and why not so you know but that also works great too you know it's a great tool tool box curl you know is great for cooking during testing as well for an API and sitting outside you know a variety of different on queries and
then python and however i do is it's great that you're just lay by knowing on different way of doing it is fine too and so you know great thing with you know postman is free the history so i can quickly say oh yeah back on 24th i did this test i can this query a boom I just quickly just like click play you know plop but could scan or the top right button we'll see you later and quickly redo the test with the same parameters your part need token but I can quickly reiterate quickly through different kind of testing scenarios saving me time so not problem we see with having client high security controls other our client side well I'll
be the client side client I don't stop restriction so this is not ways as well that validate that the back end is to annihilation testing as well so I mean if you're lying only the client if they're not using a client to be pretty hard to have that control there to protect the application itself so the postman music do the postman comes to be done in zapper and a lot of different ways but it's keeping that in mind as a writer writing up the report say well to rely solely on clients are controls that can be common style or bypass entirely so definitely having that defense in depth layer of protection health validate both sides of that transaction
so you know Mitch hassel about Burt so very cool as a great tool for proxying requests and dream assessments and you know it's still pretty cheap at 399 per user but even the free version is very well it doesn't have a lot of the features in the pearl and a lot of the extensions and burp require pearl but completely worth it as a tester or even a internal organization definitely should be a center tool used but if not Zack isn't our tool as well but you know if by all means please get bourbon and trial two things bubble tools are consuming updated with new features and functionalities as the web sites themselves change with more
WebSocket based communications and kind of different API is and kind of keeping up with the times with the ever-changing landscape so we see again the screenshot we see this a website transaction we see that there's a put operation put option available that in this transaction if you see on the bottom there it's kind of hard to see you see a quantity and a two so as again as we're attaching security we should be a really a little bit limiting what kind of operation of options we limit to transaction do we allow put the delete and update on everything or only on certain operations so we will allow getting posts or just even get so we're going to be mindful of
how the developers allowing people to communicate with the application and if they're just like I'll be firing on all output but puts a very dangerous operation as if we've put information back onto the system or delete you know the same way take off the server so to make sure that as we're assessing being mindful of one of the options available to us if I were to do a put operation instead of a get would that work and why not you know why wouldn't it work so kind of why not ask you to like miss fry it puts a 404 or denied he's you subscribe so finally the thing to break is the OAuth juice saw so the new job is
a intentionally insecure about that for scary training kind of sensing town helping people get to habit of how I look at a JavaScript based application with API is and how I break that kind of motivation for this was my last location last position miles asked to pen test this this new product and this a userform the Future Forum was entirely done a JavaScript and head api's and so you know did the testing but I thought like as far as the community how if I had never seen JavaScript only applications that had api's how did I learn this how would I try to understand the problems associated this in the safe environment and how to make this you
know you know better my skills to you know learn as kind of particular you're growing fields of web apps so I'll finally found the OS juice shop that does just that and you know it's a great word great application is constantly updated by ort meek and timid Nick and even has a CTF version as well so you know pretty cool thing as well but we'll see kind of how there's a committee CTF in it already but it knows as a different strategy as well for having like open a shop a CTF or with the local media has a vga based on new shop as well and this includes I just two days ago he just updated new languages more
CTF focused updates in foreign abilities and to that 26 and the author recommends are not cheating but it's kind of interesting point you know not skiing well that guys don't care about that I mean that guy was like oh my gosh I shouldn't cheat I should go to the github well they will I mean they're not going to talk about in the bad guys aren't going to say like I really should put the main application I shouldn't try to use postman or should try to I'd use API in a bad way so I mean for me by all means do it anything you can to break it you know try to learn brick as fast as
soon as possible in fact title any fruit why can't you why can't you also try to those kind of dream is that you know show up on a you know on scan or just kind of a bit of a testing so sara lee cheating if you're trying to learn i guess and so with this application it runs in a variety of places you know it's great how the developer try to make it much as possible it's a slow everywhere it could be run on Heroku hook for free Dino and in fact the bottom right there online right now that's running on a dime Alfred I know and but any back from right now go to that website and start
breaking the juice shop that's owned by the developer but I mean as free don't need any kind of BM or if I at that but today excuse me I'll be running this on a docker container or I can run the cloud on AWS or on your own vm excuse me so for my machine for my demo I'm just running on a basic Ubuntu 1604 LTS or so nothing paying fees nothing impossible very easy to spin up download and kind of get familiar with using unity so long Libby duty but that's a full term discussion so download the ISO put it up into a sudo apt-get update and upgrade and then installing a docker the latest
dr. CD versions that you have a great set of instructions are very straightforward you know let I say less than two minutes of work 9-5 two minutes you know not counting that download time in the update update time I had system ready to download to run the Jew shell so basically we can fall a doctor pull down the doctor image of juice shop dr. run and then whip those primers for back rounding and wearing a port 3000 with that image name with an image of juice shop and you have it running you have it you know leopard of do anything else right make sure i patch is cool or anything like that and trying to robot
permissions yes i'm ready to rock and roll so sometimes you'll see a lot of things like best local three or different kind of versions of intentionally insecure web apps they kind of say go ahead finding the vulnerabilities that's kind of part of the learning process right well after Anil its kind of Timothy you know we're all of you once and so no no it's going to say oh yeah is we should do first this is how you look at second this is how you should try to figure out without giving the answer how to solve this challenge so in companion with this project there's the opponent a lot of you shot book so posting the pathology
of walking the dog of going through the website and click on the things cholera fiber or regular user how do I use application kind of first understanding how I would use did you shop in normal setting and then as an attacker how diets are attacking it so the vulnerabilities are like a lock on an sss to popping alert one that's great still happens in production but still you want to get deeper and have more real kind of very similar attacks you would see that are more nested and harder to get to so with what this project definitely achieves that you know find fun sequel Egyptian problems and like tiered XSS problems without using the front application like I said
earlier using postman to help bypass those kind of quiet I restrictions that we usually bypass using the API so it it really is a reflection of the more modern environment so chronic i mentioned do a perfect movie we'll walk through the application kind of see how it works quick walk through and then we'll go through some vulnerabilities and load the steamer with the book they say that go through the scoreboard and trying to find that and then we'll try to you know go through these 14 abilities and see how Bill any questions so far or comments means especially is like reigns of course still commercial tools versus a free and low-cost tools as well I
think this idea of a scam I've also a great school but you know that's good for more point and shoot and as well as honest with you know for an automated testing scenario but follow up with as well may know testing kind i have ever contain them with like say one user account using that you know the apps can to help skin and then using never camp with a ripper zap and kind of figuring out like you know from at the same time you know he's no tools as well but you know they work great too is just as far as you know how you coupled with then kind of put the time into like open
tools but yeah i like burp a lot there's a lot of mail this repair petition and then run through apps and then the apps game is really good too I'll find a lot of cool things soon anything else all right dope so I'm going to pop right over to AA vmware oh darn fi what's it on all right one second almost there right thoughtful look all right so you know a very basic application where we see that we can just quickly spin up on a standard a blue tuned machine so all I have chromium installed in here and especially been hard outside would be so you know the basic setup for running this box will running this version of
whew running the docker image as simple as well as mentioned running the Justice command so copy that real quick back to our terminal paste that in not talking about for twice
alright that's it the websites running literally that's all it takes if you browse that website boom now we're into the juice out so the Jew shop is like it suggests it just shopped so here we have different kind of juices we can add to our basket and a sinner ecommerce website so we can't really do a whole lot from here without creating an account so first we'll create an account log on register Andy 80.com super secret spring 2017 I'll be uh I got changed to summer 2017 all right so now we're in our website and we're just go ahead and we can see a product description through here juice all-time classic apple juice and always cook float button here add to
our cart so our basket now has one thing of apple juice you can see a price here is 199 got one of those juices and we'll go ahead and check out so that's our receipt for our order and yeah that's basically a pretty straightforward but you know I'll all along the whole entire way there's about bajillion for abilities that will soon discover so even the those is a similarly simple website there's so many issues that pops nur of you know available to us to help discover that will soon see that you know may seem simple and short but has a lot of opportunity for us to learning investigate so earlier we mentioned there's a scoreboard and so if I didn't
read the book and if I was trying to start poke around high LOL all those screenshots familiar all reflected vulnerabilities associated with a juice shop surprise so start with going to more tools developer tools now we have a really a super sweet way of assessing the website so let's refresh the page and now we can see all the traffic associated with her cooking with the tight it's all so we know that you know we wanted to see the source code for the website so we go to the source source has all the website is the index particular particular has oops agreements we have like the vulnerability the source code for this website and so basically it just start
reading so unfortunately I was already scroll down to what's that I thought but I look at the effort is in their website goes by down yeah it takes you commonly see in the production and double our second college is really cool this weekend some production now oh great what's the assessed not really so we go through here and just like quickly skating through the comments we see Internet Explorer sadness up there and that compatibility issues but that's fine one day so we scroll through header night interesting you can see that we see the log on which we saw earlier blog out now that we're Fenech ated the language menu for the McConnell languages you can see here like English
French and all those different languages and scroll down scroll down the nav and the kind of checks to see this thing called chopped down and scoreboard so I always like to say what does that do is it still lion is it living is it accessible so let's get rid of search and then CEO always been checking things out we see his scoreboard and hopefully we see these green will pop up at the very top showing what challenge what we have solved so here we can see we saw the very first challenge of discovering the scoreboard associated with this project so the scoreboard that's for kind of various challenges at different levels difficulties that help us to
understand really like to know the level of effort you know to like help find these kind of problems so this problem is really kind of highlighting the you know the ease of availability of funding comedy a code that we will still have dead code or a forgotten website that may be vulnerable that was forgotten about not removed and this will pose a problem to the website will to the company Sophie ff5 or refresh that we see now this is now solved the scoreboard challenge is now solved with this difficulty of once darn so with docker you could commit changes and kind of snapshot the painter but or if you know your reboot or in kind of change
like that equals your progress so the nice thing about this as well as we consider progress I believe it's a code and can restore so if we know the rubber boot or where new maybe we can save our progress and you come back to it and has you know the same number challenges unlocked so the next challenge is a proven of providing air that's not very gracefully handled so the best place to do that is in anywhere there's a text so I'm going to start hacking hackney ' you know possibly is best way to hack so we click enter we see that this leet hack resulted in a knockout not graceful I air we can see here the console that
we've got a 500 I was the apostrophe at the very end yeah yes I'll talk to Sonia a lot hacks has a hatch first in that posture piece it runs faster that way and you can see that we had a glacial error here that console kind of gave me this new all it trying to be very helpful and kind of helpless understand oh wow that's cool so we'll go back to our scoreboard we can see that now we have to challenge is done so apostrophes are comely and you'll use to help new sequel injection in a sequel injection is a way to help lied break out those queries to a database with information or any kind of
way to help you know circumvent kind controls and make that position to what was intended to do so that's why I do i do the poss refuse to help show up generally officially handled it's not going to be good news for this application and so again another way you know another fun thing that we try to do is do the infamous alert one box again to the attack them put it feels so let's trust morally acts and we'll just do a script Oh at first about the challenge so we have an SS str1 so for the Tier one performer reflected excess attacked with this specific script so kind of lazy so this is copy scrolls
oh that's the test one nice so here we see again the green box it's pretty sweet I pretty much to be done by now what's a million dollars lovely hacks but this is great opportunity to learn the different kind of like this bowl hanging fruit doesn't take much work to help provide you know to like the developers and the management team that like oh the possibly ask injection not just angels at all but at this text view of the search box because pop XSS you know forth that's really or trying to accomplish here and kind of understand that you know for these kind of problems it's not really to take much rocket science to try to understand that like
developers diddly do their job of due diligence to make sure that these kind of things were not scrubbed out through client side or even server side validation checks of character and sanitization so we need to make sure that we help communicate with preferably a demo of this how easy is perform this kind of attacks to kind of communicate that kind of threat to the organization and so on interest of time we know that with these developer tools you can see all the different kinds of source code associated with the application itself so we can see that that's the picture awkward we see again this long stream of information I mean I've read really fast but I can't read that fast to help me
except in a disinformation so again that pretty print print please boom we have now the cleaner and workable aversion to offer be the source of foreign kind of nasties or anything like that so we scroll down where we're looking we're looking we're and we see that we see all the routes associated with this website route slight change password and things like administration all that's pretty sweet I bet you if i were to go to administration section i'm not going to get into its kind of portal all the good you know prevention that methodology is helping to prevent that nope there's the administrator portal so you know again this that helps look for authentication for history of users i just created that
Andy user as a basic user I mean it'll get to the MS rate portal the problem is now a mystery point of view I can see all the edge account associated with this website and if he would be back I see a lot is I should see as a regular user so again occation and kind of those kind of control that should be in place and test and validated so one of the challenges is to remove all the suite five star feedback and see one five star feedback a four star to star force star well as another user I shouldn't be able to delete anything in this portal but I can't so you can see what's in our
challenge delete all the five star feedback and so it's really start wrecking things just the only use in Chrome I'm like busting out a scan which is great tool as well I'm not you know busting out lengthening sick sick load up some problems I'm just basically using application and kind of using path forward that I went you know I didn't see administrative administration up in the top nor it is the scoreboard but doing analysis of a source show the kind of life is thinking about oh if I try administration I can probably make you know if so then get to this portal on that without an administrator this administrator account and tools like as your Buster and dear be would also kind
of numerate in kind of directories and give you hit as well to let me quickly no for real left side timeless key so trying to help you salute health component enumerate commonly used names for web pages and rouse associated with this you know with this outsider where we're trying to assess so you know this is great way to learn I you know JavaScript problems and api's I'm gonna try to do another one so
I don't know offhand it might be but not too sure I'll hold up sorry about that all right yep um I offhand yeah I believe it like that is the eyes country here in the network you know all the eggs are xhr calls as well so I think like that yeah I think she looks like a call right here and yeah it's a great tool to help just understand more application as far as what kind of headers are we are we sending what kind of what kind of things always should not be advertising to attacker as far as like say server version or any kind of thing else that should be removed as a header from our our website but yeah
that's great question as well and the challenge I think they're all the same off of those squids alright so let's bust out postman so post manager yourself work with those AP ice and the great thing about working with the api's is that they're pretty they try to help the user kind of a developer make a very straightforward to help make an operation go forward so I know that I can go back here to the main website make sure have my tools running so if I add say this egg egg something juice until my basket I'm stimulus operations here on the left hand right hand side so if I were to say increase the quantity I should be able to see see
I should see below see the request payload views in operation so funny slowly get this over and Sebring deal information here about this this is Miss request so I'm making a request that's really weird to you know for my basket you know for this thing great thing about a dumper tools right click copy copy as a curl so cruel could be used to the command line to help you create the website and perform fillet of a test + man is super helpful like you want to import that I would love to import that that's important a straw text you paste that whole curl command so that's a lie text absolutely word whatever so in mine
now in my operation for postman I can see all those headers at chrome is using so i had to token I have everything else I was going to use and in the body that was to be sent I have wanted he at two so this goes back to valuation of sanitation female or using positive negative inputs are we using character so we're using any kind of like things that we should be expecting so if I were to do like negative affinities doesn't send something and send that along I should it should be I should not a see that much quantity or I make it a value but as going to see this operation succeeded so now you know this you know
went along talk to the website saying cool whatever yeah bajillion values so if I were to go back to the website at five I see a mega you know Weipa julian plenti check out and Feldon are challenged so i should not have been able to do this and for produce you know being paid and I goes ahead and solve the challenge you can see it right here of let's see successfully he'll challenge payback time listen where that makes you rich so as we're exploring website you kind of look for interesting URLs and so when we make an order it's kind of hard to see up here but right after the orders made we see a website for the you know the IP
the port and we also see flash ftp why what orders you serve off at mt p website why would i receive to be served out there let's browse it boom that's a lot of cool things in their receive and so here with the all kinds of things lie package.json that back file as a backup file bar json so this is all inventory of all the libraries and packages no packages used on our website so that shouldn't be there which shouldn't CB here's my orders I've made you know through the normal portal but we also see all these other files that we shouldn't be able to see so if we just try to browse them we can see a lot of
different things like all the things we should not be able to see like this should not be available to us this were a real file and so you know it's exploring kind of prodding and touching all the things that we want to us we want to make sure that we're testing all the things that we don't wait you know would not accept a normal user to do but potentially could do and so there's a lot more explore there's a ton more challenges to explore and understand and learn and the book and there's a lot of websites available as well to help I help you out with the different challenges I progressively kind of issue towards
trying to learn like without giving you the answer what to look for how to look for them how you would test them and just explore the website more and more and keep on going so this thing myself us would may a cts and cool way to learn ways to break JavaScript API is and just keep on going to harder and more full challenges and so you know that's great for you know messing around with oops that's great for messing around with you know play things and kind of you know hopefully in production might see some of the things but also as support where else you might see this kind of challenges well effective security has
these kind of different challenges with you know Lisa certifications with the offensive security certifications and so one of them the OSCE you know the one of the courses they have is correct in perimeter and so to get into the crack the perimeter course need to help do these kind of challenges the first break through these challenges because are easy to tell what you know austech yep I know these skills I can get through like this kind of shakedown things help you kind of prove like I'd not have some knowledge of these kind of technologies and ways to break in and right here they say use of source you know as we saw with you know what's a juice shop we saw
that there's no using the source without gleaned a lot information and help break in and so it's kind of like poking fun and kind of understand what's going on really help us in real life situations and with that I'm done website I have twitter and I'm part of a black group over in Omaha and nearest enjoying as well we have that URL to help to join a nurse black group you might be a part of and talk about security olla I'm in some beans wealthy security and live for the Oscar shop and questions alright thanks appreciate





