Password911: Authentication Adventures in Healthcare
Show original YouTube description
Show transcript [en]
so the last speaker had a really good dad joke okay you guys ready for this you might have heard it I'm stuck on this now okay how did the hacker get away from the FBI he ran somewhere isn't that good isn't that good all right we ready Alex the colle all right good afternoon good afternoon we've made it through almost the first St besides Las Vegas how y'all feeling fantastic fantastic we have the amazing Dr Matt wear with us today this afternoon password 911 authentication adventures and healthc care so somebody earlier said he saw him talk 16 years ago so let's give it up for this man he's been talking a long time okay all right well let me get some
stuff out of the way real quick first of all your cell phones turn them off again unless it's God or somebody's dying we don't want to hear it or at least turn the ringer off okay um I want to take a shout out for our sponsors the diamond Adobe our gold prism Cloud blue cat Plex truck Toyota all that good stuff so without further Ado Dr wear take it away cool well thank you very much it's good to be back at passord con um the last time I spoke in person was in 2019 in uh Pastor Con in Sweden and a few things happened in the health care world since then there uh so it's really good to be
back here and talking about passwords and Healthcare which are two of my great big passions here so in my day job I'm a cyber security researcher focusing on trying to figure out the Cyber resiliency for medical systems so I both look at kind of the impact analysis side so like a vulnerability comes out you know what is it going to be the the clinical or the patient impact of this vulnerability I also looked at this from the defensive side as well of like how do we go ahead and Design Systems so when that next vulnerability comes out they still are you know resilient patients can still have care um and we can still go ahead and do a good job so
as part of this too um I'm also a member of The biohacking Village uh so if any of you will show up at Defcon over the next couple of days uh we're going to have some medical devices for you to be able to hack and learn on maybe apply some of these lessons that I talk about here too um a side tangent um I was really pleasantly surprised by how easy it was to get medical equipment through TSA security like I I was coming through here I was like okay this is going to be the cover story this looks dodgy as hell you know you know how are we going to get this through here and um you know no
problem they were like okay it's not bottle of water we don't care uh so just right on through um so um as I was mentioned a little bit ear I I have been doing this a long time I'm a longtime member of the John Ripper uh passer cracking team because while um I'm passionate about medical advice security uh I am absolutely obsessed about pass through crack so you know whenever I get to you know combine these two things together here uh it's just a great day for me so um kind of talking about how long I've done this here uh I was one of the first researchers to study the rocky password list so I was able to go ahead and grab
it online uh I did published you know some analysis of this here other researchers were interested so I shared the list with them so if you're sick of the rocky password list I'm really sorry okay um but uh if you want to ever have some good stories about that talk to me afterwards about this so one thing though I I have a disclaimer here is I am not a medical doctor don't let this lab cope here you know fool you um I got my doctorate in uh in computer science and was really try trying to model how people create and use passwords and out of this came this pcfg password guess generator and I've been talking about
that for a long time so this is the password's con so if you'll just you know uh give me a little bit of latitude I want to talk about this a little bit more oh and also before I kind of continue uh if you're asking like why I don't actually get any work done you know it's because of these uh you know two little Helens here uh so they're always walking across my keyboard and generating really good random passwords for me so when I talk about the you know pcfg password cracking you know the kind of the base question is you know what actually is that and so the the official term is it stands for probalistic
context free grammar and this probably doesn't mean anything to anybody here unless you're really into computer science or a grammar nerd or something else along those lines and so I went ahead and I renamed it uh the pretty cool fuzzy guesser and this kind of better describes what this actually does here uh so basically you train this on a sets of disclosed passwords it uses machine learning to go ahead and figure out probabilities associated with all the different types of mangling rules that people use so you know sometimes you'll put you know uh it capitalize the first letter they'll cap or but they'll also capitalize the last letter at a certain probability you know people
usually add numbers to the end of their password but sometimes they add numbers to the beginning or they replace letters with numbers and so what this uh uh pretty cool fuzzy guesser does here is it goes ahead and takes all the information and then generates passwords in probability order so it'll get generate the first most prob password guest the second most probable password guest and so on and as you can imagine this is really useful if you're trying to go ahead and crack passwords so I'm not going to talk too much about this because I really want to focus on medical device cyber security uh but there has been some work in this uh here that I just want to briefly
mention so the the first thing I've had really recently here is a default Russian rulle set because I believe in kind of sharing this all around not just focusing on all of us English speakers uh so it's got a lot new support now for you know cracking cerlic passwords and you can find out more about that if you go ahead and read the developer guide I also added in Honey word and synthetic password generation so what this does here is instead of generating the most probable password guess and then the second most probable one it actually generates it according to the distribution that you would normally see in a normal population so it generates essentially fake password dumps so these
are passwords dumps that look very realistic to what you find in the real world and the question is like why would you want to do that there and really the kind of main use case for this here is being able to help provision quickly large deception environment ments uh because no one wants to go ahead and you know generate a thousand you know active directory user passwords by hand and so this is a really good way to be able to make that you know be able to fool an adversary uh based upon this though uh I also added in what's called a weighted random walk guest generation so this generates password guesses the same way
so it will go ahead and just kind of randomly walk through the grammar and generate password so by default it'll generate you know the most problem password guesses first but it kind of go walks around and it causes a lot of you know duplicates as well so the question is you know why would I go ahead and do that and the simple fact is that the pcfg password guest generator is slow it's really really slow so like it cracks passwords but you know you generally want to go ahead and use other attack modes if you're not targeting something that's really computationally expensive with this weighted random walk though um it's fast you know you don't
have to keep track of state so the memory requirements don't change over time uh it's highly paralyzable because each guess is independent of each other and what this really means is that it you know it really kind of hopefully scales to a GPU password cracking type of a a message there so just to give you a preview what I'll be talking about next year hopefully is I really want to go ahead and get this included into hashcat there so that's going to be kind of my go goal there but that's all really kind of to the side you know because you know what I really want to talk to you about though is passwords in
hospitals uh because this is something that's really important there you know with password cracking you know we're we're getting better you know that's I won't say it's a solve problem the next talk we're going to hear is going to be really trying to get into that last hard part of it there um but you know there's a lot more problems here with you know trying to secure hospitals you know how do we go ahead and uh be able to provide care in a kind of a hostile thread environment and it definitely is a hostile thread environment too hospitals are absolutely under attack so the the primary people that are targeting them right now is your standard kind of ransomware type of
uh you know criminal organization there uh because they like the money and hospitals have money I mean that's really kind of what it comes down to there so you know kind of if you look at what they're doing right now it's kind of the standard that you see across any other industry there they they they break in they they encrypt the files they demand a ransom payment in order to decrypt them um in order to do that um but um hospitals have luckily and this is a really good development here have gone better at being able to respond to this because being able to provide uninterrupted CL you know clinical care is kind of cord to their mission so
unfortunately the attackers they don't go well okay no this is getting harder we're just going to walk away and Target other Industries uh they've definitely been going ahead and changing their tactics as well uh so recently we've been seeing them go ahead and start trying to Target like Hospital support structures like Voiceover IP systems and you know it's really hard to run a hospital if you don't have a phone um you different departments need to call each other patients need to be able to call it so when a phone system goes down in hospital it's a really bad day uh the other new tactic that's really been kind of popping up lately and this is a
really um just horrible one is extortion of patient medical data so they'll go ahead and they'll break it into the the hospital they'll steal very sensitive patient data and then the hospital won't pay them because they're going ahead and they have recovery procedures in place to be able to respond to that there so the hackers then reach out to the patients and say hey look we're going to go ahead and publish this very very sensitive data about you online and then tell everyone you know about about that sensitive data unless this Hospital over here that has all the millions of dollars goes ahead and pays the ransom and so they're getting the patients now to try to you know pressure the
hospitals in order to pay the ransom so that data doesn't get leaked and so you can see this is a this is a really important problem for us to be able to solve because we're all future medical patients hopefully you know that we you know if we live long enough we are going to go ahead and end up in these types of systems here and so and so same goes for everyone that we love and care about uh so being able to provide safe and effective Healthcare is a really important topic that I'm very passionate about now one thing and one of the reasons why I want to give this talk though is because our Solutions have to
fit into a clinical setting um there's no if ANS or buts about that there and so it this is really causes a lot of problems because a clinical setting is very different from your typical enterprise system there you don't want you know someone to go ahead and reboot the you know the uh infusion pumps or something like that there when you're in the middle of get receiving treatment there you know you don't want your anesthesiologist to forget their password as they're trying to log into their computer or something like that um you don't want you know password change policies are suddenly break systems that are providing care so trying to figure out you know how we can go ahead and
secure the system and apply you know strong password you know policies and authentication uh mitigations into this here is really important so I could keep on ranting about this but I'd really talk rather talk about you know case studies here so the first one I really want to talk about is control substance infusion pumps so these are very common devices you'll find across hospitals and they're used to dispense pain medication uh so you know any of the really good drugs uh there that you can think of there they they generally fall into this here and you don't want patients just go ahead and open them up and start reaching in and start squeezing that you know bag of
morphine really hard there uh so pretty much the defining feature of a controlled substance INF Fusion pump is a lock and key so like here's one model here there's where the key goes here's where you know well I guess that's a lock but you know you know there they go for that so if you go ahead and see a device with like you know dispensing drugs that you know has a key that's probably a controlled substance infusion pump so this is probably the most you know Common basic security password type of a you know Paradigm ever you know you got something that's really valuable you don't want people to go ahead and just grab it so you put a door on there you
put a key on that door or lock on that door and you call it a day so this is pretty kind of a standard uh you know password type of a problem so what if I told you though that this is also kind of a standard issue that comes up a lot is about key reuse and specifically it's a common practice across all these different manufacturers here that they will use the exact same key on all of their devices so uh for example like if you go down to the hospital down here uh on the Strip uh you know you know what type of infusion pump they have uh you can go ahead and get the key really easy
and go ahead and log right in open it right on up and as as I said this is very similar to for all these pumps so this is a pretty much a universal say I'm not trying to give you know individual manufacturers a hard time uh the only kind of disclaimer that I have is that you have a lot of these kind of thirdparty you know plastic cases they put on there and there's not really standardization of the keys for those simply because there's not standardization between the manufacturers so this is the audience participation part here to talk but is this a problem okay we have some you know you know important stuff we don't
want patients going ahead and squeezing it we don't want people stealing it we put a lock on there we use the same key for every single lock all around the world um is this okay no well I would actually argue it is okay um because you know you have to be physically close to this in order to be able to do this this is not a remote attack and if you start going ahead and opening up these infusion pumps and squeezing that bag really wicked hard you you know the nurses might want to stop you as well and you know so you know this is not a huge problem and at this on the other side there um
Physicians and nurses and everybody else need to be able to get into these pumps very quickly and so these Keys have to be very reliable uh because you don't want that to jam when you're going ahead and trying to go ahead and change you know a patient's medication uh you also can't really change your treatment plans while that key is locked as well so you have to be able to unlock it because you don't want patients pressing that button as well so making sure that lock is really reliable uh that can be open to all types of situations it has a you know strong failure mode and stuff like that there they have to worry about is
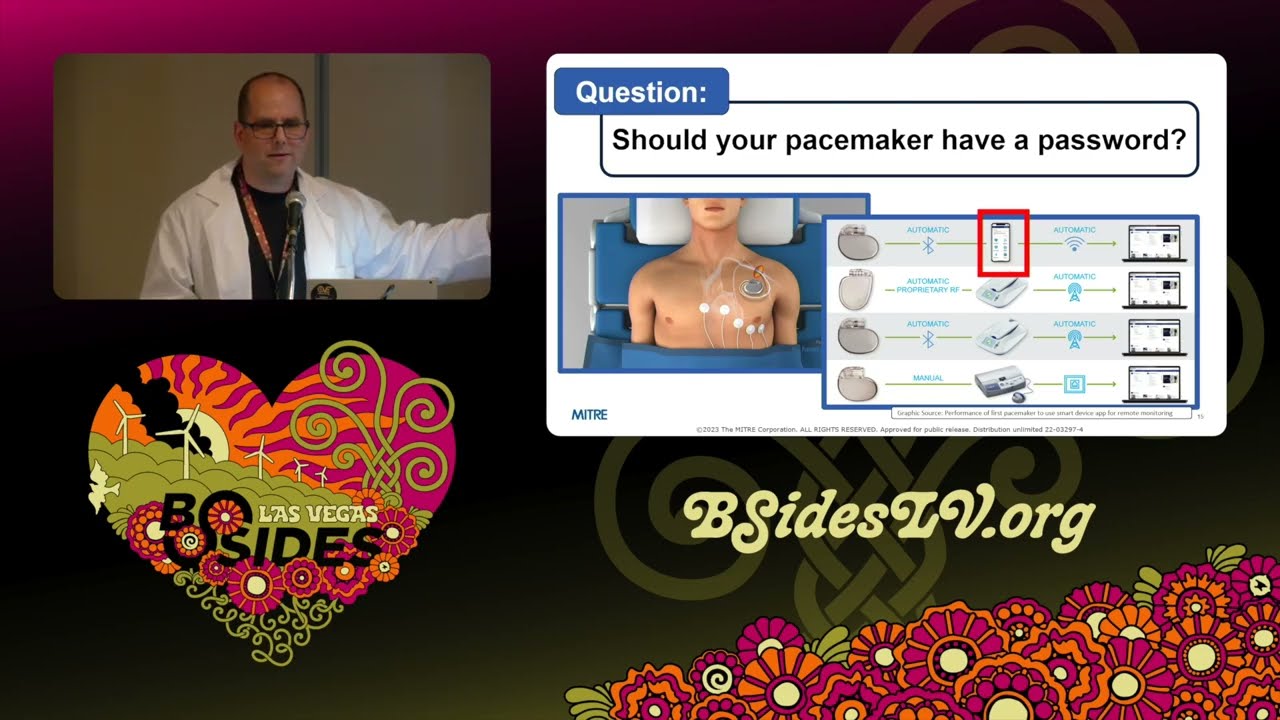
really important for providing patient care so there's not really been any uh you know uh examples as far as I know either of you know patients actually compromising this so you know the chances of someone you know having that key around their wrist when they get in a motorcycle accident is pretty low so this is kind of an acceptable trade-off that you know most people take when it comes to passord security or you know authentication issues when it comes to infusion pumps so let's take this up a notch though should your pacemaker have a pass password I know yeah everyone's kind of sucking in like yeah that that seems like something that' be really important
there you know we don't want people just going ahead and logging into pacemakers and pacemakers are absolutely very connected um like right here you see like a a cell phone okay you don't want just everyone you know walking by you know logging into your pacemaker there and this this is very important to enable people always ask like why are we enabling this well this is providing information to your your doctor uh about you know how that pacemaker is functioning uh often pacemakers need to be tuned around and stuff like that there because it's you know it's a it's a very delicate type of a thing so being able to provide that level of reporting saves lives so we can't go ahead and
just say we're going to go ahead and disconnect all these devices make them dumb devices we have to be able to enable this but like even looking at this like how does that pairing work like there's not a button on there I can push like you know when I go to like pair my cell phone that do I do need to do like 15 minutes of cardio or something like that there in order to like get my heart rate up and uh you know accept that request and I mean the short answer and there's a couple different ways that to do this here is that you'll have an app you'll go ahead and you'll enter in your
serial number into that app it goes out to the the manufacturer and the manufacturer gives you kind of a rotating pin that you can then use in order to go ahead and pair your cell phone with your pacemaker so I know we have a lot of Security Experts watching this right now and you're like okay sms okay that's a problem sometimes there's there's challenges with this you know how random is this serial number that there actually being generated for someone to be able guess there's a lot of different rabbit holes that we can go down into the security of this here uh but before we do I just want to point out another different use case that will kind of uh
negate a lot of that and that is the pacemaker physician programmers so the cell phones generally just report data about that that operation there uh but you know Physicians need to be able to to modify that treatment plan of those pacemakers as well so these programmers not only can they read data but they can go ahead and set the settings of your pacemaker as well and so that's really serious and the other challenge is that often these devices need to operate in kind of an offline environment you don't want to say like I'm sorry we can't deliver life you know giving care because our internet is off uh so you know these Pace these pos position programmers need
to be able to access pretty much you know anybody's uh Pacemaker and this can happen whether you're here in Vegas whether you're at home whether you're in Australia or or anywhere else you might want need to be able to receive a medic care and so these uh programs are kind of interesting each manufacturer has a different one so you'll often see them like just kind of stacked one upon each other in the hospital there uh each of these will also be running you a bunch of different apps on there for each different model that they want to be able to be able to support if you look at that guey you're like wow that's really old yeah you're right it's about
you know three years old there uh but you know you have a gooey that works in a hospital you know healthare system me why why boser to update that there so how do you secure this okay this is something that has to be access pretty much anybody's pacemaker you have to be able to go ahead and distribute this you know all over the world basically uh you can't really have that know functionality to phone home to a centralized database to be able to receive these you know whatever security code that you have like how do you like how does this work with passwords um so like one thing they might start to think though is like
maybe the manufacturer really has some proprietary algorithm that no one can reverse engineer or maybe we like hardcode the password onto here and you know really try to keep these programers safe you know we really try to lock them down and ensure that they don't get out to the wrong hands and oh well that's not going to work um so you know these things show up on eBay as well you know be maint being able to maintain physical security these devices is very hard so one thing I just want to highlight is you know I've looked at this here I actually haven't bought one of these uh doing uh pacemaker research is actually really hard because you don't want to be
like oh I wonder what this does and someone just drops dead outside your hallway um but uh you know this is definitely something you need worry about when we talk about you know the the Threat Level to be able to do this here you know adversaries if they really want to be able to get into this here there are definitely ways that they can be able to obtain these types of devices now I want to take a kind of a step back though okay uh and it really just kind of um ground this because um I don't want anyone to leave this scared okay these devices they save lives full stop I have people that I know and care
about that have connected pacemakers and I okay with that because the the the value of this the care that they're receiving from that there is way outside the risk that they could potentially be having there's also no evidence of any implantable devices being exploited in the wild so while we we're basically talking about Ser rical attacks that could potentially happen they're not saying that's currently being exploited and then the level of expertise and resources develop you work exploit is non-trivial okay it does take work and luckily the vend diagram of people that have the technical skill to be able to do this and people who want to kill people is pretty low uh you know
as far as overlap goes and but I want to have a better story than this and this is why I'm giving this talk here it's because I really want to inspire everybody here to really start trying to figure out better Solutions uh because you know we have to enable this connect connected functionality we have to even add to this connected functionality make it even better make it more connected so that we can get start getting data and in order to save pe people's lives but we also want this to be safe and we don't want to have any caveats we don't want to have anybody worried about whether they're goingon to be hacked by their pacemaker or not so we really need
to get together as a community and figure out you know Secure Solutions in order to be able to you know address problems like this so some of the key topics I'm going to be really talking about here and kind of harping on is uh you know first of all when we talk about medical devices and stuff like that what we're really talking about is medical systems like everyone focuses on the end device that you can buy on eBay but it's connected to all these other different types of systems and that's the whole reason why we're making that connected in the first place so trying to understand the whole security of the system of systems is
extremely important the other thing I really want to highlight is the idea of resiliency so you know devices are going to get hacked keys are going to get leaked the the real important question is you know how do we still you know maintain and deliver Safe Care to people when these problems happen so for example like what's the pacemaker option we might not be able to have a password with that so what else can we do maybe and I know this is a hard problem to ask for you know at a password con conference but like are there non-password solutions that we can have you know uh for example like can we have better reporting so
that way we can say you know if something does happen we're able to detect it very early in real respond to it uh one thing that manufacturers do is they have safeguards in these pacemakers um mostly they're from a safety standpoint you don't want the physician to like hit the wrong key or their to walk over their keyboard or something like that and all a sudden you know for it to you cause harm to a patient uh so a lot of times these devices you can give them you know you know bad data uh but they'll fail into a safe mode that will still provide you know not great care but at least some level of care uh
for them so maybe you go ahead and start doing that in order to be able to better secure it so even though you know anybody can log into this pacemaker uh they have a harder time actually causing actual physical harm but what I really want to inspire people to do is start thinking like as a system of systems and outside the box of how do we go ahead and secure and enable these really hard uh um clinical use cases so let's have another you know uh case study here stor credentials we've heard about this quite a bit actually uh from all the previous talks that we've had throughout the day here and I'm sure we'll be hearing more about this later
too so medical devices store credentials just like everything else so here's a cve it's basically for an infusion pump and I I'm sorry about all the words um but really what it boils down to is that the CVA came out and said that you know an hacker may be able to obtain unencrypted wireless network authentication credentials to the hospital uh by disassembling one of these infusion pump units and just reading the flash drive so the caveat There Was You Know accessing internal flash memory require specialized tools and then like nurses might get a little bit annoyed at you too if you're going ahead and just you know unscrewing these uh on the the ward there um so that was
really kind of what it was saying there and you know the kind of mitigation saying that this wasn't a really big problem so my question to the group did I want this to be a little bit more interactive you know is this a problem you know Wi-Fi credentials to the hospital stored on a medical device that you have to physically open up in order to extract a flash drive in order to read who thinks that's a problem oh we got a few hands here okay guess what I'm with you there okay because it that doesn't have to be in a hospital when you go ahead and extract that data so here's a bunch of infusion pumps in that
cve listing there um they're a lot cheaper so we went ahead and bought one um and so here is that infusion pump in our lab uh we name everything after Simpsons characters in our lab because that brings me a lot of Joy um and so like you know there's me opening up there's a tamper evident uh seal that was just a sticker and I'm actually kind of cool with that security feature because um you know it doesn't I'm not going to report it myself so having a really good temper the steel doesn't isn't that important it's probably worth that one penny so the board biom Med just doesn't start unscrewing it in the you know and when
they're messing around with it and stuff like that you know there's the flash card uh in it um and so there's me with you know Proof of Life with that flash card there so you know being able to uh you know uh pull that out is a very realistic you know type of a a threat there now one thing I want to say though is you know after all that work there I actually didn't find any uh credentials on that particular model there uh but what I will say is I have found lots of Wi-Fi credentials on other eBay purchase equipment that we've bought as well there uh so this is absolutely a very real thing um um the disclosure is
always a a pain as well because she like you know it's like oh my God I hope there's not patient date on here as well um but uh so you you have a lot of fun talks with lawyers when this happens here uh so this is an example though of device retirement uh so this is something that all devices go through you know uh the device you know gets used and someday it doesn't get used it gets you know replaced it's either thrown out or sold on secondary Market um and then you need to make sure that um you know they that's done securely there because you know people don't change their P Wi-Fi passwords
very much especially in uh you know high value environments there so one thing that I really kind of believe in is the idea of threat modeling and so this is something that you know our team's really been involved in quite a bit uh a couple years ago we published A playbook for uh mly medical devices uh This was um uh sponsored by the FDA uh to uh really try to get stre Molly involved in early on in the development of medical uh devices there and uh throughout this we have the idea of kind of example of high value data flows and these are common things that like a lot of medical devices do that have a lot of security problems so like
device retirement that has a lot of security challenges that can occur there it' really be nice if we started to seeing like you know more Advanced Techniques like TPMS or you know other types of things like your cell phone you know is pretty good at being secure all these different things even if you lose it you know somewhere um so there's a lot of different other kind of high value data flows that you know then trip people up as well so in this Playbook what we did was we have a bunch of example you know fake but you know realistic kind of looking medical devices um and we start walking through kind of you know how you go
ahead and do threat modeling of these devices as well as common problems that occur so like a big one that we have is software update you know software update is a a really important thing we want to be able to make these devices be uh responsive uh to attacks when they come out so being able to update software provides a really good mechanism for that there uh but it's really hard to do secure software update um there's a lot of things that can go wrong and so one other research question I kind of like to put out to the whole audience here is um you know how do you do this and how do we make this easier for medical ADV
manufacturers to actually Implement because trying to implement secure software update especially for some of these you know not real-time operating systems and stuff like that there is actually non-trivial and if you're wondering like do people get them wrong absolutely okay uh so here's another uh cve uh this was also for another infusion pump and basically it says application does not restrict upload of malicious files during firmware upload update so there was no device signing there's no authentication you just pop an executable in there it's like sure sounds good and it goes ahead and installs it so like I'm not the greatest hacker in the world but you know even that level there I can go ahead and be
able to deal with so this is another example though from like credential management and stuff like that there of being able to you know properly sign software updates be able to distribute them out there correctly and stuff like that is a really hard problem to be able to solve that pops up in pretty much all these different types of medical devices out there now I've been given a lot of different uh infusion pump examples here and um you know the initial thing might be like oh my God you know infusion pumps are really insecure and not completely wrong uh but uh you know the reason why we see all these different vulnerabilities pop up about them there is really it comes down
to they're cheaper than MRI machines when you start looking at other medical devices you see a lot of same problems uh that's actually one of the things where I love being in uh cyber security for medical devices is because it feels like I went into a like a time machine and I'm suddenly back in the 1990s like oh look telet hey cool um so you know there's a lot of different you know there's a lot of room for improvement uh in medical device Security in order to be able to uh get them to start using more modern protocols and uh be more resilient um but I have to say I'm I'm cautiously optimistic um because you know the
security research that we're doing right now is having a huge impact and I really do believe that security research acts a lot like a vaccine there you know you're you're basically stressing uh the organism uh in a way that's you know safe and it develops defenses against you know what those stressors are and so in this case it's cyber security we're stressing these infusion pumps here and across the industry we're really seeing that infusion pumps in infusion pump manufacturers are really kind of taking uh notice so there's a lot more Guides of how they go ahead and secure devices securely and they they're starting to implement much much better security there uh the really big problem though
is Legacy systems you know hospitals just don't go ahead and update their systems all uh you know all the time there so these systems you hang around for a long long period of time and then the other thing that I really think is kind of important is how do we you know translate the lessons learned from these types of devices and this type of research there to all the other types of devices in a hospital because we don't want to go through this long painful process with every single device in that hospital it'd be really nice if we could kind of learn from everything and go ahead and develop more Secure Solutions and really apply that to other people as
well there so I've been on my high horse a little bit too long here so let's talk more about you know other types of examples uh that you know kind pop up here in uh Healthcare so Health electronic health record systems are really kind of the core of any sort of hospital if you follow any sort of cable from any medical device in a hospital and you follow it long enough through all the different wiring closets and stuff like that there eventually you're going to end up at an EHR system okay because this has all the data about all the patients that you care about so this is you know what we use in a lab we have open EMR because it's free
and uh once again that's kind of nice uh but this is actually inhr that's actually used in a lot of smaller organizations as well because it's free and you don't want to have the billion dollars to spend on Epic or Cerner um so um we also just um and kind of a quick shout out uh we use uh synthetic patient records for this so there's a project called Cynthia allows you to generate very uh realistic synthetic patients uh so this will have you know they'll have the proper Co comorbidities so you're not having like a a baby with dementia um so U if you squint it it looks like you know a real estate patient and that
way you don't have to worry about dealing with napi when you're doing anv research there so these electronic health record systems though they need to be connected to a lot of different other types of systems and so he starts thinking about this and you look back at the couple of you know previous talks that we had in this track here and that means apis you know everyone's you know favorite you know thing that we're talking about when it comes to computer security so there's a lot of different ways to be able to connect to to these types of systems um and um basically one of the newer ones that's really kind of interesting is called the fast
Healthcare interconnect interoperability Resource number one and it's a it's a fairly new standard it's only about 10 years old um and number one as you can see it's you know they're they're still trying to build it out uh but it's a lot better than the previous uh standard called hl7 uh which um it's it's like Vibes of a standard kind of it's not really uh um so you know with um fire it's actually it's a pretty good uh way to be able to U be able to transfer medical records between different devices and because it is a newer protocol it does support other types of you know newer you know authentication mechanisms as well like oos to and so o
L is is pretty good actually okay I mean I see a couple people noding like okay you know that's uh and that's not horrifying uh so that that's pretty good there uh so so that's that's really good and that's really optimistic there uh but the problem is what happens when we take you know these protocols that we're using in a hospital and we start trying to go ahead and use them to enable other types of healthcare delivery oper options there so a good one is kind of Aging at home you know we want to go ahead and move more you know medical devices and you know Health Care you know systems into the house so that way
you don't actually have to go to the hospital you can get better care at home you want to be able to see your patient records which is really important for everybody as well and then we also have a lot of different other areas too where you we want to be able to um you know interconnect different uh companies together we want to be able to interconnect different Services together we want to connect this to the cloud um so you know how does this go ahead and work and the the short answer is there's some Growing Pains um so so uh recently um or a couple years ago actually but so it was a number of really kind of
interesting vulnerabilities came out called uh plane with fire and um the work that Alysa KN and her team did was really kind of cool they found a lot of different challenges with uh basically trying to analyze um uh web apps you know on your phone uh that you know connected back up to EHR type systems there and while they found a ton of different problems really the core one that I kind of narrowed in on there was that um a lot of these patient apps here focused on authentication but not authorization so they would make sure that they authenticate you really well they would make sure to you account on the system that you were actually who
you were talking about and You' say I want everybody's record it goes sure you know there you go you know you can have whoever's record that you want there uh so what it really had come boiled down to is they didn't Implement a whole lot of serers side controls so they they make sure that you actually had an account to the door but once you're in the door you could go ahead and take out everything that you wanted with that and kind of the question is you know why didn't they hit the syn of that there you know that seems like a pretty really you know basic or important type of a thing and my hypothesis kind of looking
at some of like our EHR systems here is hospitals really don't work that way you know a hospital you're not trying to say okay this patient only has access to this one piece of data what you're trying to say is this medical device has access to all this type of data here so okay this one can have access to your dental records okay this one can have access to your X x-rays here or this one here can have access to you know your billing information for some reason um so when you look at you know how you go ahead and specify authentication and authorization with these devices here it's really these broad categories that these really focus on so this works good
in a hospital it causes a lot of problems when you start just taking these protocols like you know willy-nilly and trying to move them to kind of a patient facing app where you say you know you really only need to have access to only your data and so I suspect that this is going to be an area where we're going to continue to see a lot of uh challenges with you know over the coming years and so from a security research researcher standpoint I would say this is something that you know you should probably almost immediately look at when you're trying to analyze these Health apps is are they actually you know uh having any sort of authorization
as well as the authentication that they're doing there so getting back to the patient bedside though um let's talk about service pin codes so if you find something in a hospital and it has buttons on it it probably has a hardcoded unchangeable service pin code that you can use in order to enter into kind of some restricted mode in that and this is this once again this is a universal issue it doesn't matter as I said if it has buttons it has a backend you know hardcoded password on this so this is kind of once again here's our lab uh of course because I can't remember these uh we you know you know wrote them down on a piece of paper and
just taped them onto the device here um so now I have to say like I've been doing password cracking for a long time uh I know a lot of you know good reverse Engineers too where I work um so the question kind of comes down to you know how do we find out this data here you know do we have to go ahead you know crack this open you know pull out that flash card again start reversing this you know extracting these passwords uh there was a previous talk about you reversing mobile applications do we need to go ahead and do this in order to get the you know that those service pins and uh the short answer is uh I'm lazy so no
I just go ahead and I download the manuals and then you know like somewhere in there this was like in one here's all those PIN codes for that right [Laughter] there so I I heard some people saying oh no here uh I guess my question to you is is this a problem uh who here thinks this is a problem right now okay let's get some hands up here oh we got a couple of them yeah we got some wavies as well um I actually will say I don't lose any sleep about this here okay I don't think this is a problem because I kind of like factors around to like having that physical key like if you're like physically d and are
able to start pushing things into the button and that there like if if I'm connected at device I'm not going to be doing that because I don't want to be like I Pon the device and you're dead you know um yeah so um uh you know I really don't have too much of a problem with you know these you know physically you have to be physically there in order to be able to access these modes because it's really the main goal for this year is just to make sure that like a a nurse doesn't accidentally like change the IP address of a device here or like you know uh you know a patient just doesn't like you
know start messing around with it and get into an unsafe mode here uh but it's not really a a real secure uh you know access control that needs to be kept secret from everybody so what about hardcoded remote passwords so this is a um a problem here so I was kind of curious about you know trying to figure out like how big of a problem this is so um I work at miter and so we're all about our different enumerations we have you know a million different ones there you hear about attack cve cwe and stuff like that there so cve common vulnerability enumeration is a really good way to be able to kind of see you
know what vulnerabilities have come out in devices before uh but there's a lot of vulnerabilities that come out so being able to narrow your search for them is a little bit hard sometimes so one thing I want to kind of highlight is cwe common weakness enumeration so you can say you know I want to find out this particular type of vulnerability like you know use of hardcoded credentials uh so why don't I go ahead and search all the cves for this particular cwe and see which ones pop up here and the short answer is a lot okay um and actually I was surprised by how few I found because I've done a lot of work with medical
devices and um I've definitely seen a lot more medical devices that had hard-coded unchangeable remotely accessible passwords uh than what pop up here so this is a real problem okay and this is definitely something that you know we do need to be able to address and this is I'm a lot less forgiving for from when it comes to trying to assess the the impact of these security vulnerabilities here now there's definitely other mitigations that be put in place in order to try to limit the damage that's done by these here here uh but you know this is something that you know you know going forward I would really like to see less of here so you know we talked about a bunch
of different types of password you know vulnerabilities with issue uh you know different medical devices here and I didn't offer a whole lot of solutions as well I have to admit and um I'm very um aware of that and that's actually one of the big things that really spurred me to have this talk here is we need more cyber secur researchers in the medical field um there's a lot of different work that needs to be done and I I don't want anyone to here leave here you know afraid I don't want you to be afraid of receiving Medical Care uh I don't want you be afraid for your um your loved ones here when they they're receiving
medical care but I want you to leave here inspired I want you to leave here really determined to kind of look into you know different types of uh medical devices and really try to start doing some of this research and it's fun work it's impactful work and there's a lot of low hanging vulnerabilities for you to be able to deal with as well there so one other thing I really want to be able to highlight though is that the solutions that you come up with have to fit into a clinical setting okay you have to really always keep that patient you know uh Care at the the Forefront of your mind so making sure that's it's
available making sure that these workflows are able to work is probably the number one priority there and so we have to make sure that we have to change our security practices around that versus trying to change you know these clinical care workflows in order to fit into our security uh uh methods here um I also really am a big fan of threat modeling uh so um I really think that you know if people start doing threat modeling that really can be you know Help win the war a little bit here at least try to identify what are the threats what are the trade-offs that we're making and you know how are you going to go ahead and address those
threats there as well the other thing I really do strongly believe is that cyber security is too hard right now okay medical manufacturers are not going to go ahead and you know focus on cyber security that's not a that doesn't you know make money for them there uh so what we need to do as a community though is make cyber SEC easier so that way it's easier for them to actually Implement devices in the right way uh than just trying to roll their own solution there so comeing up with like common practices and common libraries like how do we go ahead and do authenticate for you know pacemakers and stuff like that there and come up with
standards for that there I think is a really important area of research for us to go forward with here as well um but really at the end of day there you know it's really important that we we can't say no to all these different options like someone's goingon to say I want to connect you know this medical device to the cloud and I mean I got feelings like no don't do that don't connect that to the cloud I don't even like connecting my home you know uh you know smoke alarm to the cloud or anything else along those lines uh but we really need to be able to enable this we need to say yes we need to be able to
do this so that people are able to receive effective care going forward so that's really kind of my uh you know stump speech here for the importance of this work I hope that you're you know inspired by this here uh I love talking about this so feel free to hit me up really whenever and I will you know rant your ear off about this and I really want to learn from you as well here uh and also come visit the biohacking village later on if you actually want to hack some of these devices uh for real as well so with that does anyone have any questions R in the back there a question so I used to be a oh thank you uh Matt I
used to be a paramedic and now I'm in the cyber security field and I'm curious I got two questions one's long one's short first one is how do you deal with the what's your personal philosophy on dealing with cyber security and Medicine of that like emergency situations need to have you know break glass in case of emergency those keys versus keeping things secure so that the first question the second was was are you guys hiring so I I'll answer the second question first yes uh so uh talk to me afterwards uh for the first one um I will say uh I am all for Blake break class uh at the end of the day uh I I
once again kind of going back to that bullet point earlier there I think we have to be able to enable those clinical workflows like I I forget my password all the time I mean that's just the case there I don't want to be like in the doctor's office like I forgot my password I like well guess we got to operate you on you you know take out that medical device there that's just not an acceptable answer that I'm willing to take uh so uh we really have to be able to enable all those Brak glass options there and that causes a lot of problems because that means that passwords are a lot harder you know we
have to be able to allow people that may not you know be good actors in order to be able to break that glass as well so coming up with other resilient options so when that glass is broken um you know your house still doesn't get you know completely ransacked you know maybe uh you know safe for your important data or something that there uh so long story short I'm absolutely on the break glass functionality there I'm I'm you know availability and being able to provide care over you know following just kind of a a standard security thing we need to update security in order to make enable those that that that functionality yep a question right
there y than uh thank you mat great talk obviously um so kind of to Pivot with that same break last last emergency sort of thing um I work for the defense health agency um and so one of the things we all be the first thing we always say is patient care is first right what happens when our medical professionals starting to weaponize that against us so when we start to make what I consider the very basic cyber hygienic policies in place they fight saying like oh this might kill someone I was like sir your ability to watch YouTube videos is not going to kill a patient but I can't but like all the veterans in the
room I'm really sorry that's an actual Ro case study um so so like how how do we basically in your opinion like what's the right balance of like no no we really want you to save people but also don't be a dick about security um that's a real hard question and certainly one that I'm certainly struggling with myself here uh quite a bit because I like watching YouTube videos too uh um but I think it's a really a conversation and that's where I'm actually kind of a fan of threat modeling uh if we tell people like you got to implement a security uh Pro process and they're like well no um you need to come back and say okay here's
why and you kind of walk them through it because if you tell people like okay uh you know the hospital over there got hacked because you know they enabled you know internet access to this you know clinician facing you know computer here and malware got into that and then a ran somewhere to the hospital there uh people can sort of start to understand it and you still have to have a conversation because they're like well I'm not going to click on that link uh but um you know being able to really kind of walk through these types of threats really try to walk through the procedures and then maybe come with an alternative option like okay you need to
be able to show YouTube videos to your patients because there's a lot of useful healthare information why don't we go ahead and make another laptop available for you to be able to uh you know um uh you know have this really important interaction that you're having with your patients as well uh so I certainly haven't found a good answer to that question it's a it's one that's going to continue to pop up all the time um I mean I know like I'm a I'm a bad user too like when my Corporation says like okay you need to change your password I'm like I've done a lot of studies say you don't and uh it's not helpful
um uh so you having those uh you know interactions and stuff like that there uh it's really tricky but we need to kind of come to the table with them as well to try to figure out alternate workflows for them uh so um B botnets have been a very very uh uh critical uh you know um uh attack Vector for uh all these medical devices so um the the the problem lies with the device manufacturers not abiding by a process supply chain uh you know uh validation and stuff like that so how do how do how does mree take this to a Next Level to uh know better educate uh the actual vendors of these
uh devices and uh supply chain um so that's a really good question there um uh so um everyone has a role when it comes to the medical device security you know patients have a role doctors have a role hospitals have a role medical device manufacturers have a role the thing is when you go further Upstream there um the the more resilient the system becomes because like trying to expect users to be secure is just you know not going to work you know trying to expect doctors to be secure you know you're going to have Exceptions there trying to expect hospitals to be secure you're going to have Exceptions there uh so trying to move that up and you know
really focus on the make Place manufacturers can have a huge impact uh throughout the entire industry there now I mean the challenge there is you know how do you actually inspire this and so um one way is you know what's legislation so you know there's a whole I am the calary track here that really focuses on policy um but you know that's a that's a dirty RW there you know you don't you know you have to be really careful about that as well uh so the other thing I think is really kind of important is just making it easier uh for medical device manufacturers there uh so you know expecting them to have a cyber security and password and
authentication expert on our team is just not realistic I mean there's just not a lot of those people out there and let alone you know fory smaller device shops here so you know having practice guides so that when they go ahead and say you know I need to make this device I need to get it through you know FDA certification I need to do go ahead and do all this stuff here hey I can go ahead and use these libraries I can go ahead and use this you know follow the standard practice guide that's put been put out there um you know that's just easier you know than trying to roll your own solution and do it so if we can go
ahead and make security easy that's really the way to be able to inspire them and so there's different resources available for medical voice manufacturers uh so the nist national cyber Center of Excellence publishes some implementation guides that are really useful for different areas there so they have one for like telea Health one for Infusion pumps and so on um as I mentioned like we've you know authored A A playbook for S Molly medical devices uh so and you you know now we're starting to need to be able to do threat modeling if you want to get your device through certification so being able to kind of use some of the Lessons Learned in that that Playbook there uh can be
very useful for you as well um and then just being able to use kind of standardized libraries and you know there's a lot of overlap now with like iot so you see standards like matter that coming out for the iot setting and uh medical devices look a lot like your smart door lock you know or something like that t sometimes too so especially when you're starting to move them into the house so we we start to see you know security features being used across other Industries trying to figure out how medical voice manufacturers can Implement them uh is nice because then they don't have to roll that themselves so once again it's just easy for them to
be able to do so uh long story short the easier that we can make it for them the better off we are and I think that's really how we uh Implement change in IND industry any other questions oh what we in back again
there thank you Matt going on the same uh track because I've seen the same thing like these companies don't have a whole lot of budget for for doing cyber security have it has anyone proposed a distributed model kind of like an an mssp but for healthcare where you have like a whole bunch of small shops pitch in a little bit to sort of pay for a cyber security professional that can evaluate their software to make it affordable um there are definitely are um Industries are popping up there uh because the second you say you know this is hard we want to pay somebody be like I can do that uh so I really don't want
to kind of start listing them off because I don't want this to be uh you know the the Highlight one or the other uh but there definitely are uh you know um you know um especially if you go to like let's say a conference there you know down the the way there there'll be a lot of vendors that will be telling you how to be able to do that and I think that's actually it's a very important Niche to be able to do because having that cyber security professional and then pay being able to pay for them you know on your staff is very hard to be able to do as well uh so you're see
we're seeing that a lot for hospitals U because they just don't have that cyber security professional on staff they have some want to patched systems uh but they don't have someone that's really you know aware of all these different types of systems that coming into their Hospital there uh so there is a lot of Outsourcing that's going on currently in the industry for that there I don't know if that got anywhere near your question or not but um
and there's definitely areas there so if you're singing a startup that would probably not be a bad one
so cool Matt I just want to say thank you this is a very important topic for me as well I've been in healthcare industry my entire career most of it in audit compliance and these doctors will straight up tell you I'm not take I'm not doing multi Factor cuz somebody's going to die right or you know um it's really real especially in the public safety period you know these firefighters EMS you guys are doing your job so I appreciate your comment about making it easy bringing it to them so I guess I I you pretty much answer my questions when it comes to supply chain you know vendors having that responsibility but um do you have any
other like specific suggestions about how to make it easy do you think it would be more like just uh security awareness training you know like having that that you know that that that handholding like how can we really drive it home to make these healthc care providers understand the significance of security um I'm still trying to figure that one out myself just to be full disclaimer here that's that's a really hard problem to be able to solve um so um I think it is kind of like a ho of Industry there uh so you're trying to get um you know security decisions built into uh the decision- making process for hospitals and purchasing process for
hospitals is actually uh really hard to do and uh there's a there's not an easy way for hospitals to be able to evaluate the security of their systems as well like you'll get a fact sheet from the the medical device manufacturer saying yeah we're Totally Secure it's like okay um uh so we're starting to see things like you know es bomb coming out uh software building materials uh for medical devices uh but even that um like you get a list of all the different software and device and it's like okay I mean what am I going to do to make use of this especially in a hospital setting there uh for being able to incorporate
this so trying to figure out how we start making use of this type of information in order to help influence uh purchasing decisions I think is a a really important area of research to be able to do to help kind of spur that there um I think hospitals themselves though are actually kind of really coming on board I mean they're they're being hacked at the end of the day I mean that's a uh tremendous uh motivator to be secure uh so I think the Big Challenge right now is that they're responding to um they're they're doing triage uh just like any other type of Medical Care there so they're responding to um you know the ta that they're
dealing with right now there so your standard as I said your ransomware they're really focusing on that if you talk to any CIO or C you know or you president of a hospital there uh they were going to you know mention their you know backup procedures their ability to be able to detect adversary um but um when it comes to these medical devices um a lot of times right now they're like no one's targeting them yet so we don't really that's not where we're going to focus on and I think that's an area that um really requires a lot of U work as an industry to really try to get these devices uh secured before the hackers
start focusing on them because you know once they start focusing on them that's really going to be a bad day so I really like want us to get ahead of that uh curve there so once again not really answering your question so I apologize but it's a it's a hard question to answer
there exactly
answer no matter what there's going to be some uh quote unquote provider can't even B call own we're getting a yeah so a gentleman in Theos in the audience here just said you know it was a furer confirmation that working in healthcare uh you know doctors and patients will just kind of do what they want uh that's a [Laughter] challenge so uh thank you very much I really enjoy talking here again uh I hope to see you again next year you have a good [Applause] besides





