Purple View
Show transcript [en]
hmm
the next talk is purpleview and this is hayden johnson and laura rafferty and without further ado
so before we do our talk i just want to mention these three guys all shocked that everyone's great great value they've added one guy's like oh i didn't know users should uh click everything like that like wow and then this guy doesn't even know you can log everything like four terabytes a second or something someone said so i thought although if we've had b sides here before at this exact spot i would look like an ass
okay so now i'll talk about our actual talk um so this is our talk on purple view purple teaming has recently been gaining attention in the industry due to the recent trend of using offensive and defensive capabilities together we thought a talk on purple teaming would be interesting so we hope to benefit those on the attack side the red team and the defensive blue team by mixing the two together
so it's gonna be a bit weird with us back and forth on the mic but who we are i'm hayden johnson i'm uh from australia we have really creative twitter names mine's at hayden johnson i have my oscp i just couple weeks before derbycon so yay and i have an offensive oh thank you any other oecps here oh wow yes there we go try harder you'll get it um and i enjoy speaking so we'll see how this turns out i'm laura rafferty my twitter is rafferty laura i have a master's in computer science for security and privacy and i have an interest in both sides of security and i love
it's not presenting it worked for me okay so first off why are you sitting here why have you paid money to listen to us to random talks it's on purple view what you can expect is an introduction to red blue and purple teaming and what each is we're going to run through an attack from gaining access to lateral movement privilege escalation and data exfiltration and we're going to show the red side the attacking side and the blue side i'm just gonna do this yep so and then possible purple team exercises i'm gonna have to that one yeah so the first definitions are for maybe people that are in school or new to infosec or just don't know or
you old people have forgotten a bit of memory leak the the and exploit is the thing used to gain access to a system so in our case we can use a flash exploit it could be a smb exploit or some something through that so that's what we mean when we refer to the exploit a payload is what goes along with the exploit and what happens in a computer or a system or a device when the exploit happens so you might want a shell command you might want to just run a dir an ls or print something but most of the time we want to get a reverse or bind shell metasploit those new people it's an open
source framework basically you download it's free you shoot attacks pretty much it's got like attacks from decades ago and famous meterpreter from oliver reeves is an advanced payload it does dll injection through windows natively and you can extend it with functionality as you want so when we refer to a reversal blind shell we just mean getting remote access cmd terminal or in unix it would be bash or something like that
so the red team has anyone heard of that term before it's not convoluted or like the cloud or anything what what it was originally a military term so from that the military actually use it to train as an attacker either like china or whatnot to test the blue team's defense so in this context it's meant to mean that it's used in the college cyber defense competition ccdc which are raphael margin everyone they test the college blue team defenders red team is for wargaming so we refer to them as like penetration testers advanced pen testing things like that they do the scans they do the exploits they do logic abuse so you shouldn't really need an exploit
within an enterprise environment you can just sniff the traffic or default passwords and they try to get access to things they shouldn't and hence the memes scan all the things blue team so us as blue teamers i forgot i'm sort of swapping between two heroes so sorry we block we prevent we defend we log all the things as the previous talks said we look at emails for phishing emails we look at events triggers networking and then we log more oh look at more logs the goals of red teaming as pen testing and whatnot to model recent threats and trends their red teaming are more longer term engagements they highlight gaps in security controls and whatnot and if
they're advanced enough they'll try to escape and evade persistence try to stay in your network longer and maybe model an apt
that was meant to be my uh timer for 50 minutes so the blue team goals are obviously to detect respond as much as possible and defend all the things identify gaps and for management try to get more investment so now we come to the idea of purple teaming at their most basic level the ultimate goal of both the red and the blue team is to help an organization to be more secure both teams have useful skills that could benefit the other to help them be more effective at their jobs so simply the idea of purple teaming is to use the knowledge between the red and the blue team to achieve this goal of helping the organization to be more
secure purple teaming has a focus on training security personnel in an effort to help identify and respond to attacks it exposes the blue team to different threats so they can identify and respond to them and they're also able to test their incident detection and response to live simulated threats observing or the red team observing how their attacks are or are not detected allows for the tuning of controls policies and procedures and also allows the red team to more thoroughly understand the impact of their penetration testing and sharpen their skills purple teaming can include live exercises so potentially sitting with a network defense team and educating them on a pen test arsenal exposing them to attacker mindset and tools
um also replicating attacks of a race recent apt or a threat and discussing how to mitigate and detect those threats blue team can also test traffic generation in their sim cobalt strike is an apt threat simulation tool that can also be used for purple teaming exercises and wargaming is also an option to do live exercises with higher level management so with purple tving we are analyzing the security posture of the organization and finding weaknesses then using them for scenarios or walkthroughs the idea is on training staff and tuning appliances so this allows for both red and blue teamers to understand the technology they're working with rather than blindly depending on tools this is different from penetration
testing and how it's not just receiving a report at the end and then finding the same issues in the next pen test instead it's goal oriented and tested live with everyone actively involved so being goal oriented it focuses on particular weakness in the organization instead of just vulnerability scanning microsoft uses their red team to identify the key points in this slide and to reduce the impact of these from here they can identify what areas could use more investment these will help identify and test security appliances it'll test if they actually work when the attack was picked up and how and how good the response is one of the major benefits of purple teaming is the exposure to practical
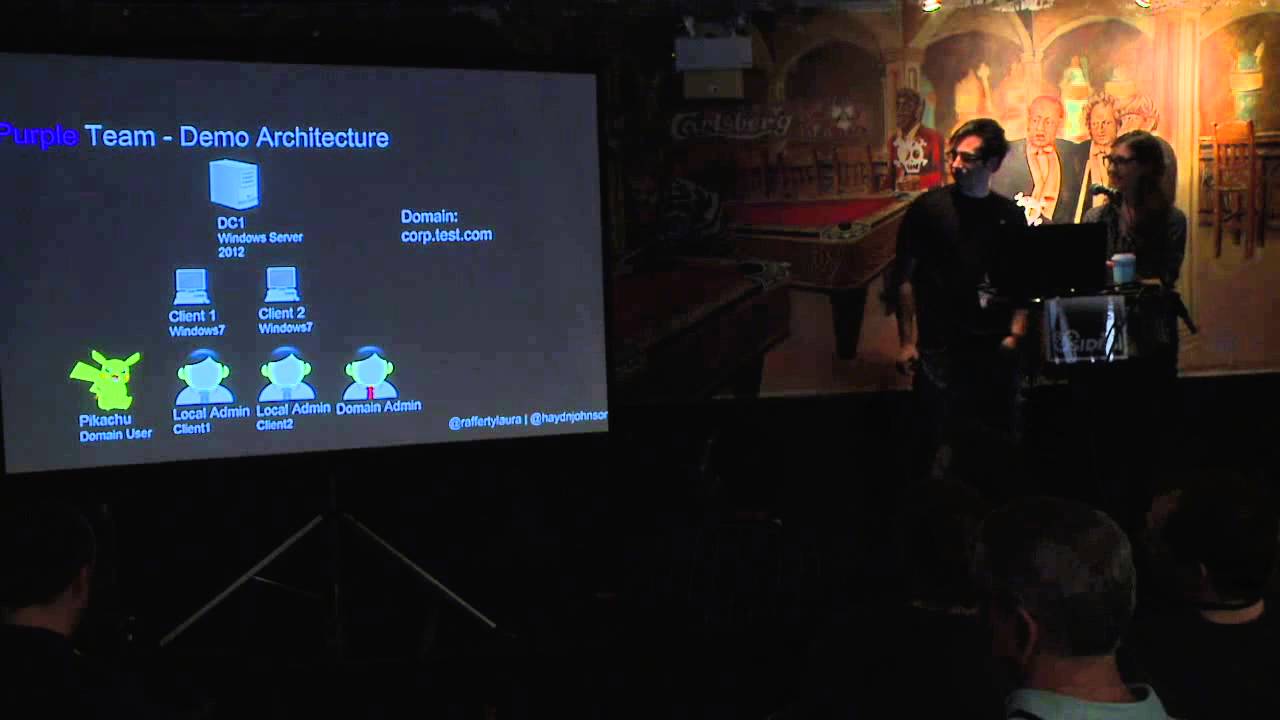
exercises as a team many people see events and logs but not many have live experience dealing with an active threat so this quote here just emphasizes that purple teaming is a real thing companies offer it as a service and companies pay for it so as discussed we're very simply going to show gaining access some lateral movement privilege escalation from local admin to domain admin maintaining access with a c2 and some data exfiltration so this is our demo architecture that we put together in virtualbox we have a windows server 2012 domain controller and two client pcs running windows 7. we also have one domain user pikachu as well as one local admin for each client and one domain admin for the whole
domain so first off the tools we use uh they are kali linux is a very commonly used penetration testing distribution that probably 99 of you use metasploit as mentioned before interpreter we're going to show powersport which is available on github it's a bunch of powershell modules twitter not twitter as a c2 backdoor and we're going to show wireshark some peak apps and uh security event logs which are amazingly hard to actually get set up to actually record so on our domain controller we set up group policies and active directory to enable logging for both successful and failed events such as account logon events and privilege use and we'll see this later on during our attacks which
generate these logs so first i'll start with the initial attack vector gaining access and here we're using a flat uh flash exploit from the hacking team from july so first i'll just talk a little bit about flash exploits so flash plugins are written in c and vulnerable to come and see attacks such as buffer overflows um you can embed a javascript binder or binary object within a flash file so this is an easy way to deliver an encoded version of an executable wrapped in a flash object shockwave flash files are also a thing a flash action script supports events and can be used to redirect to a malicious url you can define an event for example
hovering over a flash object and then when the event triggers redirect the browser to a landing page so most exploit kit landing pages redirect to pages containing flash exploit objects for example the angular landing page supports different versions of flash exploits and delivers exploit after scanning the browser version and flash installed on the victim's machine so since flash is installed by default on the browser is a good entry point into the system new vulnerabilities are identified on almost a weekly basis and actively researched by attackers there have been several zero-day vulnerabilities for flash during the past few months so here is just an overview of this attack we gain initial access to the corp.test.com domain using the hacking
team zero day flash exploit from july 2015. we imported the metasploit module for the flash exploit on our cali machine we're assuming that the user was redirected to this page through a phishing email which we just skipped over that part for interest of time but the client is using an old version of flash vulnerable to this exploit when the client connects a session is established and we're able to get a shell on client one so here is the flash exploit we used available on security focus and on the client machine we have flash version 18. so here we're just setting the options through metasploit we attached the payload into metasploit and shows the ip of the attacking
machine and the ip address of the web server as well as the port 8080. we set a reverse tcp payload set with the iap address for catching the payload with and the port number 4444 so here we start the exploit hosted on our web server and wait for the victim to navigate to the page uh here from the client pc we see the user navigated to the malicious page in internet explorer and then is redirected to the page infected with the flash exploit for illustration we made a redirect button but in real life this would likely be hidden to the user who would automatically be redirected in an iframe although a lot of people like to click buttons so
probably they would also click it um yeah in the instance of a real attack there would be multiple redirection gates and gates so upon redirection the client is connected to our exploit and an interpreter session is established with the client pc this shows the attacker sending the exploit and simply receiving a connection from the victim in this case the 102 address which is client one so now we can run commands such as get uid and see the the user is pikachu on the corp domain now we can also successfully drop into a shell on the client one pc so we've gained initial access into the network and have all the functionality that um interpreter session provides
so here's the peak app you can see that the user connects to the slash redirect.html file and it uh they click the button the fabulous redirect button and then we're delivering the payload because they redirect to our page on 8080 and then that's what you can see from the client side so as you can clearly see it's a flash exploit so it's pretty easy to correlate and then the three packets on the bottom are just a meterpreter session beginning so it sounds like a thousand packets or something once it connects and so what you can take away is that you can instantly install security on you it's free it's a linux distro with some great defender
tools including snort you can then confirm is if flash is needed in your business a lot of people will say yes i need flash to run my cat videos but do you really need to and because it's one of the most common attack vectors i would advise putting flash in your patching cycle as one of the top priorities so that it's patched as soon as possible we did find some snort rules uh we were unable to get them working snort due to time constraints but they are available and that's actually relevant to the same cvs the flash exploit we just showed you so from this purple team exercise the blue team understands how an attackers
can gain initial access flash exploits are an ongoing issue so this helps the blue team understand what suspicious traffic looks like and what is happening from the attacker perspective the red team sees how attacks are visible by the blue team and they can think of ways to make it more stealthy for example iframes automatic redirects or different types of payloads next we would have a privilege escalation but we're skipping this part for interest of time i'll quickly just mention it as a critical step so we gained initial access as a domain user and we will then escalate privileges to local admin to perform the next attack and privilege escalation from local admin to domain admin will be
discussed in a future section so our fictitious attacker now is a local admin user on client one uh privileged escalated from pikachu and now an attacker will want to get situational awareness in your enterprise network so we're just going to show you anateca they're attempting to move around and using powersport to do so in order to get a reverse shell on client too so the very first thing is power supply it's open it's free from github it's open source and it's developed by manifestation so a lot of powershell modules as it says it says it's focused on all stages of a penetration test or a threat simulation but it's more focused on post exploitation and uh being stealthy or not writing to
disk is what it mostly claims if you do want to try it out yourself it's on github i would also suggest using power view because nua and it's run through powershell empire which was released at blackout so it's open source free as well and then you can be elite hacker with the big guys the main reason i wanted to show this type of lateral movement is because sean metcalf ads security.org released an article on october 14th i think and it's one of the top problems he sees in enterprise environments is that the same password can be used on every system so local admin one two three up to three thousand however many clients you have so it's almost a pseudo
type of domain admin so once you get local admin you can just move around quite freely as this uh nice nice little diagram laura created you can just jump from one to the other quite easily so our setup was um that power i normally read off the slides anyway but um we are going to use powershell to connect from client one to client two because we already have a shell on client one and in order to do that we're gonna remotely connect to client two have client to connect into the internet so the malicious web server download a power script file and execute it in order to execute our payload to the attacking machine so that's just that simple diagram but
if you're on the internal network you would probably be easier or stealthier to just connect to your own kali web server if you're on the internal network so we're going to use a powershell command that's used as an iex cradle this command tells client to to download from our malicious web server the powershell script that we want to run and then use the syntax for the interpreter windows payload on port 443 and the ix cradle actually meant to execute it in memory so for those wanting to replicate this i suggest base64 encoding the payload because there can be issues when transferring over the wire due to white spacing or some random null bytes or something even though
they're not sent but you can also find this technique in the the hacker playbook number one there is a number two now but the url is just down there so for client to download the power shell script from a malicious server we need to upload it or have a web server there so this one's just to show that we've uploaded it and it's in a plain text right there so to connect to client 2 we'll use the invoke wmi method because that remotely connects to another machine and it's the windows management instrumentation methods we will then pass along when the win32 process which allows us to create a windows process if you use python it
would be similar to using just the subprocess command will then execute and run via the terminal so the example here is how we simply launch notepad we we use the wmi invoke with the argument win32 and then we just create a process argument one notepad actually so it's quite simple so using wmi we create the uh the command and create the class the process name in order to execute the base64 encoded command with the powershell.enc in order to decode the base64 command also this is some way to maybe bypass ids but i doubt it we then um use computer name with the ip address to connect remotely and then the chronet credentials and once you press enter it tries to
connect to the remote machine ask for client whose password and being the same password as with the issue i mentioned before we can just easily execute it and gain a shell so we set up a listener to catch the reverse shell with metasploit as it connects to the attacking machine we receive the shell and it automatically migrates from the internet explorer process because the ix cradle will execute the command and then close it and then we lose our shell so you really need to quickly move to another process and then we just use the getuid and we're the admin on client2 using the same password so from the blue side we're looking at our wireshark traffic and here we can
see the tcp handshake where the client1machine.101 tries to connect to client two which is 104. uh below that we can also see bind requests between the two here we see name queries for client two as client one is trying to connect to the right machine client two acknowledges that and creates a remote instance establishing a connection so this is suspicious traffic because a local admin really shouldn't be trying to connect to another machine and then trying to create an instance so here we see the two machines talking to each other with a power shell command which tells client 2 to download a script from the cali machine and then sends an arp request asking where the cali machine is
so on client 2 you can see it reach out to the web server and download the shell code below that in plain text you can see what the powershell script actually looks like once that's executed we can see meterpreter executing through https with tls connections which is interpreters using its dll injection to create a shell sorry when we set up the gpo policy and we looked at security logs i was actually intrigued because in this screenshot we can see the initial connection from client one to client two with this logon id and the reason this is important is because on the next slide you can see the same logon id executing powershell that would be very suspicious if local
admin was connecting to local 2 executing powershell on it you would want to know why and then we can even see what's even more suspicious is that after that the power powershell connects to our attacking machine on port 80. so so that's actually pretty interesting because it's like what the it's a good trail to follow and powersport is meant to leave no trace and run in memory but it's obviously leaving something there so what you can take away is that this uh powershell command is connecting to a third machine internally and that this would obviously be suspicious um ah let's get this one so based on the security events you should correlate them and a sim should
do that or can do that if you have it set up correctly you can then test the sim to see if those events will be picked up live and someone's logged in from this thing and there's log md which are is really great for powershell because there's been some videos at derbycon and whatnotware or torx where they remove powershell off the machine still run it through the the powershell.exe and then there's meant to be no logs but log md works better and records it somehow i haven't looked into it too much but it's a great recommendation for for that side of things the benefits of testing later lateral movement is to identify and confirm that
your defensive controls are in place within the network so is malicious traffic being picked up things like network monitors ids ips packet inspection and you want to confirm that what you've paid for your blinky box is actually a providing value finding out that you have x in place xbox and x does nothing it is a great save before being puned so it's actually it's great to test these things live and for management it's really good in gaining justification for more resources so the whole enterprise thing like last five years or so it was let's buy all the things but not hire anyone to run the things and we need to break that trend so next i'll talk about privilege
escalation uh this also shows lateral movement however the focus is on grabbing the credentials off another machine so first why do we want to escalate privileges to domain admin domain admin privileges give ultimate control over active active directory and all computers connected if you have this these privileges you can access tamper with or destroy ict resources alter or disable security policies and auditing evidence of any action on the domain also you could create new accounts with administrative privileges on resources which could be accessed at a later time as well as place malware on any machine to achieve any variety of tasks so here we already have our connection from the cali machine to client one and
we have local admin privileges we've also observed that a domain admin has actually logged into client two so now we want to grab their credentials off of there here we're using mimikatz which has some features for reading hashes and passwords from memory we're running it remotely from the client 1 to the client 2 pc using ps exec and we need to send over our dll file to client two in order to extract these uh the passwords from memory on the client too so first we map the shared drive on client two to client one send over our dll file and then run memicats get the credentials and send them back to the cali machine so here this is showing on client one
where we're mapping the client to admin share and copying over our dll file next we use ps exec to run memi cats remotely on client 2 and then we use the privilege debug command to check that it has the right privileges to dump passwords from memory on client 2. then using our logon passwords command we can dump the plain text credentials stored in lsas memory as you can see we now have domain admin logon credentials from the client to in plain text with our secure password it's been discovered so from the blue team's perspective so from the peak up we see the two machines connecting asking for the secure the dll file so it copies it over and this would
be suspicious especially if it's named the exact dll file we can also see client one logging into client2 as local admin is using the same password again the same issue we've been discussing so it's just a quick screenshot of that is also the next one is we see mimicats.exe being run on client two from the admin share that was um mounted on client one with the source address of client one so this would be very suspicious so i don't imagine local admins having to run mummy cats for any reason we also have an event for sensitive privilege use on client two where we can see that pigs ps exec is uh being executed so it actually
logs that which is uh really good even though we had to set the gpa settings and click click yes on everything it can pick it up if you don't just leave it default logging nothing and considering this is a short time frame between client one and client two connections you you would notice that it's quite suspicious so blue team takeaways from this exercise first of all prevention ways that they can improve process processes the blue team can consider access control for the shared drive which we mapped on the other pc um you could also limit access to ps exec and monitor use um you can consider active directory best practices for permissions to prevent privilege
derivation across domains also a domain admin or any other type of user with sensitive privileges logging onto an infected pc opens up opportunities for an attacker to perform privilege escalations such as this so from a defensive architectural perspective it would be useful not to have a situation where a domain admin would be accessing a client pc at all also maybe accounts could be created which only have minimal privileges that are required in terms of detection you could create ids signatures to trigger on the dll file we used mimi cats or ps exec you could create a simus case looking at event correlation between system logs and network proxy logs for example if a domain admin logs on through rdp and
then transfers the dll file such as this for lateral movement you could enable file level auditing on each system to monitor file modification so the logs generated from audit logs can be correlated with network events and logs the blue team may also consider implementing something such as canary accounts which are unused accounts specifically designed for bait and will alert if they have been accessed so this would allow the blue team to detect this type of attack right away so through this purple teaming exercise the blue teaming becomes familiar with the attacker mindset and path they may take for this type of attack the red team sees how their attacks are observed by the blue team and any
artifacts left behind they may wish to clean up the dll file and unmap the network drive after to leave less of a footprint when observing the blue team's detection and response processes they can also provide more thorough recommendations by identifying gaps in their processes so after getting domain admin in your enterprise a attacker may or should want to establish assistant persistence or maintain access in case of a reboot or their shell dies so in this example we're going to show twitter which is a back door using twitter so twitter can be downloaded on github it's another open source tool it's actually easy to use it's easy to install it's just python files and we were actually able to send it shell code
to launch an interpreter meterpreter shell so and on my um corporate workstation antivirus didn't didn't fire at all so from here it's just a python file and it uses subprocess that's how it executes the the cmd command that you send it so directory listing or ipconfig whatnot it then stores that command in a base64 encoded message on twitter and then the client pulls it down so if it's written in a python file not many windows machines should have python installed by default so you need to turn it into an executable how do you do that you do that with pi installer free on github again easy to use so pi installer will take the script
you've written or any script you steal or find on the internet take all the modules and things you've imported as well as the python interpreter itself and we'll put it into a single executable for you to use which is pretty awesome so for some scripts on windows we don't like to write in a batch we'll write python file and turn it into an executable much easier so the scenario here is that our kali machine wants to maintain access so it sends a command to twitter or twitter the api then sends it to the implant which is our python executable the python executable receives the command runs it then sends the output to the ipi which then sends it to a twitter message
and from there you have to manually retrieve the command so in this example we're launching the python file and then you write the exclamation mark cmd and the mac address of the bot because it automatically tries to find your the bots like a zom a zombie net or whatnot botnet and then it'll send the command up to the api it runs it puts it back and you're given a job id which is like a random string and then you just use exclamation mark retrieve as part of their syntax and the job id and it pulls it down for you so on this this one i think we just listed the directory no this is the one with the directory
listing so that's uh exactly how you get it to run you just retrieve it with a job id and whatnot there you go there that's yours so from the blue team side it's really interesting because mostly it looks like normal traffic all we can see are multiple requests reaching out to the twitter api um which is pretty normal um since the python executable was compiled with the no console flag when it's running it shows nothing on the client's desktop visually it's just running in the background and so here we can see headers with the twitter api the internal ip addresses and you can see which ips it's communicating with in the actual packet it also says the ips it's communicating
with and you can see the machine that's infected by the destination iep address so what can you take away from this say is it against policy should you be able to connect to twitter you know a lot of organizations they're blocking twitter and github for example i was able to use a powersport one on a live client system and i actually keylogged it that worked um you can then see if your arc site or your net network traffic tools monitoring tools actually picking up known ip addresses or malicious that you've actually put in also because twitter is meant to act like a beacon so it beacons every 60 seconds or something it'll be randomized it actually doesn't have that
functionality so it's actually constant connection so if you have anything being after hours or any constant connection to twitter when it's blocked it may be suspicious you might want to look into that also your browser may block it but you may be able to connect via the api so there are still different ways that they can get around what you think is being controlled and then the purple benef purple team benefits of this is does anything alert of something beaconing out any hunters threat hunting that want to go look for it look for malicious ips can they find it and what not and then just live testing as all the other purple team slides have said
before it's just testing your defending staff as well as the actual appliances so making sure it actually does what you think it's doing so some simple data exfiltration our attacker now has domain admin access they want to find some data and they want to get it out of their network so we just wanted to show some clear ftp data exfiltration and then if you want to follow along at home that's fine because this is being aired to the internet not but our situation was that we have a kali machine with meterpreter session as domain admin we are looking for some data and we're just going to send it to our attacking machine in ftp with clear text
so with our clear text ftp session we are looking for some important data we found a folder called imp underscore data so that's pretty much all i could show from the attacking view was you've now found it and you can write a script that searches for file names such as pass or password or usernames as most ransomware loves to do because they like to chase the extension the file name or the extension and then they'll encrypt it that way but in this case we've just simply browsed to a folder with important data so here we can see when we list it the important data is some pii through am underscored contacts and some very rare
pokemon jpeg and images we should have had some um rare pokemon though i think instead so quick show of finding the data so on windows when you have a shell it's mostly non-interactive if it's remotely and you're an attacker so when you write the ftp commands when you log in great and then you can't do anything else there it just shuts down so windows has this great ftp.s flag or syntax and it pretty much runs in text file as a pseudo ftp script so you simply place your username password and the files you either want to download or put onto the machine and then you run that with that dash s and it just runs it as if it's like
interactively and it downloads nice and easy so here it downloads our pokemon and then we simply close the connection and then here's just a screenshot to show we have our pokemon in our ftp home directory so from the blue team side we can see the dll injection on wireshark and also lots of chatter created on the network we see everything is in clear text so we can see the ftp response and requests is not stealthy at all the user name and passwords are also in clear text right there and then here we can see successful file transfer and our pokemon are all being stolen off than ever
so the simple takeaway from this talk is if you want to go home and practice is that you want to test if a simple ftp transfer would be would trigger on your network so hopefully by default your security appliance or whatever the vendor has sold you would see this so you could then test to see when it's picked up if if that's after the data's been sent out or when the data's been sent out so you can have a look at that and then if it is picked up what is your ir process so the investigators that say hey we've seen this did did they respond urgently enough did they just see the alert and
go oh that's another alert overflow who cares sort of thing and then you may want to create or block ftp i don't really see business use for ftp but if you do have one you may want to just create a group for ftp and whitelisting remote ftp servers would be great internally would be easy to to whitelist so purple team exercise again as we've said on all the slides it's all about training testing what you have and if it triggers when does it trigger you may want to swap it tune it to your environment so if you're used to seeing 30 30 megabytes be sent out set your alerting higher your threshold higher maybe 500 megabytes or
a gig or something what not and just yeah play around and have some live exercises so in conclusion we think purple teaming is really good you should invest in it and it's probably the way the future from pen testing to red teaming to adversary threat simulation yep so if you are going to implement purple teaming there are different stages you may want to do it quarterly with just the wall rooming and drawing it up theory based you may want to do six month live exercises and then yearly you may want to involve the executives so from from like a business continuity management perspective you may want to do the whole war room thing where we've
we've been infiltrated detected here the execs decide oh crap our data's being lost what do we do and sort of the whole organization gets involved so in our talk we showed an example of a purple team exercise showing both the red and blue team perspectives of an attack on a network we've limited our scope of detection tools to windows server event logs in wireshark however we're interested in extending to enterprise security tools such as sam or ids future work could also include exploring powershell and wmi for blue teaming defense purposes as it's an incredibly powerful tool which could also be used for monitoring and detection also from the red team um we could have more
advanced attacks and persistence using powershell empire and i promised via twitter and obligatory however you pronounce the word a cute cat picture so here we go so we hope everyone are at it yeah we hope everyone learnt something from the attacker side the blue team side and mixing the two so thank you very much
questions yep so i mean i know more about this subject better than all the other presenters
uh so here's the question is i wonder if you're a little too casual when you talk about the blue team side so for example from the standpoint of the uh sound by stack on the network side right yeah okay you had some arb stuff you had obviously ip address based detection you had smb you had you know a shockwave flash payload response you had user login stuff i mean this is crazy correlation right yeah but as a human being okay maybe but i mean is it if i was to generalize this in any way
the question was is there any one application or security appliance that correlates all logs all network traffic everything and apparently not yep
resets a workstation and then you hijack the local like that that tech admin which then uh would hijack the domain admin and apparently rodc's are really good apparently because domain admins can potentially have um don't believe the uh admin credentials in memory stay upon reboot right so this would probably be cash the lss process yep so the read-only directory domain controllers yeah definitely susceptible to that yep
would you say that it's more valuable for the blue team to be unaware that the red team's
i think there's more value in them knowing that they're attacking because um in this exercise we would actually have the blue team sitting with the red team while they were doing their attacks so they could understand it better so yeah but with that it depends on your objective so if you want to see say your current state that you think you have you can then run the red team and the blue team not know whereas the purple team idea is that based from that from the blue team not knowing based on the gaps and what you've identified what got through what didn't how what the ir response was there would be great value in then
training based on that and then trying it again with them knowing together i think would be the best way to mix and match
i don't know i'm not twitter but uh it's not very stealthy at all it's just a connects to an api and then it connects into your accounts twitter messages and leaves it base64 encoded so i don't think privacy wise they can read your messages although they probably read everything so i'm not sure why twitter hasn't blocked it maybe those are changing the api but you just need the authentication tokens and the the correct credentials for the api to work and then it can send the traffic
an external red team yeah yeah it would be great that would be like various group advances
yeah exactly it's microsoft or whatnot had that tested your and know how you pronounce it but yeah there's not many places that have an internal red team
you