LTE Security: Facts & Fictions

Show transcript [en]
when i saw the submission come through i started geeking out and asking everybody who is this guy would you so i'm looking forward to this talk
so a uh a little bit of a quick story uh when i so so admitted here i thought that i was submitting to a town it's about two and a half hours from dc okay jefferson's house yeah and so i showed my uh my uh my uh girlfriend you know hey i got accepted here and she's like man that's kind of a long drive and i was like oh what no no yeah charlotte uh and so uh which is not charlotte's bill so uh so that's kind of how i got here um and i'm super excited to uh um so um so today we are going to talk a little bit about oh okay cool um
okay whatever um so today we are we are going to talk about lte security um there is a much longer eight hour class i have developed about uh gsm um ts and lt and lte but this is basically a small and quick dirty intro to lte networks and lte security and we are really going to look at it from a standards-based perspective you see a lot of different security claims about uh about lte and there was one that was really really bothering me and i was this whole notion of end to end lte so security uh people were basically saying that you know lte is in is is encrypted from start to finish and so uh
i want to show some of the yes the uh the uh standards later and show why that's probably not true um and you can make your own uh uh judgments but i'm just showing you the uh the standards and uh basically providing some evidence about my security claims um so we are we are going to to talk about different cellular standards important cellular concepts uh lte network architectures the security architecture and then i'll provide some uh some stuff for some further some further reading so i am josh franklin from dc 27 i'm totally 6-3
so yeah i do i do work at a nist i i focus in public safety networks mobile security hardware roots of trust and electronic voting so that's kind of all of the stuff i work on so what is lt lt lte that is the uh the long-term evolution that is the fourth uh i can say four it's 4g whatever whatever that means um it's uh basically being deployed worldwide um it's really really nice that we're starting to have a nice worldwide cellular standard before uh it was kind of fractured you had gsm cd cdma europe really really focusing on one us sort of having our own little fight about one and then we had whatever japan was uh doing
um yeah so uh uh lte super super cool it's probably here to stay for a long time and so it's uh it's definitely worth your time in in picking up some some lte knowledge here lte is is basically always evolving there's a standards group called 3gpp that uh that actually develops these uh standards and they uh drop new releases which is basically we have you know 400 documents and we're going to stop adding the stop stop editing them now and that's called a freeze or a release and so uh uh uh lte release 12 is actually coming out in december 2014. um you know there there's uh gonna be you know lte advanced and then what is it
lte b is what i i uh here re-referred to and basically every new drop has different features um
um
standards so 3gpp is the standards body that is that is actually developing these uh standards the same standards did both gsm and umts these are completely open and uh uh viewable standards it's not like it's not like iso where you have to pay you know 45 frames or in swiss frames to like or whatever it is 3gpp is actually made of six different standards development organizations um that are basically from different parts of the whole world um you see arab there uh addis is the uh is north americans uh you see etsy there also and that's uh uh europe's and etsy does a lot of the crypto standards and so a lot of the uh
the crypto is basically going to have um
there are other organic organizations 3gpp 2 which is the most confusing name in the whole world uh develops cdma um in their whole their whole line and there's also the the ymax form which developed ymax um 3gpp 2 just you know a quick uh note was developing a cdma variant of um of 4g uh and it was called umb and thankfully they stopped and so you know america's all moving towards the same tech knowledge there now um a note on on on on all of this uh 3hpp has technical reports which are kind of more like book reports and you know analyses and then there's there's actual technical specifications which are re requirements documents you'll probably have to read
both um some other standards use lots of jargon and and uh abbreviations frequently nested acronyms are common and this is one of the fun things i have found a three a three depth nested acronym i was you know i'm really really curious if anyone else has seen any you know anything that goes further so for instance uh g-ran stands for gprs evolution radio access network and gprs stands for like general packet i forget which what gprs technically stands for so i've seen four of those though and so you know uh let me know if you find anything deeper open challenge open challenge um so packets and circuits previously uh um any voice technique like basically any
voice technology was uh basically using a circuit for communication which is basically fixed fixed uh bandwidth you know guaranteed bandwidth um uh and you know that that actually happened with the pstn and and it happened with uh gsm and and um ts and so basically if you wanted data you had to have distinct data networks and so you had a gsm talking sorry a gsm voice traffic going to the core network and then you had a distinct gprs packet switch network that had to converge on the core network and so lte is really really different there lte is completely packet based which is really really interesting there is volte which is voice over lte um
sorry voip over lte um which is another that's the third that's a third level ness of acronym right anyway um so a voip is but is but one way of doing voice over over lte there are a bunch of of others um right now if you do make a call on lt on lte you are most likely falling falling back to either cd cdma gsm or or umts so it's not actually implemented nationwide yet um so the big lesson here is lte is completely ip based which actually uh means that uh once you uh like you can do a lot more with with lte networks now that it like now that all the uh the different offensive
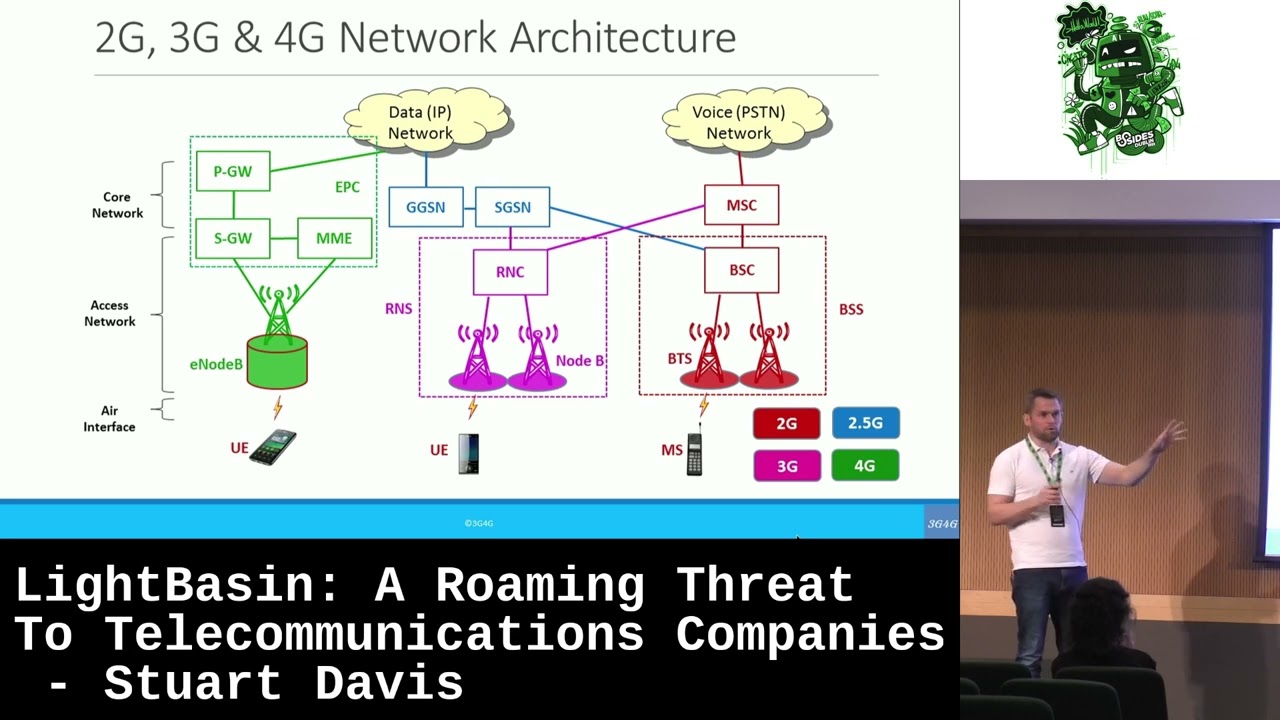
tools you know are all tcp uh you know you know pack a base basically whereas it's very very different in the past the cellular standards this is how i think of it you have 3gpp circuit switched which you see the the the gsm 2g tech and you see the the umts 3g tech there in that one column you have the 3gpp packet switched um which is gprs edge hs pa family there's a bunch of those and then lte 3gpp2 has cdma1 2000 evdo the now dead umb and wi-fax's wi-fax why max is quickly dying um and uh because basically sprint uh invested heavily in that up up front and they are now transitioning to to lte these are the primary documents
that you should basically be aware of and i would just recommend reading the first three if you're interested um it's not too difficult that's probably 200 pages you know you've probably read longer books in ninth grade right um yeah yeah so these are yeah this is just a quick little collection here we're going to zoom in here and mostly we're going to be discussing uh 33.401 and that is the specific version that i used for this presentation this is the primary lte security architecture document and you can for the most part read the first uh 20 pages without much difficulty and that's probably where the most important portion is so you know give it a quick look um it's
really confusing to to download these uh standards fyi they're going to be downloaded in a zip file and that's the only way you have to then double click on that and then open it up it's super awful so just fyi with some instructions uh so here's the big picture in case you you like really haven't looked at uh cellular networks before um so mobile devices connect to a base station which is those giant and and and antennas in the sky which connects to a core network which is basically run by verizon uh att sprint uh which then you know connects to to the internet or or uh other cellular networks or or the the public switched telephone
network the portion between just the base stations is called the radio access network the iran and you're going to see that term kind of be evolved there is a g-ran a utran and eu tran uh and so uh rand you know just just just be aware of that that is a collection of of basically base stations um as we said base stations are permanent cellular sites oftentimes they are disdisguised which is kind of funny when you find one of one of those they sometimes look like rocks um or like uh they like put trees around them so you don't really know that they're there um sometimes they can you know run off of gas like gasoline if they're like
like way high up in the the the mountains um uh it's just you know interesting when you when you come across one uh next time you do take you know take take a look and and just you know look at the different types of locks and just be aware um so base stations uh sometimes co co locate different uh uh carriers on the same uh uh base station so you might have a t uh at t buying time from sprint or uh buying time or space from uh of verizon so a base station doesn't necessarily have to be just one one company and base stations are often well base stations are connected back to the the core network via a link called
the back hall kind of pointed to it there and that backhaul interface sometimes is a fiber sometimes it's satellite uh sometimes it's microwave it all depends on what uh sorry most definitely t1 yep yep um you know it's it's basically however we we can get the information from the base station back to the core network uh mobile devices your your typical mobile device uh and whenever someone talks about mobile devices they want to take out their phone and show you right i really want to right now for some reason i know you all know what a freaking phone looks like uh so uh my my mobile device has anywhere from like four to six different uh uh
radios in it um you know wi-fi gps bluetooth uh uh you know possibly a bunch of different uh cellular radios um and so just just kind of be be aware of of that um in in lte terms bless you uh a phone is called a ue a a user equipment um and this uh this user equipment has a a uicc which is often thought of as a sim a sim a sim card uh this uh this uh this a uicc is actually running an application on on top of it called the uh the uh the uh the uh you sim and so that's just sort of a big difference from a couple years back um
uh sim and using are kind of used interchangeably but they are very very different now it is um subscriber identity um mc you've probably heard this when you're basically hearing about stingrays or you know mc catchers uh mc is basically you're uh on the cellular network it is uh your personal i identity uh it defines who you are um it is a 15 digit number uh stored on the the sim card or you sim card whatever it can consist of three of values mcc mnc msin we'll we'll take a look at that in a moment a lot of times uh carriers try not to send the emcees over over the air if they don't if they don't have to and so
they'll use a temporary identity called a uh a guti i don't know if that's how it's said that's how i say it in my head a globally unique u-u-u-e identity or a tim c again i'm not sure if that's how it's said temporary mobile subscriber i identity and these are all different from your actual phone number right your actual msis dn this is what an mc looks like and how it's kind of broken up it's just interesting to note that uh europe may use a two-digit value for the second thing there for the uh the second range um yeah this is what th you know just this is what all the fuss is about um
uh but i mean anyway um so uh ue identity um your actual phone has its own i identity called the actual imei the international mobile equipment i identity it is a 16 digit number you can actually look at it right now by doing pound zero six hash on your phone and it'll it'll probably pop right up uh for our our uh sorry sorry star zero six hash my bad um don't want to confuse our british friends um and the actual imei is often used most often used to uh to uh blacklist phones from a cellular network um so so if if someone steals your phone they can blacklist uh at t can can can blacklist that phone
from getting on their network it is um it is illegal to change a phone's imei in many in many countries for that reason i don't know about uh our country um usim cards these are basically and if if what if what i read is true this is the single most popular smart card in the whole world over seven uh over seven billion in circus circulation um they actually store cryptographic keys i mean that's their primary duty here right is they are long-term cryptographic key storage uh in a secure area they do house a processor that actually runs an operating system and uh and on on top of this operating system there is a uh stripped stripped down
mobile mobile version of the uh the java virtual machine that is used and and it and uh and uh it can actually run apps like you can run games off your your sim card which is kind of cool um and will totally not be misused by anyone ever um yeah oh yeah and like we were saying here sims are deprecated the modern term is usim so you may remember cdma did so basically a verizon used a soft sim um they have now basically you know made this huge change in their network and they are now using uh you know hard sims now um and sprint is changing from imax to lt i already went over that um here's what a sim card
looks like uh there are a bunch of different types right um we're really just removing plastic for them for the most part here in this picture um the the uh the uh yeah i'll remove plastic i don't know what that means um so uh the actual metal part is more or less the same the contacts are a little bit different um oh yeah uh sims um if you if you roll an android you are probably using a micro sim if you roll uh an iphone you're probably using a nano sim um makes it real hard to go back and forth um so lte networking here's here's what we're really here for remember it's a 4g
data and voice tech analogy it's basically split into three different portions any lte network the actual radio network which is called the the eu tran i don't want to try and go for that giant acronym uh the actual core network the the uh evolved packet core and the uh the uh the uh the uh ip multi multi media subsystem we're not gonna talk about the ims because it's kind of con confusing and we don't have enough time here and if anyone has any questions you know stop me let me know um so we're we are really going to to to focus on the interaction between the the actual phone and the base station i know this looks awful and horrible
let's talk about it for a moment and then we'll go into a nice pretty picture i promise okay um so the actual ue is the lte device uh in lte parlance base stations are called evolved node b's which is an awful name um so e node uh b's or e n b's you will see it written three or four different different ways just just just know anything with a b on the end is probably a base station um that's just you know uh so the uh the mobility management entity mme this is a really important box on the core network it is uh it is a server that is um uh that is uh basically doing all the
all of the authentication functions and all of the con like all the different control signaling allowing you on the uh the network saying you know you can go here can't go there uh the serving the serving gateway um is the uh it's it's uh basically the main route that user data passes through it's just it's just another server on the their network um it does do handoff between other 3gpp networks and so if you're going from att lte to verizon lte then if if there was a handoff that had to be done because you're going down a highway at 60 miles an hour and you have to switch from this from this base station to this base
station uh then uh that actual handoff would would occur at the us the the serving gateway the uh the uh packet gateway the p gateway uh allocates ip addresses and so yeah all your phones have have nice ip addresses now that uh now that you're on lte um the p gateway does hand off between lte or sorry between three gpp networks and non 3gpp networks so if you were trans like if you were handing off from at t lte to verizon cdma uh then uh that actual handoff would occur from from the p gateway the home subscriber server and the authentication center the difference between these are very minut i don't even talk about it i just
kind of mention them in the same thing they actually reside on the the mme and they they actually hold your long-term cryptographic key k we'll get into that and the actual mc and then ims which is kind of confusing we're not going to talk about that so here you can see we have the the phone and through some awesome lightning bolt graphic there it goes to the the base station from the the the base station control signaling is routed from the base station to the mme and as like this is where all your all your authentication information is stored at and the serving gateway is where all your user data is uh is put through um
and so from here we would go out to the internet or the the the the pstn and this is just a really basic lte network it's not really mini you know there's not much to know here um which is which is nice right um so um for communication between the phone and the uh and the uh and the enode b and then the core there are there are uh cellular specific protocols as you might as you might as you might imagine it's it's a cellular version of tcp ip right and in and in in reality tcp ip actually is you know runs on on on top of all of all of this which is which is which is nice um
so we're gonna we're gonna take a look at uh at some of these protocols here let's zoom in on the far left side so lte uses different communa communications planes primarily you should just think of three you have a a a communications plane for user data my phone to the base station to the court to the core to the core network that could be voice or whatever you're looking at um there is control signaling between your phone and the the base station right because the the base station has to know where your your phone is it has to get tracking area updates it has to you know do authentic authentication uh it has to to to say
hey you're being a little bit loud simmered down right um and you know there's actual control signaling for that uh and then there has to be control signaling from your phone to the core network um and so there's that's basically three distinct uh uh planes here um cool uh so we're gonna look at for a moment uh these three bottom uh these three bottom ones so rrc uh basically provides control signaling between the phone and the enode b the pdcp protocol packet data conversions protocol uh does uh in encryption and and it actually gets uh like it basically takes all these the signaling above it and then encapsulates and then frankly just you know encrypts
it or or uh or in integrity protects it the uh the uh the rlc um it actually readies ready's packets to be transferred over the air interface and then the actual mac layer does multiplexing and quality of service and then physical you actually have you know uh electronic uh bless you electronic transmissions you know gallivanting over the airwaves um so here are the control protocols and and and a lot of these protocols are sort of re repeated here and that's and that's fine this is just how the standards documents explain it so you have the the control protocols um which is the nas security which is the which is the non-access stratum super confusing name uh it connects your
like this is that uh that uh control signaling plane from your phone back to the core network and then you see rrc there which is control signaling from your phone to the actual base station and then simply simplified much more is where is what your your data would traverse is just these four protocols here interfaces um that nice diagram that we had earlier um every single thing like every single interface every single connection between um between a a server or a network component has its own unique identifier basically and here are the main ones that i want you to know for lte so and requirements we'll we'll say things like the actual you know it'll say the x2
interface which is between um between two base stations the x2 interface has to you know has to have this much in encryption or you know has to be protected by these by these uh means and so what you really need to pay attention to is what's going to confuse you is the is the uh s1 interface has two uh has two separate interfaces i don't know why they just didn't call them two different s1 and s2 so the actual s1 mme is the the the control plane uh signaling interface and then the s1u is the user plane enter is the user plane uh information interface security what we're all here for so there are a couple of different
security mechanisms in use here the actual usem token right the actual hardware token uh authentication and key uh agreement uh which is how your phone gets gets authenticated onto the the uh the network and that's really what what what a lot of um a lot of people that say black hat and defcon have been you know breaking over over years past and then we have crypto lte you know has its own um you know like basically has its own encryption and integrity uh cryptographic algorithms um so we're gonna talk a little bit about that um high level threats to lte there is a document and it's one of those tr's and you should probably go take a look at it
and just just sort of talks about stuff we are worried about it was the the lte designers and so these are some of the things here right uh tracking tracking i identity physical physical attacks on base stations uh manipulating control plane or user plane data uh threats to um like basically uh how there are like downgrade attacks in ssl there are you know downgraded attacks exist in cellular networks as as well to you know uh push you into using a weaker cypher um and then you know jamming it is you know an open and open interface and so um uh it's interesting to note that uh jamming is not within the threat model of lte um and you can you can basically
acquire uh jammers for like 40 40 bucks on ebay from you know it'll have some russian characters on the packages um but uh yeah so it's just interesting to know that they are not trying to to prove protect against this admittedly it's a really hard hard hard problem um so low level threats uh right i mean um basically since it is open uh there is uh sorry uh because the the air interface is open there are um uh like you can basically sniff the the traffic possibly or do jamming attack sim cloning um this used to be a way bigger problem where you would either steal someone's phone and copy their sim their sim card and then basically use
their their their account to make long distance phone calls right um and nowadays uh more of an issue is really people um people uh cloning their their their own phone and then uh and then uh using like using using that to spread out their wireless service to multiple to multiple people basically have one have one account and you know 10 different 10 different 10 different lines basically right um and i really even that i like even that i don't even like i don't see that much of that happening threats to privacy by by design i mean your phone knows where you are at all times or at the very at at the very least if you are uh
like your relation uh like your location in relation to a base station right i mean uh if if your phone can talk to a base station you're within some minimum some minimum distance between a a unique base station um and as we were saying now like basically sprint and att and verizon they have to operate this massive ip based network now with you know basically servers on on the internet and that's going to be a little bit a little bit different from uh from from before so the actual hardware token usim uicc uh it is more or less identical to what it was in um ts which is three three g it actually points to the same standard
um so it just says hey look that way um it uh uses nl uh sorry lte uses a new hardware protected 128 bit key called k and k is just really really uh like really really important you need to look into okay basically all keys are derived from k session keys long term keys um whatever uh and uh k never leaves your phone ever uh k k is is basically instantiated or sorry k is derived um or you know generated and then it is basically stored in the core network at the mme and inside of a sim card and other other than that it is it is never uh it is never released um so um uh
i had a nice segue okay yeah so one of the main points of this key k is for aka there you go um aka you know authentication and key and key agreement this is how subscribers are authenticated to to a cellular network um uh so it's basically a crypt a cryptographic protocol um it's originally specified in that standard um previous versions of of of uh aka did not do mutual authentic authentic authentic authentication and that's the big deal here is that is that lte actually ties the name of the serving network so it it it ties the name of basically verizon's network into the aka protocol and so you are actually authenticating both sides um you're yeah yeah um
an aka uh again this is confusing we'll just talk about it for a second and we'll look at the diagram um uh aka uses authentication vectors it's basically the main primitive inside of aka and it's just a bunch of different uh a bunch of different security parameters there's a baby a bunch of them but basically and an authentic authentication vector con consists of a response an autn i don't know how people say that authentication out in uh a nonce uh a random number and then uh a local uh a a session master key is how we will call that and that is kazmi or k as me um so it's actually not too bad though um
this is a simplified version it doesn't have any of the uh of the error mechanisms in case things go wrong in it but basically you have your phone with the with the usim on the the left and on the right you have the core network which which has access to the hss and and authenti authentication center you can see at the top at the top left and top right uh both sides have access to the mc and k and so what really goes on is that your phone sends either a temporary identity or or the mc over over the air interface to the core network uh that's the top thing there the second step is that the mme
receives that information uh looks it up and sends uh and sends that information to the uh to the authentic authentication center cryptographic magic happens um where basically um the the mc and k and the serving network id all basically generate uh a couple of different crypto crypto cryptographic parameters uh specifically these um the uh the the resp response and the uh and the session key uh and only that information sorry this whole authentic authentic authentication vector is sent to to the mme and then only the the uh the uh nonce and the and the authentic authentic authentication token i i still forget what what uh what uh what a au tn stands for um that is all sent to your
sim card your sim card does basically a very very similar process as what as what goes on here to uh to basically generate a a a signed response um and that signed response is then sent over to the mme at the core network and if this and if this uh and if this expected response uh is equivalent to the signed response then someone is authenticated to the end of the network yes sir um
am i missing something am i being profoundly stupid by observing that that means that the telco provider has an inventory of all k's they definitely do which means a compromise at any telco provide that compromises the entire network um so it that uh so um just because it's confusing how networks are laid out uh but but uh uh uh basically it's not it's not all your eggs in one in one basket there are there are uh uh yeah there are basically multiple baskets i'm not exactly sure um how say you know att lays out it's it's uh it's an authentic authentication centers but i would assume this is a complete josh assumption here that uh there is
basically you know maybe a north carolina authentication center and there's a washington dc and then there's a new new new jersey i have no idea um i i just don't have access to that to that information but but uh uh basically yes if if if it is all in one in one in one basket and there is a leak token then you could have then you already have modules from java card and in the java os to do uh to do asymmetric crypto you could have you know the telco provided called the public side and then no one would have yeah yeah i've actually i've actually wondered about that myself and this is just another josh thought um maybe they are
um uh like maybe it was just be because the network was built in you know late late late late 80s early 90s and they used symmetra crypto up up up front or maybe uh phones have to basically authenticate a lot and you know asymmetric crypto is much more uh oh sorry is you know not not very efficient um again that's just like that's just a guess on my part um that's a good observation though um um so yeah that's how that's how you know your phone gets onto its network um and earlier versions of this uh are like they look basically similar to this it's just some of the the acronyms are different and that uh
that uh that a sn id and that uh nonce might not be there um so we don't have time to go over this i'm running a little bit slow but there is this is the the cryptographic operation that is that is uh used to to generate the the authentic authentication vectors um uh it is a standardized algorithm but it but uh the three gpp uh standards don't say that you have to actually use it because someone uh like because verizon actually owns basically your sim card and they own the core network they can actually use you know whatever key generation and key data derivation algorithms they want to because they own both sides and so as long as it works
within their their their their network it's not a big big deal and this standardized algorithm is french and it's called milanage i hope i'm not hurting that you know hurting someone's ears real real bad um and this is what this is uh the actual usem verification i mainly made these diagrams because uh the ones inside of the standards were super ugly and these ones you can just take and do whatever you want with with them yourself so um yeah the powerpoint is all is all uh is completely available so lte crypto cryptographic algorithms used for use for uh basically uh conf confidentiality and integrity protection um this was there's like a there's like a long super fun history
here right um like basically originally um uh with gsm networks uh trying to trying to remember exactly how it how it went um it was going to be 64 bits was how far the original uh like how long the original gsm key was going to be but then the west germans were really were really worried about the east germans and britain's didn't trust anyone's sorry anyone and it it it it eventually kind of got nerfed um and the this these the same way desk did and so it's a gsm had a 56-bit key basically uh with uh like eight eight eight bits of padding um but in lte we do have 128 bit and 256
bit keys and these are uh these are fairly robust algorithms they are standardized algorithms you can go and look in and see exactly how they are they are uh they are being imp sorry how uh how they are defined not how they are implemented um these are all open uh standards you basically have e e a which is in you know encryption algorithm one and then e i a which is you know integrity algorithm one and they're a bit they're both based on snow three three g which is a umts algorithm and then uh the the us and you know me being from nist and you know our history with aes and all that um uh the us uses um like the u.s
basically got uh uh aes inside of the 3g pp standard um so basically you have e e a2 and e ia2 are basically aes and ctr mode and then you know aes cbc mac um and then china uh was kind of perturbed about this and so they decided that they uh that they that they wanted their own you know their own algorithm and so now uh zuk is is currently being standardized and uh it should be to my knowledge it's not implemented but that doesn't mean much because i don't know well i don't know anything about lte networks in china um yeah so i just i just don't um and if i did that would probably not be
safe so um right now most keys in lte um are 256 bits bits long but unfortunately only only one like there's uh basically 128 bits of zeros in in a lot of them but that is being quickly uh changed and you know uh everyone's being proactive about that just you know fyi um so here's what i kind of promised right we're gonna dip into the standards and i'm really going slower anyway um so these are the three different standardized algorithms and what it says here is that um is that aes and snow 3g have to be sub supported um but um uh zuke is you know you don't actually have to support zuke which is
which is interesting um i don't know if that's going to change in the the future if you know basically verizon and at if verizon and att will have to support a chinese cypher
it might be built in right yeah so the key the key hierarchy in lte it's a little bit con confusing but um basically you have k which again is only stored in uh core network and sim and you have ck and ik which are basically derived from uh from k and they are basically stored in in the hss and in the phone itself but then you get into the actual meet of it with the kazmi and k-a-s-m-e and this is the uh this is the uh the uh the local master key and so basically all these other keys are derived from like kazmi for the for the most part um and there's there's so many it's crazy i should have put a a
picture of what the the the standard looks like it looks like the most confusing circuit diagram you've ever seen if you're looking at at how like what the the key hierarchy looks at looks like you should actually go in and look at it it is very very comical and what you're what you what you see here is that you have different keys for different purposes which is great but then you start to have different keys for different protocols which is even cooler you have a krrc and i don't know why i'm just doing you have k r z end here and the k r c in in encryption here so you have a different key for
both encryption and and and integrity and you have the the uh the same thing here for uh nas uh being on access stratum control signaling here's a sweet little uh chart i found online and i reprodu produced and i totally cited them but um i really like this because it just shows all of the different main keys and their strengths real real fast um so signaling protection what is actually encrypted inside of lte um so as we were saying you know different different community communication paths have their own have their own keys and a common claim and this is what really perturbed me i will say that word um is that uh lte is fully encrypted i've
seen this in like ieee articles i've seen this uh on uh on just like all all across the internet and that may be true um but it is not mandated by the uh the standards and so you're basically you're putting your faith in what a t and verizon and sprint do and they may very like they may very well encrypt everything um i don't i don't know uh yet um but uh just i just i just like to you know say you know like hammer this point this point this point home and this is just a cool little diagram shows you know which keys different different different layers of the the the protocol stacker actually um
are actually protected by um so we we talked about nasa security i'm going to speed up a little bit we talked about nasa security here being uh the the signaling beats between uh the actual phone and the court the core uh the core network and uh uh and so that's called the the non-access stratum the green part is called the actual access stratum and they get protected with different with different keys and then nds ip network domain system and slash ip this is basically using ipsec in the corn in the corn the core network that's the standard if you want to read up on it that's like a five page standard um it basically says you can use uh ipsec
in a certain in a certain mode uh and uh and then uh you can put security gateways which are just basically hardware hardware ipsec appliances on your your network at various points um and uh this is not required either but to prove that here we go um so nas requirements so you see uh nas signaling confidentiality is an operator option um so the con the control uh signaling is fairly important i would have uh i would have at least suspected that the the control signaling would have been would have been encrypted um uh and it says there you know note one rrc and nas signaling confidentiality protection is recommended um and a big a big reason for this might be is that
3gpp standards have to be deployed worldwide right i mean that they have to work in all in all countries uh and in all such situations um rrc signaling confidentiality is is an operator option um and yeah um the only thing that's really mandated here uh in terms of uh cryptographic protection is in is integrity so integrity protection and replay protection shall be provided to nasa and rrc signaling which is interesting and uh yeah yeah so basically you can think of it as the uh the minimum and confidentiality protection and and there is there is a a a a caveat that says that if you physically um like if you don't physically pro protect your network devices then then you have
to in encrypt uh i haven't found much about what physically protecting your network devices means but if you want to go look at these these are the the like this is the standard and where you can find it uh before i wrap up home home enode bees i just wanted to let you guys know that these things existed these are basically femtocells or or ato cells um like these are just basically base stations in your your your uh your house mcmc catchers are typically some sort of femto femtocell what's interesting about the actual home enode b standard is that it says that uh that like uh that you have to have roots of uh trust and so basically you have to
have you know like long-term cryptographic key storage protected by uh by hardware um as part of the home eno eno de b and that uh secure boot must be done which is which is really really great um yeah it's just interesting um and then lawful interception just wanted to put this out there too i haven't fully investigated this yet but there are uh three different lawful interception standards that i'm aware of um they're actually built into the the lte standards and basically as you can imagine so um you know law law law enforcement bodies can uh you know get access to the the keys that were that were used to uh you know com to uh to uh encrypt um someone's uh
traffic um uh hopefully this is being this is being done to um to make it so uh it's it's it's done in the most secure way as possible uh i one would hope uh that like you wouldn't want lawful interception to basically make it uh to where it was really uh you know like uh the rest of the key structure was weak or um or you know reduce the size of a key um so that's basically all i got um lte security is imperfect and crazy complicated um and comp you know complicated things are all like always really really secure right um so uh in general integrity and replay protection are mandated not confidentiality protection um
and just remember that standards provide the bare minimum level of security that must be achieved um uh telcos may voluntary may vol voluntarily raise the the uh their security um it's hard to tell so thanks for for having me um here's some further reading if you want go to open social security training dot info and i just tweeted these uh slides with the uh with the besides clc clt if you want to take take a look at them so thanks