What You Can't See CAN Hurt You: SonarQube Privilege Escalation via Hidden API Calls
Show transcript [en]
and just a little intro to john's talk um he's going to talk about center cube which is a source code analyzer and he found some pretty cool ways to uh use the api that the uh they probably didn't intend to be used um so he's gonna you know give you some pretty cool information there and uh on um um you know how you can uh do remote code execution or um even i have backdoor access just using the api and not no other tools so let me um bring john in now
here anybody hear me out uh soundcheck john soundcheck can you hear me yes yep all right well thanks for having me my name is john williams i'm going to be giving a talk today on what you see what you can't see can hurt you this is how to use the sonar cube api to do privilege escalation let me get my screen up here
all right so a quick agenda for today um first of all i'll do a quick intro of myself and our target which is sonar cube we'll move on to some reconnaissance how to identify exposed instances of sonar cube and gather information from them after that is weaponization how to actually get a foothold within exposed instances of the application and prepare the exploit which is the focus of this talk which is how to escalate privilege from the application front-end into the back-end server the last part of course exploitation um how to kick off that exploit and then at the end we'll talk about how to remediate this vulnerability it's a little bit about me to begin with
my name is john williams um this picture here is actually from election day because this is how 2020 has been going um i do have a few certs to my name both from blue team side and the red team side um i started out my career in it in a support role for a financial software company and over the time i was with them i grew up into systems engineering from there i got interested in security i took on a role at a sock in the financial sector and spent my time there learning about digital forensics and incident response then i made a jump over the red team and at the moment i am working as a
penetration tester for bishop fox and greatly enjoying my time over there i just want to do a quick level set about the talk if you're here looking for a hardcore technical code exploit then i'm afraid this isn't going to be the talk for you but my focus is on simplicity and creativity i'm going to be talking more about how to find features in an application that are intended but then abusing them for means that weren't intended um the reason i'm doing this is in offensive security i find a lot of attention gets given to incredibly smart hacks and rightfully so i mean there's some brilliant people out there some brilliant ideas they come up with of how to dig deep
into code and find exploits that are really technical um and that is awesome and it's well deserved but in my experience uh in offensive security the bulk of the day-to-day work depends a lot less on these complicated attacks and much more on creative thinking um and it can be intimidating when you're first starting out in the field because you know the the people who are held up highest are the ones who are really deep in the code but the fact is if you are able to analyze your attack service creatively and abuse what you find there you can get really far just doing that and so my goal here today is just to demonstrate how to use an
attacker's mindset to compromise a target so what is our target um it's sonarcube this is an application that is open source used mainly by developers and it's pretty prevalent across the internet today it basically has several different functions it acts as a code repository so you can store code collaborate and work between developers you can share permissions you have pretty granular permissions to how you access different projects within it it is a static analyzer which means you can use it to run scans of your code to identify common coding errors and bugs in your software and it's designed specifically to integrate with continuous integration and delivery pipelines so it's great if you're a devops shop
and lastly it does security audits so well in addition to looking for bad coding it can find actual vulnerabilities and other oversights within your code that could be exploited overall pretty great tool this is a picture of their website super snazzy and from what i've seen sonar cube has a pretty high adoption rate among developers i regularly encounter this platform while i'm testing clients of ours um and so it's that's what made me choose it as a target for this talk today it's pretty relevant unfortunately center cube has had a little bit of bad press recently um the fbi has been warning that hackers have been actively targeting exposed source code in sonarcube specifically in
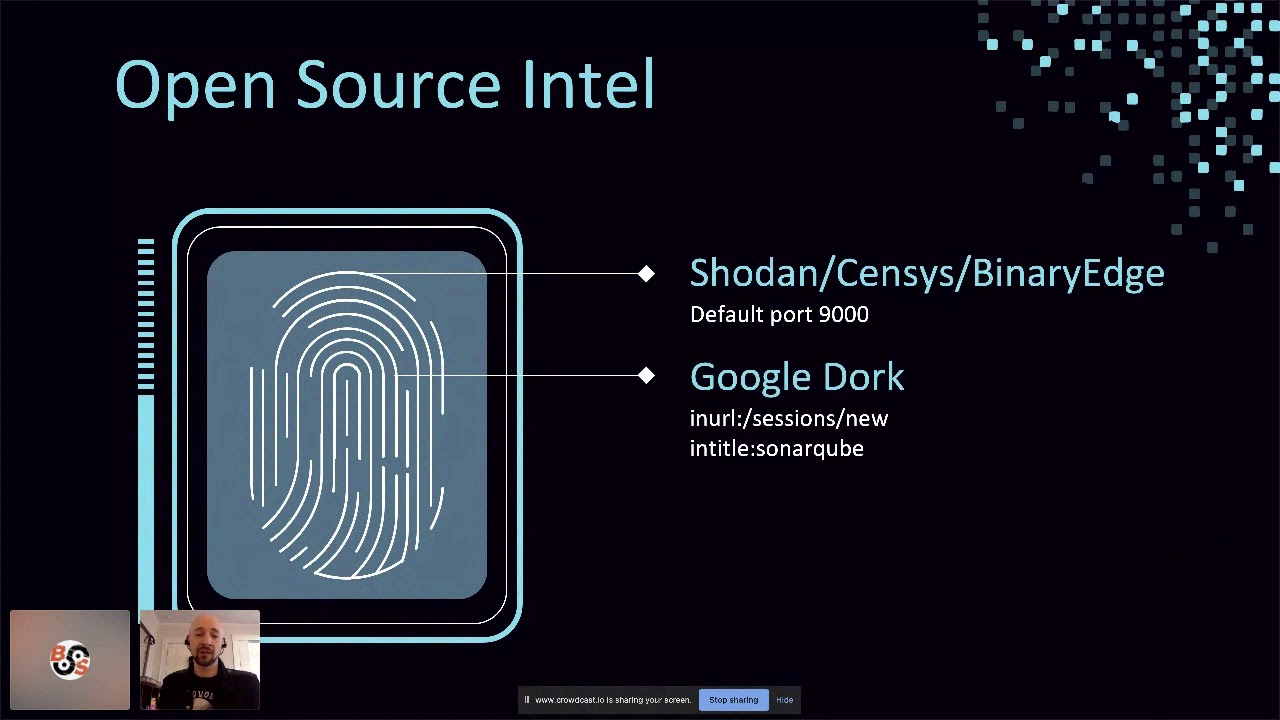
u.s government agencies and businesses since about april but i do want to point out this isn't really much of a slight against thundercube itself um because they're not emphasizing that the software is vulnerable more more often it's hackers taking advantage of misconfigured sonar cube instances um there are there do tend to be a lot of exposures and we'll get into that in just a minute that brings us to part two reconnaissance so if we're looking for stoner cube and we want to find exposures online how are we going to do that um so we'll start with the usual suspects for open source intelligence showdown census binary edge and other mass scanning tools out there are great for finding this and that's
because the default port for the administration console is nine thousand so if you're using these tools all you gotta do is search for expose 9000 and you'll find a lot of sonar cube that way also google um you if you target your search correctly you'll find a lot and all you got to do is look for the login page which is at sessions new um and the title will have sonarcube right in it so you can get uh hits really easily just searching on google for this i did do a little bit of this uh to prepare for my talk today just to be able to throw some images up so this is binary edge doing a search
for port 9000 it gave me a lot of good hits this one for example on the screen you can see it looks very promising it's got port 9000 exposed the title of the page is stoner cube and it's returning html body content so all those things are good signs this is one you'd want to look closely at it probably has some exposure now once you actually browse to the site it's a toss-up you know as to whether or not it'll actually expose anything but for example this one i came across this was in about five minutes of you know doing my search to prepare this presentation you'll notice i'm not logged in if you look at the top right corner
the login button is there and yet we have several projects showing on the screen each of those containing source code and other things that you can dig through and this is all publicly accessible right so what is the danger of having exposure like this because we're talking about source code if this is especially if you're a company and not just an open source developer you know just writing your own code but if this is commercial software that's being exposed you're giving away software stacks that your software relies upon so all the dependencies and you know what platforms it runs on you may be giving away server locations if your software interacts with other services now those web addresses are exposed and
we know how to interface with them directly file paths you could find sensitive files within the code itself you know that wouldn't normally be accessible through the application or if it's interacting with an online service you can find paths to sensitive information within those services they might expose proprietary data again if there are files you're not supposed to be able to get to through the app but they're disclosed in source that could be really bad in some case you could actually get a company's secret sauce right if their whole business model depends on a particular proprietary algorithm and that's in the code that they've inadvertently left exposed online that could be a really big problem for them
not to mention things like credentials keys tokens and other secrets which you can use to you know either get into uh the application itself with privileged access or to other sites and services that it depends on um or just sometimes it's even unrelated services you know you might find random credentials strewn about your source code just like in github so oh and not to mention bugs and other security vulnerabilities because after all cylinder cube is a static analyzer and so the results that it finds in its scans could also be exposed and give you a leg up on how to attack the code all of this basically you know amounts to a treasure trove of information for
an attacker so it's definitely something that they've been looking for as we've seen so now once you find uh some instances of summer cube online that are exposed and they have projects showing how you actually find interesting or valuable data within them and there are a few different ways you can approach this the hard way of course is just to manually browse through the source code that's great for getting your bearings understanding what an application is how it works and this is great for small projects in particular where there's not a ton of code to go through but if you are doing a much wider survey or if you find projects that are much bigger
this becomes impractical much easier is to use the issues section within center cube here is where you have the results of your scans all the things that it's found when looking at the code and they make it real easy to filter by category so you just go down the left find the categories that you're most interested in and then see what comes up as an attacker this is great because you can focus on the security categories and hone in on exposed credentials on suspicious comments on like potential sql injections all kinds of things will come up here you don't even have to do the work because it's already identified it for you then of course there's this in more
recent versions they've added a feature called security hotspots and for an attacker you click that it takes you straight to the goods just like this hard-coded credential that i found and um yeah this is exposed online um if you're paying attention the name of this application is ems that stands for election management system um i found this exposure within minutes of preparing this presentation and i am not going to bother obfuscating it because anybody can find this this is the state of our election security in 2020. now automation is also great for these kinds of exposures right um sonarcube has an api that makes it really easy to retrieve all the code from a project so if you find one that's
exposed you can write a simple script to clear the api and pull all the code down once you have the code offline there are tons of open source tools online that can help you dig through that data and hunt for secrets dumpster diver is one of them i highly recommend it it's a great tool for this type of thing there are also plenty of others out there you can choose from all right that brings us to part three weaponization so exposed code is one thing um but what about actually compromising the sonarqube platform itself um and this is where it starts to get interesting you know we want to actually um get access to the administrative
console within sonarqube so how do we do that there are three main ways one we've already talked about a little bit through credential exposure and anywhere that there's public code you might find credentials that can get you into the application you might actually find a sony cube repository that has public-facing code with the credentials to get into sonarcube itself would be stupid but it could happen right also github gitlab you know the last talk focused a lot about hunting for vulnerabilities in github if you're looking for credentials um you could find things that will get you into center cube as well as credential reuse right there are always breaches there and leaks and other ways of credentials
coming out password spraying you can take those credentials and find it like different services they will get you into so all of those you know are an easy way to get into summer cube initially the second approach is to look for vulnerabilities in the application itself now in my experience overall center cube is actually really good on this front there aren't very many vulnerabilities um there haven't been many in its history and when they have come up they've been pretty um transparent about dealing with them and resolving them in a good way but that said you can still find older versions that are publicly accessible that have vulnerabilities um like this one in some cases if
there's a jenkins plug-in installed you can abuse that to disclose the credentials and then log into sonarcube itself um so that's another way you can get in the last way of course is just pure stupidity and this is the most common way right you when you first set up stonercube it has default account credentials admin admin so you'd be shocked at the number of times that sonarqube gets stood up left exposed to the public and this account is never changed it really is that simple sometimes and this is what the fbi was warning everybody about you know just lock down your software don't make it open to the public and yes the election site that we were
just looking at also had this problem they hadn't changed the password on their admin account all right so once you are able to use one of those three approaches and get a foothold within the server now you have admin access so from here what can you see so let's do some enumeration within the admin console there's a configuration section and you can review uh the configuration for a variety of different integrations so you can see the mail settings you can see code version control you can see single sign-on if they've configured to store their code externally with github or gitlab then that config is there and they also have web hooks for interfacing with center cube programmatically
none of those passwords are disclosed within the ui which is great that's really good on sonarcube's part but all the other configs are there security that section allows you to control your users and particularly with some corporate sites once you get to this point you can start uh understanding who their developers are who their administrators are you can capture emails sometimes a lot of emails depending on how many people they have in their system you can see what groups they belong to what projects they have access to and start to understand who's responsible for what and of course you can manipulate all of these things projects um in sonarqube projects can be public or private and as an
administrator of course you have access to all the private projects as well so that's you know just like we were talking about before there's a lot more code that you can go through and check for um you know things that might be exploitable in addition to the code itself you have the issues section so you can review scan results and reports which collates the results of all of those scans now before i move on here i do want to notice um give a shout out to christian gutierrez pretty recently in october he released some research showing that there is an api endpoint at api settings values that actually discloses the passwords for some of those
integrations we just talked about in clear text so the the mail password github gitlab secrets um and possibly some others can be disclosed through the api and that that was a really great find in that particular instance i don't think you even need administrative access it depending on how things are configured you might be able to get in and get that information with a low level account or even without any access at all um so that could if you find something that is exposed that badly you might even get a credential that lets you log into sonarqube just by going to the api but i want to give credit for that finding the other thing that
having admin access gives you access to is the system section and here's where all the juicy features are right you got the server id and version you have the path to where sonar cube is installed on it on the server um you have database connection details as far as i'm aware the password for this for database connections is not exposed either in the ui or the api um but maybe somebody will figure out a way later the java virtual machine that runs center cube all of its configuration details are accessible here as well as the version of java that it's running on and then you have these handy buttons at the very top of the screen
um you can just download all of the logs that stonercube produces um and you can download all the system info so if you just want to hop in and hop out real quick and then review all of that data offline you can do that so there's again a wealth of information available to you as an attacker here and of course then there's a restart server button so you can very quickly um reboot the standard cube application just by clicking that so what does all this amount to now what what's the potential impact and as an attacker what damage can you cause through this web ui so you can mess with all those config settings that we just went over
so if you want to break their mail integration or you know cause some havoc you can do that you can add users you can remove users you can put in a backdoor account for yourself you can boot out the admins like if it just depends on what you want to do but all those user settings the projects themselves you can manipulate and here's this depending on how they're using sonar cube uh in their company this could be more or less dangerous if they've integrated their projects into some kind of ci cd pipeline any small change that you make within the code then just gets funneled down through the pipeline and possibly could make it all the way to
distribution so you could either break somebody's app and break their distribution or you could plant something malicious in it and basically you know cause a supply chain attack um you can change the logging level so if you want to get a lot more detail from sonarqube about the scans that it's running you can do that and then download the logs mentioned already you can restart it there's also a plug-in installation feature however it's a little bit limited in scope because you can only install plugins from the marketplace which is curated but in general there's a lot of mischief that you can cause just with access to the administration dashboard right now what about the uh the api right so
far we've only talked about what's accessible through the front end but if you go down to the bottom of the page once you're logged in there's this web api link click on that and that takes you to the documentation and this is brilliant as an attacker again it's like oh if this opens up everything now you can see the commands that are used to do all the functionality within the front end and if you notice up here they give us a couple very handy little toggles to show some additional api commands internal and deprecated let's take a closer look at that if we turn on the internal api uh endpoints they point out to us the
caveat that you know these endpoints are subject to change without notice so fair enough one of the ones that comes up is called update center when we take a look at this a little closer we find out that here we have a command that will allow us to upload plugins to the system remotely as long as we have administrative privilege excellent so now we have what we need to formulate a plan of attack so here's what we're going to do step one we're going to write a malicious plugin step two we're going to use the api to upload it into sonar cube step three we're gonna restart the app server so that it loads the vulnerable or the
the malicious plugin and in so doing will compromise the target suite so let's get started but in order to do this we got to know where to begin right like how do we even build a custom plug-in what does that look like um fortunately sonar source which is the company that makes sonarcube is really helpful in this regard they have great documentation online including an article about how to build your own custom plugin and they go the extra mile they actually give you a github repository with a sample plug-in to show you how it works so awesome now i spent a fair amount of time going through this documentation trying to figure out how this works and
how to exploit it and i've distilled it down into a few main takeaways right so the things that you need to know in order to build your own plug-in are uh sonar cube and the plugins are written in java 8. um they follow maven project structure so you can build the plugins with maven and for testing you can use docker because center cube is open source they've been great about making containers for each version that they've released so it's super easy to set up a test environment for development so uh if you're going to build your own malicious plugin first step is just to install these prerequisites now let's have a look at what the
plug-ins actually look like right um what i did here is i took the example plug-in that was available from sonarsource made copy analyzed it figured out how it worked and then i just kind of you know trimmed it down to the bare minimum so this is like a minimum viable plug-in if you will for this exploit and when it comes down to it there are only actually two files you need plus a little bit of scaffolding first file is the palm files the project object model and this is standard for any maven project it's just a file that an xml file that has some metadata in it that defines the project structure as well as the name of the plugin etc
the other file is the java class and this actually contains the code that will be executed when the plugin runs and that's it so let's have a look at those two files now this is the palm file um and i the the whole file is bigger than i could fit on the screen so all i did was um took out the parts that you need to change from the example plug-in that they give you and there's only a few fields right and they're pretty arbitrary you can call the plugin whatever you want write whatever description you want for it there are really only two values here that are tied to the project structure so the group id
and the plugin class those ones um have to correspond to uh part of your project structure so if you remember the other file that we have i named benign.java if you were to change the name of that to something else then you would also have to change that name in the group id and the plugin class so just be aware of that if you play around with this so now looking at the java file itself i apologize for the small text in this case but this is the entire file um at the top you can see that we have a bunch of import statements and so i forgot to mention our goal here is to make a plug-in
that is going to execute a reverse shell right so they load the plugin it makes a call back to a server and you control and pop a shell on the backend server of the sonar cube installation so in order to do that we need to import some java libraries that will support networking so we've got those at the top and then for sonarcube to recognize this as a plugin and know how to interface it we have to import a couple of their libraries so that's what the sonar libraries are that we're importing under that you have the the class itself and the class name here is benign and that corresponds to the name of the java
file so again if you change the file name change your class name here within the class we have two functions defined there's the main one and then one called rev shell the main function is very simple all it does is it sets up two variables that define where your listening host is so this is the only thing that you have to change in order to use this plug-in the way that that i've written it you specify your attack host either ip or host name and the port where you want to receive your callback then the the function takes those two things and it calls rev shell with them the rev shell function just uh it's very
simple it uses a bash one liner to open up a reverse shell back to the target that you specified um now what this means is that this will only work against linux hosts um and i wrote it that way because all the targets that i've come across for sonarqube are linux however uh you can run it on windows there are some uh windows hosts out there so if you were targeting them you would need to change the way this function works now i'm not a java developer and i'm sure that there's a way that you could implement a reverse shell in native java code and then it would be cross-compatible so i'll leave that as an exercise to the
readers you know to try and figure that out later on but for now we're targeting linux so once you've got uh your code all set it's time to build it and fortunately this is super simple all you got to do is open a terminal uh move into the directory where your plugin is and run maven clean package boom um if you're using the code that i provided here it's really quick of course if you modify it then you might have to do some troubleshooting but as soon as it builds cleanly uh it will output a jar file into the target directory that's it now you have your exploit so all that leaves is the exploitation
now you may be tempted at this point to just take that jar file and fire it at your target server and see how it goes but be advised if the plugin fails uh it could crash the sonarcube server and if you do that then you're out of luck right you've lost your foothold you can't you can no longer get in and restart the application like you just you're done now so testing is highly recommended um and because there are docker containers available that part is actually really easy all you got to do once you have docker installed is to use this run command to pull down a container and just test it out locally make sure
you use a version prior to 795 if you want to exploit this api endpoint and make sure you expose port 9000 so once you spin that up then all you have to do is browse you know pull up a web browser and go to local host port 9000 and you can log in with the default credentials admin admin um remember now if you are testing a reverse shell you want to make sure that your listening host is using a publicly accessible ip otherwise you'll have to do some networking configuration because by default your docker container can't talk to the host environment that's running in so you'd have to build networking in to allow that to
happen it's much easier just to stand up like a listening host in aws or something and have your container call out to that ip when you're all done with your testing just tear it down using docker stop zone or queue assuming that you use this name command when you oh it's fired it up then it becomes really easy to tear down all right after you're done testing we're ready to exploit so first step is to fire up a netcat listener then open up a second terminal and you can use curl to send the plugin to the vulnerable api endpoint all you need to do is use the user flag with the username and password to log into the
sonarcube instance set the method to post use the uh the file sorry so use the phone form post flag to make sure that you're uploading the file with this file label to make sure that it gets there and the app in front of this will make sure that it actually uploads the jar file instead of just sending the name of the file then the the url of course is where your target is you may need port 9000 on that you may not depending on which one you found and then the path is api update center upload assuming that that goes through without an error then the plugin has been uploaded to sonarqube and then the last step is
just to restart you can do that with another curl command you just submit an empty post request to the path api system restart give a few minutes it will take a few to to go through the restart process within the application and it's at the end of that process that it loads the plugins but as soon as that plugin gets loaded boom you should get your call back and most likely when you get that shell you'll be in the context of a of the stoner cube user but you might get lucky you might have more privilege than that depending on how the application was configured i'm pretty sure in windows environment it's more common for sonarcube to run
under the system account so there you go now if it went off smoothly your plugin got loaded into the dashboard and you just successfully escalated from an application administrator to a user on the backend server and from there of course the next step you can conduct local reconnaissance you can download sensitive files off the server and you can look for other opportunities to elevate your privilege or maybe even look around the internal network and pivot to other hosts a few other things to consider though if if you missed your callback or if you end up losing your shell at some point it's really easy to get it back all you got to do is restart the application
again and if you're feeling a little lazy with the command line you can always just log into the dashboard and then click that restart button to do that that will get your shell back real quick um if you loaded a plug-in but for some reason it didn't work especially if you modified it you know from the one i'm providing here um you can always uninstall it through the dashboard they make it really simple just select the plug-in and then remove it and then you re restart the app again and of course when you're done make sure you clean up after yourself right whether you're testing or whatever it's just bad form to leave your back door after you're done
um so last but not least what if you're on the other team and you just want to know how to defend against this attack um turns out it's really simple all you got to do is upgrade to the latest version of sonar cube um so starting with version 795 the update center api endpoint doesn't allow you to upload custom code anymore it only lists the installed plugins so that's good sonar source was actually really gracious when i reported this issue to them they informed me that they'd already dropped it from their current version eight but they acknowledged it was still an issue with their long-term support version seven um they they did get on top of that and
they remediated it so at this point in time the current version of both eight and long term support seven are not vulnerable so as long as you upgrade to the most recent version you won't have to worry about this particular attack vector um but if you're an administrator keep in mind an attacker can still abuse the plug-ins to plant a back door they would just have to find some other way to get in the server first so if there was some other vulnerability they could still use center cube to um to give them a backdoor account um also make sure that none of your projects are publicly exposed like we talked about before you can set them
private public make sure you go through all of them and mark them as private um and the easiest thing the easiest way to do this is if you go in your administration panel under configuration and security there's an option you can just toggle to force user authentication and if you do this your public projects won't be publicly accessible the api commands that could potentially disclose things won't be accessible without authentication so this is a really good way to just lock it down then of course you want to change the administrative account password don't forget that don't leave admin admin open um and realistically like if you're in a corporate environment you should have this whole platform behind firewall
it shouldn't really be on the public internet anyways um but if you are gonna expose it you can do these things to lock it down and that's all i got um if you're interested in playing around with this plugin yourself you'll find it on my github page along with instructions for how to um you know modify and build it i will also put a copy of this slide deck up there if you want to review so thanks a lot for having me um it looks like i'm actually just a little bit over time so i won't be taking questions but if you want to chat with me i will be hanging out in the discord
channel so thanks a lot john thank you very much that was a great talk thank you i appreciate being here yeah awesome yeah everyone john will be in the discord hit him up





