Injecting Automation into Pentesting
Show original YouTube description
Show transcript [en]
hi everyone like thursday from the world so today i will be uh talking about a bit of how we can inject automation into pen testing this is not just limited to pen testing but it can range from any work in the security uh this is just i would like to give a hunch to everyone of how can they automate their work and be a bit lazy so a bit about myself uh currently i'm working as a security engineer at a company called mobiquity mostly my work here revolves around uh for the things such as devsecops code reviews and automations but i have always been uh into band testing like since three years and here also i
do some pen testing but not that much but i always do pen testing so that's why i'm active in work boundaries uh everyone might have heard of synagogue so currently i'm as a cinegra team member at level four there and apart from infosec stuff and everything i play a bit apex legends if someone's there you can bring me there we can leave it there okay so uh to start uh we could say where the bug originates right uh where is the existence of it so we know that most of the developers share the same mindset not the same mindset as an all in all but even if we say in the team they have their same mindset they would have some
standards of the code that uh they want to follow uh like how a function would be returned how would you it would be called what how the command should look like then companies enforce this that a developer should write this code in this way so that uh all the code without throughout the company looks same so i see a problem here that a pattern will be repeated here and there every time right the next thing is everyone copies everyone else's code right so do hail stack overflow right because of this everyone is using the same snippets of code i have seen that many times quantum code has been uh referred to in this stack overflow
with thousands of phones and everyone just think how many people might have copied it right so this leads to like introduction of security bundle is at different places i mean at places like we can't even think of everyone knows http requests modeling right so it existed in the chain of this server who might have thought like years before that it could be vulnerable okay the next thing is that every sdl scene i won't say every sd but almost most of the sdlcs lack security controls uh like security gun controls are not even uh implemented at any stage mostly this is due to timing budget and price requirement i mean uh due to this stuff but
yes there are no sas or static analyzers or dynamic analyzer uh that is been executed on the core itself so that even the low hanging fruits would get sorted out in the starting this is i would say mostly uh habit that is uh mostly people have been also the main constraint i would say that not even the habit is the budget because everything is depends on in how much the client wants the project to be ready and yes due to this only there is no budget but after breach everything goes into security like even the ceo salary would go into uh implementing security for the project because it's one speech and now it need to be secure
there is no uh so this slide says that there is no shift left uh version here most of uh in most of the companies because of this constraints okay so this was where our issues were like or restricted now let's say due to some reason or to contract or do anything you have been given a appendec task right so in the starting we all knows that reconnaissance of the scope starts that what lies in summer scope how many servers are there what applications are there on what next stack it is running as well as what are the different chains of servers such as reverse proxy and uh i would say reverse proxy or any gene of
the server that can be in in between it right so for example uh we would be first listing out the sub domains uh doing a board scan of the server effects it's a network contest or even checking service out of the boots that what services are we offered uh is there any ftp or ssh or even any of the service that is open to us and they can be exploited so from that phase our work starts right uh everyone might be knowing that once you see some of the things such as let's say a banner where cisco is referred or let's say when you're doing an android pen testing or an even ios you whenever you
see the keyword firebase you would start finding the url of the firebase right or even uh let's say you see some services such as ftp you'll be checking that is anonymous ftp uh i mean anonymous ftp services enabled on but you can just logged in as anonymous anonymous user and access the file so these checks are like that much intuitive that once we see it we will be jumping into a check in it but what i say is that this test are quite quite obvious right that we would be doing it once we see such uh triggers right second it's a bit time consuming not taking hours but even minutes because uh we have done it every time we would be
knowing what we would be doing so it's pointless to do right and the main thing that i would be we would be focusing on is that this task could easily be automated right you don't need to do it every time so where's the hurdle i mean if such tests are so much obvious and it could be automated why not everyone using it right so yes so uh that is then this mindset of using an automation from frameworks that people will be saying that let's get up some automation framework that is already in the market i am not saying that all the frameworks are less efficient some of them are quite quite great right but still the thing is
that people don't like coding many times especially the pentester i have met many people who think that coding is boring and let's just keep up with the manual searching stuff but yeah that's the thing and the three things that i would like to hide here for about the automation framework that first they lack contextual awareness right they are not aware that what application on which application it is been tested the second thing is they are not tailor-made right it's not according to your requirement the developer of that framework would be using generic word list right generic test as well as generic list of ports or anything that would be used in assessing those applications and it's not different as
per application it's all static same right so this let's do like more noise client would be complaining that a huge amount of traffic is being generated from your side right many high number of false positives would be given uh everyone knows that right using nicto or uh any such scanner you would see many false positives but uh and less number of for i would say true positive one ratings right and i would say it's quite nice efficient right due to this reasons
okay so the light bulb moment right so let's see what we can do to avoid such stuff right so let's see what if we are able to like automate such tasks such as of recon such as of busy checks or vulnerabilities and such one could be automated right uh yes many of us would think that a five-minute task might take hours to code like debugging the code uh where the error is happening or printing the output so that a tool or even it is human readable such stuff could uh like take hours to code right but the thing is that it would collectively be beneficial for us in the long run in the money aspect
as well as the time expect right we won't be uh using that much time and that much money and let's say if a company is maintaining a repo where all such automation uh scripts are stored right and any of the pen tester could just access it so he would be uh yeah yeah so that would be quite good so i would say uh that i would differentiate this approach into two tasks one is uh the our text techniques and second is the smallest the first one would be like preparing a set of uh tests which is uh like technology agnostic it would be only uh targeting to that technology and uh you can use it whenever you uh in the
next apprentice you find it right but uh it's quite hard right to write such tests for the initial for the for one technology at an initial level so that's where the second thing comes up like you can write small small scripts and which could pass information could do some test cases or even it can provide uh output which is can be fit into another two so what you can do is that you can write such uh scripts then club them together according to their uses and you have your technology technology based automation framework right it doesn't needs to be like a single kick single button turning on and killing them all but it could be a set of scripts right
we'll be going into examples as well as some of the ideas but i would be giving a bit theory up till now so let's jump on to examples right so basically uh let's say that there is uh a task where uh subdomains need to be find right this bash it's a basically a bash command which could be a little bit uh seen like a spiderweb but believe me it is not uh basically what i am doing here that from three resources such as search spotter dot sh and dns buffer over uh i'm getting uh like domain data from that fetching it parsing it as well as putting into a file called or dot domains right and uh
yes we have a list of domains just by using this command i can use it as my basil bash alias or even i can like put it in another basket which which can do my work right it is just uh i would say when you want minimum number of domains from this you can use this this one right the this is the second script which like when i have a minimum list of sub domains and i want that to uh do sub domains subtitles so like the all other uh like running a recursive scan right so we can use this script it's actually a very simple script even though it can be a bit uh long so basically what i'm doing
here here is that i'm using sublister and taking domains out of it i'm i'm again running the dns forward for each and every single domain i'm also using you know the ema's enum data which is passive i'm not doing any intrusive scan currently just using the passive data then i'm fetching from sir dot ss or spotter as well as sort dot sh again like uh from the subdomains to extract the subdomain's domains right and at the final i'm just sorting out each and every data and like pushing it into a uni or let's say domain name dash unique dot txt this look would go all the way up till uh until the lines of domains has been
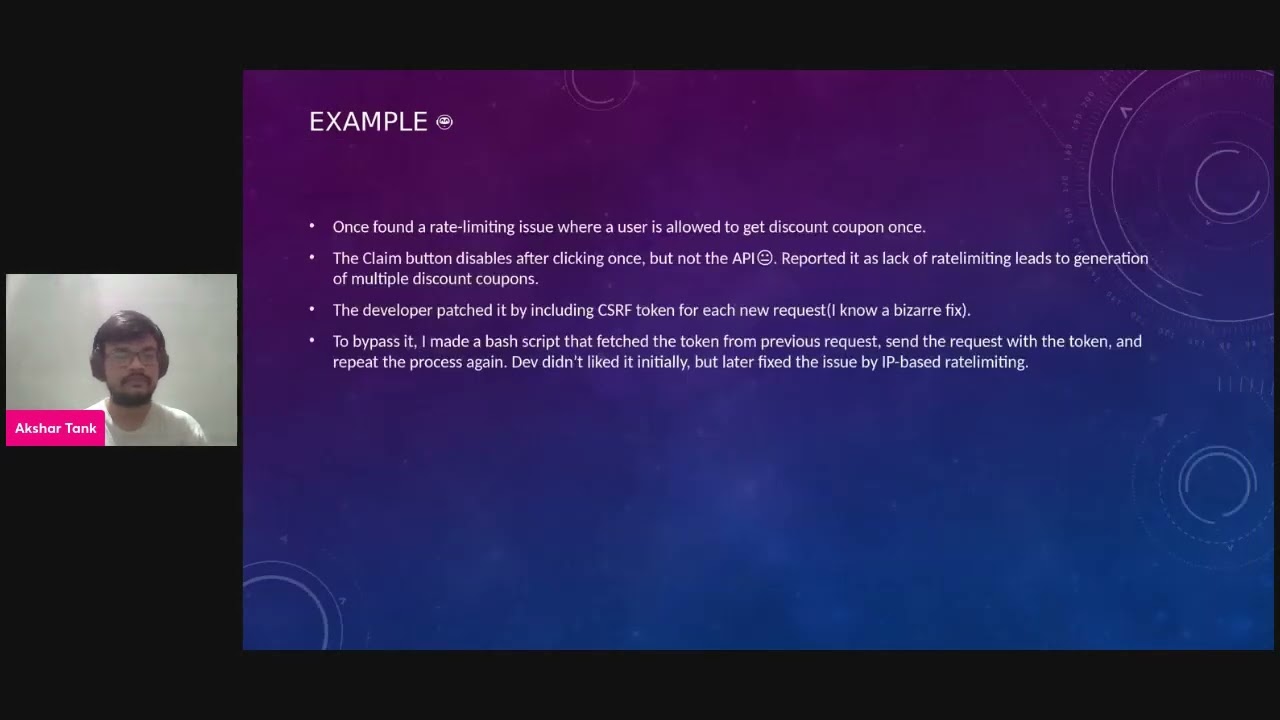
exhausted right and it finally would give you a clean output uh where you can you have all the scope that you need and then finally you can move on with your test okay the next thing okay so this was like a cool experience of one of of one of the appenders uh it was actually a e-commerce application which i was testing and what happened was that there had a claim a discount button right so whenever i clicks it i get a discount button and the button would be like disabled forever but uh the thing was that developer was only disabling card on the front-end side but not on the back answer so uh i told him that this is about for
like for rate limiting i can get as money as discount coupon as i want and still i won't be stopped by the code itself so basically what he do sorry i'm only
sorry it's lagging a bit from my side okay yes this one yes so what he did that he implemented a csrf token to immediately spontaneously i found it to be a bit bizarre but i think it worked what he was doing that he was getting csr to come from previous token embedding that into the next request and it was going on but the thing here is that i am still uh okay there is one question that i am seeing that about a git repo just
uh to be honest yes uh to be honest i have never maintained a git repo but the code that i would be sharing here i could share them in my gate repo and could like give it with this slides so that everyone can access it i have like many small scripts uh which everyone can use so yes there is nothing such as private it is for public use only yes so on this one will rotate itself so yes the csrf token was actually like stopping the request but only for one time but let's see if i'm getting a new csrf token i can like get a number of tokens right so what i did that i simply uh
called the first request grab the csrf token uh put it into the second request and start the loop again right and i i was i mean i i know that it was vulnerable but there should be some poc that can show me that at least i'm able to dump 15 or i would say 20 discount coupons uh just to show to the developer so i showed it to developer initially he thought that no actually it's not valid but later he fixed it with ip basically limiting so the gist of this example was that uh just by thinking a little bit outside of what we provide as a poc i i provided a bachelor as a poc
and actually it worked so the thing is that we can sometimes even automate our pocs as well right
okay so uh now uh many of you will be thinking that uh how shall i do my own or such kind of scripting or automation or such stuff i don't have any background or anything or any knowledge in that so see i would suggest that pick up a language it could be any language right it could be bash python or even node.js just pick it up and try to get the basic context out that how can you do some basic stuff i would recommend to start with bash then moving on to python and then you can choose go rust or any of these such fancy languages uh so in this starting uh maker uh i would say a list of checks
that you would be doing every time many people have habit that whenever they get up at the pentester or start about with the performance they will start directly forcing a target so do it just like make a bash release or make a script which do this right so the thing is that give a thought of how this test could be automated immediately right just i would say implement it even though you are not happy with your uh code just do it even though it might be the dirtiest code but with that time you can refine it i i would give i can give example that when i was learning bash or in my college days i literally passed her sqlite file
with bash just to get our data or something out of it because i was feeling uh too uh i was feeling too lazy for it right that who's gonna learn how to fetch without it so i i got it from that so yes you can do it uh basically start dirty and then refine the core as you go and let's say once those checks are up and running as i told earlier you can like combine them uh with one another of like let's say for the relevant test and you have like your own technological based framework which you can run like on any of the target right so this is the starting point from where you can
become i would be sharing some more ideas in the next slides as well
okay so let's start with some of the ideas which you can implement in your automation framework so fuzzy scripts many of the people which would be in let's say thick line security would be knowing what a fuzzer is but in web uh it is uh it's it's used but not at that smart scheme so basically what a fuzzy a fuzzer is a program which injects semi-random random or let's say curated uh data into a program just to see that uh how a bugs happen right let's say you have a list of call a single column semicolon and double quotes and some special characters you are injecting it in let's say random headers parameters and such
stuff just to see what error the server is through let's say if a stack trace is generating then what it is showing if let's say single comma uh a single quote is entering is it generating uh sqlite or let's say a sql or mysql or even postgrade uh so this error or what it is so basically what i would suggest is makes uh some word list out of this data you can use some open source you can start with some open source i would say report is a repository such as set list and then you can start curating your own based on that what you can do is take those word list select those parameters or which you
want or parameters or writer that you want to first and uh proxy all your traffic to the bug okay i think you can you do or do it quite simply like basically from tools such as ffuf or let's say even if with the call you just need to proxy to your work and then you can start manually scanning that what the the logs are from the scans right what all uh the response has been gotten from the server so this is the first basic idea that i would like to give about the fuzzing scripts you can make submit such scripts where you can just need to input the request and you would have a whole
lot of perk where which you can like go through work for some esoteric quantities it could be anything right depends on the implementation itself the only thing that i would like to add here is just don't spam the target with heavy traffic sometimes uh we try to use a tool that is extreme faster but it can like take down the server i have seen that even many times people use ffuf so much i mean without any configuration that it took down the whole server itself not allowing the legitimate user to access it in such case people can land into the problem so yes configure your tools for speed right uh the second thing is to use historical
data right what i mean by historical data and everyone knows right that what uh way back url is uh it it's actually a tool that fetches uh past urls from uh internet dot i i i think web archive.org yes and also the same is like alienware and there is a go base tool which is written uh which is written to fetch all of these urls what you can do is simply grab those urls right see that where if there have any get parameters or not and which could be like integrating uh like interacting with the backend database uh there is a cool tool called gf or graphic go or it is basically a crap based tool
right uh yes you can basically uh take this uh yes uh the database and uh now yes what i was on that yes you can take this data pass the url or query parameters and you can feed it to sql map like configure it to the lowest setting so that you can have a detection and i would suggest to attach proxy like work for this and what you can do is that sql map would be testing for sql injection and you would you just need to confirm it up until update the detection phase only and let's see uh the detection confirms that there is a sequel here you can like go with manual experimentation so you can just think that how much
effort your was saved uh for finding the sequel it's totally automatic process i won't say it won't it will find 99 of this equally but there is a chance that at least if it is a well-known target then at least uh one sequel would be sqlite would be found the same ideology could be implemented for excesses itself there are many tools such as h-a-h-w-l i know i don't know how to pronounce it but it's a really and good automatic tool to find seek to find accesses you can like give it urls it will just randomly enter payload there and yes uh you can see again in the parkour itself right because very there is no way the tools
itself could exploit it as well as give you the verification uh i would say limit your uh such kind of ideas to detection only and exploitation could be done manually
okay uh this is the last idea of mine which i'm going to talk about is let's say uh i i would say that many of the numerous leads or i would say like people of information security have made such good tools uh that that is available for us let's say ferox master ffuf g cow nuclei and bot i mean the list is quite quite quite exhausting you can like search on let's say secret finder link finder you can find tool related to it so what i would suggest is according to your methodology just grab those tools and change them together right it could be used for any and anything for example what i have done is
that you can grab a list of domains yeah right you can uh request gout to i mean all the list of domains could be input uh could be used as input for governor the output of the governor which be a list of euros could be like given to a graph command where each and every url is piped into this graph function where i am just fetching js files and this js files could be given input into the truffle actually truffle hog is a tool which fetches secrets from the gs file itself so yes uh you have like made an automation to find uh secrets from the javascript same can be used to find extract uh like
uh links uh in or apis from the uh js file itself which are not been called so this is your automation it it's quite simple right you can just tool you can actually you are just basing your automation on someone else's work and your works is also reduced as well as the other person who would also be happy that history is bad he's been used industry okay so this was the last idea of mine okay just a second
okay uh a bit of the warning before we like exit or complete our talk the first thing is the automation is here just to help you a bit it's like a additional hand that you can use in your pen test don't rely on it 100 right that i would use such automation and my work would get done the thing can replace manual testing ever even if either work from the all over the world and could control our brain it won't be able to pander because humans still maybe would be coding it right the the second thing is that over reliance on such frameworks could result into a high number of false positives and could uh like result into
the missing of for critical contributes so i would suggest go with the manual pen test uh like get some experience and with some experience you would be knowing what tests to do and you can like input your knowledge to make such automations right so i have completed my talk here any of the questions that anyone want to ask
okay i will be taking it from the chat itself uh yes so the first question that i answered was that yes i have some of the scripts which i would be giving out in my github repo uh which i will be sharing on on the slide itself so no parts of worry you can like grab that code and use it for your own purpose the second is is there any repos of fuzzing scripts to use with or osf uh i'm not aware of such uh scripts already that has been made uh my point in the uh in this slides was that you can basically like make some bash script right which makes such a request
and it is proxy throughput you don't need any scripts for burp itself you are just using the purpose of proxy uh let's say uh as your browser is processing data into the box same as the call would be proxying your data through the report so your work would be the log or logs where you can see that what request was initiated and what response were given so in that way i don't any other questions than this
okay and apart from that if anyone have any questions regarding to this talk or wants to talk with me or do anything you can just reach out at my twitter handle that is mentioned here and i would be happy to help
okay would like to ask
so thanks everyone for for giving out the time and really appreciate this opportunity
you





