Software Defined Networking and the Future of Network Security

Show original YouTube description
Show transcript [en]
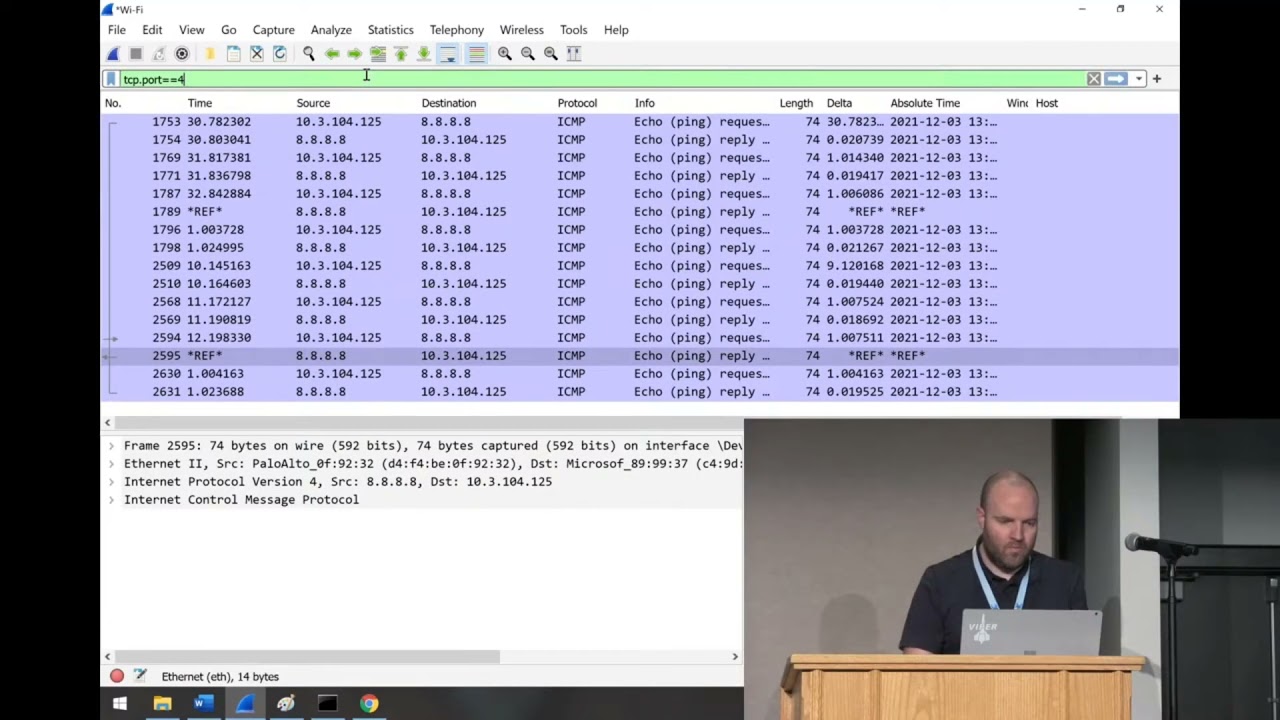
Welcome to a look at our current software defined networking solutions and moving target defense within them. So to begin, what is going wrongly with networks today? For a blue-teamer networks are difficult tools in the constant defense of users within our infrastructures. We find ourselves consistently needing to restrict users access to sensitive systems while maintaining a certain level of overall visibility of internal network traffic. In the current standard of set firewalls, and pre-defined trust groupings we can find ourselves with a less-than ideal situation. So let's look at it. What is the solution? Its certainly more complicated then just replacing one single device within the network, we find that to maintain efficient and highly customizable solutions we need to focus across multiple large platforms.
So what is it? Software Defined Networking is primarily looking at the brain of network functions and how they moved to a centralized location from the individual device themselves. Essentially SDN abstracts the control plane and data plane from devices allowing a central control mechanism to dictate flows across the infrastructure. So how exactly does it work though? In short, the core concepts of software defined networking solutions involve a centralized controller sending flows to switches across the environment. These switches then look toward the controller for instructions on what to do with packets that don't match pre-existing flows. This is all about flows, matches and actions. So let's actually look at an example. In a mininet environment, we can setup an abstracted centralized controller to observe a small mock-network of switches and hosts.
On the controller we can view each switch and see what exact flows it has within its instructions table, while across the whole network we can visualize the connection topology between hosts. So taking this to blue-teams, what exactly do we provide for our defensive solutions? First and foremost we give ourselves granular control of traffic as it flows between systems. We empower our infrastructures to maintain proactive defense in response to triggers from security appliances or suspicious network traffic. For red-teamers this can change the way network recon and initial attacks take place. No longer do we have consistent targets as network configurations can modified across whole systems in milliseconds. By leveraging moving target defense tactics, we essentially make our networks able to move a host to any location in our infrastructure. For example, moving a machine and its corresponding network services that are currently under attack to another network.
So what is the bottom line correctly from software defined networking? We can essentially make our network topology actively defensible while allowing for zero-human intervention in the heat of a system attack. Thanks very much for coming today, we really enjoyed being here. Does anyone have any final questions about our SDN and MTD solutions?