BSides Perth Day 1 (Part 2)
Show transcript [en]
up which is a local brevesque script it can enumerate various uh common local admin privilege escalation techniques which isn't going to run because it's blocked but if we use this powershell command which cool that's fairly legible we're going to invoke expression we're going to download the script which ah that's cut it off a bit uh there we go i found a scroll bar neat we've got the url there which is my local vm host but obviously it could be anything else um we're gonna so basically it's gonna run the the powershell straight from memory uh and then run the invocal checks command which it's running and neat we found some creds these might be local admin we don't know we'd have
to check cool you're paying attention that's great
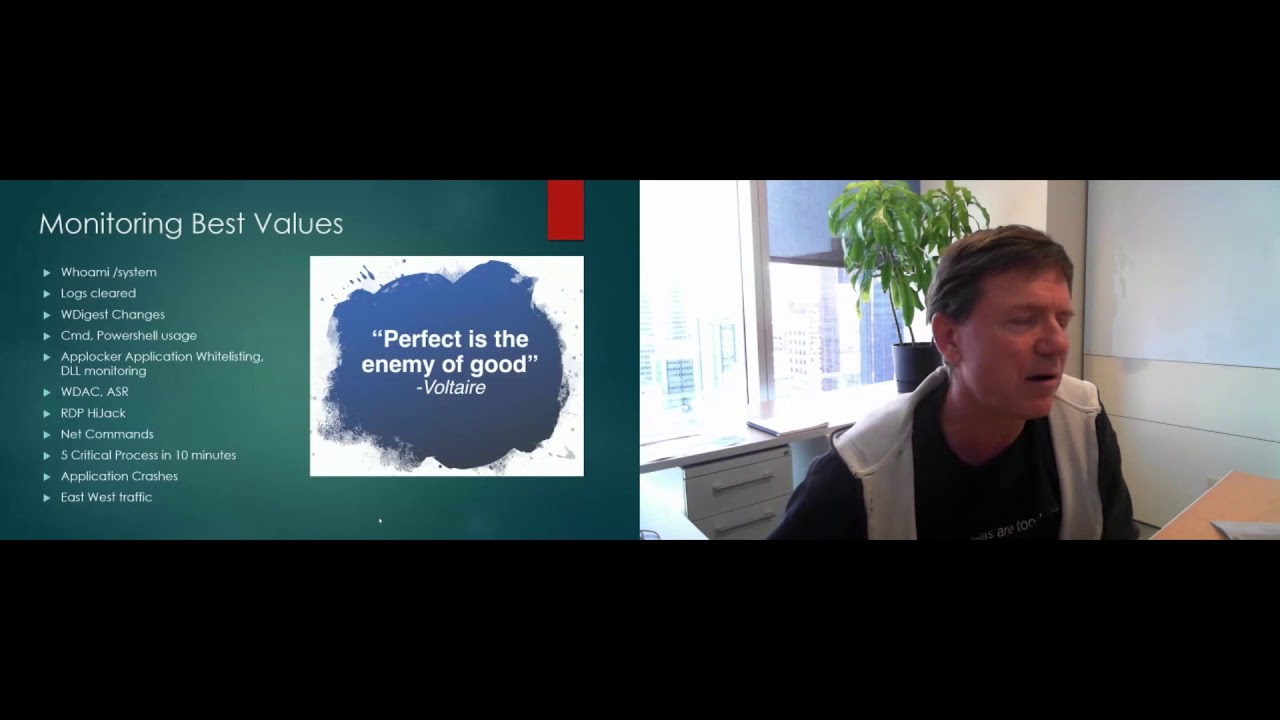
as we've seen we can't simply solve this by blocking file extensions on the machine it's not going to work you need a defense in-depth approach so if you're in an environment where you've got users that need an interpreted language like maybe python or another interpreter build up a policy for those users maybe it's data scientists devs sysadmins group them all in that and allow python or whatever your interpreter is to run just for them as for powershell there's a few modern modern security features from modern versions of powershell which can help detect and prevent these attacks script block logging can be used to take you can configure it to send any the code that you execute within powershell
to your seam where your analysts can have a look triage work out whether it's malicious you could probably even go a step further if you if you're really keen on working out which users really shouldn't be running powershell and trigger some alerts for that so you can go straight to triage constrained language mode blocks specific operations for running in powershell and um when i was playing around with uh with the download technique here um i found that on a system with powershell 5.1 installed and an app locker policy configured and script rules enforced constrained language modes was just kind of just enabled but i never found any good microsoft references that explained exactly what was happening there
as to whether there was any particular variables that were needed or whether it was just a blanket rule or even if it applied to just app locker and device that's a defender application control or if third-party products like like i mentioned any names any other commercial allow list products are able to feed into that as well so your mileage may vary i never found any solid proof but uh yeah it's definitely something to consider lastly animal wear scan interface or amsi can provide some visibility into the stuff that's happening within powershell to your endpoint protection you've got there so that might be to detect and block stuff too all this stuff is awesome but powershell
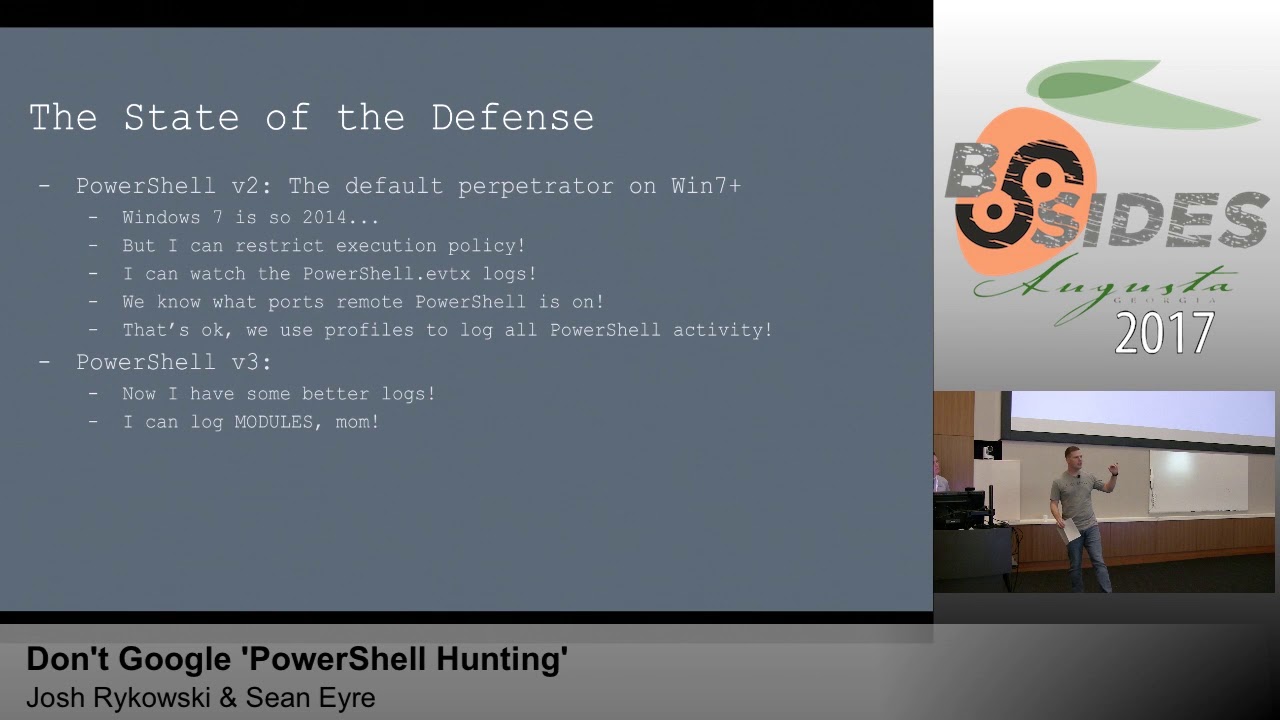
2 doesn't support any of it uh which means that if you've got powershell 2 in your environment you could just append dash version 2 to your command that you're running and it would sail past all those defenses so you want to block powershell 2 from running as well you might be able to do that through your allow list policy or maybe you uninstall it thinking back to our attacker with a standard shell again we were able to download the powershell that we wanted to to bypass the allow list which uh which as we just sort of talked about it reads constraint language mode to be disabled when you do that or you need to have
powershell version 2 enabled as well so it might not be as effective as some of the other methods but it really depends on the environment you're trying to use it in and with powerup which was the example we use we're able to look for local previous techniques and run look for any bugs that might let us get local admin but one of the other kind of neat things you might be to use this for is to automate enumerating the app locker policy and then poke at random for the the file path rules that come out of it so to really quickly give you the quick win that opens up that first file path use case we have where you can
just then run anything you want so kind of upgrading your attack from powershell to anything so where to from here for those of you that are lucky enough to have a loud listing enabled in your environment think back over all the weaknesses we've seen today think back about if there's anything that maybe you could you could improve if there's anything you get oh i really want to look at that before monday maybe do that and if you haven't already look into the microsoft recommended block rules to prevent your low bin attacks this is going to require you to plan out how you're going to audit monitor tweak as required because you're probably running some of this stuff
and then ultimately execute it to block uh the those low bins from running for those of you that don't have an allow list in your environment or maybe you don't have an environment i'm going to be publishing this app locker policy we're using today on github in i guess 20 minutes have a play around with it it was designed for this talk so it does have those vulnerabilities we've seen in it but it's probably got some others too so just don't go yeting it into production i don't know why you would but just don't if you're wanting to use it i'm going to have to suggest that you use a windows vm that's windows server
windows workstation os uh the enterprise licensing is needed for applocker to work and when i say that i i played around with this as part of this demo to have a look it happily imports the policy it applies the policy you can start the app id service it just fails open it's so dumb but uh the last thing i'll say is that if you do think you're breaking something there's a allow rule for any admin stuff so admin can run anything so if you really break something or something's not working as expected log in as a local admin on your vm clear the policy and away you go on that slide there's the references i'll probably put those couple of
references in the github when i publish it but you've got the the low baz stuff where you can look at all the different logins you've got the link to the ghost bill where we created our malicious xml c-sharp project and you've got the app locker policy which will be up by the end of the day before the years um any questions yes sorry oh kiwifruit is like the icon for mimikats which was like one of the first attacks we use but yeah
cool
thank you i have no idea how long that went for because
yeah awesome all right kill that
one cool okay thanks for us for that one um we are just not even taking a break uh we are getting straight on to matt green from rapid seven talking about velociraptor so that's a stream talk so we'll just fire that one up and get it going straight away thank you
hurting velociraptors so first of all a little bit of an introduction my name's matt um i work at rapid seven on the velociraptor project i have a background in dfir and detection things and i've been using velociraptor since the very early days the agenda for today is i'm going to cover a little bit of background on what velociraptor actually is i'm going to cover off um some requirements for incident response and then introduce kind of like a demo scenario that i've created that i demo a bit and test on and then i'm going to kind of cover off how we hit those incident response needs in in a demo the goal at the end of this will be to
kind of introduce everyone to velociraptor and then to encourage use and for people to go off and explore their own use cases and workflow so first of all what is velociraptor velociraptor is an open source digital forensics an incident response tool it's an endpoint tool that covers pretty much all the big use cases for dfir if you don't know who mike cohen is he's very well known on the blue team side of the shop but he was the lead developer in google rapid response and recall um so has quite a good pedigree in terms of building amazing tools essentially velociraptor was is seen as kind of ger 2.0 that's been built from the ground up up to be very
simple and solve a lot of the complexity problems that go had it's a single binary written in go for both the server and the client components and because of that it's statically linked and we support a very wide array of operating systems you can see the architecture is really simple i serve a client relationship the whole idea here is that simple architecture drives dfir at scale which is pretty hard to do and we're trying to simplify both the deployment as well as execution it's query language driven so if you're familiar with tools like os query you're going to be very familiar with the kind of syntax that we're using in velociraptor velociraptor query language is kind of formatted like you can see on
the screen we essentially generate our rows of data using what we call plugins we select columns with the selectors there and then we can manipulate data with functions and and and functionality that we have in the platform and finally you can see at the end we have filter condition it's that lets you limit return rows do things like um grouping and and things like that as well so with that in mind pretty much all of our use cases are driven um from that vql structure um you can kind of read what's on the screen here but what drew me to velociraptor was the customization it's essentially like a big swiss army life and when you're doing an ir
the available content in the platform is pretty good and we cover most use cases but the ability to quickly kind of write um ad-lib or to quickly roll out capability tactically for me was an absolute game-changer um i could quickly write some content short term that i needed to collect something or get a piece of data for research or whatnot um alternatively if i wanted to say apply longer term i could deploy a plug-in as well and modify the platform finally if if you're really stretched you can look at using some of our shell out plug-ins to just run third-party tools and things like that so it's that expandability that's critical when you're doing an ir
to just get the job done here's some links i recommend to everybody starting out there first of all our project page at the top secondly is a document and training page that has things like videos as well as like references for all of the functions plugins etc and finally you've got our discord community which has a really nice community of contributors and that i would definitely recommend plugging into that and asking questions to learn so the next kind of area i'd like to cover is some incident response needs and here you can see is access to data and this is a primary need of ir where essentially you've got your traditional digital forensics and instant response data at the top um
which is say volatile data like in-memory artifacts running processes network connections all of that stuff the middle section you've got kind of static data so think of that as like your logs on disk your file system your registry event logs that kind of stuff so that's more your traditional disk forensics and finally at the bottom you've got more your modern edr focus which for the most part it's heavily heavily processed focus um but essentially it's that telemetry that that gives you view on active threat um and all three of these are kind of critical to do effective ion nowadays on the endpoint and this is how velociraptor covers these use case um essentially the access to
data is driven by what we call accesses and i'll use the static the grey box as an example here essentially you have accesses might be file to access the windows api you might have read this system you might have registered access the registry in tfs to access raw disk system and then for plugins you might use those accesses um to pass the event log or or another forensic artifact um an interesting accessor that i'm going to cover today is zip which essentially lets us see inside zip files um and i'm also going to show blob which is kind of a plugin using a lot of artifacts that that lets you do exactly like globbies in programming um search
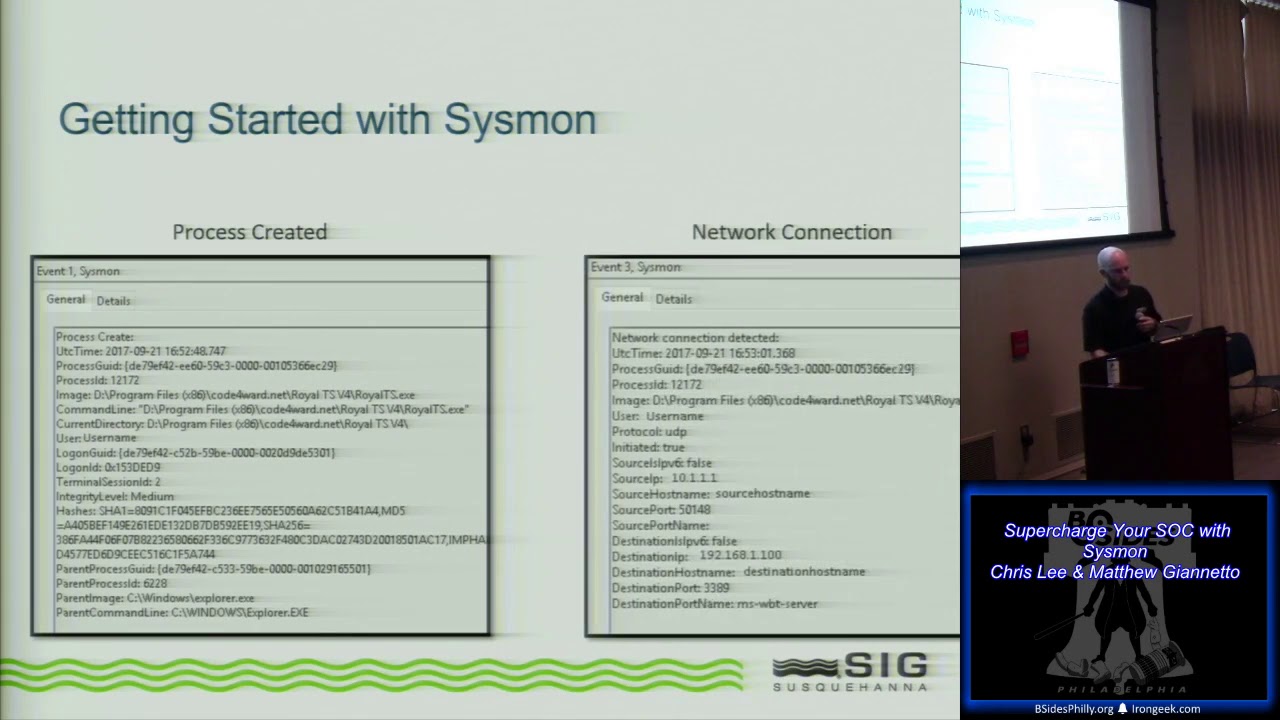
over the file system or registry um to look for things of interest on the right-hand side we've got volatone i've listed a few of our uh plugins there probably this is a good one to point out third-party integration where if you don't have a particular plug-in you can just write third-party integration i've put the example there as injection we can also run yara natively so there's a lot of capability that we have here in memory and finally event telemetry a lot of customers will use say a third party here like sysmon or an edr as kind of like a detection layer and velociraptor fits in very well in that use case where um you know you might deploy your idr
because they've got really tight detection for the things you're interested in and then you might use velociraptor for more of those forensics or live response use cases velociraptor also does our own telemetry if i have time i'll show it today but probably won't where we can leverage things like etw wmi we can also use um like monitoring artifacts and and monitor things like the event logs and that kind of stuff um so essentially i'm trying to set the scene here that velociraptor is this big swiss army knife of capability that that gives you visibility into the things on an operating system that an incident response team would be interested in like to cover off our
scenario overview for the demo essentially i'm going to be showcasing a an initial infection from a template injection use case and this is a really interesting sample the sample essentially doesn't have a traditional execution that you'd be able to review with an edr in that it just drops a persistence mechanism it drops a link file in a startup folder the actual payload itself is kind of side loaded by sign binary a custom encoded cobalt strike and if you're interested in looking at the sample i've added the hash there in the virus total section i've also added my fake template with embedded like payloads and things in there if you want to check it out there's some markers there that you
can tell it's made to make it easy the key indicators that we're going to use is the top right hand side so we're going to search and discover this particular threat out there okay so the first component i'm going to show is the discovery or identification stage of our scenario a velociraptor has the concept of hunt which is effectively running a vql across groups of machines in this case i'm going to be targeting all machines but you can say limit your hunts by pointing at say a group by label or by operating system the first artifact i'm going to add to the hunt is a detection artifact for template injection template injection is interesting because
instead of storing the malicious macro payload inside an office document an adversary will configure the document to kind of point externally for a second stage payload this technique is a defense evasion technique that to bypass maldox scanning on delivery it's also a similar technique to cve202140 triple four which instead of using a vba it uses a different payload but it has a similar style of configuration so i've added it into this artifact um the artifact itself is laid out pretty easy to understand we've got a search bob that's recursively searching the users folder looking for the document files we're then obtaining the path of all the document files and then we're using the zip accessor to kind of look inside and
look for those configuration files that we're interested in after we have all of those configuration files we're using the zip accessor again and we're pulling out the configuration the target um that i was referencing before we also um pull out like enrichment and um like timestamps as well as hash sections the document itself for presentation but the whole idea is we're able to then detect those malicious configurations that template injection or that cva uses similarly i also want to add an artifact called office server cache and this was submitted by one of our velociraptor users to our artifact exchange this works kind of similarly in that it uses glob as the main finding mechanism but it's using a registry glob here and
what it's doing is it's looking at an artifact that is generated when an office document reaches out to an external server there'll be a registry key that's generated and it's a really handy artifact for kind of giving yourself validation to find out if there was like an opening and there was that successful was that attempted connection out i finally i'm going to search for the link file that was referenced and this one definitely is an indicator of successful execution of the template injection and this is dropped from the the payload um you can see here we've got a glob that's looking for the link file that's generated and then it's using what we call a
binary parser to pass out the the details of that link file so once you select your artifacts you see you've got configuration and it's quite quite easy to add in changes or add in targeting we can select to upload if you'd like to preserve a copy or maybe analyze it offline but in this case i'm just going to launch it and when i hit play it's only going to take a few moments to run all of these are fairly lightweight detections interestingly the template injection is using as i mentioned the zip accessor so it can kind of see inside zip files um you can also run things like yara using our zip accessor it's worthy to note
that if you were going to use yara and just do a straight yara scan you may not have visibility inside zip file so it might be a bit difficult depending on the tool set you're using um in this case you can kind of see we have results here so at the top we've got a detection for our template injection and you can see it looks like it's a resume in the downloads folder we've got a section listing that settings.xml.rel so that is a template injection file and we do have our domain that was an ioc along with the template file reference there other useful kind of forensic artifacts are the modification time of the section
so this is taken from the zip file which is kind of interesting and the last two hits are from cve 2021 40 triple four and you can see there's a slightly different reference file there because the target configuration there uh is in a bit of a different location um also the template target is slightly different and in this one we're actually keying on that mh tml string inside the target you can see the second item we run in our hunt but we do have a registry key that's named our domain um so we can confirm that yes the the malicious vba ran and it did reach out to the internet and finally we have found the link file
so the link file has been dropped and you can see it's been parsed with relevant timestamps as well as payload on each of the artifacts we do have the fully qualified domain name of the machine that the hit was on so the next stage is triage of our machine in scope and we simply can search for it and here we can do things like add labels um we've already added a couple to this machine you can click on it and see additional metadata um some people actually use this client method over here for really advanced workflow like uh case management and allocating analysts and things like that but the first thing i'm going to show
you is what we call the vfs view and in the vfs view you can see on the left hand side we list different accesses so here we've got ntfs which is essentially parsing the mft at the top we have file which is essentially using the windows api to review the file system and what i can do is drill down and i can show you the items of interest there's ecmd.exe and this is one of the files that was dropped and we can see that yes it is an mz file i've actually already uploaded these to the server just to save a little bit of time in the presentation and here we have a cobalt strike
stager which is essentially an encode encoded in hex and then it's loaded by that executable and then this is the kind of view that you get from you know other forensics tools and enables you drilling into the file system or or the registry in a similar way
so the other thing i wanted to show was the collections view and what you can see is essentially all the vql jobs that we've ran on the endpoint and here you can see the hunt for instance and you can see the results um as well as the vfs browsing that we were just doing previously and as i click on them you can see that it's literally a row for each of the folders we're viewing or when we're looking at the file etc and this is a really good example to get your head around how how vql works in that every function on the client and on the server is just a vql query and when you start
to think that way you start to understand how you can really leverage a velociraptor to do some amazing functionality um in this particular use case the next step for me would be say a live response like a triage of the machine now a lot of customers they would run maybe a live response collection and collect relevant artifacts and in this case we've got a cape which is essentially a parody of eric zimmerman's cape files tool and what cake files does is lets you collect those raw artifacts in a really easy to consume way now in my use case typically i just do preservation so i've got a copy of event logs as soon as possible to the incident so i
can go back and take a look but you can see here we've got an easy way to select either artifact packs or individual artifacts that may be relevant and i can just add them together and just add what i'm interested in um i can maybe target the vss or target a different disk i prefer um some customers actually use a capability that we have in velociraptor called offline collector which lets you build kind of like a self running binary that will automatically execute artifacts and then you can give that binary to say an end user to run and then it will generate uh that live response collection for you um which is a really powerful capability some
customers even say add into that uh an artifact that will send the results to like a cloud share and again it's all fitting into the workflow that they that they decide to deploy with velociraptor for me i run lots of live analysis so in this particular use case i might be interested in scoping to see if i can find any files were written around the time of the exploit or afterwards within the attacker activity um so i might want to look at the say mft but one capability i have that i want to show is leveraging the velociraptor macro parser velociraptor has a plug-in for vba parsing and you can see in this particular artifact what i've done is
implemented the ole tools macro raptor capability in vql um so what we do is we parse essentially the same as last time a glob recursively looking in the user's folders and that's going to hit things like internet file in temporary internet files what we do is once we parse all the documents that are associated there i then run a regex over and look for these parameters and what macroraptor actually does is macros will always obfuscate bad guys will obfuscate and try to hide their malicious code but there's some things in malicious macros that you can't hide like autoexec that has to be unobfuscated to actually execute um so that's kind of what we're looking for
and this tool is absolutely amazing as a first step to run over macros and we can run that capability remotely so i'm going to bounce through this and show you and obviously you can change the search terms if you prefer um but when that runs we should get results popping back again pretty quickly and you can see straight away we found temporary internet files you can say it's the same this you can see it's the same file name as our template that we discovered in the previous hunt and then you've got a copy of the vba code i know that view isn't too good but we can actually download um a csv then copy paste it out
you can see we have a malicious macro there you can also see we're detecting on user forms and those user forms actually have the payloads encoded in them so this workflow typically might take you know a while you need to look in the mft you need to then search temper internet files and you need to go back and make sure you've actually downloaded them and collect them again but i'm able to pull this information back in a matter of seconds and that's pretty pretty amazing pretty amazing workflow
okay so next up i want to triage the binary that was dropped so i've written a little artifact that essentially extracts things like pe attributes and authenticode um it works by taking a glob target and in this case i'm globbing program data and all files located in there this one is super fast and when it returns results you can see its output file information um system information timestamps it's worth it to note we can add file name timestamps if we want to use um our mft parser and our ntfs artifacts um it also is included um pe information so you can kind of see here things like pdb i'm good for research information but this particular binary is claiming to be
an eset command line tool um import that dll import um does reference um a.net binary um there's no exports but interestingly authentic code so the file itself is signed but it is invalid this is a really good point uh to make with velociraptor uh because we're on the endpoint our authentic code parser we'll also look at things like catalog files and we'll be able to validate binaries really fast i've recently written um an artifact and some monitoring for the print nightmare vulnerability where i was monitoring for a print creation event and then i was using this kind of enrichment to look for untrusted binaries and these are the kind of use cases that you can build out and there's
lots of options for us okay so one other thing i'd like to follow up in terms of this scenario and that's a cobot strike parser okay so in terms of cobalt strike parser um the artifact itself is doing a lot of things um we're using a feature that we call binary parser but before we do that we're extracting the config out using yara um cobalt strike is interesting in that typically the config is uh xored um and it's either xored by 69 for an older version 3 um or 2e for the newer versions i've also included the option here to brute force if anyone has maybe modified cobot strike and decided to mess with it so
i'll select that but what we do is once we have a hit for a configuration pattern we'll then extract bytes and then we will run our parser profile over the top of it and we'll also do things like detect so you can copy paste some yarn here that you'd like to run as a detection use case um in in terms of selecting what we want to run the config over we can either scan on disk and use the glob or we can specify a process id or a process name that we're going to run on so i'll launch that and it's actually pretty fast um cobalt struct itself isn't really anything special in terms of um
how it's configured in that it's just a simple kind of an index type length and then value structure and velociraptor's binary parser is really simple in there it's kind of like volatility v-types and it's designed essentially to overlay um over the top and very simple to be very repeatable um and in this case i've literally just you know copied all the other parsers out there and have enabled extra extracting the config really quickly um so what we're doing is we're essentially cutting out a step of triage here where typically you might have say a detection via scanning memory by error and then you need to dump the process and then analyze it here we can just run
this content to extract the config straight away and you can kind of see all the configs in here which is pretty awesome in terms of speed i've also included the decoded data so you can take that and run additional analysis on it if you need to but i think this is a really handy capability it really showcases some really advanced functionality that velociraptor can do i think just to close up in terms of the demo part it's probably worthy to touch on some of the other capability that velociraptor has and that might be useful i haven't really had time to showcase like our event log stuff or any other content but essentially because we've got access
to data we can do things like regex over or grep over event logs and have detection and scoping use cases there what i would like to show is some of our yara artifacts so in terms of deploying error i've got a cross-platform yara capability here that will hit linux mac or windows using our glob function and you can kind of see the description here um we select the yarra rule either via a url or shorthand version or just copy paste the arrow rule in and then we can run a whole bunch of blobs to hit we've also got an ntfs version which does the same thing but searches with ntfs fields and finally we've got our process yara
which by default will search for cobot strike but literally you can copy and paste any arrow rule in these rules and and scan for the the targets in scope um it's really handy and it really helps with detection um and not not only detection but discovery and identification when you're doing doing an engagement the wrap-up for today is velociraptor enables sirius dfr at scale there's something for everyone um my advice is to work towards building your own workflow like like i was touching on before like what i see is typically people will start out doing like traditional live response then as they get more mature they'll start to do more live analysis they'll start to
build out use cases with things like soar and automation and things like that but just start playing with it um and you'll see like how easy it is to modify and the modularization of it just makes it an amazing tool to work with and most importantly join the community because the community is just really starting to take off now compared to even a year ago like we've got exponential amount of people coming into the platform and a lot of that is just drawn by the word getting out for how awesome the tool is our goals are to essentially make velociraptor the default dfire tool and not only endpoint forensics but instant response um doing a bit of malware
analysis you can just run really awesome use cases using velociraptor and here's the links again um that i've hosted before i won't read them out you can see them um but feel free to contact us you've got myself and mike who currently are permanently working on the project but also i adam wes in here because he's done some recent talks that have been absolutely amazing talking about some workflow with voice raptor so he's worth following as well but follow us on discord and you'll you'll get a lot of value thank you that's it hurting velociraptors so first of all a little bit of an introduction
first of all a little bit of an introduction
to everybody on youtube
to everybody on youtube that concludes the online portion of day one for streaming so we'll see you tomorrow back here 9am perth time okay let's kill it kill that cut
[Applause] everybody is still physically here we have one more talk so gareth come on up
my
[Music]
[Music] [Music]
[Music]
[Music]
[Music]
[Music]
you