WEANING THE WORLD OFF PASSWORDS
Show transcript [en]
[Music] like garland Sherratt I'm with HootSuite security architect but the views here expressed are my own that's a little bit loud for you guys everyone's good okay alright so I want you to realize that you've entered a bit of a different world I call it garland or the land of gar so a lot of the speakers here are here because they're experts I'm an expert because sorry I'm here because I'm not an expert I thought that identity I still think identity authentication very interesting subjects and I wanted to learn more about them and I thought this is a good opportunity for me to have do you have that kind of force learning and now I want to share that
with you guys so what I want to do is essentially survey the whole space a lot of it anyway of authentication a little bit of identity and leave you with a foundation a way of looking at the space and understanding what's going on especially with passwords but also with authentication in general and I have to say I'm pretty grateful to be able to speak to here today so I normally cringe when speakers do polls but in this case it's appropriate I want to start you thinking about some of the issues so here number one how many of you think that passwords are bad ends up please okay all right number two how many of you
would like to get rid of all passwords okay a few less than I expected this is good and how many of you think it's possible to get rid of all passwords hmm okay you guys are going to be a good audience okay so I spent a lot of time reading and reading and reading after this presentation was accepted for four b-sides and I knew I had a problem when that document I collect with all my thoughts came to about 36 pages so that's 36 pages of a Word document small print so you can imagine that kind of condense this down into 45-minute talk is a bit of a challenge I hope I'll do it justice so the topic is the title
winning the world of passwords so what does weaning mean weaning is only for mammals it's essentially the idea of taking an infant of that mammal getting it on to adult food getting it away from its mother's milk and if you've spent any time on a farm like I have you know that weaning is quite a distressing process and it's distressing for not only the service provider but also the user so passwords are going to be the same way it's going to be distressful to get rid of them it'll be disruptive but I'm going to show you why there's hope so I'm going to talk a little bit about all spaces to try to try to cover enterprise business
to consumer and also the personal space as well so passwords started a long time ago probably the beginning of human civilization certainly you know organized civilization but in time should in nit password started with time sharing in the nineteen sixties the idea being that a user you don't tend to get yourself to the mainframe quite a different situation as today now passwords are a form of identification and authentication it's always been a game of cat and mouse there's the bad guys fighting the good guys new ideas on one side opposing ideas on the other side the whole subject of identity authentication fascinating areas and I become more and more interested as I've gotten into them and I encourage you to
go do some research as well to start you off with a very very simple view you can look at identification as using a user ID to assert an identity and then after that you can look at authentication as using a password or something to prove that identity now that's a highly simplified view but it's a good place to start so there's a whole bunch of things wrong with passwords let's let's start one of the major ones is the passwords push responsibility on to users that they're simply not prepared to handle and they they do not want that responsibility so they find it really hard to manage them you have to keep those passwords secret you have to store
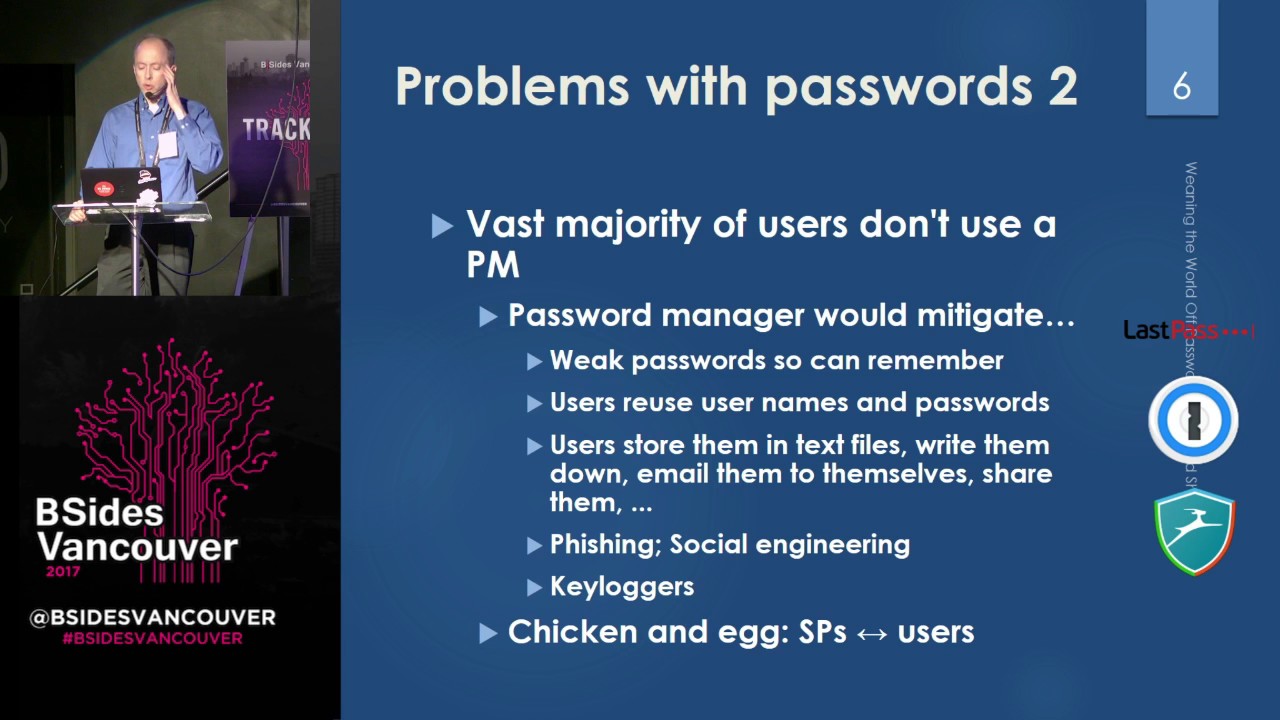
them for a long period of time and of course users can't really create and generate good quality passwords and they can't create and generate and use and store unique passwords across all sites now it turns out the only way today to manage the chaos of passwords I think I've got about 300 I remember those the only way to do is with the password manager and of course when you start looking at this you discover the first thing is that the vast majority of people don't use a password manager now in this audience my guess is going to be that half a you do I don't know let's let's take a poll how many of you use a password manager
it's more than half that's very very nice I don't know how anyone would survive without it but a lot of people do now I'm going to start with some of the problems with passwords so these problems that I'm talking about on this chart are in fact all solvable today with password managers if the majority of people use password managers those problems would either be gone away or they'd be mitigated so weak passwords people choose them so they can remember them at Deloitte study 2013 found that six mill million passwords and they found that the 10,000 of those passwords that were most used would access 98% of the accounts so you rankle the passwords that the one the 10,000 that occurred
the most did all the 2% of accounts it could open them up pretty scary right that's massive reuse so users are routinely reusing passwords and usernames of course because usernames are often email addresses they store them in text files they write them down they email them to themselves they shared with other people users are subject to phishing social engineering key loggers on their devices now all of these password managers would help with but the fact is people are not using them they haven't sent something's wrong but they're just not using them there's a bit of a chicken and egg in fact there's quite a bit of a chicken and egg until users all have password
managers or the majority do service providers cannot insist on long complex passwords and until service providers insist on long complex passwords most users who are lazy quite frankly in their computing are not going to go get themselves a password manager so we're stuck it's it's simply not going anywhere now some other issues with passwords a lot of service providers don't manage passwords well thankfully the things going away but someone and still collect passwords over HTTP and some of them still collect passwords for third-party sites using by directly collecting user IDs and passwords they should be using OAuth a lot of them have to learn now at the in the enterprise space one of the big thing is you're going to run
into is probably have run into is shared accounts and the issues that causes especially with off-boarding so a lot of accounts have more than one person using the credentials when the people leave company should be changing those credentials do they oftentimes not now help desk help desks cost a lot of money to run and a lot of those help desk calls are actually for password changes there is a study by mandiant labs just this year average enterprise spends $180,000 on password resets for every thousand users $180,000 for every thousand users and on average about twenty to fifty percent of all the calls to the help desk were to reset passwords so with the problems wire password still
being used there's a lot of advantages to them it worked for about 50 years and for users they're pretty easy to understand users have no challenge at all you don't need any special hardware you simply walk up to any thing in the world today and you can log into your account may not be safe to do that but you can do it it's easy to change your password to revoke the account if you forget your email you simply request a link through email you've got a new link to log in and it's very easy on the other side for the service providers to implement every every language has libraries you know to implement password systems there's also economics I find in
any space not security I mean everywhere it's really fun to look at the incentives that are making things the way they are now here you can see essentially a tragedy of the Commons or in economics that's called a negative externality it turns out many types of market failures a negative externality is one of those types of market failures if you're interested in economics like I have encourage you to go read all the flavors of market a constraint of market failures quite interesting so a negative externality is when two parties are in a transaction and some third party is being hit with some negative benefits so they're not involved in the transaction but they're still still being impacted by it so in
in password security you find that low value sites have no incentive at all to improve the security of their authentication systems so when there's breaches say their password files are stolen it's the high value sites that are impacted because people reuse passwords any and user IDs so the high-value sites get hit by going to drive-by shootings in a sense the low value sites have no cost at all because their stuffs not of high value and you find that okay yeah let's that's enough I'm doing pretty well I've got I've got 12 minutes down and 10 charts down so I can I don't have to rush quite as much as I thought I might need to so I'm
going to start with the issues what are passwords so passwords are a shared secret now shared secrets can be good and bad in the case of passwords good and bad where do you see passwords most people think about passwords as the logins for all their accounts of their web accounts they think of those passwords but there's other places too where passwords occurs so equally important and in fact you could argue it's more important because it gets less attention and I'll talk more about this is account recovery so account recovery uses a variety of mechanisms I'll talk a lot more about this but passwords are clearly one of those you would know those passwords as challenge/response or security answers
and questions or recovery one-time passwords all those are essentially passwords now there's also master passwords people call the master passwords for things like password managers so it's kind of a meta password it's not a password to a simple account it's an account that gives you access to passwords for a lot of accounts and of course there's device password there's your computer password your phone password so passwords are one form of authentication factor what are some of the other forms so you all know MFA and authentication know have an AR so have can be hardware or software you've got mobile devices smart cards and they're on the software side you've got seeds for your DOP totp devices
software and hardware in the old days and certificates and then what you are typically comes down to biometrics and I'll talk a lot more about this as well fascinating subject so everything you can imagine about your body has already been or will become a biometric and people are now adding additional factors like location and more to come the biometrics are definitely all the rage and I guess it probably started with smartphones so I've got to come up with a way to categorize biometrics it's my own personal way of doing it I'm sure there's many ways of breaking them down but I've tried to think about the risks the relative risks of the different types of biometrics so I've broken it
down into two four different categories so contact is where you actually have to be at the person in order to measure the thing to record it so fingerprint and DNA are really good examples of those things that could be done at a distance kind of more interesting right selfie photos selfie videos even your iris scans could be done at a distance visible pulse on your skin can be done from video very interesting stuff persistent things so fingerprints and DNA hangs around everywhere you go you leave your fingerprints and your DNA and there's more things to come kind of science fiction a few years ago but people are starting to do them invasive so invasive meaning kind of affects your body so you
swallow something you implant something or you can tattoo something and there's more so one of the issues is biometrics is that they are slowly in some instances at least replacing passwords touch ID on my phone a lot of the time as I turn my phone on and use it it doesn't ask for a password it asks me for touch ID there's windows hello realsense cameras so it raises a really important question that I don't think it's adequately dealt with and that question is are biometrics more like passwords or are they more like user IDs so I want to ask you guys how many of you think biometric various kinds more like passwords how many you think more
like user IDs okay could you all come up here and do the presentation okay all right so I see I'm preaching to the choir very nice so the issue to the biometrics they're easy to steal and you can use them without the owner of the biometrics being aware of them that's um that's a big deal so persistent and remote type biometrics in my taxonomy there those can all be done it can all be stolen and used without your knowledge and of course even with your knowledge one of our government's probably have your biometrics how certain are you that though that data is really safe with them biometrics can be fooled so iris scanning can be fooled by
photographs if it's not well done fingerprint verification with Plato and there's stories about people when they're drunk sleeping having their fingers used on their phones so that the point is that biometrics are a lot more public than passwords you don't go around telling people your passwords at least most normal people don't but biometrics you you spray them around essentially so if you look at a spectrum passwords on the one hand or quite private user IDs very public biometric somewhere in the middle and very interesting hard to define space in the middle most importantly I think is that you can change your passwords you can't change your biometrics if if your service provider has a breach you lose
your password whatever you can just change it if you lose your DNA if you lose your iris scans if you lose your fingerprints and I would argue they're already gone then you can't change those they're yours for life unless you believe in too much science fiction so I would say the conclusion is that biometrics are a factor of authentication but they cannot be relied on entirely and cannot be fully trusted either so I'm going to try an experiment here I hope this works so there's this really cool clip and let me let me just do this a simple way I will extend you see that Oh sir duplicate okay so I want to set the scene a mind share has just happened
or has it here we go
[Music]
[Music]
[Music]
i gathering that you probably didn't hear a single word of that am i right
let's do this again alright so I have to tell you what happened so a mindshare did it happen or not you've got to prove whether it's you or not you biometrics don't work after a mine chair because you've got somebody else's body right or the body goes someone else's mind big long password master password okay that would have worked better if you could have heard it so an important consideration for passwords for biometrics especially for a few different types of authentication is the local versus remote dichotomy so the key point is what's appropriate for local and what's appropriate for remote authentication so locally if you're talking to your computer your phone what's appropriate and I would argue
that when it's a local authentication it's okay to use what I would call unstrung methods a password biometric those are things that are very useful for authenticating you either fully or somewhat but they must not leave your device you should not be sending passwords across the network you should not be sending biometrics across the network if you have any interest in this subject I'll point you to the global identity foundation their principles of identity in 3.0 principle number 8 talks about biometrics fascinating stuff if you get into identity you'll be spending a long time reading it's really fun so remote or cloud on the other hand I would argue you need strong methods you should be using methods based on
publicly public key crypto should not be sending biometrics should not be sending passwords across the network now how do you mitigate passwords passwords have a lot of faults and you can mitigate them you can replace them so I'm going to start with some of the simpler ways so on devices there's biometrics that can partially replace passwords so you know that your phone sometimes a super password most of the time asks you for biometrics the biometrics are meaning that you don't have to use your password quite as often and it lets you lose essentially a longer password if you want to now two-factor authentication passwords sorry with two-factor authentication you can essentially reduce the strength of the password I'm
sorry we took that authentication you are able to have an additional factor therefore you don't need a strong a password now some of the ways of doing this totp you can fish them real time though as the previous speaker just mentioned there's out-of-band aka mobile push and there's five boat Fido UTF Universal second factor which is based on a hardware token and public key crypto very nice stuff something coming up is called by few different names so I've chosen to call it adaptive continuous authentication it started out as risk-based authentication it's also called behavioral and any combination of the words I've just stated so the whole idea of adaptive is that you're looking at the risk of the action being done and
the risk of the act or of that action and continuous means not only when you log into your device your computer the whole time you're using it you're continuously being evaluated for risk factors so essentially your device the cloud potentially has sensors that are that are being used to collect risk type information and make decisions in real time banks started out with risk based authentication in this so there's a few different flavors the bank one I mentioned that's primarily cloud based there's local base and then this combination of local and cloud and Google trust API is something interested to look at it's a risk based system so with passwords you can easily hide them today using password managers
and using something called a few names but secure web authentication a type of password manager built into some SSO systems secure SSO secure web that education is not sam'l I'll talk about that a bit later
so if you really want to stop sharing passwords and sharing I mean between sites so I mentioned before the the need to authenticate or to gain access to resources on a third-party site so oh I'd lets you do that in the old days your your site that wanted to post to your Facebook page would collect your user ID and password it's such a great idea because then they've got it too and they can misuse it they can lose it Oh on fixes that and others really I would say one of the marvels of the universe and and if you ever have a chance of using it you definitely should and anybody who is still collecting
credentials should definitely move to OAuth type systems now a complete replacement some of you will definitely recognize these how many of you have ever played with client certificates okay so quite a typic time around a really long time they have a long history their form a public key crypto they're essentially the reverse of a server certificate so normally you care about who the server is and you only want to go to that server if through TLS if it's if it's the right server client certificates are the reverse the server cares about who you are and the server knows who you are and whether you should have access there fantastic idea in my opinion I've never actually played with
one my understanding is the issues with server side with client certificates essentially bad use experiences for managing the certs so certs they interact with browsers with operating systems with multiple devices and then around the issues these days I've got four different devices I use for various things I want everything to work seamlessly amongst those devices how do you do that with client certificates now I got to thinking everything with this for a little while I've seen this a few other places a couple other places on the web people thinking the same ideas but it hasn't been pursued what if everyone had a password manager would my password manager be able to manage my client certificates and sync them between
devices store them securely as easily for my client certificates as it does for my passwords I think it might however I wouldn't put money on this I think TLS certificates have probably passed their opportunity window so replacing passwords will keep going I'm going to talk about how authentication can be put from passwords to other things and in this case hardware things so hardware tokens have be around for a while in the form of smart cards totp tokens those are those old secure ID things I'm pretty sure every single one of you if you're old enough at one point was carrying one around I certainly did and now more recently Fido UTF tokens so UTF token is client-server and really
nicely secured there's also increasingly smart devices doing this you no longer need a piece of hardware your phones your watches your tablets your your nimmy bands the really important thing is that you've now got something in your pocket that used to be the special piece of hardware and this opens up the door for all sorts of new authentication things now I want to talk a little bit about trusted computing trusted computing started out with things like TPM chips and it's moved on to mobile devices like secure and clave on Apple and I forget what it's called on Google the idea is that there's this little hardened processor in your computer your phone which stores your keys and protects them
from the bad world and also protects them from you so it's a kind of intelligent thing has its own mind in a sense storing your keys and enabling you to do secure public private key type protocols this is a really key increasingly all high-value or you know high-end devices have secure computing and it really changes things so moving on to replacing passwords with software this is all quite interesting so in the consumer space you might have heard of Open ID Connect it's gone to a few flavours started with open ID then moved to open ID Connect open ID Connect is a combination of open ID and so on so the idea being that you've got you know what maybe a social
logins of Google Google Facebook Microsoft Yahoo all of these are pushing this because they all want to be your portal to the rest of the web so they're doing you a favor in the sense you've only got one set of credentials to lose and to manage but they're also trying to grab you into their ecosystem now in the enterprise space sam'l is the big winner so security assertion markup language it's very much like Open ID Connect by the enterprise space and enables you how many of you use sam'l RSS oh I should say in enterprise I would have expected more okay so it's fantastic my company has it amazing thing log in once and your hundred services or more are all
off the same credentials now phyto UAF universal dedication framework is software as well it's in the same suite of protocols as by those u2f and you can look at a little bit like SSO in your pocket your device lets you log into a bun services with kind of pre stored keys and an issue though is how do you do this between different devices so let's dedicate a one phone does your tablet work automatically account recovery I looked at this before it's a pet peeve of mine and it's something that is a mess in my opinion and it gets not nearly enough attention so today as nearly as I can figure the best thing you can do for account recovery is to
answer all those security questions with completely fake answers and store those completely fake answers that are long and random by the way in some other completely safe place how many people do that not a hell of a lot so challenge response essentially account recovery mechanism is very hard to manage for users and users are encouraged in fact you know what's your favorite pet dumb idea right so as a result service providers are tending towards preferring recovery using other mechanisms the other mechanisms they tend towards are email and SMS do you think email and SMS are secure probably not so if you compromise the email or SMS you've now compromised many of the accounts that rely on this mechanism this by the way
recently deprecated the use of SMS for multi-factor authentication what are some of the alternatives to this in the enterprise it's probably not a big deal because there's help desks and help desk you know they have ways of authenticating users in the consumer space it's a bit more problematic to come up with good solutions there are some real-world identity verification services but you've probably never run into them so you can you can authenticate with with a mail service so the governments of Canada tend to use that for some things works well take a few days people don't like that in Germany they have the post ident system where you have to go to a post office
to to authenticate yourself and recently Facebook has created Facebook delegated account recovery so for github and more things in the future likely I'll mention that Fido doesn't cover account recovery and I want to say that this whole area needs a lot more attention that it's getting because authentication you know everyone looks at that they don't think about recovery but recovery can take over your account as easily as bad a dedication or lost authentication so it's pretty obvious passwords aren't perfect why are they still hanging around so a lot of lower risk lower value sites have simply no incentive to movement to move beyond them a more kind of positive reason is that for multi-factor authentication you need
multiple factors and and I'm going to argue more and more as good so something you know is pretty important you never want to get rid of that something you know as one of the factors in your authentication so what happens if you cannot use a trusted device for some reason so you you've lost your phone you have to log into a public terminal heaven forbid if you use a friend's phone friends computer or you live in part of the world where you have to use a public terminal maybe you don't have a cell phone what do you do if you don't have a trusted device then a device you own that you're reasonably sure you know
what's happening to it and you can't store secrets on the device for instance so it's really important in that case that will fall back into ekend ism of passwords I do want to mention some privacy concerns as well not of passwords but of some of the alternatives so with SSO all everything is tied back to that identity provider and that does create privacy concerns it means that more tension as you paid to this so you need to look at schemes sometimes called variable authentic identity so you create pseudonyms for some types of services you can create anonym x' public key crypto makes this possible it makes possible all sorts of really cool stuff and identity now where
are you still going to need passwords indicated you can't get rid of them you don't want to get rid of them where do you still need them so device passwords as a fallback to the biometric and underlying the biometric your device password is really the thing encrypting your phone it's the biometrics that are kind of a key into that now master passwords as well master passwords password managers you have TP managers if you like doing that kind of thing like Aussie there's debate about that but that's certainly a valid place for a master password and of course rested so you could you could argue that the password getting you into SSO system is kind of like a master password is it
matter password I talked about giving you access to multiple passwords now you used to you're essentially moving from a world where you had n passwords like 300 in my case maybe a little bit more to a few passwords and I want to call those those end passwords what I call them forgotten passwords essentially they're forgettable they're forgotten they're typically bad passwords with a few good passwords I want to call those memorized passwords so they're memorable you make them memorable you remember them you pay attention to them I think a really key point about the first point I didn't mention this but for device passwords it's really important to recognize that a lot of things in the world are
starting to push authentication or delegated in this end to your device they'll happily let you use the device to authenticate the service or second fact or whatever that means the security of your device is pretty critical those services in a sense are letting your device choose for you you need to pay attention to that device this is my second last slide so I want to say there's no silver bullet for for getting rid of passwords but you can see that the trends are all going the right direction so two trends decreasing number of passwords you're going from one password per account to a couple of master passwords that you guard with your life well not literally
so Hardware tokens smart devices the UAF of Phi oh not to be confused with you to f SS o and o on are all things that are going to decrease the number of passwords in your lives and on the other side there's a whole bunch of things that are causing you to need to use passwords less often so password managers are clearly one of those because they hide that complexity from you see OTP will push the you to F of phyto biometrics definitely and I'll say a bit more on my ultimate slide and continuous adaptive authentication as that grows over time we're still very early that grows over time that'll have a big impact on decreasing
number of passwords and asking your password only when it's really important for something something critical so some final thoughts for you don't over rely on biometrics don't trick don't treat biometrics as as an absolute truth they are very far from that and don't misuse them don't send them across the network don't store them into database somewhere bad ideas they're very much ok on your device on your computer stored locally and something you control but don't send them across the network account recovery definitely pay more attention to this it's really important that all aspects of authentication of a service the rebalance not only the login portion but also the recovery at the backend now for businesses I want to
encourage you to not allow users to use dumb passwords now what's a dumb password it's certainly one of the top thousand most use passwords and I'd argue even the most 10,000 10,000 most use passwords with bad choices as well it's great if you can block users from choosing those passwords and also block them from choosing otherwise we'd passwords like too short for instance for the industry as a whole I talked about incentives before I would love to come up with a way to create incentives for the use of password managers I'm not saying pasture managers are a solution to everything but today given the technology today deployed given the critical mass and the weight of all the
websites that use password managers desk you can do today to manage the complexity for users how do you get to a point where users want to use a password manager if you can figure that one out you should go buy stock in the password managers and go work for them I haven't figured it out I - of any thoughts in the coffee break I would love to hear them and then the other side of this essentially how do you create disincentives for dumb passwords for companies allowing people to use dumb passwords how would you encourage all sides to disallow dumb passwords weak passwords and even more importantly how would you ever create a way of
preventing reuse of passwords if you could create a system that would prevent reuse of passwords you'd be solving a lot of problems now I created one of these myself it so happens if you go look for my blog you'll find it it's a little bit controversial but it's definitely a way of doing it now on the government side governments have a mixed record of doing things they do good they do bad a lot of people in security automatically dislike government intervention and redaction but I want to argue there are some places like the tragedy of the comments those market failures where government's can't have a good role to play so I would like to find I'd like to see
whether there's a role for governments in in regulating some aspect of authentication to help solve some of these problems you can get a little bit of a flavor of some of the kind of thinking Bruce Meyers recent vlog on thoughts about the need for regulation in the IOT space I would encourage you to go read that and if you're not following should I or definitely do so that's it that's it for my presentation I've left a fair bit of time for for questions and let's don't forget to wait for a microphone please I noticed that some of the canadian banks for instance force you to use a particular length password and following a particular format how on earth could this be
beneficial for the user so i length
I'll repeat that so he's saying more cannot pass her cannot be longer than six cannot be shorter than six that that's pretty plain dumb no idea I never heard of that one I can't even see there's a lot of legacy things right so oh can someone give them my key this is really interesting so part of the reason you do that is so that the users don't reuse passwords if you have a completely different password format you prevent somebody from using their Facebook password on the bank security risks the bank face are not password guessing because like you said we detect any sort of multiple attempt so that's not where the whole is effectively thank
you I'm glad we could get that answered that's really interesting so that's trying to work around the problem of as mentioned before with the vast majority of people out in the real world not in this room don't use password managers trying to work around that quite an interesting solution
my company has a nerf cube with a microphone in it and we toss it around to speakers for questioners pretty interesting yes please hi thanks for the talk I'm just wondering if if we're using password managers could we not just give people the password instead of saying make up your own password and then it's gonna have your dog's name or whatever just here's the password that you should use and it's you know 32 characters long and very random that's a fantastic question so you recall I was talking about my blood exercise what if everyone had a password manager could you somehow start using TLS client certs instead of passwords it would open up all sorts of
new ways of looking at things and this in fact is one of them rather than hoping users who choose a long password complex you'd give it to them and of course you know it sounds nice right I'd love it because I use a passive manager religiously most users would would croak on that would definitely find another website to use they never go back so it's it's part of the chicken leg that I talked about again you until you have the critical mass you can't do these things and without with the critical mass you can't get there it's a it's a no-win situation requires a bit of intelligent thinking any more questions yes so I mean this is a literacy issue
as soon as the users can be educated to the ramifications of using weak passwords they will then be invested in not doing so so being able to at least have a parsley shoulder the burden of responsibility is the key here and because this plays such an impactful role across so many different services in our society then there are a number of different bodies from organizational to governmental that can actually help to raise the level of literacy around the need for robust passwords so why are we kind of granted we're expecting the users to be lazy or unwilling etc but that is actually where we can be most impactful instead of trying to enforce some sort of mechanism
yes so did you guys hear that yeah okay so I'm not very hopeful about the ability to educate users too or give in to them to start using password managers and good password hygiene and good device I Aegina and all those things I honestly don't know how you would ever do that you could issue everybody at birth with a little implanted you know implanted token with their certificate but that might have problems as well I can't imagine how you'd ever educate users I'd love to see that I've often thought I talked about government action I've often thought that government should be doing more to educate people just like you said but it's interesting I'm not
aware of any governments that have really done that in any serious way and I'm not holding my breath any more questions
this is possibly kind of an edge case in terms of past reviews but kind of recently there's been reports of you know crossing borders into the US where some will ask you for your Facebook password so what's the interplay there is like oh I have a specific password for Facebook versus let me login to last test and get my Facebook password it's like oh no give me that too so I can look at all of your passwords and kind of how do you can you think of that so might be ways to mitigate those circumstances that's a really interesting one you know you guys probably all know I mean I read every single article article I can find about
border crossings and impacts and troubles the the big think remembered a border crossing is you have very few rights at least in the short term so to do that yes very interesting question if you tell the guy I can't log into pacer at Facebook I don't remember the password Oh login your password manager no problem however there is another way luckily there are cookies left on your mobile device hopefully so that you can get into Facebook without having to be authentic 8 so it's sure make sure you're authenticated to Facebook before you cross the border or and more importantly make sure you don't get called in to secondary screening that I don't see any more questions
okay there is one so some of the discussion makes me think of No Child Left Behind because some people don't really want to use Internet services I mean I'm not snobby but you know when internet banking came on I was right not to but not everybody is like that so you're talking about kind of getting a critical mass and things like that for better practitioners I think client-side certificates been around for forever um but I don't know it maybe it's just a comment like good luck with that because not everybody has planned to use the services that they've been given or need to use right yeah so I do know one person in the world who has no internet services it's
my mother I lied actually she has email now because I set it up for but that's it her iPad has no password she wouldn't know how to log in a website or for life depended on it but other people I'd say on the whole people are slowly getting into it I think it's really important to not forget all the privacy issues as technology goes forward the world goes forward privacy tends to fall by the wayside you want to find solutions that enable privacy I mentioned before I think I touched on it very briefly couples with SSO for instance the identity provider is always tying things back to you I'm guessing that even in a hundred years with technology that none
of us can fathom I'm guessing there's going to be password still to access you know certain types of dark web dish type accounts that you want to have no ability for anyone to tie to anything I don't think passwords are going away I think that they will always have some kind of value both kind of on the privacy enhancing side and on the side of enhancing just the other factors I think that maybe it's one work okay you seem to be a big proponent of the password managers and I you know I I'm not against them I have lots of clients who use them and they're definitely better than nothing personally I'm a bit of a dinosaur so the the whole threat of
it of having a single point of failure has kept me away from them in my own use because over the years I've developed sort of a rolling password algorithm that I found that works really well and I'm happy with it and I just haven't made the jump so the my question is you know can you convince me and someone who sort of knows what's going on you know is a password manager better than whatever system that I've got that you know I can't teach all users to you so you know for those people yeah absolutely use the pasture manager but you know my wife all the people are close to me I've talked to no use decent
algorithms and how to you know keep them non guessable even if somebody gets a decent sample of them is that better or should I still be looking more seriously into a password manager so I want to be clear pasture managers are not the be-all end-all but I think today they're the best we're going to do for the vast majority of cases and users so so that's being the case I I didn't touch on in my presentation something that kind of underlies my thinking and a lot of subjects and it's the word resilience and resilience means that no matter what happens you can kind of come back from it and in the case of case of passwords
password managers you want to keep in mind resilience as well as privacy obviously and security so password managers you want to look for one that zero knowledge and if you don't know is ear o knowledge is pretty interesting concept the idea is that everything is encrypted at your end only time it ever gets to the network is after it's been encrypted and the keys for that encryption don't get to the network either so any good password manager today the big ones they're all zero knowledge very very important if anyone even walks into their data centers takes all the hard drives off and spends a lot of time trying to decrypt them they're not going to get anything and from
Brasilians point of view so that's that's because to protection essentially of your information the risks then are not at the server side they're not the servant side assuming is properly implemented and a lot of those companies do bug bounties and adopt the risks right your device and in fact in security the risks are usually at the end device and from resilience point of view putting stuff in the cloud increases your resilience and that's true with any service really there's obviously issues to be addressed but the cloud gives you resilience and my passwords are synced between all my devices one of my devices doesn't work I go to the other one to help recover that device
while I was preparing this presentation my home computer crapped out totally we're talking it wouldn't respond to control-alt-delete what the hell so I needed my recovery password for BitLocker because what you know what paranoid security guy wouldn't use BitLocker how do they get that recovery password pull up my phone it's it's there through my password manager that gives me resilience gives me the ability to sufferin to come back from you know issues with with computing environments and I can also of course use it offline as well if the cloud goes down my devices keep working with my password manager there's a question here yeah I think one of the important things is that you don't necessarily use the same
set of recovery mechanisms do you treat all of your data in your passwords differently so your bitcoins would be recoverable in a different way than your hugging at work or on a website certain things might be stored in a password manager other things you might store a key that you can use to decrypt decrypt the printed password that you keep around and you keep the second half of that at your mom's house yes DZ that goes to resilience the more knowledgeable you are about IT and security in general I would argue the more forms of backup you have of all things not only your data but your passwords your keys your tokens and indeed you don't want to rely on any one
thing if you have multiple things ways the back things up you're better off of course you now increase the probability of losing it one of those things or using them so infrequently you forget how they work or they stopped working but it's always a trade-off resilience is very important that our I would argue you should always consider that in anything you do including occasion going once going twice sold thank you very much it's really a pleasure [Applause]





