Scan Pwn Next! – exploiting service accounts in Windows

Show original YouTube description
Show transcript [en]
by speaking into the microphone
I one more an author mic
check all right guys can everyone hear me okay working awesome uh before we start I just want to once again say thank you to our uh sponsors they're right there take a look um they've been very helpful in this uh whole thing uh also want to remind everyone to take uh feedback fill the feedback forms out there's uh one on the schedule website and there's also one on your ticket and your email um so please do that that'll help us improve this uh for next year uh so I'd like to introduce Andre and maton to talk about let's see scan pone next thanks hi guys so welcome everybody and good afternoon um we are going to uh as we
said scuss a service accounts in Windows networks so if everybody is here we'll just get [Music] started anybody remember how to defeat an electronic keypad oh don't even joke about that Martin those things are impossible think I'm joking [Music] this might work yeah yeah about yeah right uhhuh uh-huh yeah yeah okay I'll give it a
shot a classic right sneakers everybody here you bid so I guess everybody remembers that one yeah okay for those who haven't seen it you must go with see it now so since the days of sneakers after the days of Mr Robot a lot has changed in the IT industry in in our networks but one of the things that remains for a very long time are services and automated processes both those operating in our environment to access other stuff and those services that we can access in our systems we are going to discuss how those services and the accounts that those services use actually expose our networks to attacks by attackers and what you can do about it in order to
mitigate that attack Vector so who are we my name is Andre dlin and I'm the head of research for cyber labs and I've been doing targeted attacks research for the last bit over 15 years in my spare time I do some Rasberry Pi and Android development so if any of you have some interesting projects that you would like to discuss I'll be happy to hear about them and hi I am Matan Hart I'm a security researcher at the Cyber Labs H formally I was in the if and IDF as a Mal analysist and uh I like to do CrossFit so if anybody want to suffer with me this evening is welcome so care Bros is Network tication
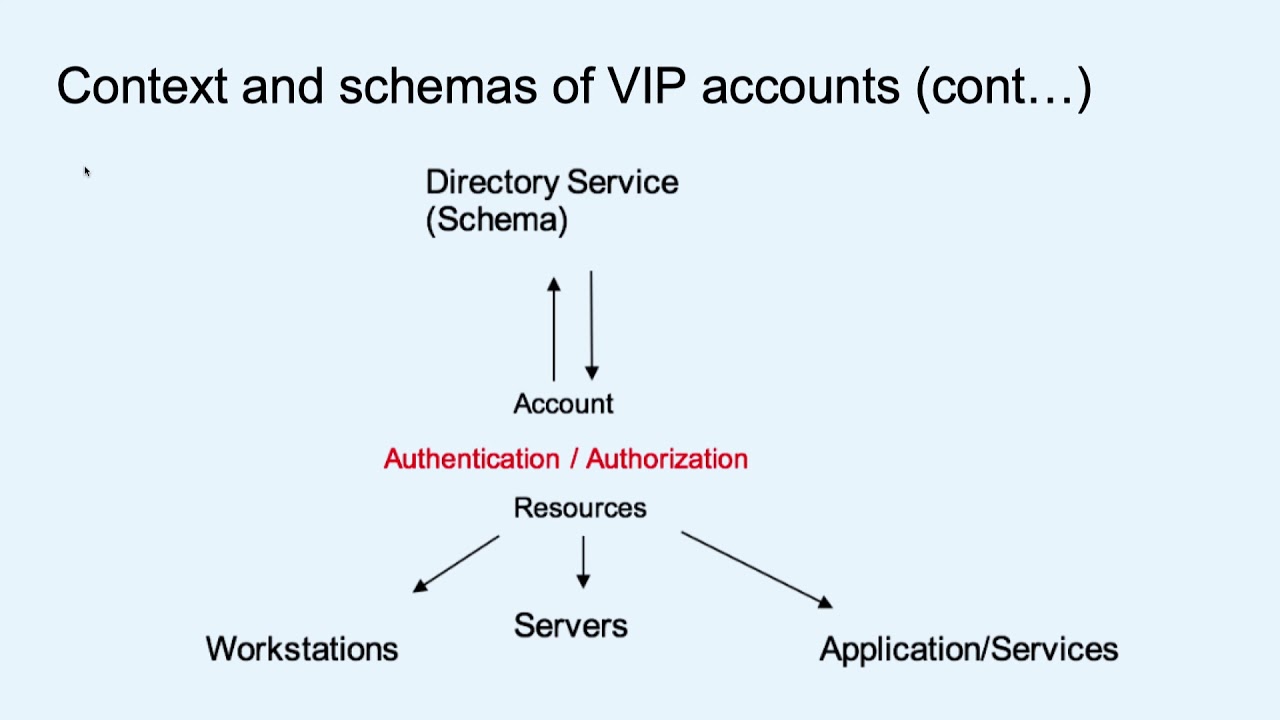
protocol which is based on tickets and secret key cryptography in Windows networks um the domain controller is responsible for the for authentication and it uses kbros as the main as the default Authentication Protocol but however the authorization is performed by each service so how the service know who to authorize so Microsoft extended the care protocol to include additional authorization data also known as pack which include information from the active directory such as group memberships authentication SOS and Logan hours and Etc so the service can decide to authorize based on that information in the ticket service account are principls that are running services and uh are used as the security context uh of the service so uh in Windows networks there are two
main accounts computer accounts and user accounts computer accounts are are making some tasks such as retrieving and er enforcing gpos H and are used by the computer and user accounts are used by human to access resources such as emat because there's no service accounts in the active directory usually the computer account will be used H as the account for the service is running on but sometimes H even standard user accounts which are used by humans will be used as the service as the service account so when we are using a user accounts as service accounts basically we have Services automated processes running user user accounts there are many differences from between those accounts configuration and the accounts
that are used by standard users uh probably the most uh relevant one is the fact that the password policies for those uh accounts will be different so if our standard users are changing their password every 90 days it is very often that for accounts that are used for services there passwords are set to never expire for example and the password complexity can be different it is also often the case that those accounts can be overprivileged I'm sure all of you have visited stock overflow or similar websites where people ask questions on how to configure how in order for some service to work and one of the worse uh recommendations that they usually get is you probably
don't have sufficient permissions or some privileges just raise them and then configure it later to reduce it and that later time never comes right so they are left overprivileged there are issues with the delegation we are not going to go into that uh but uh you usually service accounts have some ways to delegate uh privileges of others and in general those attack those uh service accounts expose larger attack service when we talk about attack surface basically we mean that attackers have more ways to exploore them in standard user account for example we said that this account is running service so perhaps that service has some vulnerabilities an attacker can exploit sorry that an attacker can
exploit and then hijack the credentials we say that the service is potentially running on multiple machines and if an attacker can get to any of them they might be able to hijack the credentials of that service as opposed to human users who are just using one machine right so there are differences here and in general when we discuss Services we discuss two types now the terminology here is our own so um but it makes it easy to distinguish between those services that are you that are using accounts in order to go out into the network in order to access other network resources and we have services that are listening for income informations that we are going to call
them the in Services they will usually have Associated SPN so uh we will start with the out Services basically those services that are going or automated processes that are going out into the network and we will start by looking into an attack bridge that happened about a year ago with a major US retailer where an attacker they were able to hijack the credentials of a single traveling salesperson of that organization um as an anecdote the IT personnel of that organization said that that guy had his password on a sticky note on his laptop so it wasn't such a sophisticated hack ER but the attack also the attacker got was way into the Citrix portal of
that organization now from that Citrix portal the attackers were able to find machines in the network and on those machines the ATT ERS found multiple VB scripts configured to operate inside the network conduct various tasks all of them configured to use a domain admin account okay so people here know that this problematic and what the attackers did with that is they use that those credentials in order to get to the point of sales over 6,000 point of sale devices where they installed the malware and stole lots and lots of credit uh credit card info from so that single account configured in those Vib script was highly lucrative for the attackers good morning Gentlemen please be
seated I see we're still dressing in the dark Eugene once again don't call me Eugene our recent unknown Intruder penetrated using a super user account giving him access to our whole system precisely what you're paid to prevent someone didn't bother reading my carefully prepared memo on commonly used passwords now then as I so meticulously pointed out the four most used passwords are love sex secret and God so would your Holiness care to change her password okay this movie is recognized right aers what year 1995 okay so very close it's a 20-year-old movie discussing the same problem we are dealing with today there are super user accounts in our Network that if hijacked by attackers will enable them to do what
they want in the network and very often those overprivileged accounts are service accounts as they are used by automated processes now uh we conducted a research throughout 2015 Where We examined the dozens of real world Networks we have our tool cyber DNA it's a free tool that uh any of you can run and uh basically what it does it scans the network and it looks for the privileged accounts and it looks not just for the privileged accounts and their configuration but also for where the credentials of those privileged accounts are And We Gather this information from uh over 70 networks uh in order to conduct This research just as an anecdote here are some of the
interesting finds of DNA from U various networks for example in this network we found a server where all the domain users were configured to be power users so basically any domain user is a administrator on that Network on that server we found administrators running jokes over administrative accounts so in this case the account name is Batman it's an administrative account and the account description says who wants to be the bra soul to disable it and then Nick became Brave on September 9th the account is disabl we found the temporary service accounts set up as administrative accounts so again this is one of those St overflow right examples where somebody sets up a temporary account runs it excessive Privileges and it just
gets left behind and we even found uh the ex the is opusc here but basically this is an application account that has been used by Security Control in that Network where somebody has put the password for the account in the account description so as you all know the account description is available to any user in the network so that's nice one of the things that we do uh with DNA is we map H credentials in the network now as you know in Windows uh Network whenever you establish an interactive session to a computer to a machine you actually leave your credentials on that machine right because either the hash or the ticket sometimes the password itself is Left
Behind so what we do is we access every machine and we look for the credentials on that machine and we put an arrow saying on that database server 2 there is some credential that could be used by an attacker to gain administrative privileges to that file server one and on that file server one there is some other credential that could be used to access that it file server one okay we are just mapping those routs that attackers could take inside the network just as an example from a single scan you can see here we naturally anonymized all the accounts but you can see the account name you can see whether it is used by service or automated
process you can see the threat count the threat count is on how many machines out of the thousands that we scanned in this environment there are credentials for that account the victim count is how many machines would be compromised if an attacker hij that account the groups that account belongs to the password age and password whether it never said to never expire and you can see for example this account 18 you can't see because it's red and the Sun is against us but it's a service account that is present on over 300 machines the credentials of it are present on over 300 machines maches they can be used by an attacker to compromise over a thousand machines in the
network the password age against you can see here is over 5,000 days old 5,000 okay and the password naturally set to never expire so this single account present whose credentials are present on over third of the machines can be used to compromise the entire network and what we do is we created this metric and we split all the networks H That We examined into one of three groups the low risk the medium risk and the high risk and this is just the risk according to the service accounts and then again you can see except for the P but over 40% of the account of the network that we scan were of high risk of total
compromise due to service accounts being present on a majority of the machines in them not just service account but the credentials for those accounts for those of you interested we will provide you can see anything here so we'll provide the research in the notes and you are able to go and see some more details on it but the problem of service accounts and of credentials embedded in those services and automated processes is a real one and actually present in a lot of networks an important point to note here is that we said that those uh service accounts accounts are of are used by automated process it is often the case that the same account is used in
parallel by a human user and when it's used by human user it creates dual uh exposure because both the human users and the automated processes leave behind those credentials so we've touched on the we've covered the out service accounts basically all those accounts that are used by automated processes operating in the network now we are going to discuss the in service accounts those that are associated with SPN and are listening for incoming for incoming
con so SPN service principal name is basically basically what we present in services like Andre said and in the domain and so those are used those are contain the service type the host name and sometimes the port the service is listening on so actually when you RDP between two computers you actually request access to the terminal service services on that computer so if you have a shared printer you actually request access to the file and printer service on that um print server so so in other words you basically request access to the SPN which represent that service when you need access to something if you have a SharePoint you actually request access to the web
service and and if this um SharePoint uses a backend database you the the SharePoint actually need to request access to that database also so we have a lot of SPN in the network and all all of all of those SPN are registered in the active directory and they're easily discoverable using built-in Microsoft tools so how should actually how it works the client authenticates to The Domain and request access to a service right so the domain controller will issue a ticket or t or TGs for that uh service which will be signed and encrypted using a secret which is only known by the domain controller and the service so when the user get this ticket it cannot read or temper that ticket and
when it represented to the to the service the service can decrypt it using the secret and authorize the user based on the information on the ticket so that secret I'm talking about is actually the service account password hash so when you join a a computer to The Domain it automatically creates a um an SPN to that machine when you use when you create a new Microsoft SQL instance with the domain admin credentials it will also create automatically an SPN using this domain admin running on this domain admin so basically most of the SPN will be created automat basally so you don't need to bother about this and they are um and even if you delete this SQL instance the SPN will
still be in the active directory so you actually can still request tickets to that service even if it's not available anymore so you we have to manually delete this SPN in order to make it in order to delete it another thing is another another interesting point is is that the same account can be used to with can be used with many um spns they can be with different uh service Types on different
machines so as Matan said most of the SPN will be created automatically and will use the computer accounts and but some of them will be using user accounts and and this is one way to set up a new h a new service just use the set SPN command and we Define here web server listening on a server and we Define the account that it's going to be used right Damian is the account and what's interesting about this is that those service those spns that are configured with user accounts they are exposed to different risks than those configured with computer accounts so what what are those different risks well first of all the accounts themselves they are and
they are creating an issue usually our computer accounts are not overprivileged right because this is just a machine in the network and there are Set Set uh privileges for those computers but the user accounts can be potentially overprivileged for example the example that you saw earlier we used a an administrative accounts in order to configure that web server which is bad H the ticket request by anyone for Z SPN will be legitimate this is the same issue whether it's a computer account or service or a user account any user can request a ticket to any SPN in the network and potentially the same account will be used to run multiple services and multiple machines okay so if one is
compromised it is possible for an attacker now to compromise others as well the password policy we already touched on that that the password policy for those service accounts is different and they usually change from that of a standard user we know that H very often those passwords are set to never expire you saw the example earlier for those automated processes going out it's the same happens for spn's services that are listening for incoming connection and they are usually configured to use ntlm hashes instead of AAS which are the stronger hashes and with ntlm is basically an unsalted rc4 which potentially can be problematic right so in this I don't know you can see there so at least it doesn't use Des
encryption but it also doesn't use a 128 or as 256 by default which means that it is potentially crackable especially the password that is used for that user account that Rec configur NN is is it wi one car withit [Music] Grandpa thank [Music]
you Mark what are you doing disable auto drive enter password Foolish Boy you'll never guess Elon musk's master password musk rules with a z password verified manual control enabled okay so if the password is an easy one we can crack and break it and this is what we are going to demonstrate now and uh for this work we would like to thank uh Tim medine for uh his work on koros for those of you familiar with that we expanded a bit [Music] so basically we have created a script H which will be which is available on GitHub which request a care ticket for a a given SPN then I will show what we can do with
it so let's
start so I request the ticket for the SPN we manually created
earlier I will just hack it now it okay so as you can see I now have a ticket I have a ticket for the web service we just created under the Damian user account and the ticket is encrypted using rc4 and you barely see the encrypted part of the ticket so why does it help me uh basically we said that the H ticket is encrypted using the secret the ticket is encrypted using the service account password hash which means that the pass the password hash of Damian account so when I have the ticket all I need I need to do is know what is the password is to enable to decrypt it so two weeks ago hashcat the famous
password cracker created a new hash mode which is able to offline H crack Kos tickets basically what it does it generates password hashes and try to decrypt the ticket if it succeeds we know what the password is Right Secret so we don't want to waste your time H to see our cracking password here so we take this ticket earlier and Brutus it using hashcat and so is this is the proof and hashcat using a standard graphics card will take about 10 hours to crack seven letters alpha numeric password which is the windows H domain and policy so here we crack the
password so and so um okay so we have a service account password what can we do with it naturally the first thing that we are going to do is to impersonate that service after all if H it's a standard user account in the network then we can log on with it we can access uh network resources and uh use whatever privileges are granted to that service account in order to operate inside the network okay impersonation and we can also go ahead and create silver tickets so silver tickets basically as Matan mentioned earlier uh in care brough uh there is the back component of the ticket where the Privileges of the group membership uh of the of the account are
described above U among other information and so if we have that secret password we can craft our own tickets to that service making it possible for us to gain any sort of privileges to that service and potentially to the whole machine on which that service is running so this is called the silver ticket as opposed to Golden Ticket which I'm sure all of you heard about the Gras operation in the entire network this is De specific to that one service and there are some other stuff that we are still researching so you can follow our work and I hope in the next few months we'll be able to provide some new stuff let's try to see all the ways that
we've discussed up until now for an tle to gain credentials in the network so users when connect to machines in the network and have interactive sessions leave behind credentials that an attacker can steal Services again or automated processes when they connect to machines in the network leave behind credentials that an attacker who compromis that machine can still more we have the services themselves that are using credentials so on the machine from which that automated process connects there are credentials such as those credentials in the US in that in that breach example that I discussed where those credentials were embedded in the Vib scripts and also those 300 machines that we showed earlier which have those
credentials embedded in them and we have services with SPN so an attacker can request tickets to those services and break them in order to retrieve their password and their credentials so it's mainly a question of whether the attacker is able to discover those SPN those services that are configured with user accounts and could potentially be lucrative for exploitation and for that we have another [Music]
script so we have another script which will which is available on GitHub 2 which actually find the riskiest pen in your network so we previously showed how we can crack those tickets but how do how from an attacker perspective I decide which ticket I want to cck offline it takes time to cck right so here's the magic goes yes so basically what the script does it find all the sensitive groups in your network and then find all the user account account associated with SPN then it takes all that spns and find which are the services that are running them and check if they're available in the network and then we have a map we have a table which show all the accounts
and and their properties so here's how it looks yes okay so the script found three user accounts which are um which are using rc4 as the encrytion encryption type for tickets they set to never expire so all of them are member of a sensitive group some kind of a sensitive group and they are having multiple spns like in the third example they are running three instances of um SQL Ser SQL services on different um databases servers so in other world words we have three accounts which potentially have a guessable password they are wickly encrypted and they have high permissions on the network which makes them very H interesting for an attacker to exploit
[Music]
okay so now you can find all those uh SPN in your network that can be abused what can you do about it and about the ve the surface created the attack surface created by those surface accounts well first of all delete all those unused spns and disable all those used accounts it's a very basic technique H that is often overlooked and so just look at them and then make sure that you don't have anything that you don't need in your network you should avoid dual accounts dual accounts are those accounts that are used by both human users and services and there shouldn't be any such accounts you should create dedicated granular accounts for every service that is uh is
running your network and they shouldn't use any actual human user account you should uh change uh the encryption types used by those accounts to as those are much more difficult to break than the ER rc4 unsalted rc4 used U for ntlm hashes and you should employ the least privilege approach in this specific cases usually means switching to computer accounts when possible switching to local accounts many services are running with um access privileges or with the domain accounts when they could run just fine with local accounts and there is also the option to use Virtual accounts virtual accounts are accounts that are local that are used exclusively by Services there are local accounts on those machines and
whenever the service needs to access some Network resource they will use the computer account of the machine that they are running in in order to conduct that Network operation so it's a like a combination of both worlds you should also manage those accounts and enforce strong and complex credentials for them there are great systems that do a password rotation and enforce strong password policy and you should definitely look into them they can manage Service uh accounts as well you can also look into managed accounts manage service accounts this is a special type of a setting for an account that for es ER basically the default is again 30 days same as for a computer account it forces a password
rotation for them as well you should use credentials management to avoid any hardcoded credentials especially in automated processes in almost in every Network that we looked into there are hardcoded credentials is hardcoded in automated processes themselves in scripts in config files next to the service or the process so just replace all of them with a call to a central system that will provide those credentials on demand or with a central system that will manage at least for those Legacy scripts where you can uh remove the hardcode credentials that will at least be able to manage them and you should monitor the use of service accounts as we said many of those service accounts can be
overprivileged and if you deploy some monitor in your network this is is one of the areas to focus on now I'm sure many of you have heard about Behavior analytics user Behavior analytics they are dealing with building profiles and detecting anomalies against those profiles so service accounts is a very interesting thing to look into what our research showed that there are somewhat challenging uh to use analytics on and also they become doubly challenging when you are using dual account so if the same account is used both by a human user and by an automated process the profile becomes very problematic and uh challenging to address so to some the whole thing up which we've discussed up until now
service accounts and the services in general are prevalent in our networks both used to connect to other resources as automated processes and those listening for incoming connections their accounts are often H overlooked and you need to know where they are and what their parameters are you can use our tools you can use our tool or you can use or our to either our tools or our tools whatever you want to use but you can look for the credentials that they leave behind or you can use the the script that Matan showed earlier it's available on GitHub in order to look for the risky SPN in your environment and you should manage them this is the most important part if you
don't manage them if you are not aware they are an attack surface in your network so with that we will just give our thanks to Tim medine and his work on care buroughs that is inspired and some of our scripts H to Hash cat for uh John reer for adding the careb breaking functionality to our customers who shared with us data on their networks and to our colleagues Beck at Cyber Arch who supported and participated in this research um all the scripts will be available as said earlier the research is available as well and uh we we'll be happy to hear any questions any questions thank you thank you
questions there so sorry excellent okay so if you can send me an email I'll will'll add it to to GitHub as well pointer any other
suggestion your own and modify the I you can use that to escalate priv by put yourself you're not actually exactly yes this is the T the silver ticket Vector that we describe basically you H heighten the Privileges against that specific service which potentially can gain you excessive privileges on the whole machine and and it can lead you to do interesting stuff through it other questions great thank you very much thank you all right thanks for everybody for hanging out um on behalf of Fitbit and from bsides SF we have gifts for you both and uh let's have another round of applause thank [Applause] you it's really awesome I know you guys got little for whye
s
where are you
should work yes I do it okay [Music]
sorry yeah I just say it's amazing what you're doing I love this
let
okay [Music]
than
but it's not really there [Music]
[Music]
is that coming through yep
next