Fantastic signals and where to find them

Show transcript [en]
thank you hello good morning everyone [Music] we are I'm Sabrina most people know me as a douche if you want to follow me on Twitter there's the nickname yeah the mouse and the dog and we there's my Twitter we like to - we like signals and we like ones and zeros in cybersecurity and everything we're doing the day we do that usually what they let us do on s 21 SEC and yeah we do those those security things that I think everyone here likes that so first of all we love signals and and the show of hands please if anyone here has ever heard of software-defined radio as they it nice okay so you're on
the right room I think what about this ham anyone here own a software-defined radio receiver and transmitter and a carafe or or blade RF nice that's okay lots of people as well great so you guys ever used new radio before okay less hands but we will try it we I don't know maybe six months ago both of us we we haven't used that very much very much and we're starting to so this this talk the idea of this talk is to first of all say to you that we are not experts on this subject we started we are basically information security guys we started working on radio very recently we're also not lawyers but we have consulted
land for some things we are going to show you and the things we've done we try to keep on the right side of the law so and not and basically there's a racing and the radio software-defined radio is to be a good neighbor don't you know don't do unlawful interception don't do jamming those kinds of things we try to not to do that so yeah basically the main objectives here is not to show you any groundbreaking stuff but basically try to give information security people the the enthusiasm for this this field and to show you that is a very interesting field right now and you should be doing that if you're doing information security you should be
looking into that because there are very interesting things here and there are very interesting vulnerabilities that have been solved outside of the radio field but they're still abundant in the ended in this spectrum and yeah that's it and we did some we did some fails and we did some we had some issues that we're still having but anyway we want to show them to you so you can learn from them and maybe help us for the next steps is there someone here that has some knowledge on ESP digital sign o processing or any radio on the low level not much people okay so yeah basically we are why are we doing this first of all and why should you yeah
first of all there are signals everywhere we find signals everywhere your mobile phones have lots of signals you probably know that there are a lot of transceivers on your radio transceivers on your phones we're going to talk about some of them but not just on phones right so on cars you know basically yeah the most common that you must know that's the femm radio that's the name write it so it's pretty obvious but there are some other components on the car that are using radio and sometimes we don't even know or imagine that what's happening that is the wireless key fobs work with also radio that is maybe you have an atoll system like via vir or
some other kind that's also working with the radio maybe you have blue - for your speakers that's also radio maybe you can use GPS we have the type pressure that's a sensor that measures the tire pressure and send it to the dashboard and is you these are the most the obvious ones in the non abuse ones you probably heard about almost all of them we and we are going to talk a lot about behavior today with Cori since TPMS is a protocol is a standard protocol to send to the to the head unit into the car the current high pressure because you know car cars have wheels and wheels are spinning very quickly so you can't fit a wire of the
the pressure sensor to the inside of the car you have to do this wirelessly so these are the obvious and the non-obvious receivers that cars have as well and of course you know an airplane is like 31 radio transmitters and receivers for radar for secondary radar for anti-collision for in-flight Wi-Fi some some some airplanes at that as well and we for instance ats-v is something that you can very easily receive with a very cheap radio a very cheap dongle we are going to talk about this well and actually I don't know if we're going to talk about this in more detail later I don't think so but for instance a DSP is not encrypted or authenticated and it's
basically a secondary radar in which the aircraft say to the rest of the aircraft and then the ground stations where I am and where I'm going and now to to them so far and there have been some attacks and some research on spoofing and and sending the wrong location data and basically saying that there's an aircraft where there is one yeah what's happening that's so easy to receive but it it's also easy to to tourist meet so it's like you get the new and the bed you can receive it but maybe you can do something wrong with transmitting it and yeah there's a lot of signals on your house as well you'll probably know that you know there are
there are wireless doorbells and bluetooth speakers and alarms and you're probably you have your computer at home with wireless as well Wi-Fi satellite TV is also a wireless NIC signal that can be decoded there's your dog chip if you have a dog I have a dog actually and I have two dogs at home and I think the most dangerous here is the baby monitors because people buy this to monitor their babies but they don't have notion that it's a unencrypted transmitting and every neighbor that it's near your house can receive it and it's like a huge bug inside your house because anyone in the neighborhood can listen what you are you talking about near the military or Bible
and some of them also have videos of your baby on a video streaming yeah and of course there are a lot of other signals from satellite signals to number stations we're back we're going to talk about some of these signals in the next in the next present next slides so yeah in each Ethan basically your your computer and any electronic equipment usually does also transmit radio because it operates at there are I frequency devices and they operated at certain frequencies and they basically emanate radio radio emissions that can be received by someone else there that's not you this can be a security problem there has been work regarding that as well so basically what this all means is that as
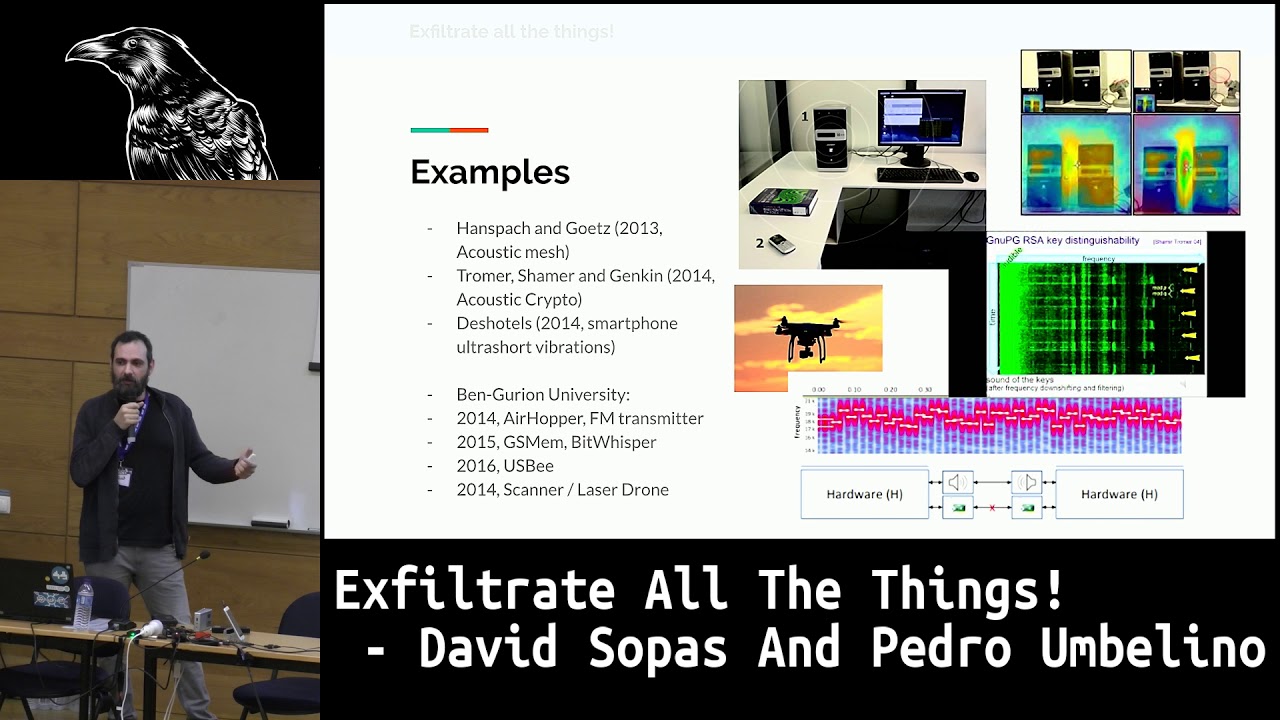
a information security and as we information security XK specialists that we like to think we are we see a lot of attack surface and this in this area attack surface that it's it's not being very explored right now by by by most researchers that don't have access to software-defined radio in the these are some examples here these are actually they are it's interesting to note a pattern here most attacks using wireless and the wireless medium are being more and more frequent probably because of the cheaper devices right now that can be used to exploit this and people are getting into this so basically this year we had the blue barn which was a remote code
execution on blue on certain devices with Bluetooth enabled we had crack which is a low-level attack on WPA we had mouse check last year which was basically sending keystrokes through the radio of an RF dongle such as this one that I'm using and basically yeah there's there have been a lot of attacks recently some of them can only be exploited using specific equipment some of them require you to work at the RF level but in a way that you can use maybe your your own dongle you have your own booth booth dongle or wireless card but but some of them for instance based some certain baseband exploits that have been that have been very recent just
last week actually I wanted to show you this of course there are these attacks as well some of them more recent than others to steal cars you can basically there have been news of attacks on restaurants where the waiter comes at your table activates your your key fob your your car key and has a receiver that is sent the signal essentially to an accomplice which is near the car that unlocks the car and he steals the inside of the car and maybe you can actually turn it on in a leaf there have been reports of drones military drones being hijacked using GPS spoofing which is also something that you can do with the nasty SDR of course not at this scale
but it can be done this was just last week or this week maybe certain reports of GPS jamming in Norway by Russians I don't know if it's true or not you can read the paper it's it's there have been some reports about that as well and also this is something that will I think we can talk about it right here you've probably heard of something called an MC catcher which is basically a device that can be used to locate you and then understand Europe your your identify yourself own identifier sometimes it can be used and some devices can actually intercept calls and it is actually variants easily to intercept the GSM call using an SDR
device the problem is with LTE LTE or 4G networks authenticate or or they the mobile device requests an authentication of the network is a micro connecting to the right network and so you cannot easily spoof an outtie and lt from an operator and lt up network carmen operator and this was just last year this is research by a Chinese researcher from here basically she found the vulnerability and the LTE protocol before authentication that she could basically downgrade the the mobile device certain mobile devices could be a directed attack and she could downgrade it to gsm network she says you're not welcome here to the Saltine network please connect to this G and GSM network instead and that GSM network was a rogue
network that could be used to intercept course so this is another slide trying to give you the message of we are of the the attack surface theories and the easily the easy basically the the ease of attacks that can be performed using using the RF and using wireless signals basically I put we put a huawei there why reform because it was used it was attacked just last week on mobile control which is a competition trying to to gain access to gain remote access to devices and basically the the guys that that won this challenge they used a stack-based buffer overflow on the baseband processor okay so basically they used what what is essentially a 90s
style attack to gain remote code execution to the processor that processes the incoming LTE signals okay so we don't have any of the more modern exploit mitigations that exists on the iOS side which is automated or automatic segment layout randomization memory randomization mitigations per process permissions you don't have any of that on the baseband side on these simple stacks simple software stack that processes the wireless signals so it's much easier to execute an attack if you have access to the RF medium and you can perform the attack using LTE low-level packets so basically tools what can what do you use and we have some here start to so if you want to start on this field
you must have something to capture the the signals there is a lot of tools that you you can have someone cheaper someone a more expensive but there is a lot of tools and there is a lot of to new tools coming everyday because start to be mass production and it's coming cheaper so it's a new field to start with so for starting you have the realtek as they are dongle it's a generic RTL dongle with the realtek tuner it's it cheap is like $20 it's not much so it's not like nice like a big device but can have like two mega samples per second that's in for the most of the protocols that there are and the problem is its receive only
so you can receive signals and not transmit anything you can just receive with this one in the spectrum that it gets its little slow you can get from the 30 megahertz to 1g going 27 points yeah Tina for some fun yeah next you can have the a car f1 it's a most expensive device like $300 that one this one is capable of receiving and transmitting but not the both at the same time it's just off duplex your or you receive are you transmit when one each you can have a wider spectrum you can go from almost one Maggert non-official to seven and something bigger so that's a lot of spectrum and you can have 20 mega samples per second
that's a lot of sample right so it's a nice device to start with you have double I dare EF it's a more expensive device this one you can put an expansion board for a amplifier I take this one and I got walkie talkie like three kilometers away from my house so it's nice the spectrum is not so so wide as the Akari f1 so it goes from 300 megahertz to 3 gigahertz but the sample right that can go it's a lot higher 40 yeah it's since it's USB 3 you can obtain much more information per second on your computer then with a knocker hacker F which is just USB 2 so it has a limited sample range something right
also the blade area affair is a FPGA inside so you can program it and optimize your applications can goes more faster than the next you have the YMS they are meaning it's a startup project it's like a gathering of the iqari F and the blade area the positive points it can cause a lot higher sample right and it has almost the same sample right at the same spectrum that the Akari F and the price hits we have the okay it goes on the next and I will show you the difference the the last quantity that is it's from A to Z research research team it's a more professional board and a lot more expensive it it's like it goes so in
compassion you can go to real tech dangled it's 20 euros you get a Curie F more expensive double either you have more expensive and goes you can check the difference the RTL goes on the 2.4 mega samples that carry I've got 220 it's more than enough for the most protocols that you want to work with but if you want to have a wider spectrum to analyze at the same time and do other projects you have other boards with higher sample rate and depending on what you want to research maybe want to go to higher frequencies like the V aware that we were working on we had applied areas but it can not go to the 5.5 gigahertz
that's the dead frequency that the behavior is using so we had to use Akari F so you have to do a tap the the part that you want to the research that you want to do just basically even the most expensive radio is still cheaper than either pro license so if you like trying to do cutting-edge security research you probably should should look at this as well also even if you buy a real tech don't go cheap one you can buy another board converted on converter that converts the higher or the lower frequencies to a frequency that the real talk can receive there are also other tools yeah we have we I think we have
nuber tooth one here which is basically a specific device for Bluetooth sniffing and there's actually there's something some people think that bluetooth is very hard to sniff it's true but Bluetooth Low Energy which is another protocol that only has like the same frequency range than Bluetooth and it's complete almost completely different protocol it's very easy to stay free using this device and it's a protocol used for a lot of low energy things like smart watches and stuff like that and there are a lot of other specific tools that that we can use to do radio here what we want to give you this the main point of this talk apart from other things that you might learn is that this is a really
interesting field and there are two things that are being aligned here which is affordable relatively affordable tools and a really like green field of attack surface that's not being very researched at so this is like the Golden Age of RF hacking and software-defined radio right hacking and this is a really good time for people start to start to work look at this existing things so yeah there's a theory we don't know anything about math and this is the great thing about software-defined radio is that we can we can experiment a lot and we can see the results immediately other than like having like complex equations and stuff like that yes so the the meaning of this presentation not to
give you the insights of red in the physic way and the low-level but now you can start with just a little few knowledge and like your real tech tangle or whatever you you buy and start to talk around so the the basics of the radio that's you have a carrier wave issue usually it's a sinusoidal and you have the information and you want to mix that and make the mood light of wife that you're going to transmit so most of you have already have seen this on the top that's the sign that you want to twinkle like ones in and zeros and then actually so if you want to model a tit in a.m. that's
simply to the modulation you can check that the amplitude up and down is changing so it's a amplitude modulation and the period of the the waves are the same so it's just amplitude modulation on the bottom you have the frequency modulation where you can see the the amplitude is the same and the period the frequency of the the wife is changing so you have the frequency modulation it's the the two most known modulations the take the exists but most of the time you don't want to see that on that level that low level most of the time you use a in spectrum that's a software that use for analyzing the cenotes and if you look on
the the first one so we have the frequency on the y-axis and the time on the X and you notice on the the first image that the frequency is the same but you notice the color is changing when you have the green line green line and it goes to yellow and right so it's the strength of the the signal and it's related to to the amplitude so you can see that the amplitude is changing and the frequency remains the the same and if you looked at you notice that there are some gaps near the the more color colored lines and it's Arnoff king it's amplitude shift keying and you we are mood lighting one and zeros and this is
the morse code is just ones and zeros he and you you send it send that signal on the bottom image you you get a frequency modulation modulated signal and you can see the frequency is going up and down but the color of the line is still the same so it has the frequency modulated but the amplitude is the same there are other model Eisen it's the face mutilation because the the radio sino is a 3d since I know it's a complex number so it has the real part and the imaginary part and yeah you can see the picture it's an Alex and the face is the clockwise that it's turning and sometimes it goes on the the other
way and you have a face ship basically what sorry basically what I've learned and we don't want to learn anything the mathematics of this we can learn it later but basically from the radio front end when you capture the signals we capture two components because the signal is a 3d component so and you have to have like two components to be able to compose a 3d wife okay so other motivations are just mixing of the three main model license so that's the this is the basic of the variety since you want to capture the signal that our analog on the the hair you have to convert it to to digital so you can receive it on your
computer and the same if you want to send you have to to get the digital final that is on your computer and compared it to analog and send it to to the antenna just to reinforce the idea that we're sending basically samples which is I tend identity of the of the the wave at a certain point and then the RF component we are basically modulating the signal in software that's the thing that's the thing about software radio is that we're going to do everything here instead of sending it to the radio on the radio does it so we do everything the modulation in software using samples that we sent or that we read from the
radio content so yeah should know it's higher frequencies ever lower distance that most of the low frequencies is from both to communicate like longer distance and the the protocol that they use have in mind the frequency also use these are the things that we learn experimentally at least I did it's basically the the stronger or the higher frequency the less transmit you have the transmit distance for the same power so and the thing is that we are doing this and if we like me I don't know I did it I did know very little about radio and we learn this experimentally I think one of the things that we would like to see is that every University has like a
software-defined really for experimenting for the students to experiment which is much easier to learn than using math okay so yeah we have to hurry you know so there are antennas and we have we're going to show you this yeah this is like the Wireshark of the networks but 4sy knows this the software that you use for watching the what's happening on the spectrum and okay and test the the modulation that you can it's just a small software that stuff first to use software on the as the SDR work yeah and there's which is a little bit scary at first that's the second software that you want you since first you you see the sign of aden DKR sheesh
X and then you want to start to work around with the designers and unglue ready you can make your own flow graph and the mood light and work so I know this is the engine of this is in Python so you can basically you do this like coding in graphical way there's the the source signal on the leftmost side and then you can like do an FM receiver this is this is basically an FM receiver that sends the output to this sound card so you can listen to radio so yeah this is the FFT is their presentation of the wife since you we were capturing a lot of spectrum we had to chip the station
that you we want to hear and then filter the auto other sinus that we didn't want to do here and then the modulated it in frequency and put that on the the sync house this is transmitter that does the opposite so you can have your own FM radio station which is nice it works although we can't use it because we can't emit ahem so basically we are going to show you some of the practical cases some of the things that we did they are still very limited but yeah we did some progress and we are understanding that this is a very interesting field so if you're doing something like this be aware of what you're doing there is an account it
regulates our spectrum so be careful and let's start with this so restaurant pagers everybody went to restaurant where they give you that pager that beeps or gives flashlights when the food is ready to you pick it up so I went to a restaurant there was this with a system auntie Rob that sensitive active GPS or whatever if you trusted come on but we look on the the liable and you noticed the FCC I did that's American it's almost like the enter combat for America and it has the ID that some details about that product so we started to do some open source intelligence we went to the FF FCC ID website and we search for that serial number and it
gave us some information like the the frequency that is working on and some pictures of the insides and outside so this is the pager on the front and since we are we already at the the frequency I tuned my geeky are see he adds to a near frequency to watch the spectrum at send Utley after since a few time I start to see a wave coming out so we had our frequency that the pagers were working on so we already know the frequency let's start to decode it so I start my new radio I put a source that's the the Akari F and I save it to a file sync for a further and now
and I did also give ec to watch the the say no where it's happening appearing and so on so this point I was exploiting the the restaurant because since we have to go to pick the the the pager we all will be two times the first one to you to pick the the chips and the second the second one to pick the sandwich so you know if you capture the first one on on the go to when you want to pick the chips you can save that signal and replay it later before someone going to pick the the sandwich so University I did a new radio flow graph to just pick the design of that I add on the file source and send
it to the deck area on the sink to transmit it and suddenly someone was to pick the sandwich that was not done yet that happen start to blink and someone went to pick it up so yeah I have then I picked that so you know and I went to to analyze and you can see that's a frequency modulated see know where the frequency is changing but the color of the the line it's still the same you can start here and decode the signal get the one and zeros and try to to get some knowledge of that signal so what I wanted to do next that's getting some more samples to compare all the samples and know where's the preamble what's the
ID on that signal encoded and on the lighter progress do a brute force and goes on the all possible numbers and flash all the the restaurant and like big party with flashing lights so other things that you can start to do it that's a garage start that's a really easy see know that you can decode we just need to to capture a signal most of them work on for 30 T megahertz
this is a record of TRX receiving a radio key fob signal you can see it so you already know the frequency let's start to to save the the signal to further decode the DK are a new radio flow graph to receive the signal and save it you can see the C no beard there so we already know that we have captured the SC no let's start to decode it so we fired up in spectrum and why's that we watch the the signal we knew that it was amplitude we went to amplitude the plot we slider that with the threshold we got the one and zeros and then we extracted the one and zeros to STD out
the beauty of in spectrum is that you can save the entire signal to a file and then analyze it later in the demodulated offline without so that's your garage key it's really easy next you just want to you just need to to do a flow graph on radio to to receive all the one n zeros in a vector and transmit it to your dongle and your garage door will open really easy yeah yeah another thing we did was to take a look at CF which is a Portuguese system of emergency that uses a known protocol called tetra which is used all over Europe and I think part of the states as well it's loosely very
loosely based on GSM but but uses much lower frequencies to allow for longer range it's in Portugal it uses around 93-95 and this is documented in an accountant documentation and basically we took a look we didn't transmit anything but we took a look at the Atlas signals and they are there in fact CHP is working in Portugal apparently encryption is optional in this protocol but it's work it's it's enabled here in Portugal so everything is encrypted so security yeah it works the thing is that it's really not very known algorithm it's it's kept a secret so there's a standard but it's not available so you don't we don't have access to it but the meatman
metadata is not encrypted so we can actually see the communications as they occur we can see the transmissions and numbers of because there are each terminal has a specific identifier and we can see them exchanging voice messages and exchanging text messages which are encrypted as well and we have we have used basically a tool that is already available on on on the internet for free from a Polish guy and we have like a video of the thing working yeah it doesn't show anything and much but it shows the correct demodulation on the on the left and this is the software that's used to tune in to the specific channels and to see communications happening on each channel
it tries to demodulate the voice communications but it can't because it uses encryption if you pause the video you can see that it's it's correctly identifying encryption on the on the voice Channel so it can't be it can't be read so yeah this is the another thing that we did and for future work I I'm going to publish a docker file to make it easy to install this software on your new Linux because it's very it's relatively complicated has a lots of modules one thing that we would like to do of course with permission but we'd like to look at the encryption algorithm used by this and it probably it probably can be reversing by obtaining a terminal with encryption
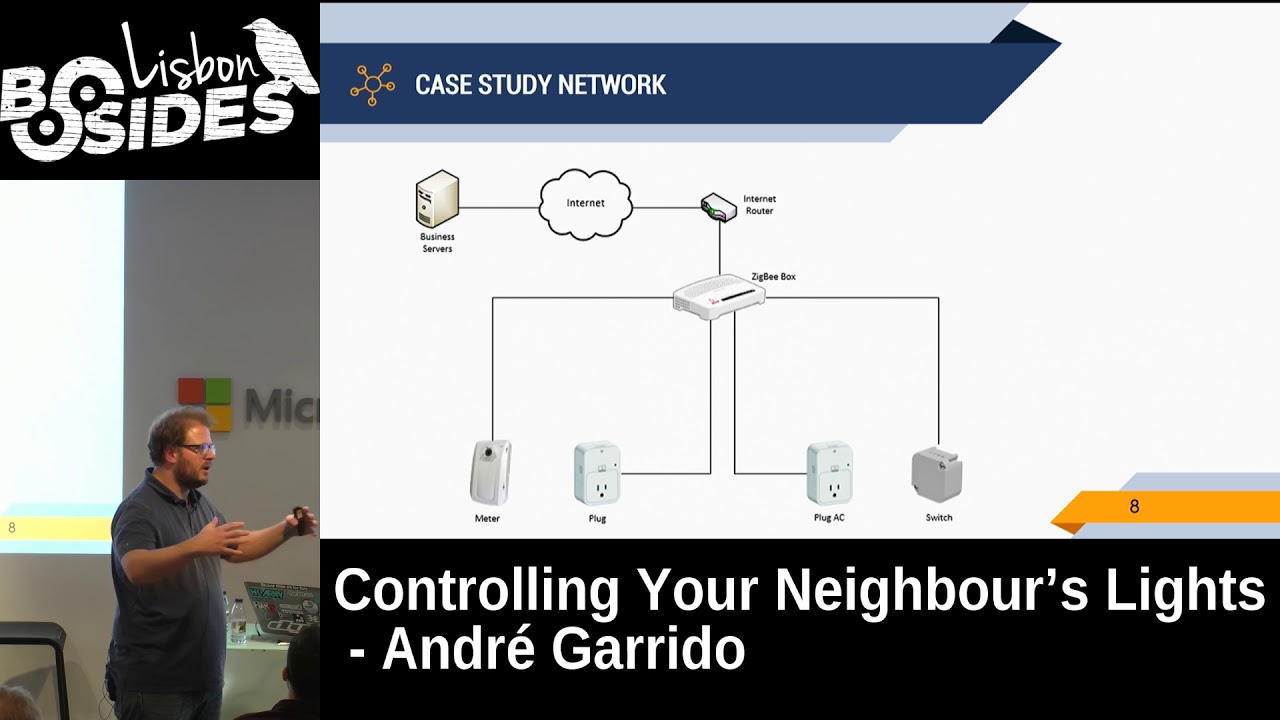
and decoding the firmware and reversing gem where and basically see if it's possible to obtain encryption keys in and so forth and we would like to know how the terminals are authenticated or if they are authenticated and how does the encryption key rotates if it rotates in Portugal so basically we would like to look at the security of CNET man but we have to ask permission for that the the thing that we took us a lot of our time as well was looking at behavior we've heard these basically a Portuguese Wireless tolling system then it's used for us to go through the freeways and and pay for for the freeway use but we can also use it for for paying paying
gas paying paying at the McDonald's actually they have vehicle readers for us to pay it's a it's an unpublished protocol although we found the frequency because it's listed on the enecon website as well and it's out of reach of most relatively cheap especially ours like yak RF but now actually the aircraft is can it can can reach that need the blade RF cannot so we had to we had to basically do some some some capturing we went out to the street oh this is the this is the reader if you don't know it the reader and the gates the gates are the ones that that have the antenna that captured the reader signal and they actually do something
else they actually send it send the signal send the signal to the reader and then wait for a response from from it we actually have a guy in the room that helped us with with the with a will an open via valve reader so we can look at the chips we haven't had time to look at the exact chips used so one of the things that could be done as well is to read the firmware of these chips and see what what they do okay so this is were driving into 2017 we don't use the world skaars anymore that's that's old-school we basically used Anna koreff to go to gates and read the gate signals and
reader signals and in getting getting captures on disk so we can now analyze them later okay actually as a side note these are really big files so you have to turn on the capturing mode just as you are going to pass through the gate because they take a lot take up a lot of space on the disk so we did we get we got the signals from this is basically the the frequency the operating frequency of the of the VFL protocol it's very very fast it happens very quickly it's logic because you're going to throw a relatively high speed through the gate and you have to negotiate a protocol very quickly and yeah but this
is the the first signal is the signal from the from the reader actually this is this is a carrier wave that's being constantly emitted by the by the the gate but it periodically sends a request as you pass pass through the gate okay and the reader reply the reply is very quick as well it's just four hundred microseconds for a reply to go back to the to the gate okay your process takes very little time sometimes they repeat themselves to make sure that they have the correct reading so what what can we learn from the signal okay first the gate signal it's basically looking at this we can see its amplitude modulated okay there's a carrier wave and then the
intensity goes up and down to modulate ones and zeros so we did we could very easily be modulate the signal using in spectrum this is by the way that shows a already already gave we basically it's the period of the symbol is 16 micro seconds and we can easily extract ones in zeros from there we understood that basically they have like a preamble the sync has a preamble that can vary according to the gate some gates specifically gates that are used when the car is stopped like on the gas station and on McDowell's have a longer preamble because they can they can be longer signals because the car is not moving it's so it's easier to to to send and
there's time to send it and some gates vary the identifiers okay we saw two gates different gates on different spots sending out the exact same identifier so it's static but some gates very have like a sequential number if you're going through the freeway you get through gate a and you get the signal a and then you get the signal be a sequential number on on the next on the next game okay the the reader reply is not that's easy to demodulate okay this is a very we call this space invader or yeah it's the space it looks like a space invader from the game and it's what we can understand from this it's not amplitude modulated
it's a much weaker signal but it's there's these are other signals that are being repeated by the winner but by looking at this we think that this is freaky frequency modulated using a OFDM which is actually something that's very used on actually why it's a part of a big parts of Wi-Fi and stuff like that but we didn't have and we don't have a knowledge yet to demodulate the signal easily what we look by looking at the appearance of the seal it is that it seems to be constant by the reader the reader always sends out the same signal that that's what it appears to us okay okay so the next step and we wanted to
you know stop going around in cars into McDonald's we don't I don't like McDonald's at that much so we want to be able to reproduce this old process inside the lab okay so we set up a lab a lab environment okay this is us trying to set up the web environments is they actually the the the the we used a very expensive device all the Faraday cage it looks like a microwave it's not it's very expensive in Faraday cage to prevent signals from coming in or out okay and we used to occur fs1 for transmitting one for receiving the response okay the reader it start with the the reader is there okay unfortunately we try a lot and okay we
did we since we did demodulate the signal we could actually reproduce the signal just as well just looks that it looked like just just like the the original gate the the difference here and duration is basically we're using a different signal than the captured one with the longer preamble to make sure that the reader reads it but yeah this is the this is our generated signal using radio and this is the the capture an actual capture file that we did from from passing through through a gate unfortunately we were not able to get a response from the reader we try the what and basically what what we think is happening is that these are very small
devices with a very low transmit power in the battery and because they have a very limited battery they probably have a very high squelch which means they only respond to very strong signals and the gates send out a really strong signal compared to our hack RF which sends out such a small signal that if you like you separate the reader from the receiver or for like 50 seconds you can't get any signal so we would need to be able to send out a much stronger signal to be able to to extract the the response from from the reader okay we also used some you can see here actually there here these are circular polarized antennas which are good because they
send out in all directions but they probably concentrate very few power and very little power and in this purse a lot of power so maybe if we used a different polarization and we would probably get with back from the reader but we're going to keep trying so we hope to give you guys some news and published amps and some of our research soon so yeah the thing we would like to work of course with with permission because some things can be done without permission but we would like to demodulate the the the signal from the the marker the reader may bleed without without demodulating replicating it back to the gate because the probably the gate has a
lot more sensitivity and can be back reader signal and see if we can emulate a reader passing through the gate we would like to up to obtain try to obtain the framer of the readers if it's available and if it's on the chips and maybe somehow boost the signal to be able to get a response back from the reader and yeah we have this is the the main things that we've done we have a lot of other protocols and in fact that fantastic thing singles to show you one is the number station okay let me try to most of the signals that we are showing here or they are really easy to decode or there is already a software to to
decode it this is a number station if it was used by secret agents to deploy them or sending secret messages and the basically numbers yeah it had like a the poacher song and then there was a lady saying some random numbers that in the end Iggy had some meaning yeah this is SS TV so it's used by space stations to stream video to earth these are the things of the these are like attacked the data a data system for into interchanging messages between airplanes on airports and in you buy you know for checklist reporting and stuff like that NFC which is used by a lot of cards card readers there's the garage door I hope that's not a code
that from that we use let's Amanda go ahead yeah you can do the weather stations you can get image like these ones from the station these are beamed down from weather satellites all the time you just have to have an antenna pick it up and you modulate the signal and get the real-time view of the weather stations of course radio walkie talkies baby monitors this is the signals from tire pressure monitoring systems that have been decoded we would like I would like to see how this can be used to attack cars maybe you know maybe cars have a hard time decoding these signals and maybe they can be the the head unit of the cars of the electronics
of the car can be manipulated it's just an another attack surface of cars and you you should be aware of that and it's also interesting for having like a way to to identify people that pass really a street because these send out a specific identifier GSM of course you can consider the packets on Wireshark it's really easy yeah and you can actually have your own roll your own pirates pirates GSM network if you want using ETA to BTS which is the software country I think we have a slide for that as well a DSP that's the springing meaning of the planes where they stream they position their speed and a lot of details and you can map all the the
planes that are near you in the Google Maps and really find it what the planes going know about it uses this data from that is to map all the airplanes in the time the LTE you can actually do some some there's also some software for out LTE but it's not very well developed or some of it it's proprietary so you can't use it yet but you can use parts of the there's a software called open LTE which you you can have you can you can use as well GPS is actually not encrypted the civilian part is not encrypted so it can be spoofed and it has been spoof the military part is apparently yeah okay
GPS the RF dongles proprietary rectangles also used and there's a thing called mass check you heard about the attack it's it's also being used is using injection of these signals of course there's goober tooth Bluetooth Low Energy which is very as very little security and you don't you don't actually need specific hardware to do this attacks these attacks Wi-Fi iridium which is a satellite phone system but basically we just teach how to steal a car here so it's not that important now it's just basically using jamming to obtain a signal and then repeat it back to the car since most of the old cars didn't to disable the the old signals that weren't received you can jam a sino
and then filter the this you know that was coming from the key fob and reuse it because it was not invalidated yet and also you can of course you can make your own GSM network I published the image on my github with easy to install v8 VTS please do so in a place where you know you don't you have to be a good neighbor and you have to have license to transmit of course and yeah the idea here is this this is a really good time for you to be looking into us SDR because it's the hardware is cheap it's getting cheaper we can we can learn a lot without the math I remember in college trying to understand
signals and I really couldn't understand anything but experimentally is much easier the transceivers the the the devices that decode all these all these signals have really really bad vulnerabilities that modern operating systems don't have so if you take a page out from you know a frack article from the 90s how to buffer overflow you can follow we do that on the code that's running these these receivers in these transceivers so yeah there are a lot of zero days waiting to be found just last week there's there was one on one way devices and yeah of course you have to respect the laws vocal walls in vehicle divert and I don't know if you want to any anything else so yeah
basically it's the Golden Age of software-defined radio hacking and we hope to have given you interesting an interest in start exploring this this this fuel thank you very much any questions yet we have time for Q&A or this anyone so have you looked into biomedical devices I think that's that to be an interesting thing yeah of course you probably know about Barnaby Jack the-the-the did very good work on that we don't want to kill anyone so we have to have like devices to test on and we don't have them so yeah but this that's another area that's very interesting thank you you