Scam Message Service: SMS Traffic Pumping and Fraud at Scale
Show transcript [en]
[Applause] wow I'm shocked it's the first time I'm at an event that actually in the time frame I have to do something about kidding I know I know there's a ah that what always happens you say we don't okay so they're really not going to stop right so ladies and gentlemen we have one more presentation left before the Jeopardy game of course but since uh it seems to be a thing that the first and the third part of our meeting has to end with a double action so this time again we can welcome two presenters and they're going to tell us about why not to trust SMS again damn it how am I going to communicate with my mom now
that's that's a bit disappointing but we're going to hear all about security problems of text messaging from toring and silver [Applause]
sucks so hello can you hear us yep hello from us so uh I guess we have to introduce us a bit so we are seops Engineers from a small financial company called wise well not so small anymore um raise hands who know what why does or Y is yeah okay so so most mostly mostly Financial transfers I think we have something like 6 million customers now I think it was like 7,000 people on slack so we've grown quite Big and of course all sorts of hackers really really like places with with lots of money so we have some problems and we are here to tell you about one of these problems today so this whole idea of coming here
to present this started with the uh tweet by the world's most famous [ __ ] poster Elon Musk uh so they he posted that hey Twitter is getting scammed by phone companies for 60 million a year with fake 2fa SMS messages and this got some news coverage um and everyone was like okay so Elon has gone crazy he's saying crazy Elon things again you know uh but me and Tommy we like looked at each other and thought about it bit yep did some calculations yeah this seems about right like we're seeing the same thing this seems like a very reasonable number so let's talk about how this happen I I will this overy so I'm going to firstly introduce
you to a little story our experiences what we have seen then then we'll go into how this thing actually works and then perhaps Solutions or things you can do to avoid damage as much as possible so let's start our story with the little fintech uh playing Vamo with bad guys uh it's very cold February 2019 and our apis are getting hot like really hot so what's up there okay we start look looking into it and it looks like we have like some weird accounts popping up uh using L ipsum disposable email domains and what's the most weird thing there's swapping phone numbers they have like over 900 phone numbers within like 20 days that's super weird like why would
someone do that let's look into it so we understand it's BT accounts okay and they're using voice calls and little bit SMS but they're using voice calls which is like backup of SMS that's definitely something is super weird so this is our very first case we noticed this pumping happening and uh they're using mostly Telecom Jersey airel uh which is uh small island between UK and France where there isn't a lot of people and they're using uh for example vpns like IP vanish then we get to July 2019 and the big wave washes over us we get 25,000 users that are exactly the the same bot accounts uh they're using same M Mo uh and this time more Telos are involved
different Telos uh all always kind of small ones not big ones and and uh all sorts of proxy networks vpns so we got hit hard we thought we need to do something about it uh so easy let's add IP based rate limits and capture and that will solve everything I'm sure we all thought that so a bit time goes on and now we notice they're not creating accounts there's doing logins so they're like doing accounts and then just pumping logins on them with voice methods so but we just added protections like what gives okay so cture was clearly not the problem at all IP based rate limits not the problem at all 2020 March the same guys are back
hello uh this time they created again tens of thousands of users same M Mo all over the place okay okay we started thinking hard uh we have enough duct tape to solve this problem most likely so let's add more rate limits let's start Gathering actually like number data and start doing number based blocks not only IP based blocks uh let's block voice to countries we don't serve like no need to serve voice calls to small Caribbean island uh and let's build out metrics to actually like start to understand what's happening and that should solve our problems and of course block the Disposable domain email domains easy what can happen then stuff happens here attempts here and there and
we get to year 2021 now we get to fake registrations they're not doing accounts anymore they're attempting to create accounts but they fail in the last step uh why this is happening is because in 20 21 our API changed and we forced SMS in our registration flow so they don't need to finish accounts anymore to use SMS they can just do it right away April 2021 hello boys you're back uh now they're pumping very different countries all over the place Central Asia Africa South America everything uh they're using more vpns they're like Distributing their traffic way more they're trying to use because we added phone number rate limits they're staying exactly under the rate limits and adding
more numbers to their number pool uh okay uh weird uh let's tighty up a bit uh maybe this thing will go over July something changed they're not using voice calls anymore they're using purely SMS now uh again thousands of users created and the registrations done everything like all the previous things they done have done they're still doing they're just adding layers on top of it uh this time we were introduced to a group that operates in Vietnam uh they actually use their OTP codes so for example when they do registration they use the SMS code you sent them uh then it kind of got piu we thought they went away uh so we started looking more into
metrics uh so let's look a bit different metrics on different device types so this is like Android metrics and we can see some interesting stuff Happening Here uh firstly the very low line is essentially uh blocks that are happen happening uh so we blocking numbers or uh like our provider blocking numbers something like that uh central line is unused OTP codes so code was left hanging and never used and above line is uh used top codes clearly we can see something weird is happening here which correlates to a lot of blocks happening uh a lot of blocks happening here but not much unused OTP codes happening here hm weird uh let's look into I traffic we
have some weird stuff Happening Here uh mostly in here but in general not much weird stuff when we get to web traffic it's all over the place so we have a lot of unused a codes we have very spiky traffic uh and of course our blocks are all over the place and we had some very big wave here apparently so let's look some examples 2022 uh again thousand a bit over thousand users it's again the Vietnam group uh seems to be more or less the same guys we are pretty sure of it uh we thought easy fix let's just block all the ranges and we're done June they're back with 177,000 users okay clearly what we did is not
effective let's TIY more things up uh let me just show you some style example of how they try to bypass W rules uh so they use like Firefox versions from the future uh so clearly things are getting hard so we thought a bit added more metadata to our logs uh added more different rate limits to different time periods so let's not look only like 5 minute periods let's look 30 minute 1 hour 24 Hour 3 month 6 month period of these numbers reappearing uh and start like actually hunting stuff and doing exponential rate limits surely that will solve all our problems July 2022 hello Android boys so we are introduced to a new group attacking us this time all of our
previous problems are represented essentially in here our new problems started in here uh style example these guys really like to use Android phones and they really like for some reason Central Asian numbers so here we have a graph of used OTP codes in usbekistan and unused OTP codes in usbekistan okay we have a lot of pots so these guys tend to use our wise app and like Nokia phones and OnePlus phones and Motorola phones and as far as we can see uh on our intelligence uh CU we use like a thing called Google attestation uh which Google also uses to like recognize is it actual device or not uh we can see it's it looks like
they're not emulators they're actual devices so these attackers are using some kind of rig like this okay [ __ ] is getting very hard now and we're kind of getting out of ideas uh so we're adding now device based rate limits cuz we can can have we added device concept so we can see same device using like a lot of different numbers and creating trying to create a lot of different accounts so it's very sus adding more metad database rate limits so for example we can rate limit like only headless chromes or whatever stuff like that uh dedicate significant amount of time to thread hunting and like General look for stuff we can do this we can survive this
they will give up we're sure of it 2023 so this is our previous problems this is our new problems they pumped their traffic up over like 10 or 15 fold okay so what's up here it's getting really extremely hard to stop these guys um essentially we're now down to like can we drop SMS like this like it's unusable in that sense the bigger you get the more bumping you get so we we at this point of time roughly around this point of time Elon tweeted and we were with silver like we feel you like really we feel you so in 2023 our SMS costs got higher than our infra costs which is stupid so we did we started doing a lot
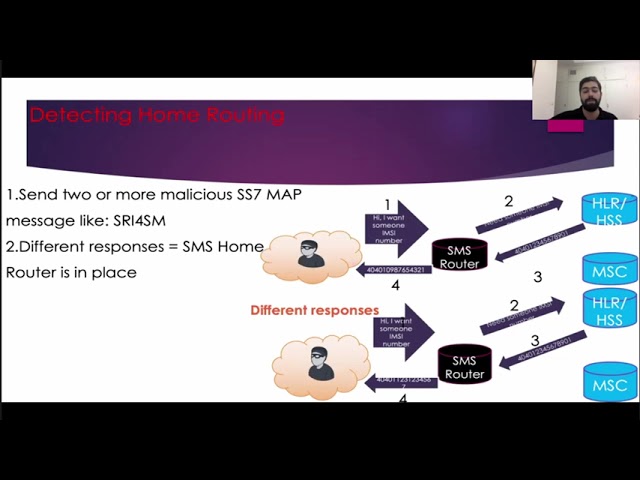
of digging with silver and we found these guys have been around since the beginning of time they're very well funded or since May they have used at least 650,000 numbers against us uh and they're probably targeting you too so silver please explain how it works yeah so of course we see we see all these messages coming to like all these messages getting sent out by us and we're like trying to figure out okay well why are they doing this like how does this actually work how are they getting money out of this like why are they sending sms to like these particular numbers in uh and so on um so of course like why is this a
publicly traded company it's possible that someone is just messing with us to make our share price drop and you know make money out of that somehow but uh kind of seems very unlikely right uh so there must be some other way they're getting paid out of this so we started looking around and we basically discover the world we were basically unaware of and unless you're working at a Telco you are probably also unaware of this world so it's the world of International Revenue sharing fraud um to give you a some sense of scale how how big of a problem this is uh I found some numbers for 2022 about various uh you know types of scams and
attacks so you have like a bit like half a billion that's get that gets paid in ransomware payments um you know data breaches somewhere around the same I had the sources for them they seemed reliable so you know numbers uh gdpr fines are about the billion then you get the the big scams and frauds like business email compromis investment scams which were like 2.5 billion and then you get to the International Revenue sharing fraud which is 7 billion so this is a massive problem for everyone in comparison here's the not pay attack which essentially took down several large companies across the world and has some this far been the most destructive attack and this was estimated around 10
billion but these guys are doing the same every year so how does does this work first thing they need premium rate numbers uh so it used to be that well this also works with leg regular premium rate numbers like the 900 numbers in Estonia and I think 979 was the international prefix for premium rate numbers but uh but no in this case they're not using standard premium rate numbers because of course you know the prefixes for them they're easy to block right they're using what are called International premium rate numbers so this is basically just a regular phone number it gets assigned to a user and every time someone calls or sends a message to this phone number they get
paid for it um and they're not actually premium so us as wise we're still playing paying you know the list price to our SMS operator for sending out an SMS we are not paying any more than we would otherwise sending sms to that country so how much does sending sms cost anyway like how are they making so much money out of this Well turns out like sending sms to like within a country is obviously very cheap uh sending sms internationally can get very expensive but it depends on a country like for example United States Canada I believe also India they're also they're all very cheap uh but some countries are up to 71 cents for each me message so
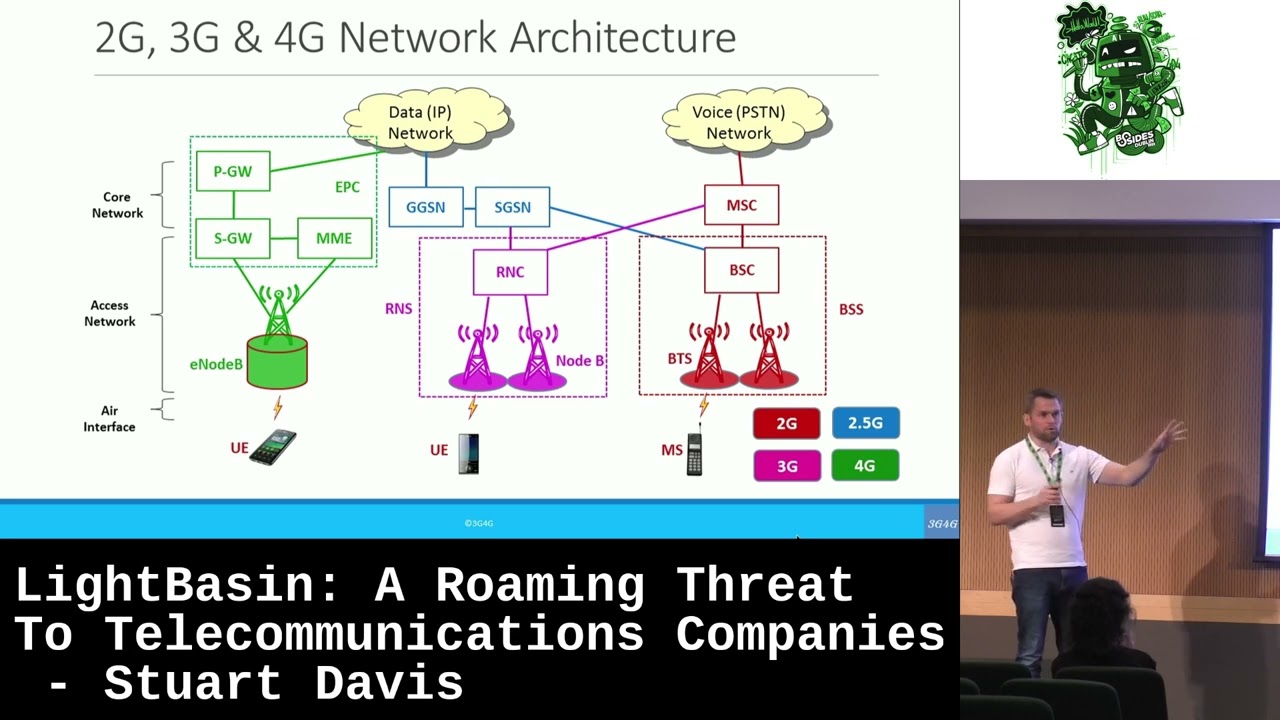
this is the highest from twio price list right now in this case well this is a bit special circumstances because this is Russia uh but uh still you have a lot of countries that hover around 20 to 30 cents per message which is uh quite a lot of money especially if you can well SMS has the nice feature compared to voice calls that you don't need to like keep the Line open you don't need to keep a call running you can just send SMS SMS SMS as fast as uh the API allows you to so why are the why is it so expensive uh we get to a thing in TCO they call termination rates so this is
basically the amount of money a mobile network operator can ask for receiving a call or a message it's usually around the same for all operators in one country because well obviously if one operator is much cheaper than the others then everyone would just send all of their traffic there but within a country they can basically set it to whatever there's uh there's some regulation for example in European Union it's regulated what the maximum termination rate can be some other count have their own regulation but you know small Caribbean islands ain't nobody going to regulate those and it's a very significant source of operator Revenue especially nowadays where like SMS 2fa traffic is something like 80% of all SMS traffic uh so SMS
traffic has probably gone up a lot in recent years um so yeah highrisk countries basically have high termination rates that's the correlation we found most of the SMS is getting sent to some countries with very high um termination rates and well this is not since I was actually talking to some Telco guys backstage this is not entirely correct because as I found out like maintaining SMS infrastructure right now is a whole separate infrastructure to the rest of your Telco infrastructure so this might not be completely correct but still they're charging way more than actually receiving an SMS would cost for them and this also means that this is sort of a soft cap on premium number
payouts because um like this is the maximum frauds that could possibly get paid from a premium number they usually don't get all of that they get something like 60 to 80% so how do you get those premium numbers like where do they come from this is a screenshot from a Facebook group uh lots of like various I don't know how legitimate more operators they are but lot lots of them offering these numbers and as far as we can tell from our research this is completely legal so there is nothing illegal going on here uh like the official use case is that you can use these International premium rate numbers for micro payments for services like
let's say you're in some less developed country your users don't have a way to do like card payments or Bank transfers or so on they can just use their phone call this number and you get paid for it um so yeah not all of the premium rate number provides there are frosters but it's probably a similar percentage as the cryptocurrency world um so how does it work so here's an example what a happy happy SMS would look like so this is how legitimately stuffs would work so we send out well we tell our SMS API operator that hey we want to send out an SMS uh they will basically check the giant list on their
side which is their price list okay this SMS must go to this country here uh let's check from the price list which is the cheapest like Transit operator we can send this to um and basically once they send it off to this Transit operator they have no idea what path the SMS will take afterwards it probably goes through several other operators uh they all take some cut uh the money you pay your operator and finally the like final operator then gets the termination fee and your SMS gets to your happy customer how the premium rate numbers work is that essentially there is some operator somewhere in the path that is hijacking certain number ranges so for example I found some
um so basically this number ages can be hijacked from absolutely anywhere and this is because this whole routing thing here has essentially no security like you can tell that yep I have these phone numbers just you know send stuff to me I'll I'll make sure it gets to the right destination no problem so with the premium rate numbers they generally don't uh try to hijack ranges which are actually in use they only hijack ranges which are like not in use invalid numbers stuff like that so you have you have 170 countries in the world and they all have their own rules on phone number allocation uh so there's a whole bunch of unused numbers there but they
generally want to have numbers that are assigned to some uh some actual zelco operator um so but yeah there's I think for our operator there is basically no way to check if this is a invalid number when they're trying to send it out they just check the number prefix okay this must go to discount country let's send it off to some Transit operator and yeah how you can tell that this kind of hijacking is happening so here yeah the froster is getting like a quite a significant chunk of the money you're paying your operator uh the transit operator of course takes a cut as well then the ipn operator takes a cut and then the
froster gets some money um so how you can tell this sort of hijack is happening let's say you're looking at iprn number offerings on Google and you notice that they offer test ranges so what is what is the test range for uh essentially the test range is for like you have some way of sending sms or voice calls you need to find out if your particular path will hit the hijacking operator so the test number is there so you can test that the hijack is working and you get paid um usually in this case the numers is a lot also very close to each other um so they hijack like a larger prefix and then use the numbers from
that and if you look at the advertisements in the ads of uh here uh you can see like access from UK USA Saudi Arabia Nigeria Philippines so on so this basically means that these are the routes they have tested where they know their hijack is working not even in Estonia we not undouched yeah exactly so actually when this was still mostly a Telco problem and mostly a voice problem uh 10 or so years ago lva was one of the like most uh used countries for these sort of numbers so not that far from us and another way uh this same thing can happen is if the terminating operator themselves are bad um so any operator in the world
basically wants to receive as many messages as possible because it's obviously ly money for them U like they get all determination free and and it like the marginal cost of receiving a message isn't really anything it doesn't matter how many messages you're getting unless it's you know overwhelming your systems but I'm not sure how possible it is with SMS um but yeah in this case you will see something you will basically see abnormal traffic but it's all going to the same uh mobile network operator uh in some country and all Alo what we have noticed is that uh they are using numbers that are very close uh to legitimately used numbers like on one number these our customer and one number
off from that is already the premium rate number example of these guys are the very first guys we saw yeah Jersey air tail guys uh as far as we can see it's all fraud and in this case um if you're looking at the premium rate number provider online they advertise Global access so this basically means that we have control of the terminating M so we can offer access from everywhere because basically stuff needs to get there so to put it all together here's a diagram flowchart whatever you want to call it what do the frauders need to successfully do this fraud well they need a method to call or send messages so we've been talking about why isn't
how they're are using a registration flow to send MSS Ms but it's not only these sort of things that they're abusing so it used to be like hacked pbxs uh you hack a PBX you start making calls you get paid um in our in our case it's the API of use but it can also be stolen or clone SIM cards it can be stolen phones uh it can be malware on your Android phones that making that's making these calls uh then you have the free SMS sites where basically like you know you want to create an anous account you have okay receive SMS for free here you go there uh you get the SMS but
these guys well they they get paid for it um and there's also a thing called callback fraud which is basically when they're just calling random numbers leaving like unanswered calls and hoping uh they get called back and they also need either premium rate numbers so the international premium rate numbers or they need uh some kind of collusion with the mobile network operators or uh or Transit operators um so yeah numbers you get either from The Operators or by hij checking and the highjacking is enabled by the insecure routing protocols that are used in the Telco world and another thing critical thing you need for this is you need the SMS to cost relatively um well you need the cost of
the SMS to be relatively High because like if they're doing this for 1 cent per SMS like maybe it's not that profitable yeah so in conclusion anyone can be a victim of this fraud so it's not just wise it's not just Twitter it's not other multi-billion dollar companies that are fraud victim of this anyone can be your phone gets stolen uh they start making calls you go you get a phone bill if you're lucky your phone company will cover some of it and then the phone company is getting frauded uh but yeah the frauds are also Almost Never caught so we tried looking into it can we find like any case where these guys have gone to jail and we
found one case where they got three months probation and a fine I think um so yeah international call and SMS routing is opaque and insecure there's no there's like as someone trying to send a message somewhere there's no way to make sure it actually makes it to the correct destination there's no way to verify what path it took there is also in the case of SMS I think it's also plain text all the way probably um SMS is 160 characters like can you imagine sending 160 characters over TCP somewhere and getting charged for it it makes no sense right so what can you do um avoid sms-based multiactor authentication um if you can it's not
possible in all cases because phones are things everyone has it's by far the easiest way to do it but well if you add this to add this to your product you're opening yourself up to this kind of frauds unless you're very very good at preventing it and well those guys are pretty good as we have shown um also like all the high checking business there that's probably also not the great thing you want out of your authentication solution um you can try to block fraudulent operators and number ranges but for this you know it's actual work there are of course companies offering services that hey we have number intelligence we will block them for you and as far as we can
tell they work but they're also quite expensive there always a question of how much they catch yeah because we see these guys are very fell funded and they are always finding ways around yeah um AI can work uh so a lot of the research we found for this was actually from a CCC presentation a few years ago uh where the paper they were presenting was about using machine learning to detect this type of fraud uh and I think they got pretty good results something like over 90% uh true positive rate so could good work um rate limit your messages if you are sending out SMS from your product money for anomalies in your teleph traffic monitor the iprn test number
ranges because if you see a test number there's probably a number close by uh that you will be soon uh getting pumped on and we have seen this being a good indicator of incoming wave so if you see a test number popping up in your services you are most likely tested to be targeted but there's no like open source intelligence list for these numbers which I feel they absolutely should be it shouldn't be that hard to set up some web scrapers and just collect it from all the different sites and yeah basically demand better from your phone operators that's it from us thank [Applause] [Music]
you well and then they say that old school doesn't work apparently it does so so questions somebody wants to confess something no yes please there's a question over there lady in a pink shirt I believe ah okay thank you hello I'm from Elisa um here we go talk about confessions we were waiting for you um I don't know where to start but um in some ways I didn't understand this uh uh topic and um I understand yeah this is like uh the amount of SMS you're sending that this is like that the companies should um monitor uh how many smss they send not to get the big bill from the operator but um and those um irsf and there are a
lot of different kind of Delco frauds that can be done in the world and uh I see when I hear your present presentation that actually your uh website is used for fraud and what kind of activities have you done from your side yeah from the SEC Ops I understand what you done but uh what are you done from the website or the I don't know why those accounts were created or what was the bigger purpose because this method that you uh showed that how Telos uh exchange money between themselves that how this uh actually gets to the fraud fraudsters and um why is irsf numbers allowed in your uh website or the portal you are
using because there is no way to tell these numbers apart from actual legitimate phone numbers so that is the main problem uh with these type of numbers yeah if it's a hijacked range we have no way of telling if it's hijacked yeah in in the worst case it can actually be using the same number range that our customers are using which means that we also have an unhappy Customer because they are not receiving their messages uh so what we like what we have done I think we mostly showed on the slides uh we have also done like trials with various companies that promise to prevent this type of fraud but still we see that they are not that effective um
and and the other message to everybody is your in your product design think about this fraud add as many layers to make it uncomfortable for them yes we can discuss later as well okay but it's interesting I would like to see more know more about this kind of uh thing how it works like more technical way because one thing to notice that we are not CCO guys like we don't have the technical details how this works so this is most of the stuff how this works which just literally from a few papers that we found online where researchers have researched this topic yes I we can discuss discuss it later but uh to clarify one um fact that you
told that those fraud St never get caught uh this is not true they actually get caught but it's yeah not publicly uh maybe discussed that's good to know yep that's good to know indeed that's all from my side hello she didn't go said they go to jail um we just happened to discuss this here um first of all thank you uh I had a very similar thing happen with one of my customers and we couldnot figure out why someone would spam their uh SMS API to get more text messages so this was very insightful uh in this case it was uh as easy as just blocking all other countries because they don't really need to send SMS anywhere aside from well
Finland is in this case but we were thinking um wouldn't it be possible to just change the like uh flow of how you sign up for an account such that you don't get a text message until you've gotten like your like human verification done or would that be a problem in some other I can take this so we have seen and tried a lot of things and we can see even if you had a human layer there at certain scale it's not feasible if you're servicing millions of customers like if you get daily tens of thousands of customers you can't human it so uh and they're using all sorts of methods you can have even in your backup
method of backup method they will find it so and to add to this um so the guys that are doing this they are very resourceful if we do add the human verification step before that I have absolutely no doubt they will find some way to bypass that as well because our verification initially at least is also automatic or well almost automatic um so yeah thank you um hello um thank you for the talk car here uh one comment and one question uh the comment is that one extra mitigation that you can have is limit the money that you can pay for the messaging service provider uh we got hit by a attack like this in one company
where I worked and we were saved by the fact that the credit card that was tied to our uhia account had relatively low limit it was drained but then the attack was stopped because no more messages from the company of course it stopped the service as well but at least financially it is a working mitigation but uh but a question that I would like to ask and not only from you but for everybody in the audience this is a very clear cyber fraud attack with very clear Financial impact to the company can this be insured because cyber Insurance exists several companies here are definitely insured on the cyber crime as well can you cover this simply by
Insurance the cost of FR yes um so actually we we just had a call with one of the companies who promises to prevent this type of fraud uh two days ago and they are actually offering 1 million insurance that if their systems do not prevent this they will pay us 1 million up to 1 million uh back in what we spend so yes you can get insurance for this did the mitigations highly depend on your service so we are financial institution we have requirements we need to serve our customers so for us adding cap to credit card is not going to work yeah and and also you can set like a cap on how much an SMS can cost but
since these are not they are not special rate sms's they are regular International smss this means you will be cutting off countries above the threshold from your service completely which well it works if you're an Estonian company you only need to send Ms to Estonia or like you just need to send to us but if you need to serve everyone glob you can't really just do that uh how do you teleport the test messages before we said we can't tell them apart uh but still you're mentioning their test num so are you getting them after the factor somehow the test numbers are published on the websites yeah they are so nice that they give you
like three samples uh and if you look around in those provider websites a bit they have some vulnerabilities and uh you can get actually all of their ranges but of course we would never abuse the vulnerabilties we never abuse them yes they if you look you can see
them hi um if I understood correctly like the whole issue arises from International routing so and as you mentioned sending an SMS over TCP and Char charging for it is kind of you know mental uh so why not try to make it sort of like local traffic so instead of international routing you directly send SMS over TCP to local Telos and maybe that solves the case again I don't fully follow with the techic details that is a very good question and we have absolutely no idea why this is not
done so there's another possibility to add to this so question do you see that is also part of the SC uh cannot answer you because reasons as far as we can see no so as far as we can see no big operator is knowingly participating in it uh they are being abused like the victims are being abused it's to well they earn from it so they get their termination fee and that's what they care about exactly unless uh yeah okay thank you very interesting uh kind of representing police small parts ofia byebye uh I was just trying to say that U this is a problem for us too to investigate and um please raise your hand who has a
4G or 5G internet router uh how many of you uh know if uh there is only data allowed not smses the card the SIM card inside the router are you sure okay and other ones you don't know uh house uh security the router yeah we've had cases where the routers have been hacked and uh approximately €2,000 loss because the uh routers uh were able to send sms's exactly as they said uh numbers just in row ending 1 2 3 4 5 and uh even even though there was a limit for the card maybe TCO can say when does the limit apply if you send them sms's in a very short time can it be applied
[Laughter] it's yeah and come again yeah okay well so we have seen please check the security and uh We've also had cases where uh cars from U uh South come and they have a a a big boxes where they can add like 50 or 100 SM SIM cards and they just start to send uh sms's from Estonian operators and we've also had a a case not very uh quite quite reent a recent case where an ipx ipx server was also hacked so yeah Sim boxing is a thing uh and we have seen uh regular people fall a victim of U like their phone getting stolen and them getting like 700 EUR bills yeah so it's uh it's here
also so please don't stay away from because I said I'm from police so thank you it looks like I have to come back next year with like a Delco FR talk because this is only the tip of the iceberg to be honest um we see it everywhere so every place in Telco world as well if you can send an SMS if you can create a call this will get attacked our own IMS our own web services everything are hammered exactly the same way so this is happening the router example you made exactly the same way most of the data packages we are selling these have voice and these have SMS yes this has been an issue in Estonia other
places as well so and it comes back to the same thing the Terminator gets the money that's the whole business model so if you can send an SMS or if you can get a call you will get these Fosters at some point can be your security camera it can be your security camera it can be your car whatever I mean everything works uh there's a question in front just as it this story time just short short comment on starting from the Jersey we happen to be sailing past the Jersey this summer and uh our Wii router made a bill of €2,000 and it did have limit of 800 EUR so there was a question how long Fast it
uh kind of like catches uh way not fast for a sailboat at least so thanks it's nice to see it's getting a bus our old P whole presentation point was to see has the community seen this uh let's talk more about it and maybe do some action all together like share [Laughter] Intel thank [Applause]
you seems to me that in humala we are about to fil film the second part of the Spy Thriller o t or something I don't know we can come up with a title later on which then again just since everybody are telling a story as somebody with a law background it's interesting to see that shockingly old school can still take over digital if digital forgets that old school tries but then again driving Sim boxes to Estonia now that's a hobby but why not you know I mean I feel for the police it's like another one coming should we stop it it it might be not what we think so before we get to jeopardizing ourselves
with questions uh I was asked to once again Ask back lovely organizers uh from the morning and uh tell you thank you for coming so