Using policy delay to gain RCE and to execute Ransomware
Show transcript [en]
i okay now i can okay so uh thank you again for having me here so let's talk about the using policy delay to gain the remote code execution and to execute the ransomware to in fact effect to infection with my machine so this is my contact on twitter right so at flip piers and um here my contact on social medias and i have here my webpage if you like to see some informations about me and some talks that i've been participating in uh some articles that have been published there in my twitter and my github by the way and this talk is based on some articles not i'm not only articles but i i perform some tests and i of course i
wrote some articles and i publish it and all those informations are inside of my youtube club here and my linkedin if you'd like to you know send me a message if you have some questions so please you can send me during the conversation now or after this presentation okay so just uh some information about me let me introduce myself so i'm a priest prosecutor engineer at talktest it's a company from portugal responsible to sell in a product from contact center as a service and a security research at singa segura it's a global company from japan it's a privilege access management solutions in my fault there is to to make a research actually not only exactly in this way with this product
specifically but to perform some uh researches in different uh topics related to cyber security i'm advocate of the hackiness dollar crime it's an awesome project by the way that we our idea is projected to spread the message about the hacking uh because hacking is uh how you can see that the software's and how you can use in your creative mind when you need to perform something related to a technology and by the way i will explain about this uh technique that i'm using this this task is and how you can use in your hacking mindset okay and i'm a part of the coordinate team of this the defcon groups here in sao paulo and by the way
i'm talking from brazil now in this moment and i'm instructor of the hacker security or hacker sec it's a brazilian company and i have a course of the moral analysis in portuguese language and i'm a structure of this uh fantastic magazine i have a course of more analysis and more hunting actually and i'm a writer and viewer in these three magazines okay so just information about me and before to talk about exactly the test i would like just to putting all those people in the same page so i would like to talk more about the what is exactly uh thread right so just a simple definition it's not not my definition it's according this is just to explain more
what is exactly right so it's a potential cause for an incident may cause arms to the systems and organizations okay i mean it's related sometimes it's a software attack or a theft of intellectual property or maybe identity death or sabotage or extortional information all those things is related to a threat so why need to understand about the threat fleet because it's very important you understand about the no threats and unknown threats but you need to understand about the how the non-threads works because when you need to perform some investigations about that or when you need to uh perform some passes in your environment you need to understand the behavior about the threats right because you don't know if it's malicious
or not if you have some sample for example or some artifacts you need to investigate more deeply you need to execute some steps and after that you can understand if he's malicious or not okay so this is the first step when you need to perform something that when we talk about the malware hunting or malware analysis for example the identification step is very important you need to define it if is malicious or not or malware malicious software or malware malicious document and after that you can define what the best methodology that you can apply inside that right so you define you you can using the statistic analysis or the name cannons right you have a different approaches
here maybe you are asking what is the best way you can use both of them it depends of course what the result you need to have in after this this analysis okay and my recommendations to you is always when you have this when you need to perform some tasks in this way you need to prepare a report you need to you know register that because you need when you register that you can understand about all those steps that you perform in these tests and you have the you know evidence of your analysis and why you can do when you have this kind of information you can improve your defense's mechanism right and by the way
these tasks that i performed and i represent you now during this conversation i perform it in my environment enough and after that i can improve my defenses mechanism in that time when i perform at these tests okay and of course you can improve your cyber threat intelligence environment when you have if you don't have you can create something you can build it right in your environment because the threats are changing all the time so you need to restrain it in the sub resilience because again when you are talking now during these presentations or this during this conversation probably someone are creating some new attacks or even uh not only new attack but creating a new uh variant of this
the same or the known attacks okay so let me invite you to think on a different way so because of this i i i call change your mind um you probably you know what is exactly cyber athletic hunting right so but my idea is to explain more about this uh different thoughts because when you talk about the cyber the sub the threading hunter specifically we are talking about how you can see the logs in some tools for example or if you have a soar right or if you have a cm or if you have some so if you're working in a secured operation center uh you've seen many logs and and of course it's pretty
important understand the logs and to see the evidence but how the attacker thinks that's my idea here because of this i i call change your mind because when you talk about the hunting you see about the cyber defenses with the offensive mind so how you can see the process proactively interactively searching through the network to detect and isolate advanced uh threats remember about that threat so how you can using your uh offensive mind to work with a defensive perspective this is my idea here so what is exactly hunter the people that worked with hunter if you see in my social media for example i like to use a lot more currency it's not a normal it's not common this
word is in them when you talk about the cyber security but how you can using the hunting to uh you know to searching something related to a cyber you know cyber criminals or cyber attacks or something like that and because of this i i i would like to invite you to think in a different way right so the trading hunter is a qualified security professional to recognize so here here's a good point to recognize something the this professional needs to understand about the known threads works so how exactly is the behavior of the specifically binary that you are analyzing right and what kind of dll this binary have not only have but what kind of function this
dll is imported by this or this function is imported by this dll so how this works in environment for example if you find some function called slip inside of this binary so probably this functions is important uh from the same dll inside of this this binary and probably this function is responsible to using or to executing some techniques inside of the environment that this mower is executed this technical this sleepy technique is more when the mower uh are being executed in some ascend box it's another concept that you can using to analyze the behavior of the moderating controller environment right so how you can recognize that so because of this is important you understand the behavior in
a practical way okay the second characteristic is it's it's about isolate so how you can isolate this thread to investigate and to see more deeply and of course the main topic is disable the potentials apt it's economy of the advanced persistent threat because it's more advanced and of course it have many others different techniques and characteristics of these apts the groups involved and this kind of attack okay so how we can use in the manual or artificial intelligence techniques to to disable not only disabled but isolate or recognize this kind of techniques okay and this professional is responsible to search some evidence in a possible internal and external intruder so here we have in another interesting
point internal it means probably if you have some issues suffering some attack they have this kind of uh a pocket maybe can be uh stay inside of the organization inside the network okay so it's important to understand the behavior and to see what exactly is the place this attack are happening okay in around your network right so let's talk about this some techniques in using a threading hand it's very famous about the iocs and bit of compromise probably you know about that so here's some characteristics or indicators like a suspicious and no hostile domain or ip such pictures no hostile fire cryptography but usually when we talk about iocs is only related to and attacking already happened so it's a
cause infections right and you can find for by signatures that actually suspect to suspect um infections or no hostile data such as antivirals or ideas signatures you can see more information about the some datas or potential data related some exploitations or some cve ideas related to some exploiting using to explore some vulnerabilities and you can see more deeply and you can investigate some indicators about the ttps the famous statistics and techniques and procedures associated with some suspected and suspected or unknown hostile events or maybe some behavior different like for example an authorized instance with a meaning or for example if you don't have any uh um offensive team in your environment executing seven is scanning in your
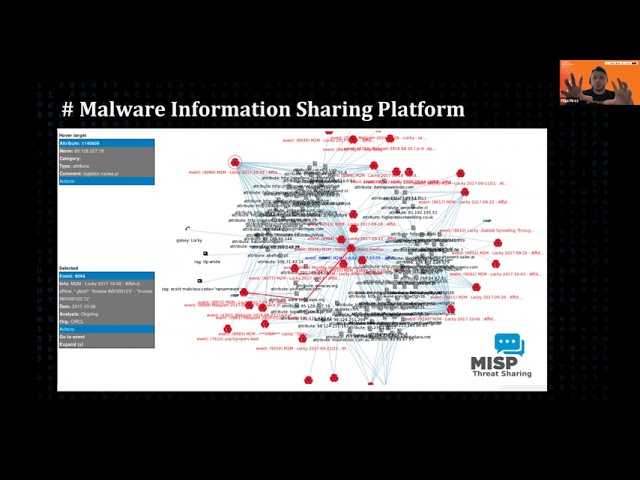
environment so it's probably totally suspicious right but it's a good point another tech not all another technique but you have in the market here the mower information sharing platform it's a platform responsible to consolidate many different evidences of the events of the attacks it's an open source platform that you can see many evidences like you can see here in this picture this picture is from google so it's you don't have any information from the customer here so there are no words about that but it's a good platform to see and to consolidate more information about ioc's remember when you talk about ioses is evidence of the attack already happen but how you can work with the proactive
way so here we can using another different techniques based on eoa an indicator of attack it's only be based on the behavior and the why what is exactly the intention of this attack so this is a very important understand that it's more a strategy view it's more um mature view right so it's more intelligence view when you use it it's more a mature intelligence program right so you can use it to see the behavior and when you understand about this behavior understand about the unknown threads you can works you can protect them itself the your organization from the new attacks or not only new but the no known threat right so this is very important so some indicators included
the real time behavior not only limited on the endy point behavior analysis like for example if you see some noise standard behavior for example at a 1 am right in your organization on your company let's suppose that you have some uh past ex from microsoft it's as part of this is internals it's recruiting some remote descripting in your environment at 1am it's it's uh it's it's it's not common if you don't have any gpu to executing and in that time so on this time probably suspicious because why remember the why so why you are seeing in this log what are happened this is scripting running at 1am in my organizations don't have it's a total totally real time behavior right
and another point is what kind of dll so now i'm talking about dll what kind of uh functions uh are imported from the dll what exactly the sequence of the events for example like the same example of the pss act for example when you see the logs when you see the behavior we can see you can find for example um not only 1 a.m but 1 a.m 2 a.m 3 a.m 4 00 am some descriptive running in your environment but you don't have any uh you know task in that in this time so it's totally suspicious but you need to think about that and you need to ask why it happened in my environment okay
and user behavior in relationship to the digital threads like um there's some some user trying to connect many times or trying to authenticate different apps in a different time in the same time but in different for example uh region so it's uh why it happened because we're just only one user right and how it happened so maybe they have different access or they have some platform integrated with the systems but why you need to do we need to make a questions okay and and another point is about the ttps techniques uh techniques and procedures such using this kind of technique and this is another point so philip i don't know what is exactly ttp so how this
works so you need to understand about that you need to you know study more i need to gain the acknowledgement you need for example uh read more about the my tree about the techniques in using some attacks so you need to to find these informations when you have this information you can see the logs you can see the binary and you can create the the hypothesis and when you see that you can of course asking yourself about why this happened in my environment okay and another point is uh something happened in my my environment it is as persistent and stealth with stealth components so it's a totally using with attack so why it happened in
my environment if you don't have any for example applications running some because sometimes we have some like a false positive in our environment because they have some uh persistent components depends on of course depends of the applications but sometimes we have so we need to understand about that and you need to think about the questions why okay here's something like a suggestion to you about the same indicators on internal goals with the bad destinations why it happened because for example let's suppose that you don't have any uh business with brazil that supports that so why you have some internal hosts to try to connect with brazil if you don't have any kind of business with brazil or
internal hosts with a non-standard port very common in many companies so what you have some applications works in a different known standard port right so or many times many times to have or sometimes actually we have a public services or dmz to try to connect with internal walls if you don't have any applications within in this way okay and another point is off of our mower detection like i mentioned during our conversation for example um at 1am when the same time something tried to happen in my environment trying to infected my environment but i have the block the the block from the antivirus for example i have the some solutions block this tentative but why this happen always the same time so
i need to investigate more because remember the threads are changing all the time so for example for now i can block it but if this attacker changing the techniques maybe it will be blocked or not blocked so remember about the questions why okay networks this network scanned by internal halls let's suppose you don't have any offensive team so why multiple alarms events from a single host it's very interesting here because for example different infections right from the single holes why it happened or me or or even the the systems is reinfected with the mower so why this we have in my environment this host or this system with a target right so has a target why i have this so all
those indicators is based on the threading hunting or eoa indicator of attack remember based on behavior okay multiples logging from different regions if you are just one user maybe it's impossible to write you stay in the same place in different in different places the same time right and internal host using matches smtp protocol if you you know if you have just some environment inside of your comp organization and you have internal hosts to try uh connect with a different smtp okay internal host with the many queries to internal and external dns when you have of course the environment with internal dns okay so i i try to explain more about this concept to you because it's very
important you understand how i performed this test that i would like to present even during this conversation it's just to first of all it's a part of a theory you know idea and now i would like to explain more about the tests okay so first of all this is just a responsible disclosure for cyber reason company and by the way uh all those tests are reported to the company i talked with the managers i talked on by the way with the cso uh and sam sam curry i would like to say thank you for sam because they was they they he uh talked a lot with me that we have many meetings and and i can help the solution
to improve the some information after this the stasis that i perform in my previous job not in this this company that i have been working now but in my previous job and i will explain more during this presentation but i would like to say thank you to the cyber region team and this participation and this uh returning actually uh from the my reports because i performed this and the same task in different vendors but the answer is totally different because of this i would like to say thank you for some reason okay so let me explain more about the article presentation i'll be using my article here to explain all those steps here right so this is the inspection
with the brands we're using the laypolis um actually i would like to explain more about this first because i i have this in two different uh articles here right and i will present you some informations about this can you see i think you can see my page here right and um let me uh explain more about that by the way all those informations are here in my in my github right so you can see my github philip 86 slash strategy hunting you can find it here all those tests that i have been executing right so you can see here the cyber reason all those tests that i perform in here you can see you can read if you want if you don't
want no words about that we continue to be a friend okay but here you can find many others articles that have been worked right so let me explain about the idea behind all this um tests that have been executed in these different um vendors okay so first of all the idea is to perform let me explain more about this first id so the idea of this test is a simulate of the some uh target attacks is using some uh evasion it was invasion techniques like a dellal injections using a payload created by msf venom very common uh in the in the unix platform based on the on the kali linux or perot os right and
another it's using some power shell to try to explore some uh apis or using some apis in this um on this test right the second test is using shell injection right to using some the same or the same payload using msf panel right so uh just creating a reverse shell in this environment and the third test i will using another tool to execute the dll injection the coldness of this did this to its remote the dll injector right so from security exploited just uh using different tools to executing the same um test right so here is the scope of the test let me return here this is the scope this is the version of the the test that i'm executing and i
use executing this in two different machines and the windows 7 and the windows 10 so maybe you are asking why you as it could flip in a windows 7 because we have nowadays many companies with in those seven and by the way this version it is um supported by the vendor okay by the cyber reason right so this is the my the host name trendy hunting windows seven and i i have another uh with uh try the not ready but another windows with uh windows 7 operational system okay so i performed these two tests and then two different machines so this is the first uh they need um some requirement actually uh to perform i need to uh update some
requirements to executing the windows 7 specifically so i update the version here just to be clear right during this task as i installed this update sometimes the the words just in portuguese because i was whenever performing these passes in portuguese system operations right but i can translate to you this is the update of the security from indo this is the kb of the microsoft basically this kb okay this is to be supported from the vendor and all those things is updated that machine is updated okay so this is the attacking validations first of all i enable all those ops sorry for that i enable let me return here i enable all those features like antiviral anti-ransomware
anti-malware powershell and.net exploit protections collecting pictures app control and any point controls i enable all those three features and these cyber reason manager okay so that's my idea here what happened how i can uh uh execute the attack so first of all i enable the the policies as you can see here and after that my idea is to executing the attack but i needed to disable the policy to see if my attacking happened uh in the in a good way right it's my code it happened so first of all i disable the policies to execute this attack it will happen and after that i will apply the policies and execute the same attack to understand if the policy uh it works
well and they protect the environment okay so this is my my point here so first of all i disable as you can see here i creating a new policy that i called here policy used by zoop secret labs and i i call no police i mean i disabled all those policies and after that i using the first test performed i using this simple uh function from powershell to call this um invoke dll injection dot power shell here to try using the dll injection to infect that same process process id here and that will using the process from the cyber reason to infect that the machine using the dll injection this is a very common or known techniques right so this is my
idea here so as i could hear the the power shell right so i call the the binary from the internet as you can see here right and after that i invoke the solutions as you can see here choosing this process id 5032 right and i sat here by the way the the dll that i am using my attack and after that i will inject the malicious powershell here so as you can see here it's it's easier so i chose here this process uh 46 let me 4604 minion it's not a fun name but it's minion host it's a process from cyber reason by the way and as you can see here i inject my power shell and i invoke the dll
injection and i set here the process that i you inject my powershell inside of this dll and if you see here i called the same kernel.32.dll name i mean i i called the same name with the the kernel 32 dll using this uh this um process id right because i will inject the dll injection using these techniques in the cyber reason process using the antivirus process to infected the machine right so just to to using in this in this way okay so i execute this using this malicious dll and after that let me show you here i oops sorry for that let's return here okay i inject the attack here and the second the next page is
okay and i open my machine here and i open the the netcat basically no netcat i'm using a metal exploit actually to open the shell because inside of my script i have this uh using how as i mentioned the msfiveno and i open this port and i have the remote reverse shell here as you can see here the host name and i call the name it's uh financial things in portuguese financier right just to you know suppose that i am a financial guy okay so the the process injection leads by this msf venom created by me okay so have and so now i have here the remote uh code execution that i can manipulate this
environment as you can see here i have the control of the victor machine using the dll injection to inject my process here and to using the process by the way i using the process id from the cyber reason right so just to be this is the first test using here this this is the second let me check here okay the second step is i mean my attack here it's happened okay so i using the msf event to inject my um shell inside of this dll injection and are you using um a messenger to create my binary and after that i have the reverse shell but remember i disable the policy so i need to apply the points now here so i
after that i enable the policies and i try to execute the same the same attack as you can see here i enable the policies using by zoop security labs i mean i enable all those policies as you can see here but in this case now i call i call the payload in a different way i called it pa dot dll it's not more um can your doctor kernel 32.ll i using another dll right pa doctll to gain the remote code execution in our victim machine so as you can see here this is my uh new attack but now with a policies applied in this weakness machine okay so let's continue to see okay let me go to the beginning here
the policy was enabled as you can see here okay it's applied but as you can see here i gained the access one more time so maybe you are asking what happened philip the solution didn't block it then blocking you and here is the good point when i was analyzing this uh steps i i saw that we have a delay in this time to the policies applied by the manager so let me explain more how this works in a security solution when you have some solutions with antivirus for example and you have the manager one in the one side in another side you have an agent that you need to install in your endpoint you have a heart to beat
this is the communication with the manager with the binary side of the entry point okay so you're having a hard to beat some sometimes not sometimes but if you have the time with the communications between the client and the manager right so maybe the manager can be inside of your network or maybe this manager can be in the cloud depends of the solutions that you install in your environment okay but you have the hard to beat the timing of the communications between the agent and the manager right so when you have some solutions it's very important that they're saying what is exactly the timing of these heart beats so not only to receive some new policies or new change or a new uh
for example um update of the the the for example the engines or new updates of the vaccine or whatever but you have the heart beat it's this heartbeat can be in in for example in one second or one minute two minutes three minutes five minutes it depends of the solution and i'm i'm i'm i when i is performing that i will analyze what is exactly this delay and when i know that when i saw this delay i was um i thought man i can exploit this delay so remember when i explain about the hacking it's a how you can look into this and software and how you can use in your creative mind so take a look at that so why or
how you can explore the simple delay of the updates right and this is one of this interesting thing that i talk with the uh cyber reason because when i talk with the cyber reason the the cso talk to me and and and pass me the the video and my video uh talk with me about the vision from the cyberism he explained philippe if the attacker the attacker perspective explore explore my manager the attacker didn't disable all those the attacker will disable all those policies in the environment not only changing some policies and to try explore the delay in my environment if the attacker perspective the attacker will disable all those policies and you explore everything this is the vision
from the cyber reason and i agree in part but i agree but i mentioned with the cso in that case that if i if you are i am attacker i i i will change in just some policies because you know i would like to to as i put some attack more silence right so if you see uh how how many times do you execute some attacks in in more silence way the change you have to be successful in this attack it's it's more it's higher right because you will using in the silence attack but if you like to just to disable everything when you when you perform some attack maybe the the organization has some sock team or some
you know blue team it's more easier to see this kind of attacking happen but if your attack is more silenced the change to be suicidal it's it's bigger right so because of this i are are explained to the cso i can just change the points because i know if i found some delay longer because take a look that sometimes this delay it happened because or if the solutions has the long time or maybe because the internet connections in some remote offices is is not too too big right so they don't have a good internet on internet connections in this small offices so sometimes if you have the connections not to too good you have this delay and this is the
opportunity from the other attacker perspective to explore the victim machine right so when i see about that i thought man if i have this delay i can try to execute some ransomware in this environment so here is the another article when i explore the same vulnerability about the delay let me explain here and i will execute here in the same environment so first of all using the same approach i disable policies here as you can see and after that i using this script to infected with my machine so this is a simple powershell as you can see here you have just a uh information that um the idea here is to call using this api from our bazaar i
don't know if you know but more bazaar it's a repository from the community very that many uh researchers uploaded many different mowers there and by basically i call this api and i request this specifically hash this hash it's from wannacry by the way and uh here is the exactly folder that i will upload right in the victim machine but the point is philip i don't know what is exactly the path in the customer but remember if you have the remote code execution you can you can know about about this path right you you can agree with me you have the control you have the path that you have inside of the machine you probably you have about the
credentials of what kind of privilege you have in this user that you explore right and after that you call the api probably but no problem but you need to have this api here from our bazaar in your uh in your account okay and after that you can automatically call the invoke web request to execute something right to download the zip zip file and after that you can uh extract this file they will call some password you can set here the password and after that you can call the evoke expression to execute the mower inside of the vehicle machine basically this is the script in powershare right so we're using the invoke web request and you're
using the vote expression so if you see here is just a um a function from powershell right it's a true process in the windows environment right so this is a simple script here uh developed by when my colleague and me and the in jupiter innovation right so here is the script so again this is cryptic call in executing this behavior so let me explain here so if you see here in this uh results i call here right this i call this powershell called wannacry because it's hashi from wannacry once once again and i download here this is the request by api from our bazaar remember that you need to have the this key from mar bazar
to download this specifically uh okay and after that uh you need to to have in your environment the zip file just to unzip this file and after that after you extract this file you can execute itself in the victor machine so after after i execute this in with my machine the victory machine it was in fact that remember this test executing i was executed in the um with the known policies okay no no one policies enabled in the windows set environment and windows in the windows 10 environment here let me show you here windows 7 here and here in the windows 10 machine so we have in both system operations here and the machine it was in fact that as you can
see here so now i need to apply the policy okay so the second point is i enable here the policies using again remember the policy i enable about the anti-malware's anti-hands-over app control and all those configurations here uh suggest and i'm not suggesting but recommended by the vendor write exploit protection powershell.net all those protections so i've enabled and after that i executing the same uh attack as you can see here the policy it is a naval i think it's it's small but i will it's enabled ready hunting policies okay so here is the time that i enable this point so the next step is to execute the same attack right and let's see here i as i could hear the same
attack but if you see here using the same hash as i mentioned here and take a look what happened it was in fact that just only windows set machine why i feel like it was happened just only in windows 7 machining just a simple uh case because the time let me see here uh do it to this delay the synchronization between the server and the sensor that's installed on the vehicle machine during this four minutes maybe more the machine will be vulnerable to any type of attack so as you can see here in the windows 7 machine the environment it was infected because we have the delay to receive a new policy right and this is my point here
windows 7 but when i execute this in the windows 10 let's check here we have this some [Music] okay this let me check here and the windows 7 no assuming this is windows 10 in the windows 10 we have the time with the seven minutes to receive a new policy so in this way the machine it was infected but if you see here take a look at this here in this case i use another different hash that the hashing is different it's not i want to cry here are using another hash there's another branch or patch as you can see here so if you see here this is the new log okay uh it's the execution
the program doesn't works so i have some block it in this case i execute the another power shell as you can see here patchya dot ps1 it's a powershell but i called another um hash as if you see here i i still running not the execute demo i download here the zip file as you can see here i open the file i i unzip the file but when i try to execute the the binary i receive the block it by the cyber reason so why it happened because the update right of the windows 10 when you compare to windows server windows 7 we have different time to update the new um the new uh policies of the date so
that's my point here it depends of the system operation that you have in your environment it depends your office when you try to execute some updates you know and this is the point here so let me explain here here it's a good point when i i execute the same uh process in the windows 7 as you can see here but in windows 7 it was in fact that but in the windows 10 it was a block when you compare the both of the system operations okay so let's see here it's here it's another test it's another test but it's for another uh talk and yes so here i finished my presentations right so here some books recommended by
this kind of talk about the moral analysis and by the way i received this gift from the pack and it's pretty nice book i really recommend you because you can improve your knowledgement and more analysis and more hunting so how you can see more deeply uh any and you can create your own tests in your environment right so uh remember that just to clarify my idea here is not to tell you what the best solution that you can use if it's a reason trend micro or count striker or another one is just to give you this creative mind so how you can see the exact behavior of the binary non-binary the antivirus and how you can test it you can how can you can
execute the efficient and detection test why i am telling you this because when you perform some pocs or proof of concept in your environment you know it's sometimes it is difficult to understand the solution it's really good to protect about the threats right because you need to desire receive some attack during the poc time it don't make sense for me right and because of this my suggestion you uh how you can create your own attack and you can try to explore your own environment right so if you have any question guys so i i'm here and again thank you so much the staff team for having me here and my contacts again on social media so if you have any question
please let me know
i can hear i can't hear you christian i don't know i don't know if you are ah yeah you always forget that i have a specific button on my microphone to mute as well so i have like double mutes to make sure that i'm using it uh anyway so thank you very much for your presentation that was quite interesting i i don't see any questions on the q a but i i do have one question about like uh so this was a specific cyber reason i was wondering if you did any type of testing on any other vendor products to see if they were kind of vulnerable they had the same vulnerability actually when i performed stuff this i perform
this test is in a separate reason crowdstrike and so forth and actually is this is not a mainly test the melee test it is to understand how the engine works with uh no you know no mower so this is the first test the second test is to perform some uh uh actually to manipulate some more inside the environment this is the second test the the main test right so the first is download many gnome hours from the zoom repository from the github for example or minimum hours from our bazaar so this is the first the second is i will cop for example 20 to 20 hours in the folder and i will cop and pass in
another folder because when you're performing this you are writing some new files inside that the hard disk so if you have some engines they need to to you know uh perform some scanning this new file and this is the second in the third test i will be executing the full scan in the machine to understand about this this behavior all those tests that i am performing its phone is always using my real hours right so this is the main test that i perform but in in some vendors i have i know i saw different behaviors about the aims so the the simple answer about the question it's about the delay time i just said performing the cyber reason because we
had in that time this solution but my focus is more in the cyber reason but i have a a different surprise and in a so far than maybe not mainly encounter strike and by the way i have a talk about that so how we can explore using a power shell using a python script and how you do you know using all those informations are in my youtube you can see my information that about the tests in some classes i have the the demo by the way the video that i recorded and um but yes my suggestion from the audience is test is a cutting test in your security sensor because only this way you can exactly prove if
this solution is efficient or not because when you don't execute this test the solution maybe can be protect you but you you just don't know if it works well if you're suffering some attack right so that's my point here yeah that's quite interesting and it also kind of reminds me on and it kind of uh the word that comes to my mind is methodology right it seems like you have like a methodology to try um different kind of edr products uh and i wonder like do do you have that published somewhere like uh like you know like you know like the pentest mental body is like okay you do reconnaissance you do this you do die
you do that right it would be interesting to to know uh to read about like the methodology that you use like the basic things that you look for when you are evaluating one of these edr produce like first download the second like try to disable it re-enable it and put real model yeah different types of mobile uh anything like that do you have anything published uh around that uh yeah i have all those uh information that i published it is my web my webpage and the linkaging and uh about my evaluations in my about my tests our publishers are there and another interesting test that i'm executing is for example i don't i we haven't bazaar
for example you can call by api the all those mowers uploaded during the day uh they all those models uploaded during for example the day the marbles are has a repository they when they put all those mowers there so for example probably let's suppose that you have in a in on wednesday more bazaar can receive for example 1 000 in this day right so it's a daily breaks called daily breaks so you can request this daily bread and you can download more than one thousand hours in your environment so you can simulate for example somehow to break infection in your environment as i i executed in with sofas for example and the answer is totally you know like i would
like i will use this this word it's the answer it was right because the the the security solution tell me oh yes we we try to execute these tests and uh you know i mentioned you're the changing in my environment it's the cpu is too high the memory is too high because i'm you know how to break fashion and the cyber in that sofas tell me yes it's true we know that so you know that's the high cpu high memory so and if the engine is broke so what happened with the protection i didn't receive the answer about that right so that's my point here i'm and the answer again from the sophos it's and it's not exactly test that there's
surface executing in our uh engine so nice but if i suffer it's a multi-break infections so how does your solution happen you didn't test that i know probably it's not como attack but now i know how i can broken the sofas right so you know the the the the mindset and um but unfortunately we in some security sensors we don't have this uh open uh to take open talks right right so open conversations to talk more about the some efficient detection tests and um i i think that's it's very important to open to conversation with the researchers with you know to understand because man some lab some you know some organizations like a gardener like you
know uh forester pinger called it's you know it's a good reference of the the organizations with some uh you know information about the secret solutions recommendations but how exactly happened the tasks right it's a commercial password it's a detection attached with a real malware it's a real life right this is the point here in your in the end of the day right yeah yeah i feel like sometimes you get tests with malware that they of course know that they're going to detect right but when you throw something else you never know all right so we've got another question from the q a i'm going to read that for you is how did you manage to
to do isolation on the virtual machine for malware analysis and still get updates from uh av i'm planning to get into my way analysis and thread hunting in the future and i'm wondering how to do that that was asked by terence yeah yeah good question so how did you manage to do installation of the vm firmware now this is a good point here because for example you when you have some virtual machine you can pass the mower but when you created this virtual machine you configure some networks and you you execute them out inside of the virtual machine but it's totally different and by the way it's a misconfiguration concept when you this when you tell not
know in this case the the question but when some people tell about i you have the virtual machine and i have the sandbox there now it's not a sunbox virtual machine sandbox is that you have a virtual machine with many engines inside of that and these engines is responsible to understand the behavior of the mower right so this is the point here and when you can install of course the amount the antivirus inside of the virtual machine but you need to have the same scripting running inside of the virtual machine to understand all those behavior when you perform this monitor inside of this when you run the mower inside of the machine and off reports because nowadays we have
many mowers using the sleep techniques as i mentioned during the conversation it's the simple uh functions important from dll from the microsoft by the way and you can import of this virtual machine in in sometimes because the mower will see the environment and the more one will think i am here in the virtual machine i can execute my malicious uh disturbs right so this is the point here and of course when you need to perform some analysis it's very important when you perform this in our isolate environment like a virto machine has mentioned but it suggests to clarify the concept when you talk about the sandbox and virtual machine right so and this is the first question right and
another question is am i planning to get into more analysis prodigante in the future and i was wondering how to do that right so that's the point uh we need to understand these different behaviors right and and how you can investigate that in the sandbox concept and the virtual machine concept and by the way and in my github i have some um awesome our analysis and uh in awesome tradition if i remember correctly i for this awesome project just to to be easier to find some informations and you have there in the awesome our analysis many different uh in antivirus scanning and and sandbox uh using the cloud and you can perform some hours inside that and you can see the behavior
all those techniques is based on the analysis dynamic analysis right because when you perform this modernization controlled environment and you see the behavior and runtime when you talk about the statistical analysis you analyze the malware in not a runtime it's usually it's more safe right because you see the the structure of the code how specifically dll called in the system operations but you don't execute sometimes in the environment right thank you for for answering that uh i would also like to to give someone a bit of answer to terence there about like the isolation that you usually have on on your virtual machine you configure your network and you put a firewall on front of your virtual
machine so you can figure very tight rules that you only allow the virtual machine to talk to basically the service that you wanted to talk so you allow to talk with the ip addresses of where you av get the updates for instance but you don't allow it to talk to anywhere to anything else and that's the only uh traffic that your lives for instance so that's smallest yeah you know another point is when you talk about the virtual machine is uh sometimes we the analysts like to disable the network with the virtual machine right to just to see the behavior or you know not to spread the network or inside of the environment but sometimes the malware in
your environment needs to have she needs to access the internet so because on this it's for example if he's a dropper for example properly it's not totally malicious because they may mainly strategic many functional structures many the main function of the dropper is download another malware so they need to access the internet to drop another model to download the model actually so and this is the point here all right thank you very much for for all the the answers there and for the talk uh it was a pleasure to have you here yeah thank you thank you everyone thank you again christian for for for having me here and i hope next year to be in
person and by the way in january i will move to portugal i will i will be next to barcelona and uh
and that's it thank you so much everyone perfect thank you very much