Security Engineering != (Admin || Analyst || Responder)

Show original YouTube description
Show transcript [en]
foreign
hey welcome uh so uh I'm Craig Bowser and this is uh Lou we're here to talk to you about security engineers and security engineering so standard disclaimer uh the opinions are most likely ours but definitely nobody else's so I am Craig Bowser I have been doing security for over 20 years uh and I have a bunch of letters that I have earned or paid for I've worked in the DC area in government and Consulting Contracting type of environments uh married got kids boys which means I have a full house and no food in the fridge and so that's me that's your turn I know I was waiting for you to do the slide thing oh no oh
okay because you know my pictures might be a little bit more cuter than well it is your kids are younger uh good afternoon my name is Luke mcgoon I go by Lou uh I do have a Twitter handle known as infiltrate I was lucky to grab that one with the league speak uh I've been in cyber security for about 10 years but in it in total about going on 25 years I've been primarily in defense contractor industry uh we recently moved over to uh security Consulting with a known so-called uh security consultant vendor uh I do have some letters behind my name and uh I've I'm really excited to come and talk to you guys about
security Engineers because you know I don't you know raise your hand when was the last time you had somebody talk to you about security engineering I don't see any hands maybe one all right so we're going to talk about security engineering we're going to give you some you know some Frameworks in fact we're going to give you another framework because we love Frameworks we have the the nist framework we have yeah so we're going to give you another one because you know you can't have enough framework exactly talk about the cyber security job market as it applies to the security Engineers a little bit about education about uh you know what it how to become one how to get there
and give you some some of the current challenges going forward in the Outlook of what security engineering is like so let's start off with a little bit of Baseline let's kind of Define what a security engineer security security engineering does what yeah security engineering does anybody know what security engineering does anyone do pure security Engineering in here they consider themselves an a security engineer anyone well I mean I do but I swear to you this is not one of those drug farmer and sales pitches or whatever but anyway security engineering is the Art and Science of designing security controls into your organization into your infrastructure and things like that that is what security engineering is in a nutshell
that's true so a security engineer is someone who does those things but does those things with the added context of doing it in uh interactively or interoperability interoperating with operations and business making sure that those two those two parts of the of the work environment continue to function so we're classically you know there's been this whole thing you know when your mama asked you what do you do and you tell her I'm in I.T you know that's what that was used to be and you know so so nowadays we can now say we're in security engineers and that's why right we're we're doing this so let's talk a little bit about the history of where
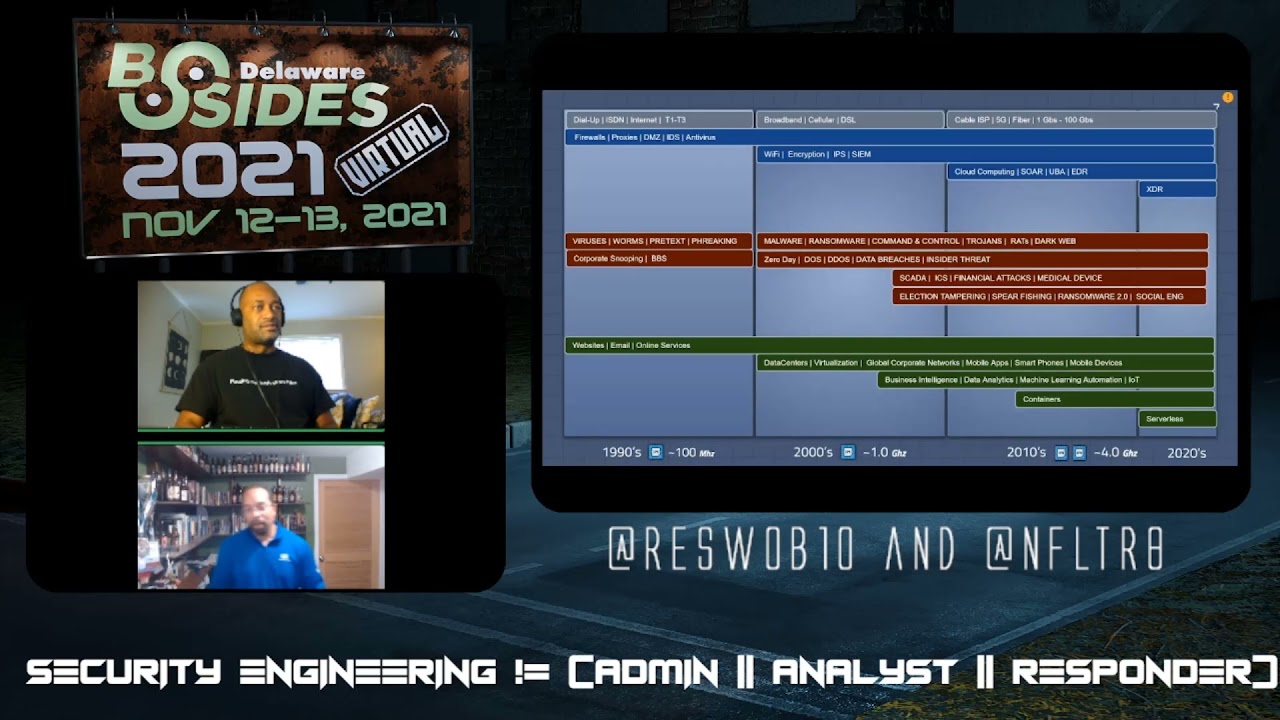
you know security security engineering came from and why it tends to you know why we think it really needs to be viewed separately all right many of you on you know been around a while you know some of the history of this but we're gonna you know do this about five seconds right or maybe 25 seconds but yeah yeah so if you look at technology you look at uh where we where we've been to the night uh early 1990s at the beginning of the internet if you look at where we are today with web and Cloud you you can see uh with this slide that the progression of Technology the progression of everything accessing technology also progress the threats and
vulnerabilities and things that are happening in the in this world today and that really is the Nexus of how our our cyber security industry really kind of uh formed and and um and morphed into what it is where we have all these Specialties penetration testing uh uh compliance you know we just had a guy in here talking about compliance and and uh and the software developers web security and all those other things and now we're going reaching out into other things such as drones such as ICS even going up into space so most of this represents uh that transition of Technologies as as we go uh based over the last 30 years and I think what we want you guys to take away
from the slide is the increase in the number of things that we in security have to be aware of and are responsible for right as Lou said back in the 90s it was you know very simple uh relatively in the sense that you had maybe some a couple viruses some worms running around you had your very simple websites and emails uh you know whereas today the you know some all those things are still around but you've added all of these Technologies such as you already mentioned and so now all of those things still have to work together I remember when I was in the early 90s I'm in the Air Force and I'm doing Opera uh um what
do we call it interoperability interoperability of doing um making things efficient and making working on doing going to Air Force bases and we're doing troubleshooting and optimization at different bases and going into a base in its windows nt4 I mean some of you guys have no idea that Windows had an NT version but you know it that's what you know we're we're looking at their configuration and making it work better but we're adding Security in so security is sort of just sort of part of your job now you have as he said all these uh specializations I was talking to a friend just earlier today and he says you know there are now up to I think 45 individual definitions
of cyber cyber security jobs uh you know that that you can go into including cyber security and fishing expert right not not the not not not you know catch a fish but catch a person guys so how do we how does how does security engineering how does a career path uh flow this is from cyber seek this this website's pretty uh pretty interactive as far as just being able to kind of show your progression of tech of of of a career I think the one thing I really want to say from this slide is that cyber security engineering is not an entry-level job it's not designed to be and we'll talk about more why that is
the case but you can see that you can go from where you start off on the on the left as a you know so the beginner rules so these entry-level positions you hear talked about of traditional the I.T support server Administration Network Administration uh you know these give you that Foundation of understanding the environment the Enterprise the networking and then roll from there into a more advanced positions such as cyber security Specialists incident response you know you can we can quibble over where these fall into the career path but the point being that you move from there into perhaps more consultant penetration testing but once you have some all these sort of tasks under your
belt it gives you that uh contextual view of the environment that you can then really get into an architect or an engineer role with the roles that you need to understand all these previous tasks all these previous careers and previous views of the network to really apply and don't worry about the some of those numbers right there below which are have some what remaining consistence we'll dive more into salaries later in the in the slide deck so where are some of these skills what are some of these positions that all kind of flow up into being a security engineer well there is sort of the isso isse role and this may while this may apply more in a regulated industry uh
these skills are still can be used in many commercial or other companies or organizations because companies still have policies that they need to apply or write or security policies but you know another in regulated Industries you have compliance you have regulations and as I said no matter what you're still writing and enforcing the policies that your management should have uh you know it's still best practice even if you know whether you're a Walmart or bank to have or Mom and Pop Shop to have hey these are the things you should or shouldn't do so the isso role in that sense then you have a security Arc architect role this is the person or the individual that is actually planning out
where the organization is going as far as what how to do security down the line how to design a secure network how to integrate these new technologies how to be prepared for uh vulnerabilities and exploits and attacks and new threats coming down the pipe they are they should be looking ahead to what should we be doing how should we be preparing what should we be budgeting for in one to two to three to five years then you have your basic analyst role and this is the role we hear a lot of talk about because this encompasses encompasses things such as information I'm sorry such as incident response such as your sock analyst your eyes on on
glass type and so this person is monitoring your state of security posture they're doing that uh response and investigation and so and they're looking into incidents but the other task the other role that that really boils up into a security engineer is the network person the server admin because this is the person that's building the infrastructure maintaining the infrastructure keeping it operational that's making sure that it's accessible to in this case we're talking about you being able to log on and get to the data talking about a CIA Triad the accessibility part of it and making sure that all of the information is able to be reached and uh delivered to where its destination and so on top of all of that that's
where the security engineer comes in there or that person overlaps all these things where they are implementing the architect plans they are working with the network engineer they are ensuring the analysts can do their job and they are enabling the isso to ensure that policy and regulations are complied with requires some hard skills these are the skills these are the the touchy-feely measurable things that to be able to do your job and so infosec right built right into the name so they uh the security engineer should be able to understand policies understand what best practices are they should know about and understand vulnerabilities and how things can exploit those vulnerabilities they should be able to understand that how
those things work which leads right into knowing and understanding uh and even having some experience with attack and or defense tools you know how are you designing your network to stop or detect um you know Metasploit or or power sport or any of the tools any of those points yeah any of this it's a bloodhound yes right what are these tools what do they do and how do I know that they're being used or not used on my network so uh so this kind of hard skill is you know obviously built into it but then they should understand the server administration because if you're an engineer you're going to tell the Ops person this is how we should build these
servers to be secure or work with that the server Administration Ops and I T to build secure servers you need to be able to speak their language and not just tell them go secure that stuff it's not so speaking their language understanding what operating systems do and how they work how they actually need to be monitored and administered understanding how authentication Works how web servers work how the web platforms work how databases work understanding all of these things now you don't have to be an expert in them but you need to have that kind of minimal uh you know be able to again speak the language then architecture I'm sorry uh then the network administrator role but this is
absolutely key understanding how near network works from your protocols that are going across the network tcpip uh I you know bgp understanding just that communication layer as key to really being able to design that Network because you have to understand where your data is moving into and out of your and across your network understanding the infrastructure for your routers or your switchers your proxies your firewalls what's going on behind the scenes what is the impact of just you know the you know deny all um you know Allowed by exception you know the date be you know permit by exception boy I'm screwing up my acronyms but uh you know understanding that so you can talk to
those things so you know providing because you're providing that guidance across the Enterprise and then finally you know especially within the last five ten years it's you know we're as the move to Cloud especially in the last two years has accelerated understanding how that has impacted how that changes your engineering and your design and your the responsibility that you have of your network because you've shifted where your data and where your processing happens so what does that mean for uh the security and the monitoring of your network to allow your environment to allow your team to continue to function now you talk about the soft skills guess what as a security engineer you're not going to be doing you know a whole lot
of sitting in front of a keyboard doing you know coding in the dark corner of the room you're going to be doing a lot of documentation so writing is critical so memos emails presentations because you're going to be talking to people to say hey this is how we should do it and why we should do it and you have to explain that we are I've referenced several times talk speaking the language to other people to so that they are able to follow along why you're saying we should you should do X Y and Z you need project management time management skills because you're going to be working on things that take time to implement where you're migrating from
this version of software to that version of software you're going from on-prem to Cloud this is these are multi-step multi-month or multi-week tasks and you need that project and time management skills to do so people skill bills you're going to be working on a team you're going to be leading a team you're going to be or even if you're not on or leading a team you're going to have to be working with other divisions who have other priorities so you have to have that kind of people skills of diplomacy performance Under Pressure because these projects these tasks will have visibility across the Enterprise at a high level so you need to be able to be
diverse in who you're pulling in um you know and who you use as well as you know inclusion and that is so interesting because it's not just saying hey who am I going to hire but it's who am I going to work with you know just because I don't like this person doesn't mean I I ha I can afford to ignore him to get my project done you know learning how to work with all sorts of people is is key business skills because you're going to present projects or proposed projects and you got to say hey uh you got to convince management upper level management why you this project should be done why should we move to the cloud
why should we buy that software why should we disable this protocol or or this whole environment why should we turn off the data center in you know Wichita because we already have one you know in you know in Ashburn DC or something you know Ashburn Virginia why should we do all that okay exactly the one no one knows about um so business skills are important to understand if you're a sales engineer you're convincing customers you know why this is this is important and if you're not speaking that sales language you know you're not going to be able to uh make that sale or convince the customer to buy problem solving attention to detail security engineer is a problem solver
but at the end of the day that's what they're doing you know when Ops comes in and says we have a new widget that does you know the Whatchamacallit you know we want to install it you know you have to figure out well how does that affect the security of my environment and how do I make sure it doesn't affect it too badly and then the thing that I think is important for every security person whether no matter what in a career that you're in it's just curiosity and persistence um and so do having those key uh traits just allows you to go well why how do I get this to work and trying it and figuring
out a way so how do you get some of these skills how do you get some of these capabilities uh you know is there is there a single path there's no single path you guys know this you've been in security and you've talked to enough people there's not a single path but there are definitely uh options along the path to form your own uh destination and so you know today what's interesting is that there are more colleges uh and more schools offering security and security training now both at the undergraduate and graduate level right and they vary you know in in quality right I think it'll take a few years to kind of shake out what should be taught
at the undergraduate and at The Graduate level but as that happens you know there are those options that weren't around you know definitely not when I was going to school but they're you know this is a recent phenomenon so we continue to see this growth uh there are training companies right where most of us are very familiar with who Sans is but there are others Black Hills is building of quite a bit of a curriculum of options to do training uh udemy LinkedIn learning there are boot camps uh when I was doing my research on this I found a number of secure infosec group camps I can't speak to the quality of them but I've got a lot of links
that'll be at the end of these slides uh um when we we will put out the slides and you can go through it so there are a lot of these options for training you can do vendor specific training absolutely if your company or if your organization says you're going to manage this thing you first thing you should ask can I get training on that thing and so vendors will very happily sell you training on that thing um so if you're lucky some vendors will give you training for free AWS and which is on Google and Azure and will absolutely train you for a lot of things for free because they can lock you into their environment uh so but that's not
to say it's a bad thing but take advantage of training whether it's uh free or paid for absolutely and then we all know that you're going to have to do a lot of self self self teaching self-training and so there's you know ways to do that coming to conferences like this thank you guys coming thank you guys for attending our talk uh but you know this is training this is all good it builds soft skills of you know and gives you ideas to build hard skills there is a website uh which again I'll have what we will have in the references the national National Initiative for cyber security careers and studies and I hate that title but that's what it is
it's really hard but they are great for understanding what skills you need for different positions and so if you're applying for position and you're thinking well what do I need to be a system security developer they have a list of all the kpis all the skills that you need should have for that great for employers to help build job descriptions as well uh they actually don't have one for security engineer but if you combine some of these it does you can you know it does kind of flesh out and then you can have uh certifications there are a number of search you can uh can can get that will help you now we can debate all day long about whether or
not assert is a good thing or a bad thing and how good they are and how many you should have I like to say I have just enough to get me past HR uh so um that is uh that's my that's my view of them but they are there and uh they absolutely can help and if nothing else some of them they give you especially the beginning of your career we'll give you some of that foundational training that you can build upon as you continue to grow in your career so with that uh then let's you know how does that apply in real life you were talking you know we were talking about you know our our uh our Triad yeah yeah
definitely uh introducing the Triad um we call it the SOB because we thought that would be really uh more memorable for you except for some of the other things and um what we found out over the career path is this is that they're basically a category of things that you're going to do that we've done in these in these areas here we've supported operations we've talked to vice presidents and budget people about products and things and we've been in situations where we're going to have to respond to security incidents and things like that so we we thought that with this Triad and and with others that that you know that we could we could have a framework for you
if you're wanting to understand security and maybe be able to apply some of those things uh to that so under here details or or some bullets uh in each category that we're going to talk about but essentially uh it is something where we think that you you should use when you're considering designing or or implementing systems and security controls across your organization so the security part of the Triad represents on the function that you need to do or ha or be able to uh Implement for the control so for instance if we're looking at products and services to implement into the company such as in a virus or or or new IPS IDs or next-gen
firewalls and things like that there are a lot of things that you're going to have to understand about those systems you know are they compliant do they have uh the the latest standards and things like that the gentleman in the previous talk talked about them being compliant in terms of encryption standards and so on and so forth so those things that you have to understand are they best to breed are they top vendors or or mid-tip vendors or are they you know next Generation stuff that haven't been rated and things like that but the meantime the the main ish the the main focus in this Triad is does it help me do my job better does it
help me detect stuff better does it help me find stuff better mitigate stuff you know what are those things that we do uh what are those things that we need to have in this in this uh area to make our job better not necessarily different difficult but at least better so that's that's the main thing and then we'll have an example of that kind of shows everything uh put together for a specific scenario do you talk about operations and mainly here we're talking about supporting the business operations the security operations or or any any of the of the functioning parts of the organization that that you're responsible for you know do we how much do we work with it with our operations
teams and things like that what what is the impact to the security in the organization are we are we the people that slows things down speeds things up uh blocks this or you know or makes things faster and better are we the no you can't do that organization or are we or are we like hey go ahead we'll see what happens kind of thing so we are definitely trying to get away with being the organization of no all right it's like that we need to leave that way in the past and then and then finally a key component of operation is understanding the entire organization and the structure of what you're trying to protect and secure
and finally it's about the business it's about making sure we're making money or making things happen or or providing a service on a consistent basis it's about the ability to understand how the security operations uh I'm sorry how uh Security in general is a business uh uh value is something that we can measure a return on investment that we can measure all these financial performance indicators because like you said before you might have to be in front of the c-level folks telling them why you need to spend two million dollars on your new networking stack protocol and what's the benefits to the company right and I think the other thing is and it was mentioned during the panel this
morning is you don't want to be the friction in the business and so one of you know we have to be aware of the what the things we do does it impact profit or does it impact um you know whatever the business goals are you know we cannot as security be that that that friction because without a good reason uh that will get shot down when I say a good reason I don't mean a good reason that we think it's a good reason I mean the business has to have a good reason to have any kind of friction so we need to be cognizant of the tasks that we do and the things that we want
uh and and its impact on the the business goals so with that there are a lot of scenarios that we can talk about not hopefully a lot but a a fair amount of common day scenarios and with this one we chose to talk about attacks on the infrastructure and you can you know use your imagination to to understand where where we're going with this uh it could be anything from uh local tax pipeline attacks drone attacks to to you know War you know right but the overall situation is that that there's always something that's going on in your infrastructure that you need to be aware of right and if you're going to take that and apply this framework to it
um you can see that there are several categories that you can kind of you know begin to work work on your solutions to your problems right so for the security side of the infrastructure attacks we're looking at do we have an increased tax uh attack surface we're not just confined to the Network anymore we're now going social we're going you know iocs and and devices and and all kinds of other things that are maybe outside the perimeter of the company you know does this affect our ability to meet uh to mitigate things to detect and mitigate and respond and contain and what technology improvements do we need to have in this area you know because you know you know all Palo Alto
may not be able to to do all this stuff or you may have to get a web application firewall or you may have to look at maybe getting some kind of external uh uh news service such as uh was it uh extra hops things like that right well the the technology also comes into play as you start bringing in you know we've talked you know for a number of years in the industry about protecting OT as we start bringing ICS uh you know you think about water or or electricity or you know other types of what traditionally was not connected to the internet and suddenly is and so some of those technology improvements some of those
Technologies do not fall under the realm of our normal security tools so we have to understand how to bring in those new new tools and new new monitoring capabilities exactly and then what does that mean for your overall organization how much does this affect your socks does this mean that they're going to be doing more work they're going to have to figure out what's going on quickly quick quickly or quicker quicker quicker that's the more that's the word uh you know what's the increase in security operations what is the point to where we had to bring in more teams right so that's that's from operations perspective because we may not have expertise in drone attacks
right so we might have to figure out how to get other teams involved or maybe even other vendors involved as well uh going back to the vendor thing again it's dicey right uh so and then finally you know at some point you know the business is aware of what's going on and they want to be able to uh understand how this is affecting how attacks on their infrastructure are affecting their business will it affect resource constraints will it affect Personnel will it affect you know them shutting your you down your reputation yeah exactly and if something catastrophic were to happen to something or to a part of your your organization so again those are the things that when you're looking
at a tax on infrastructure from a security engineering perspective uh um the solutions can become uh or the the the approaches to solving the problem can become um uh vast but if you have a framework you can kind of hone in on some of the key and major things that you want to to uh to to work on so with that you know uh again a solution may be that we might move our stem to the cloud so they could be resilient it could be available 24 7 and be uh uh maybe hopefully better protected from infrastructure attacks and things like that could be available to anyone who's remote as opposed to exactly exactly so
and with operations you know um we we can consider integrating in threat intelligence teams uh hunting teams penetration testing teams to augment our uh our monitoring and and evaluation of the attack surface and then with business you know we can we can definitely focus on uh ensuring content continuity and resilience and making sure that operations stay up and focused or we can really fortify return on investments for all these services and things that we're asking our management to to to uh to invest in so as a security engineer like we said before you know understanding those those things and categorizing those with your solutions to the problem uh I think you know this Triad is is representative
of something that to help you uh down uh with your careers and and with what you want to do as a security engineer and give you a framework of what you need to learn going forward I think it helps additionally really helps frame the decisions that you need to make every day it helps Focus uh what tasks that you need to do and why you need to do it it helps you really bring bring all that concept into a methodology that you can use to talk to your peers talk to your management and even talk to your uh the people that you know your employees are or your mentees so that they better understand what they're
doing and why they're doing it is important in their daily tasks and one other thing is that all of these things here in the framework and what we're talking about is really that underlying training of leadership right because you always wonder like how do you get to be CEO or or vice president or something and very few technical people become CEOs and vice president because normally you have to understand the business side of an organization but nowadays you have the Cecil row you have all these other intermediary sea level roles and with with what we're learning here and our experiences in security engineering you're really getting to a point where you're training yourself to be a leader
or having those experiences and being a leader and hopefully lead the organization further yeah so the need for security Engineers continues to grow um you know in inc.com in just a few months ago said this is one of the three key areas that that organizations need to hire not more analysts you know I mean yes more analysts yes more incident responders but they should have a security engineer also as marked as one of the things they need to that that they need to hire and it's simply oh thank you it's simply because uh Engineers look at the broad spectrum understanding these three pillars these three areas whether you know whether you're using the framework or not but
understanding those three areas and understanding the impact across the environment so uh you know what really struck me was that uh so for those of you who are you know us-based to under you know who uh or even in and around the federal government Biden released the executive order 14208 and and I mean a quarter of my life in the last year has been taken anyone else super impacted by that because basically a quarter of my life if you if it hasn't let's just say that the number of security initiatives in this document is redonkulous that is an official word so it is quite a bit anywhere from zero trust to endpoint or security to additional
logging to multi-factor all of it is now codified in this executive order that federal agencies DOD included need to comply with so uh and he said hey if you are not including a security engineer in this initiative in these initiatives this will not work because you can't just hire a security analyst and then tell them hey go figure out how to implement multi-factor authentication across an agency that that's an engineering job how do I do that because it's more than just you know what a security analyst traditionally does and so yes that security analyst can become a security engineer but understand the thing he is doing is not analysts it's an engineering role and so that is his
point so you look at showing the money right I am showing the money let's show the money so what are we talking about you know okay spoiler alert uh in case you didn't already see the slide there are security jobs out there there's a lot of them um this slide really is just focused on a security engineering um and what we pulled from we pulled from two sites Dice and indeed.com uh you can see it and indeed it was 11 000 jobs this is uh 2021 yeah late yes only a couple of months ago but we did update the Baltimore Maryland slide recently yeah we did so let's call them there yeah trying to be a little bit you know
focused on this area you know Baltimore Maryland there's 1900 security engineering jobs open you know as of right now they're you know so they're looking for uh people to do this gig right I understand yeah there's a ton of them you can pick and choose but this is a specialty that's you know right off the bat is is a mid six figure job yeah and uh and I was talking with Craig earlier this morning I said you know we're trying to update this chart I'm now seeing Junior and entry-level cyber security engineering jobs offered now well I will say there's Junior jobs but you and I were saying I don't think there's not an entry level job now in a
sense because again this is not an entry they're not coming out of college and saying I'm going to be a security engineer you don't have enough foundational experience to to be able to do this I was uh so Jack recider guy does a dark net Diaries if you haven't listened to dark neck Diaries go listen that's great podcast um but Jack recider just put out a Twitter Thread about the you know the like 20 things he's learned as a security engineer and one of them was you know talking about the difference between Junior and senior security of folks is that you know a junior person may have enough or the same skill knowledge technical technical knowledge
thank you the same technical knowledge is a senior person but the difference is the senior person knows when and how to apply it and the business and operational impacts of that Implement implementation it's so it's really that's the concept and so sure you can come out of college having the right skills but it just don't have that you know life experience to know when and how to apply that stuff so um but it's it is interesting as you said that you're starting to see those Junior things so just you know reminder hey this covid-19 has you know impacted everything right exactly exactly work from home telework you know this impacts you know how we design and Implement security across the
board I'm pretty sure a lot of you had to augment your VPN and zoom Communications and infrastructures right over the last couple years so what's next uh presidential orders still in effect it's halfway through is still going on and we're going to see the repercussions of that for years zero trust automation yeah all of this involves engineering yeah automation is our topical word for machine learning stuff and and data analytics so uh an automated response an automated response you know so when the robots take over you know uh cyber security jobs you know the infrastructure is code yes that is something else that's coming it's very fast this is uh um but here's where we disagree yeah
yeah so securing the blockchain and what this is going to affect you know these are things that are coming up these are going to be security Avenues uh that you know we kind of he thinks that is I don't have so much of an opinion but okay we put it to the audience um pandemics and uh has been very obvious in the last couple months War yeah just you know these are things that we are going to have to engineer to protect exactly one of the things about that is that there's a lot of story out there there's a lot of people dealing with misinformation there's a lot of people trying to protect not only their
companies in Ukraine and and and relate it but they're also trying to to train up even the I.T people to help defend those lines so a very good very good point about you know how security engineering is very reactive to situations and things like that um you wanted to give that dedication yeah oh okay uh also like I said uh we had a friend of ours uh pass away several months ago our name was Stephanie Schaefer I just wanted to uh give her a dedication dedicate this talk to her uh she was a big force in security and Engineering I worked with her for several years and she was very an advocate of women in cyber security
so I just wanted to say that peace but thank you for allowing us to come and talk to you today right and there's our our contact information uh you can reach out to us at any time these slides will be posted if they're not posted already this is a bit of an update from our previous talk time we did this and one of the reasons we want to make sure we post these slides is because we have a crap ton of so so of stuff so with that we'll take any questions we've got time for some questions yes unless you're all visibly or oddly or intellectually stunned about security Engineers yes ma'am
what are the best kinds of I.T systems what kind of skills do they focus on so what are the best I.T skills for people who want to come into security engineer you go so [Music] the slide where I talked about those different uh skill sets so understanding you know operating systems and what you know what a server administrator does and how to build domains you know so having a having a solid understanding of that I'm not saying expert right because there is no way I'm an expert in building an ad I know just enough to build one but you know if Trimark came in there they would laugh me out the room so I know enough
to how why you know how to build one so under you know eight server Administration Network Administration absolutely understanding how routers and switches and firewalls and or how that the network transport protocols work uh and you know basic understanding of just pulling apart TCP packets and how those flow DNS HTTP understanding those those protocols and then obviously having a really good you know if anything you want to be deep in knowledge on of everything it's the security uh skills understanding attack and defense and understanding as exploits and vulnerabilities why and how and you know the you know you know understanding what the heck of buffer overflow is and all of those things privilege escalations so
those are the things that you really should have that kind of knowledge of and now now I did tag on this Cloud as well but and that's important too because there's a whole shift and so so you know again having good understandings of server cloud and network and a deep understanding security um if you can throw in some policy and uh understanding and compliance and regulation understanding that's good but it's I'm not going to say it's required but it's it's good because it gives that round rounded ability so that's where I would I would you know that's where I would look to you know if they're weak in any one of those I would build it up
there I I would add to that uh you should also explore parallel so for instance if you've been a person who's an application maybe you did some kind of business application or something like that you might parallel to software development or you might parallel to database management or something like that or some products where you you can analyze what's going on under the under the rim a lot of people uh who solve problems mostly been end up becoming penetration testers until they get tired of things like that I don't know I became a security engineer but but you know because because of that you know because a lot of people would see security Engineers like oh this is
thing you have to have 15 20 years of experience to be I need something that I have my my current I.T skill sets and I want to go you know kind of moving in that so always look for parallels like what are you doing now and what what what is the parallel thing that you can do just to get into the barrier and then you can Elevate from there yep cool thank you great question yes sir
yes
okay let me let me yeah sure repeat them uh so the question is it seems that a lot of companies are Outsourcing their security services what skills or things can Engineers do to keep themselves busy or I would say paraphrases say employed or more valuable to the company right good question good question so first of all it's hard to Outsource security engineering because that part needs a deep understanding of the actual environment that that's being engineered and I see this because what sometimes happens as a consultant you know my company has called and said hey we want to implement X and I have to ask a lot of questions just to under try and get a
good even make a decent recommendation and even then ninety percent of the time they're like oh that won't work because you know such and such in you know accounting does this that way well I didn't know that you know I can't project that I'm outside the company so it's really hard to Outsource that having said that the skills still apply but wouldn't the skill that you have to then grow in especially if you're going to stay in security engineering is because you can go to these Consulting companies is you have to grow in the ability and that some of the people skills and learning how to ask the right questions and then interpret the answers
to be able to develop appropriate Solutions and so that's that's a challenging thing I mean I've been working on that for two years as I've in this new role as I I came out of Government Contracting and into this more salesy role and so that's a very in that's a very different skill to that's a people skill that I've had to develop of saying okay well what about this and what do you do here and how does this work and and getting the right answers and then working with who can I talk to that has that information when can you get back to me on that so um but that's how you kind of build it
because if you're not doing security engineering internal for your own organization you can do it external for as a consultant and I would add to that that you will probably expand on what you do for your company going forward so for instance not all things security engineering have to be in security engineering you could have stuff that go into legal or Pro uh other PA person or you might have to go to operations and help solve problems there so showing that you can solve problems in other areas of the company that may not be security would be a great asset for you to to continue to work there or work you know gain the skill that you need to to move up in the
company yep yes yeah sure
so the question is how do you maintain awareness of solutions and things like that for when you want to uh recommend those to your company basically um well so sometimes you get lucky and work for a vendor that has like 500 a company that has like 500 um Partners um but other times you just so Twitter helps um uh blogs um just reading security mags magazines sometimes honestly I'm just I just Google I'm like I just Google recommended you know uh edrs and then I just skim through the bazillion articles that I get back and what you know in in today's world sometimes I have to go okay if it shows up on eight lists that
are semi-independent because you got to be careful of sources but if they show up on eight send my independent lists then okay that I'm going to say that they're probably okay and then I start narrowing it down so it takes a lot of that um kind of digging in and sometimes it's a just-in-time thing because your company says oh we need you know we need an xdr and you're like I've never heard of this thing and so now you're quickly doing research on that so part of it is knowing how to do research and gather information in a very time efficient manner so I didn't put that in there but research is definitely a something I do
a lot uh I I'd add to that uh product evaluation I know uh I'd add to that product evaluations and uh and making sure that like if you're really strong in one product uh that you can compare the capabilities and and inaccuracies of that product with the other ones to see if you can determine that so doing product evaluations is because a lot of times a lot of vendors will allow you to try something out for free or whatever and you you can definitely uh do that so uh the other thing I would recommend also uh look at the certifications such as uh I forget it's like the JD Power Associates of cyber security products or
whatever there's some standards out there you know Gartner and things like that that can can also help you with your research with that but but definitely those those kinds of things of like I said keeping abreast of what's on in social media what's going on in technology yeah coming to cons looking at who's talking about and things like that that that's how that that's a good way of doing that as well one one last one last one I think one last question get a free Coke can of Starlight Coke Starlight that that stuff is good it's really good well awesome well thank you again thank you for enduring 58 minutes of talk yeah thank you
yes and they were given to us by Heidi I'm like I am so stuck that better be on the recording but I haven't really found those where's my mouse limited edition yeah we could get the uh