Tracking Down the Rogue Node

Show original YouTube description
Show transcript [en]
yo hello what up when you hear me not hear me sorry my throat's messed up had a 8 pack some more rolls last night so it's really tough on my chest plate okay first of all I just want to say everyone thanks for being here I actually helped partly very miniscule II helped organize this besides so thank everyone for being here so that's super cool which the goal of all this is to help bring Oklahoma up to speed on security research recon Incident Response forensics that's what we want to do obviously it's cool you guys got our shirts and that's that's what we're trying to do silicon Prairie so I want you guys to spread that around we're
gonna make that a word in Oklahoma so I don't think we get recognized as much I travel around the world doing this stuff Incident Response and forensics and pin testing and stuff I don't we do have some good talent here so I want to say thanks to everyone being here thanks for coming and thanks to the sponsors for giving everyone free admission free shirts and free beer right right on thank you cool anyway I'm Donovan Farrow I'll just be quick people was just this guy with the crappy voice talkin s I have a background in information security information it's a response digital forensics all that cool stuff I've been an IT quote IT whatever you
would call it 18 years have worked over 700 cases certified as a forensic examiner by the state of Oklahoma and the federal court so I've been in court as an expert on these subjects worked over 80 Incident Response engagements all over the world you know to say jump out of the helicopter and the black parachute and all that cool stuff right so it's fun I like it this presentation I just kind of wonder for we jump into it had a couple people that missed the class I was able to get a class so thank you everyone for attending that I really appreciate it hope you guys definitely got your money's worth out of it few people about four or five people
approached me and asked if I could you know which they could take the class so I pulled a lip a little bit of content from that and put this in this in the presentation and I also wanted because forensics and incident response is not only a cool buzzword you can be like yeah man it's a response forensics right it sounds really cool in a resume but I wanted you guys to actually get some tools you could use in your house in your company for free that way you don't have to buy the like cool net witness or or you know ftk or in case or some other cool on the wire tool you can collect
peek apps and do that analysis so there may be a little below some people but again I try to try to go as heavy and as and as soft as I can because I'm actually here to teach you guys something and I hope you guys get something out of it so before I've again any questions comments concerns no one raises their hand we're doing an IT presentation that's okay all right I'm gonna kick it off all right so first thing is understanding the hack so if you guys maybe you can't I'm probably gonna walk over here a lot and if you're ok with that I don't want to neglect you you guys good all right
oh you want I get multiple distance got it I'm gonna step over here I'm a walker so not a walker like walking dead but Walker right I walk in talk I can't help so away I can sing so we got here understanding the hack so so this is a I guess I should tell what the hell we were doing here tracking down the rogue node why is it called a rogue node for multiple reasons first of all it sounds cool so if you guys like holy Road no that sounds legit he's even got zeros in like this - oh that must be super legit this is cool I'm ready ready for the presidency Isley right that's right so what it is is so
the rogue node is a an asset inside your business in your company and that is causing disruption and I want to take it from the top in forensics we're going to go far right as hey we need to do a legal thing we take those machines causing some trouble or this part we got an insider threat next step we're gonna talk about hey we have malware on the machine and we need to handle it or three we need to see what this guy's doing because we think he's you know looking at pornography or doing weird stuff at work he shouldn't be and how do you respond to that from an incident response standard we're gonna talk about
cut called traditional or cold forensics right so that's sure we call them quote/unquote old-school dead box then we're going to talk about live like okay done and that's cool that you have this image I'm glad you have the time to do that but we needed to be a little quicker so we're gonna go over some tools that you guys can download for free that you guys can have in your arsenal that are super easy and CLI people are gonna hate me the GUI people will love me so I goo for you alright so what is a hack what does the hell's that even mean we gotta understand what a hacking is so first thing I talked about
insider threat what can someone get from an insider threat when you get into an engagement I always say there's this thing in my classes as knows about this is what I preach is pre discovery and again I don't know if that's a real word that is invented but I just invented the other day from my class that night again Marlboro Reds beer pre discovery was the term I came up with before you jump in an engagement you need to know what you're getting in I'll give you the prime example someone says hey man we got some some email I've got some malware rockin an email that's cool it's let's go get it so you're gonna get your
tool bag and you're gonna you're gonna jump in there and get the email what you didn't know is that you you got the guy's email that was infected right because you went to his inbox because he's the guy that was crying the loudest because he's the CEO he's like I got this malware on my machine so you immediately run over to his machine you start collecting well well you didn't actually think the pre discovery of it was what well do you have exchanges it was a 365 what is it archived when the email comes in does it split just because you're talking to this guy who's quote-unquote more important to the business there could be 50 other people
infected just because you respond to the user which they never lie when they make tickets with the helpdesk right that's what you're responding to right and from an natural progression as humans as we are we're we naturally respond we run after stuff we're like hey man someone's hurt I need to fix them so I would say it's kind of like when you guys respond to an incident is you have a big fire so here's there's there's a big fire in the window you guys see it super big fire and not really but imagine there's a fire right here and you guys are firefighters because you guys respond you're all incident responders what you do see our firefighters by the way shout
out to a firefighter here so you're going to knock out this fire in the window because you're going to respond all right good job okay well what you didn't know is it's actually the whole buildings on fire so even though you cleaned that email from that one guy you got just the whole botnet just infecting your whole environment but you got that one guy clean and he's like man thanks guy IT guy you fixed me and then you go back to your desk and then someone's like hey I've also been infected as well and then the guy that you just fixed says hey I'm infected again because you didn't actually figure out what the root cause
was you didn't rediscover the incident does that make sense alright from that we're talking about insider threat insider threat would be you guys so looking at all of your faces I'm scanning all of you I'm looking to see your faces are for need to come investigate this guy specially insider threat could be you could be co-workers could be the director I'll tell you a lot of them are CFOs we do it all the time chief financial officer M oh and he why right what if you in charge all the money for the company you don't know where it's going coming in going out one guy does and you know he's typically the guy that we get investigated besides IT
people so that's why people hack all right talking about hacking talking about a rogue node and when I say no do you guys to probably think a device right well it's any entity a node I would consider a human a node a lot of people don't we can get an argument about it later over some beers over there that's cool I would say that a human is also a node because do you or do you not have to monitor the humans inside your environment yes why because they break stuff all the time and they're the most vulnerable and if you don't do vulnerability scans on humans then you're in big trouble sorry I get a drink of water mmm
all right so so here's what we got so so we got the insider threat because we do consider a human as a node because they will disrupt and they can cause trouble typically it's who it is right from a user perspective you have to investigate them see what's going on intellectual property theft intellectual property theft obviously is anything that you have I was checking my timer here anything that you have that is your golden egg right so if you're a company and you sell blueprints to roads I'll give you an example so we had a company that sold blueprints to roads and just as a hat tip I was like hey man all your stuff is on show Dan anyone know what
that is and I'm just idling up so show Dan is a you know a lot of people I see a lot of people share it's it's a website you can go on and you can pay the premium membership of $12.99 a month and get some decent intel we use their robots whatever something they're surfing just for lulz trying to see it what for ethical purpose so just see who's cameras on right at the Cincinnati you know college weird crazy stuff anyway so I said I'm a polite email and they probably thought I was an ambulance chaser but I was like hey man all your stuffs out there in a database just just say no I mean you know I'm not
I'm not just letting you know it was Oklahoma business right because I'm trying to make sure your Oklahoma secure they never responded anyway they finally took it down after two months not my problem so intellectual property theft not only from them being exposed right because you could take that and say the hacker even though the the person who set that up may not be the the hacker would you guys not consider that a hack did a hack not occur they didn't use any cool tools they literally went and downloaded database for free and did the connector was like holy crap was just default log and how do I get all this data right I know that's that's remedial and it's
tiny and there was no quote/unquote skill I know we're at b-sides but for someone to go that far they hooked it up is that nuts they're still considered a hack right that makes sense everyone agreeing with me good hope so well I'm getting 12 if you don't anyway credit card data PCI Bank stuff I mean it is what it is right so credit card theft you could have we had a financial institution that we had an insider threat so I'll kind of paint this picture because really guys I want you guys to get a wrap around understanding the hack because before we go into the tools you're not you can't relate it if I tell you the tools and I don't give
you situations you won't know how to utilize those in your environment okay so I do jump around so I apologize work the case where we had a a financial institution that was being compromised because we discovered some account information on the dark web that we purchased for $20 it was awesome thank you 20 bucks and we brought it to the clients attention we were doing a Content response on these guys doing some activity for them and we said hey we found this account information they're like holy crap that is legit what happened so we then popped into into the response right because everything is related you guys kind of see how that's all kind of tied together
we had to jump in incident response and we had discovered this lady was actually leaking this information she was stealing it to a USB stick that was on her keychain nothing too crazy and everyone's like we're I'm so smart cuz all I do is I disabled all the USB ports it's that for the one that's behind the keyboard because you need a keyboard to work and then it gives full access to the machine so NT so we're able to figure out that she was actually trading data this way from the investigation we figured out that she was in a court case a divorce case where there was a kid involved someone had stole her iCloud
account and found nude photos and a couple other nefarious items and was going to share that with the opposing side in the case and then they said if you don't we're going to expose this and you're going to lose custody your child or or for free you can get us those credit card information they count information anyway so not only was that blackmail not only was that quote hacking and they also sold it as well so kind of giving you guys the full picture of a obviously intellectual property theft that's even some bank information and insider threat pretty complicated right all overlaps medical information medical data it's I don't even know why I mean I can I can
speculate politically while we went that way but if you really want to protect medical files don't put it in electronic format so good for you guys and for us is that we all know have jobs because people think that that's the best way to go right so I'll get refrigerators you know video cameras it's the way to go it's the coolest it's the safest thing the public embarrassment man that one's totally cool so work in cases where someone gets hacked you know compromised like no website and I'll go back and beat up on Sony because everyone beats up on Sony yeah right so so so by the way my own professional opinion that wasn't the Koreans that's a side note
but what they did is they were taking the the CEO and pitchers I wish I had him they were putting him like in a meme like he with a whole bunch of like devils and hell it was crazy man and then they got back in because I took system access and they put skull and bones on everyone's computers when they got in right and not just the IT guys but imagine like the finance people you know the attorneys everyone's just freaking out because what the ultimate goal was public embarrassment right right I mean that's what we were talking about why are where do people hack what are the motives also political reasons I'll give you this one and this is not a
pro or a against I thought this was actually kind of neat this actually wasn't even a hack but it could again it kind of Lading so what happened was Jeb Bush was running for for presidency and Donald Trump bought Jeb Bush 2016 calm which cuz he didn't expire during the campaign if you get so he was running his website Jeb Bush 2016 and that moment it expired Trump's team bought that and then it was a trump website okay and that's not necessarily a hack it's called and get your together don't bang guy right so again what is the reason for it why do people do this I'm expanding the idea of what a hacker is I want you guys to realize that I
know we're at DEFCON we talk a lot about hackers and I know you guys don't all work for you know a company that all we do is pin testing and Incident Response I know you guys do all we do networking we do ad we also do antivirus you I'm trying to put it in your world to make it more realistic for you and you guys take something back home and then my favorite for the lols see it's like ooh Bert's for the lulz y whole bunch of hacker groups like the guys that took down the poodle Corp big one the other guys they've been arrested now that took down at that ruined Christmas for so many
children across the United States took down was the Xbox Live I remember you what was it was Xbox Live yeah yeah I mean we're talking about we were cracking up anyway yeah ruined Christmas for everybody the biggest Grinch ever lizard squad hilarious and the funny part was I gave him a shout-out on our Twitter just like oh man loser squad does it again and then they retweet and was like thanks and I was like oh how dare they know I exist delete the account run away but see again you got it all so you know what's the purpose that was pretty cool it terrified to death at the same time it going the opposite direction so I'm
gonna take this another direction I thought that's always kind of funny I always make fun of people that have forensics so this is the Internet in case you guys didn't know so he put the new virtual goggles on and you plug into the internet that's what you see just run across your face fingerprints and all that stuff so I'm gonna change it up just a bit and get a drink of water let you guys absorb this before we kick on the rest of presentation here we go you guys ready he's the Triforce
because they here is this over at 40 after hey you're good I'm gonna keep talking let me know let me know cuz I don't know all right what does that mean Donovan you got cartoons now video games the best video game right ever you guys like I put a gif in here who doesn't watch people use gifts more oh my god it's the coolest thing ever so use the Triforce Triforce to me I tried to figure out how to bring it to home everyone could understand right so what is the Triforce yes sir 4:40 what did the Triforce so I try to think of a methodology people could remember because everyone's going to remember Zelda and the Triforce after we
leave here and you're gonna have a methodology in your head that I made up from a cool ass video game many moons ago so we're gonna talk about digital forensics okay we're going to talk about when I mean its computer we're talking about hard drives next we're gonna talk about memory okay talking about memory forensics that's the next frontier right once after that anyone anyone guess if anyone can guess it I'll give you a challenge coin after this network forensics winner winner challenge coin dinner networks right because you have to manage it all you have computer hard drives you have a memory you have networking and then the next frontier is I don't know hopefully you guys figure
out before I do moving along oh there our way all right beau what is the methodology we're going to first talk about methodology a live transaction so what is a live transaction a live transaction is you engaging a client that you need to take care of right now okay you don't have time for traditional forensics and I mean like getting a forensic image and then sitting there and watching it tick for 500 hours and then after you get that physical hard drive you walk all the way over the lab like this and you set this big-ass hard drive on this guy's table and then you plug it in and then you load it and then you say yes I
want to index a dummy yes I want deleted files dummy he has somewhat bookmarks and then you click process and then you walk all the way over here and then you wait for it's done right that's that's traditional forensics and I'm not beating that up I don't know if anyone's ever done that that is painful if you're doing an investigation awesome but painful so I was trying to think we do live forensics we have an insider threat that needs to be conducted right now we don't have time to worry about anything when you figure out what this person was doing what they were touching where they were going what they access and who they were
talking to okay Incident Response and that's the whole mentality right Incident Response we got to be a little more agile because these two family groups do overlay each other forensics is the parent IR is also the child of that because they're all related then you go down the security road boom alright try four shard one hard drive forensics and this is from some of the class that I had so what happened here so I use this tool called browser history viewer and you'll be like those stupid Donavan okay well let me first say that it is free F REE and it's called a browser history viewer Explorer and it's free and this would be on a live forensics part okay we're
doing live forensics super easy super gooey you're welcome all my windows fans and you're gonna go click click and you're gonna go and you're gonna see what the last files I someone accessed how cool is that and you're like well done if I can go to recent yeah you can but can you print a report from recent you know take pictures you gonna use it your camera phone or you could say go back to your boss and say hey boss I used this tool that Donovan this forensic guy I guess it at the baby Def Con told me to use he said it was legit and I was able to print a report from it or are you gonna
say hey man I looked in his recent quick agile fast right cuz we need to know if this guy right here has been in Bad's been touching the finance folder because guess what he put it as he put it in his two weeks two weeks ago he's out the door he's ready to go he's accessing data he had access to the financials never touched it matter of fact you did you did traditional forensics you didn't find it cuz of what does it wasn't on the machine cuz where did he access that file the network because if it's not on the drive you can't find it right it's and there's no file there's no action right
it's a quick way to figure out what was in recent basically right pretty cool makes sense next one is browser history a viewer and again I'm trying this super easy for everybody you guys may know about this but um please just hang tight obviously this guy besides he's a fan somehow you can see what they access real fast not only was it the files but it is also the browser this will have a hook hook in for Chrome Firefox ie lolz and then I think Safari so you guys can just really click it and go so whatever broads are using if they're always using Safari and then magically they use Chrome in private browser because it's
super private it'll come up here not too private ok so kind of putting this in context is even from an incident response let's say now the insider threat let's say that you have a machine that keeps getting infected and your proxy guy is just super annoying and he's on vacation and his stuff is broke and you're tired of talking to him because you hate blue coat or whatever blue choke so you can literally go to this machine real quick and figure out what the last websites there were because you can find some malware websites right here would that be cool get a malware website because it's gonna be whole bunch of garbage you know what I mean real quick I'm talking
within like 15 minutes while I have to put in a ticket and go away some friggin time going through the system when you're in an incident response engagement go where the two computer guys that are stuck in a closet act like you can't get up on your feet okay go over to the user you're on this tool and you have all the data you need right there okay it's not gonna recover everything but guess what it's better than nothing right you guys like that is that good digging that okay cool next one is last activity viewer this is my favorite and I'll put it to a case to know my in my class classmates were they
like this one as well so anyone know what this is I'll just throw it out there it's kind of funny the class people don't answer do we have any pin testers in here take that as a no oh we have one who is that
it is what do you know what that program is though sorry the one in orange I got shaking hands huh hit this alright now if you ran that so I did this in literally like five minutes and you ran this real quick and you're scrolling down would you be like holy that's important you know quick agile right if you know the executables and if you don't there's this thing that we use it's called Google take that Firefox Exe drop in there and click the enter key on your keyboard like that and it will run oh it's a big ass database it's free also you can run and you can get this information okay and it'll tell you what
it is and I would not be I mean silly but I want you guys did it's comical until you don't do it and then I tell you you're like I should use Google man alright and then the next thing is is it's my favorite over here you guys what the hell is this someone connected to a Wi-Fi connection disconnected FBI surveillance van very important very scary I'm sure the FBI is watching which they are but that's okay well seven okay so FBI surveillance van how would you correlate that I'll give you a case let's say some person saying that hey no I was I was working at home the whole time you guys are trying to
say that that I mountain about HR says go get his machine and see where the hell he was at and then you pull it up here and it's like man Starbucks store number 12 44 right you guys know they label it that way then go into google and type into Starbucks store 44 and you're like well hell that was an Albuquerque wasn't Oklahoma but we have him connecting doesn't matter how long he was or was not connected but we have evidence of that how fast is that right super fast right okay moving along so this is just this is me showing you the report you can literally go file report and you can put in there I think HTML
XML format so that way you can be like look boss here's paper I know you understand paper right they like paper and if you get really cool you should make like a chart with bright colors and be like see boss see this red here that's bad guilty right pie charts graphs alright moving USB connection this is one of my favorite ones for data exfiltration insider threat rogue node so here's what we got going so we have a rogue node we have someone coming in I'll give you a case we had a case someone plugs in said hey I think this guy stole data from my computer ok I know my team my team and my classmates
know this one okay so they plugged in a USB and they took my data and they come to you IT guy I think they stole my data you're like okay how yeah I don't know I just know that they did you're like okay but why they're like I don't know you were just talking he just just he stole it I just know it you're like oh man so going back to the original slide if someone did steal something and they weren't you got to know who your the person is they're alleging right what is their cognate what is their at what is their knowledge to IT okay three different ways I'll give you a real quick email cloud solutions or USBs
okay so you're like me I'm just gonna go that use this cool tool that Donovan told me to use us connection activity foe free and I'm gonna run it and we had a case I'll use it on I ran it right here and found this cool serial number that is identical as identified for each USB stick do you guys see this created date right here in the middle that is the first time that USB stick was plugged into that device how cool is that right last plugged in okay that means last time it was plugged out might be important so if you have a new device that was plugged in today first time ever and then it was unplugged when I
said stuff could have been stolen would that not be an indicator of exfiltration right so then we did the investigation we had enough evidence on our side that again we're talking attorney side we went to the we went to our attorney and said hey attorney guess what got him we need to send a subpoena for this guy's machine and he's like come on bring it on so we had we had a legal force to go in there and seize all his electronic devices which actually I guess wasn't his laptop which was which at the time was totally cool we didn't we didn't seize it so because he said that was outside the scope I was like okay we
can't get your lap oh you know let's have the computer either we were totally hosed up what do you would do at that point you guys know we didn't have anything else so guess what I did I was like well we have rights to this so I was like going in his drawers Hey look there's USBs dick hey man look at this external hard drive so I started collecting all the external USB devices brought it to my lab and ran this little bad boy plugged it in and hey you have the exact same serial number that she said you had that was that you stole stuff it's weird that the USB stick I found at your house was the same one
plugged in at her machine at work khatim right owned right there you guys hear that so make sense cool there's people to get a real drunk back there and dropping bottles whoa thanks for coming yes sir so a rubber ducky actually will show up it will give me the serial number because it still works it works as a USB but you have to understand the driver it won't have it'll have this USB input device it'll come up as a keyboard and you'll be like oh I don't recognize that until you start running these serial numbers and then the makers you have to dig a little deeper to realize it's a ducky and I haven't found a duck
in the environment maybe I'll just suck but I use it myself but typically you know we just haven't gone that far I mean it's I mean you kind of go down the road anyway moving along good question rubber ducky I love it this is the one hard drive forensic still we're still in a hurry the hell up so traditional forensics a sleuth kit this is autopsy and and that's what I mean you take so what you do you have your hard drive this is steel we're doing we're doing cold forensics now we kind of moved on I just kind of skip so we're doing this is traditional forensics free tool autopsy we're gonna kind of speed up okay
free so when you do a forensic image and if you don't know how to do a forensic image there's this cool class called digital forensic essentials teach by this guy should come do that you can literally take this computer just this program and point it to the drive image and it'll start carving all this stuff boom boom boom we got emails we got documents access times history image because when you get an investor they're gonna say hey man we need all the images off this computer because we think he's looking at porn you're like oh crap let's he has like a porn directory which we've seen super secret it wasn't Pio Arion it was pr0n very suspicious so so
this is a quick way is what I'm saying you guys have this big noise a big dirty big dirt is the problem you have this big hard drive terabyte hard drive how do you find photos on that oh my god that's crazy right use this cool little tool use that flow free okay can I go the next step we're talking about this is a Linux old mother I should say this is a Windows tool so I'm trying to let everyone have their cool thing so part of the sift kit which is a sans tool I don't actually use the sift kit no offense to the sans team it's a good product but I do use
this tool called law to timeline the next question is Donovan is all this data we're drowning in terabytes terabytes of data we need to know what this idiot was doing on 1010 16 I'm like I don't I don't know you're gonna like load up all the day you're just gonna scroll through photos and email and activity and last access and doula check bust you can it'll take a long time or you could run this bad boy right here it's called log to Timeline this is a Linux this runs on Linux or Linux tole this is fo free it's the greatest thing ever figure out install times if and when an item was installed if it was
deleted this does a true transaction step by step of each thing that transpired on that machine and you're like but Donovan's deleted deleted like well it's it still has to have a command to call deleted deleted right and then your next thing is well Donovan you do forensics what if they deleted the deletion tool and they wiped it I'd be like well they still had to delete the delete tool right right still in action you can't delete the deletion tool that you deleted because you don't have anything to delete it with because you deleted it that confuse everyone but does it make sense right there's always a transaction for everything you do on a machine check us out so time stamps okay
red is bad all right Green is good this is literally an Excel spreadsheet that is pumped out and you can highlight what is the known good what is the known bad because right here we have sorry we have an Excel spreadsheet gone gone rogue right take a look at that okay this is all related okay should should the excel be executing this should Excel take C be executing win service host exe maybe probably not so what I'm looking at the very top is when it was created on the machine when it was put on the machine the second part is that running something outside of Excel and obviously we're looking at a base and say hey Donovan we think we
got infected this morning can you please figure out what happened this morning okay I'm not just gonna typically find evil on a whole hard drive next thing so that was shard 1 we're gonna have to go really fast I get 9 minutes short to memory forensics ok so what is memory if you don't know it sits in your brain and you collect it we're gonna we're gonna parse through it ok obviously memory is what's in your machine it also holds execute all transaction that's going across the machine don't think of it from a file aspect think of it from a running in memory ok so traditional forensics would not catch it because it's not in the hard drive and it does
not typically create a file ok these are some cool tools that comes with volatility piece can dll dump CMD we're gonna go through all that doesn't matter so this guy look at he's happy I'm happy alright we're gonna look at piece gain what does piece can do this is one of my favorite ones so P scan shows you all terminated processes and you're like Donovan no one cares about people closing out terminated processes if you had an infected machine and you couldn't figure out how it was getting affected if it keeps putting writing in self to memory and deleting itself writing itself to memory and deleting itself how would you find that you'd use volatility
is the answer okay also net scan one of my favorite ones let you know TCP listeners endpoints UDP lets you know who's listening on that machine this is from memory a collection okay you can see some Network listeners and that cool a dll dump and I typically what I say and you guys this is just the way I do it again it's an art you figure out there's many tools you can use the way I do it you have a dll dump you think you have an infected dll dump it out of memory literally dump it out of memory and then run some scans against it okay because some IVs won't catch stuff in memory but if they're a natural
file right you actually get to touch it and scan it right you're bringing it in you're touching the file now you're ripping it out of memory and you're analyzing it as if it was traditional forensics CMD scan this is also badass it lets you know the last commands that were in memory if someone used command prompt there's your list here's what was typed in the whole time from the last time the memory had been booted down or taken out of the machine that cool see what some knucklehead was typing in can't forgot why their networks causing problems cuz some dudes doing some testing well you be like look at your memory real quick bro it's okay Shh got
it you figure out the problem you got to calm them down Shh I'm gonna figure it out hi next one files can you figure out basically what it is I'll have you guys don't like to talk words read words while I get a drink
so it can even detect files that are remove when it's tied to a rootkit the hidden files how do you help it's a hidden file it's rootkit I don't know you can't find it well it'll be in memory has to run somewhere right cool cons can also probably my most favorite ever con scan what IPS addresses was this machine connecting to at that time when memory was running are these rogue ip's I don't know go to google drop them all in there what is this touching what is this tied to right he'll be whole bunch of Akamai Amazon all that cool stuff but maybe it's not maybe you'll have one and say hey dude that's
a total threat I recognize that that's a bad I P and again this is still pretty quick because we're not talking machines we're talking to eight gig 16 gig analysis and we figured out that this IP and need immediately needs to be blocked ASAP we also need to know what the threat intelligence behind it network miner cooee again you're welcome pcaps ok we're talking about networking now packet captures if you're super bored and as you should be after this conference go home do a peek app on your neighbor's wireless that is totally open to you and they told you you could use it okay alright do a pcap drop it in network mine or let it process okay dns
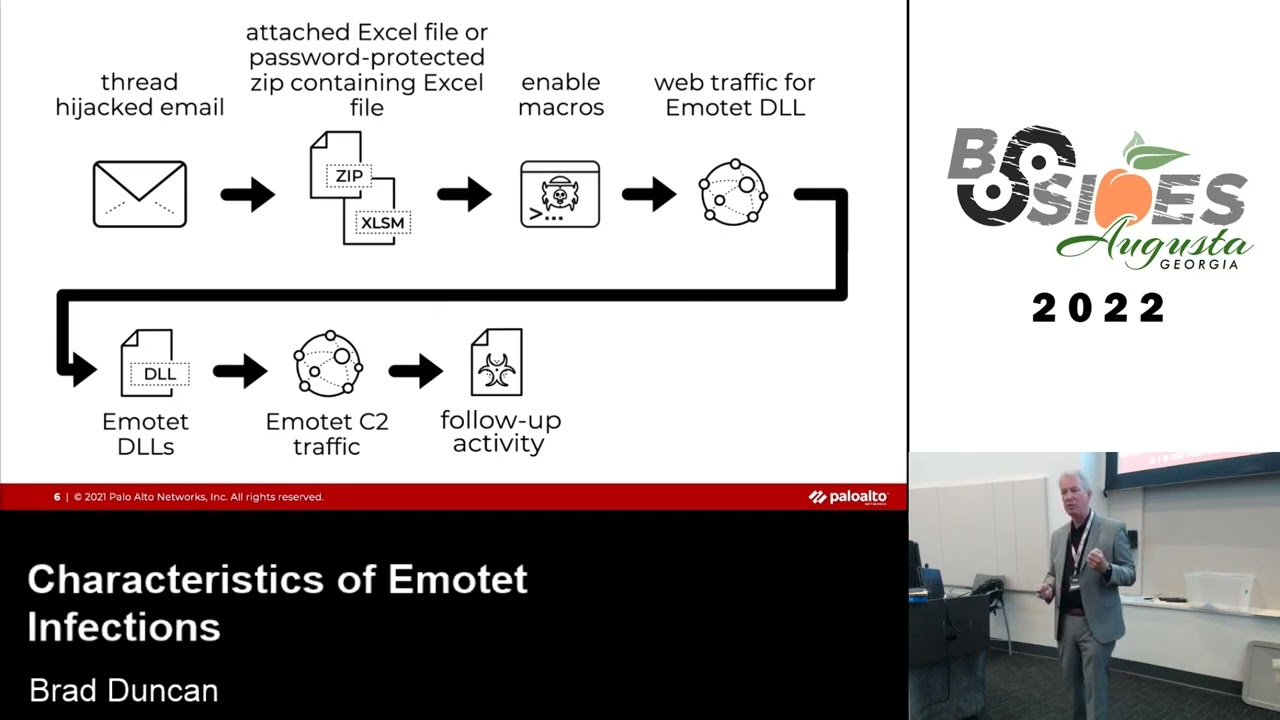
white listening browser connections is a tied to malware it could be command and control which is one of my favorites you're getting to tell the actions are how it works in there is there a lot of sessions i'll give you a quick little scope here so everyone's like commander controllers that we got malware malware is typically loud generic malware right command and control a secret so when you have this I'm gonna say here's my malware and then down here is my command and control okay so we look at data flip it upside down and we're gonna look at connections and see who's not the loudest but who's saying hey hey hey hey right talking about command and control
we're gonna see who's not the loudest we're making the most noise who's actually making those initial conversion tick tick right pitchers see pitchers pitchers good else you can also capture images which is pretty cool on the wire you can tap capture all the type of clear text and if you capture clear text that's their own fault because we are past that and you can also get emails so be careful okay okay now your environment setup and your policies are set up but or just don't tell anybody because you did it your house but you didn't explica so what does xsplit co also runs in Linux my big problem with is is is how to find
what's happening who's talking to what I always try to diagram it for for bosses because they like pictures okay it also kind of does stuff is the his network miner has a geo map which I love to death email pages IRC sessions oh my god it's so good does void SFTP has all this analyzing this cool little interface right here this is a terrible example but you can do a peek app load it in this bad boy right here all this stuff is filled up and look you have a connection to China share your boss like look boss we have a connection to China here's a piece of paper I made it red so you know that it would
be bad okay and this email interface is better I just like this one better the other one does it but this one's almost I say a little outlook non sound look it's just better it just looks better you can look at subjects it filters it better so I'm highly working to exploit go for that okay okay three takeaways I want to bring this perfectly free takeaways for the finding hackers hard drive analysis logged a timeline big fan of that the other tools that I said as well okay volatility memory forensics and then network forensics for Network minor and explique oh now we talked about the three Triforce okay again Triforce one hard drive Triforce to memory Triforce
three is networking and those are the worlds that you need to work in so that you can take better your company also find attackers insider threat rogue nodes and the thank you guys yeah seriously thanks thank you guys for coming to beat sides it's great you guys made it very successful this year and please come back next year thank you