Purple Team: How This Color Can Help You And Your Organisation Learn and Get Better
Show original YouTube description
Show transcript [en]
hi everyone off you're having a good besides so alright so just starting to present to a my Patrick Matthew I'm co-founder of access it's a conference in Quebec Canada I've been doing fantastic and consulting for around eight years I'm correctly working at Sookie compass in Toronto I've been into hiking since around 97 join this on like before internet VBS and those kind of things and found those texts about aking and never stop so um i i've talked at Derby come last year did the demo labs about the tool I did and I'm doing a black at Arsenal also this week so if you go to black hat you can join me there my Twitter and info is there so we're going
to talk about purple team what is my experience about purple team officially I've done like I said around eight years of consulting and it was mostly staff hugs inside government and huge aid agencies insurance those kind of companies and I did around ten years at the same time of pen testing so I said about both side the red side and the blue side a lot of there are those races was like I said government banks insurance and at current employer right now I create the services about the purple team so I I also lead well I create the service I lead and create two major purple team exercise which are usually one to two months exercise pen
tests and what I saw so by doing all those experience and all staff hugs inside government I saw so many things that were wrong and that's why I came out and do the talks there was so many organization that was no sock there were no a narc most of the security inside the organization was like just governance so people writing rules of what to do but nobody putting them technically or just analyze the circuit edge and really or personal people so not a lot of technical and aking or even incident response and even like one of the best government I saw in Quebec down there was the logs that were having millions of those they were not even filtering
them it was like terrible blue team so that's why we need to talk about purple team just quick like this I can people raise your hand if you're inside the blue team right now awesome anyone in red team cool too so hope I can help you guys so white talk again about purple team it's kind of a subject that come around in the last few years a lot of people online even Publix or others are talking about this but when we see what people talk about they don't cover it out or usually it's I don't find it properly so we need first a lot more talk a lot more defensive research and talk inside conference people focusing
on everything defense we're a lot into offense most of the conference and research is done inside finding issues instead of fixing them or finding ways to fix them we need to have the red team to help the blue team is not just about people going against an organization destroying everything and giving a report and run it's really to elf and I mean the red and the blue are supposed to work together they have the same role which is making the organization better and more safe purple team services shanell organization made sure and grow faster it's really a game-changer
so when I was doing like from pen tests to a major or purple team effort most most organization that we talked about those kind of service that we're looking for red team and when we explain what we can do with the purple team with the mentoring and everything will change ideas so it's really a good game changer also it's two out the blue team against red and because defense need like I said a lot of love there's red and blue I have the same objective not the same approach one is to attack when should be to defend and both sides should talk together they should mentor L grow and challenge itself so it's not just about
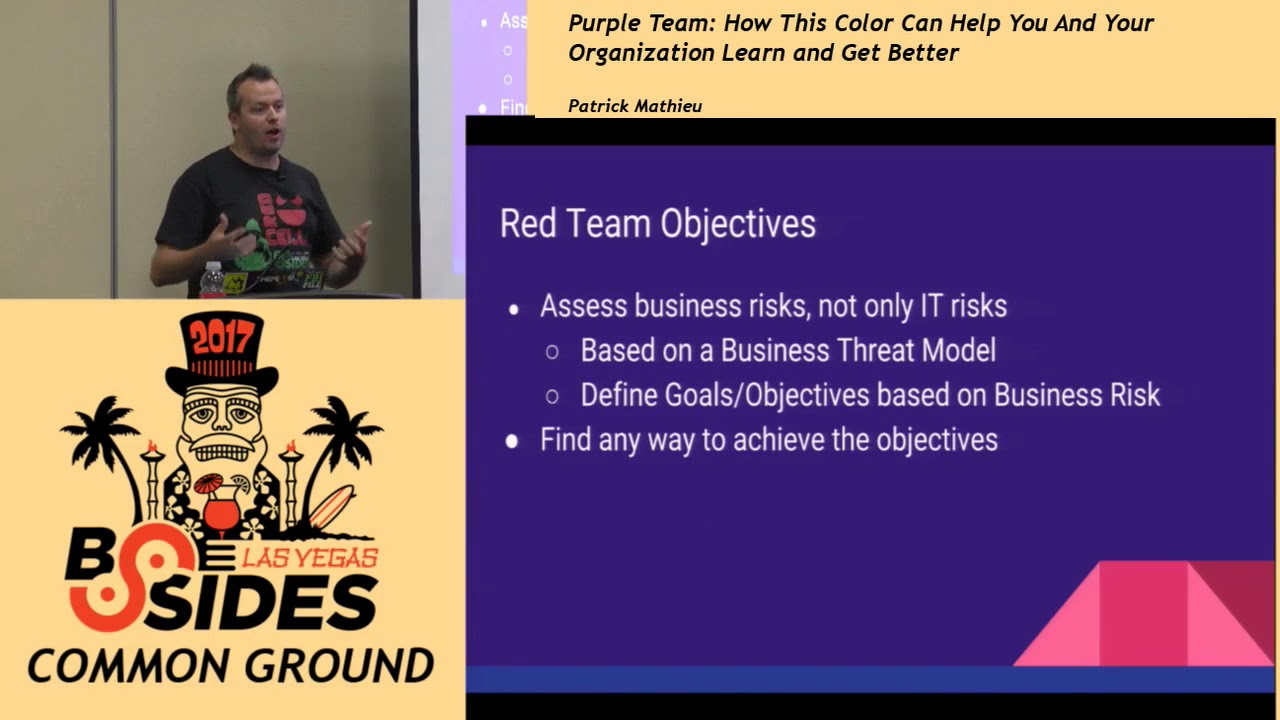
doing a pen test and finding issues and you will see the more details I will show afterwards but it's really purple things should really be an experience where both side grows and talked together to enforce security and the most important when we talk often about red team organization or kind of scared of it because it costs a lot of money like I said like a two months exercise could cost a lot when we talk about council think it could reach 100 to 200 K but there's a way to do purple team for small organization they're really cheap costs and that can help everyone so so if we go back at what a red team should be what it is it's to access the
business so the main thing you need to know is that a pen test will test against IT risk you will find technical issues a red team in a purple team is going to assess a business risk so it's based on a trademark it needs to define goals and objective based on those risks and the red team will go against the risk that were found based on the tread models so if inside an organization the main risk is the client list we don't care about testing the exact application or a specific web server we find we want to find ways to reach this list and any ways to achieve this goal so this is what really the red team should be about
it's a nose codebase so when we do an intrusion tests we want to do here's a list of IP of web servers of application that you need to test a red team a purple team is a noscope so everything inside the scope is what you should not do so technically you can do anything except the nose code which usually is like do not destroy anything do not steal an asset like go inside this server room and leave with a server it's really to limit the damage that you could do red team is based on the tree domain so social physical and electronics IT so you want to use any of those domain to achieve your goal and
objective it helps find ways to breach an organization based on a risk so like I said the red team will find a way a path that was not known by the organization to achieve their goal the objective which is to assess the specific business risk any question ok all right purple team definition so what people already talked about what it's been discussed in different talks or a blog online is usually the purple team approach would be a technical exorcist that the red team will test a specific attack against the blue team the blue team will monitor it we'll try to find the red team attacking and then they will talk and try to improve the process for this exercise
there will be like a post-mortem discussion those kind of things oh sorry about that not supposed to happen okay whatever the sliders just not showing but the computer works okay so oh there you go okay so purple definition so what people talk about is really that it should be an exercise with more like a workshop type so people will do a small exercise and post-mortem afterwards when a complete purple team should be is really base like I said on the business risk so we want it to not only assess a technical side but the business risk and regardless of the risk of the department or anything related to this so how to get the business risk is there's
multiple ways so we can do the sweet see sweet interview so interviewing anyone related to the sea levels to gather information about what the risks are for any departments we can base ourselves on the existing trip model documentation that exists inside the organization or if nothing exists we can create a fit model exercise and find a business risk of the organization based on this we need to know what kind of system data room assets or even person that are at risk where are they why they are important how the asset is protected and which security misery exists or not and based on all the other information we can create a good trade model the advantage of this is that the earth the
exercise is targeted against valuable targets so it's not just to test something but it's to test something really important and the approach is in base attack it's really risk assessment so whatever the attack used by the red team it will be what we want well it will be the path that they will find to achieve their goal so the organization at the minimum must be mature and when I say this they should usually have a minimum budget of security they should know that they should invest in security a lot of organization are not even there yet so it's important to know it's interesting at least so they have a shock or blue team in place mentoring a
team that doesn't exist is not the best they to determine the level of maturity of the to do the purple addresses there's a lot of different exercise that exists a lot of levels so we can do smaller to really like a two month exercise so what it should really be it's a mentoring and learning exercise it's actively involve the blue team inside what the red team is doing each day each week daily it should the red team should describe what they have done how it works why it work and give their recommendation and what the blue team should do it's not just about giving a report it's really to sit with them and explain how it work and why and even
make them try if they if they want so it's really like a consulting service to everyone grow like this so the different kind of service or steps that exist the first one like I said is at red model so if the trade model doesn't exist you wanna at least do it by a real chat model exercise or the c-level suite interviews then you do the workshop so you can have an organization without a lot of money doing just predefined exercise that will test some specific attacks so specific scenario or specific objective without having to go for two months and then you have the full purple team where you will sit with the team you will assess all domains the blue
team is involved inside the communication they know everything and then you have the full red team where the blue team doesn't know anything and afterwards you see how they react and if it was good so you can go this way and each year six months or whatever you can review your security and see if you improve which is to leave what every organization should do a good purple team is based on communication so when the blue team is involved each day it will be daily weekly or monthly meeting it would be to discuss what the red team is what they've done like I said and now to remain the eight and you can even do like a retest so everything
is inside the process of the communication and you got the concept of the mentoring process so by when you do workshop it could be daily weekly when you do a more bigger purple exercise you want to usually not do it daily but after each scenario after each goal that have been achieved so if the red team is going after a client list for a week well after the week you sit down and verify what everything has been done what succeed what fell on both sides so even the red team can learn from what they missed or everything regarding this so meeting will cover that the subject covered by the meeting of the red team is what has been done how it was done
why it fell and white succeed so the FEL are also important because if the red team fells it means that the blue teams have done something good so they need to explain which attacks fell so the blue team will know what good security is there and which part are missing what recommendation on short or medium and long term and is there a retest that should be done or anything to confirm the fix on the blue team side on the other side on the blue team they need to verify what was the tech what is what kind of detection what process was involved who was involved other communication inside the team was and what is the outcome of it
same thing for recommendation same thing for Rita's but they will also have a few more step regarding lugs should the lab be analyzed what are the next step inside the recommendation so planning on on fixing things then when you have everything in place which like I know is could be something big because it's a cell about the management that needs to be involving this you can have the concept of gamification everything is in place for a purple team so your organization is also made sure you've done a few exercise and maybe a real purple team so the concept of gamification is really cool you do a game with the red and the blue and you see which one got the more
points after each exercise each goal or something like this when they gain access the gain points if they complete those scenario a same thing for the blue team but you have to keep in mind that it's something for the organization to grow so we don't want to like having a bad game here you don't want people to be mad at each other it's really just a learning curve so how to sell this to our management it's really from it's really to push the concept dye management so they know the concept that the purple team will bring business risks into account and not just the idea so it can assess any part of security of the organization the mentoring is really
good so they need to understand this part and the approach that this all those steps will make the organization grow regarding security so the level of purple team will be like I said the threat model workshop purple and red so they need to understand each step and then the upper management needs worry about the business risk and I not just the IT issue so we need to have someone inside the organization that gets speak to a management level and not just report the technical issue up so it really needs to have like a seesaw level of person and then everything will make sense so mentoring to identify the gaps in security and for employees and system
and yeah so we're running a bit out of time just a minute all right so last part was the use case so just to go quick about what we've done on our side it was 21.5 two months or purple team it's a organization of five hundred thousand employees financial second-place it's aware that they need to invest in security they know about it we've done a first round of workshops then with the year after we did the blue team with rebbe reb recon external lacking social and physical and it definitely helped on the workshop because we were able to test specific attacks inside the organization what the real attacker will do and we help we sit
with the the blue team and tell them what to do what recommendation and then they fix it the year after when we access all domain within that fie the risk we test all the domains and then we confirm even the known existing security issues that they know but they wasn't aware that people could do it maybe so that covers it thanks everyone here we don't have time for questions at this point but please track this speaker down and outside and ask him any questions you might have [Applause]





