Negotiating Compromise: How to Avoid Being Labeled a 'Chicken Little' While Promoting Better Security Decision Making
Show original YouTube description
Show transcript [en]
thanks everyone um I'm not usually used to the the mic here so um and I tend to my volume goes up as I talk so at any point I need to speak up or lower you know just somebody in the back give me a signal that way we can keep it comfortable for everyone so um welcome everyone uh today we're going to be talking about negotiating compromise um something I think is often missed when we're talking about infosec in general it's not something that's commonly taught when you're when you're going through a an academic course these are some of those kind of soft skills that uh I think is really important especially as we progress in cyber security uh so um
hopefully there'll be a little bit of something for everyone here uh to start off I'll do the obligatory who am I uh and then I always like to have a slide of why this matters why am I talking about this why should you care and then the classic who's this for then we'll talk about you know what's the easy part when it comes to communicating security posture and security needs to an organization or to senior leadership and then establish what the challenge is you know from there then we can start looking at some of the solutions what my aim here is is to actually bring in common negotiation tactics that that you probably have heard of in different Industries whether
it's you know putting an offer on a house or just other General negotiation tactics you see these sometimes in negotiating salaries or or other things the the idea is to use wellestablished principles and how we can apply them to cyber security because of the time I'm going to hit six Hot Topics then we'll go through some honorable mentions of some others that we probably won't have time for um then we'll go into some common pitfalls of just things that that naturally we kind of fall into as we progress usually in midal management having to speak to senior leaders um I'll go through my personal mantras that I have to repeatedly tell myself uh and then finally uh we'll end
it up on a really high note and talk about the chance of failure so who is this is a lot of words this is all to say I currently work in financial services and information assurance I handle second line control testing and I also run the Cyber threat Intel program uh for my company previously I spent 10 years in the Air Force where I worked for a red team and I also taught at the weapons school uh locally here at Nellis where I covered topics like vulnerability management patch management uh minor attack framework my favorite course was on social engineering and uh open source intelligence I have my bachelor's in computer science and I have a sec plus
certification I'm originally from Louisiana as you might be able to tell uh generally what I like to talk about is Game Theory and usually my talk center around strategic planning and strategic um operations so this is a little bit different from what I usually talk about more on that soft skill side and uh my LinkedIn and Twitter's here it's also at the end so the great disclaimer side so I want to start by really kind of setting the scene here the number one answer in any kind of you know cyber security infoset question is usually it depends right there is no clear black and white answer it's always dependent on an environment a budget this particular industry this
particular person this presentation is going to be no different if you're looking to find a slide that you disagree with nine times out of 10 I'll probably have at least one that you're like I'm not so sure about that and that's completely okay in fact it's encouraged the whole point of having this conversational talk on soft skills is that it's going to be opinion-based it's going to be based on my experience uh and your experience is going to be different the idea is I don't think that this is a topic that we talk enough about that we have open discussions about and I want to help facilitate by giving this presentation so if you say
no I tried that and it absolutely failed that's awesome I would love to hear it and I and I would encourage everyone for any kind of disagreements or agreements that you have that conversation let's let's talk about the different experiences that are out there and ways different ways that we've been able to problem solve and be successful or fail so that we can all kind of cross learn so that we can be more successful in general as an industry so why does this matter what I have found is going to conferences in the last couple of years and uh sitting around and just talking to people that's already established in the industry it's very interesting
because there's not usually a lot of talks on the mid management level so people that are have already been in for a couple years they've seen kind of The Good the Bad and the Ugly there's not always a lot of mentorship and that middle management before you're getting up to Senior Management so that's one thing that I really noticed the other is what I'm seeing right now in the industry is a lot of people getting Masters in cyber security without having a traditional maybe computer science or um other kind of technical Bachelors um in a lot of ways I compare it to the NBA of the 70s and ' 80s as kind of a top off that
gives you that extra Edge in whatever kind of field that you're going in cyber security has become that a little bit but it's a little against tradition usually your old security people were the people that were CIS admins 20 years ago they've gone through the trenches now they know from a security perspective exactly you know for that environment what works what doesn't work what makes sense we have a lot of senior educated people that are entry level on understanding how an i department works how it works within a business or company construct um and and so that is a big portion of why I think that this is important so we can kind of bridge some
of that Gap also in my opinion a highly successful cyber security professional is one that people want to come to you don't want to be that person that's like oh gosh I'm going to have to tell Vanessa that we just introduced 10,000 more vulnerabilities in our system and she is going to flip out in my opinion that doesn't make a super effective leader what you want is someone that you know is going to be cool headed about it as much as to be expected but be able to help you problem solve and to help you be successful not be the parent or the manager that's like you suck and so I think that understanding some of these principles
can help you do that and ultimately the goal is to make the business or the company or the Enterprise as a whole better so a lot of times when we're talking about negotiation it's me getting max value for myself but in this situation your end goal is actually to make sure that the Enterprise is as secure as possible given the challenges you're not always going to get what you want so sometimes when you're told no we need to figure out a way to still achieve those goals of reducing risk for the organization without maybe getting your awesome Gucci tool that you first presented and was told no you're not going to get that who's this presentation for it's
for everyone I mean honestly these are these are common enough skills that everyone can gain some sort of insight or purpose from this like I said before though that middle management that's first now it's time for me to help make decisions I'm not just on I'm not just doing the decisions that other people made it's it's now time for me to be able to help promote better decision making this is primarily the audience for that so the easy part finding things that are wrong with processes um I'm sure that plenty of people if youve if you worked in it you show up to a place anybody that tells you that they have a well-run IT department is either woful
ignorant or they're just absolutely lying to you so you don't run away like every it department is going to have that one Department maybe two departments maybe one team there's going to be something that they don't do great and maybe they don't even do well at all maybe they do terribly those are kind of easy to spot especially as somebody just walking in right fresh eyes you can immediately see definitely this is not how it's supposed to be um or and similar to that finding things to improve oh yeah yeah yeah this doesn't work quite right how about we do this or simply threats I work in threat intel if I want to to find threats
that's going to scare the company that I'm talking to I can find those and I could probably find those pretty easily so it's all about how you're presenting your message what is it that you want to do do you want to scare them do you want to have the fud fear uncertainty and doubt approach that's certainly a tactic to use some people do find success in that that's the easy part the Doom and Gloom is kind of the easy part right the challenge of course is having a solution and then being told it's how much don't we already have enough security tools out there didn't we just buy one like two years ago like why are
we buying another tool um why can't we just use what we already have we already have 10 tools you're telling me it can't do this one thing push back is going to happen it's a very natural piece of the process sometimes it's part of the defensive process but being able to explain why in a way that your audience understands so that you can be successful from a security posture perspective is is really where the goodness
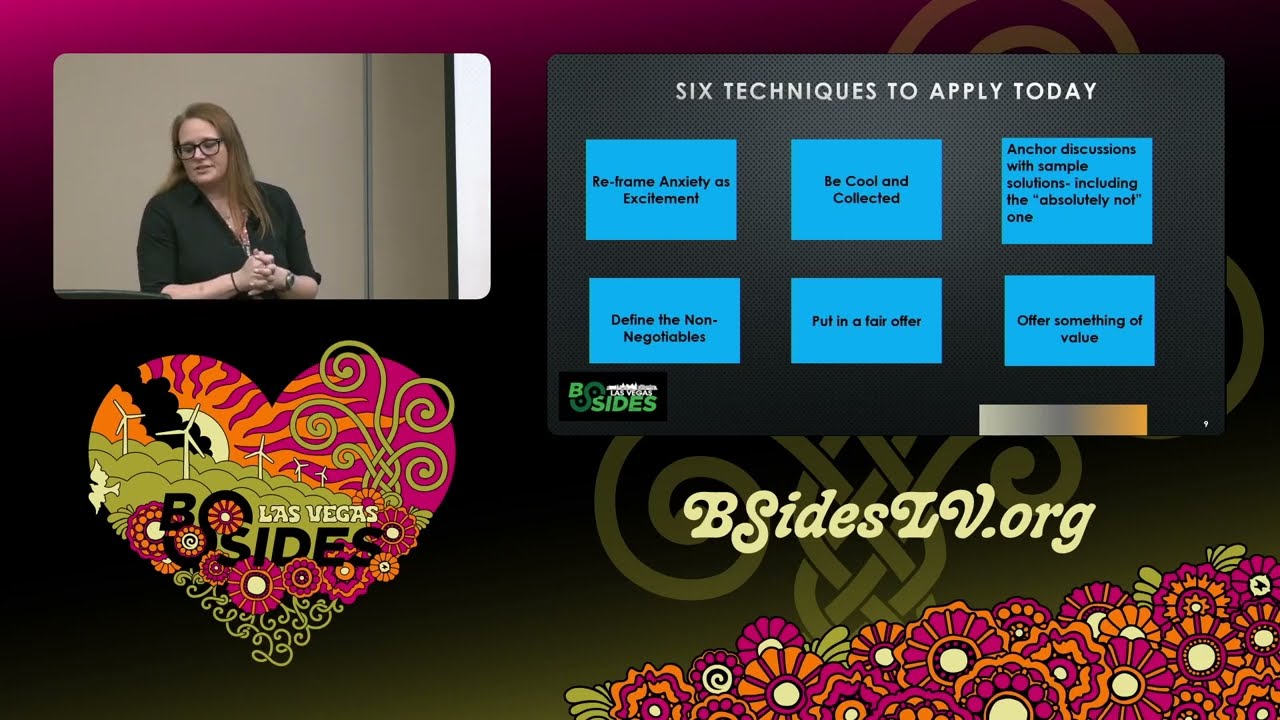
lies all right so here is the meat of the matter six techniques that I chose to talk with you today about um and we'll go through each and every one and kind of talk about them a bit uh like I said this is not groundbreaking this is not meant to be groundbreaking this is meant to be oh yes of course that makes sense hopefully if I've done my job right the first one being excited versus being anxious uh this one is near and dear to my heart because when I get excited I get loud my voice Rises people think that I'm yelling at them they think that I'm out of breath that I'm giving myself a heart attack because I'm
I'm going to talk really really fast but I'm just excited sometimes I'm just passionate about the subject but if you go through yelling at the top of your lungs and looking like that you're angry that is going to possibly hurt you when it comes to you trying to actually promote good decision- making depending on what solution you're choosing so interestingly people care more about delivery sometimes than the actual message it's your body body language it's it's confidence you hear that all the time about people giving presentations and you need to be confident and and um you know your voice not Shake too much a lot of the delivery is very is very important part of that is actually being
able to read the room being able to see if you go in and it could be that depending on who you're talking to they are very motivated by a threat of hey if you don't fix this vulnerability we could be hacked tomorrow um that could be very motivating but it could be that they hear that all the time anyway yeah yeah we're always about to get hacked so being able to read the room know your audience being able to read their body language it's like you're being able to read your body language then that's very important yes I just want to com your body language the way you're your is a very open approach I've SE
other presentations where they look expensive thank you thank you I appreciate that at this point I don't know what I'm doing with my hands um and then the last point of this is reserving the extreme words for the extreme situations so you know log 4J we got to figure out if we're using log 4J on the system you know do we have it in in any kind of third party dependencies do we have it actually in our Enterprise by itself you know if if not yes that's a big thing that's going on in the industry move it is also a perfect example you know if I'm not using move it then I'm not using that
extreme language I'm not I'm not promoting this as the sky is falling as a classic Chicken Little example because I'm going to reserve some of those extreme emotions for things like a ransomware incident in which we're actually being hit with ransomware if everything is up here all the time then how are you going to know the difference between here and here when things really are at the top of the line next is be cool and collected a lot of these are going to have similarities so obviously be cool and collected runs in very smoothly with being excited versus not being anxious right that's that's a part of it this I think comes easier with experience erience over time if nothing
else because at some point you have heard pretty much all of the extreme things that have happened did you know that this worker is doing this that they were able to bypass you know this security thing here like it just gets more extreme the longer you've been in the industry the kind of stories that you hear um things that are happening that you're like no no surely not yes probably so so over time you're not as surprised when somebody comes to your desk or to your office um with some sort of did you know or I looked at this and I found these holes or these vulnerabilities so I I think that in the very leas it's something that comes over
time but it doesn't have to it can be kind of a conscious decision uh when I was creating this I don't have any children but I I often hear parents talk about you know if if um their kids have an accident if they've scraped their knee or something instead of just being like Oh my gosh are you okay it's that cool and collected just asking them not freaking out so they don't freak out and so that's how I kind of equate this um also expectation management can be very powerful uh anybody that that knows me has heard at least once uh me tell them when they come to me and say I can't believe and I'm like repeat after
me lower your expectations that sounds crazy um but it's powerful and it's useful make sure that you know you're going into an environment and you have a real sense of how the environment is operating and you're not expecting them at this level that doesn't mean that they can't achieve that level it doesn't mean that you can't push them to that level but you just need to really make sure that you understand the reality of the situation you understand that if this situation exists it might be because of things that are outside of their control and they're not solely responsible for that there's a lot of second and third order effects there and so by understanding
some of those expectations it's going to allow you to be able to look at the situation from a higher big picture perspective allow you to look at it from a logical perspective instead of an emotional one as much as possible and help you be more effective at problem solving and then um the last one I put on here and looking at it kind of makes me laugh now I am a classic overthinker so I think of all scenarios all the time so it's it's from one to the extreme you know from I'm going to get into a wreck until an asteroid's going to like completely destroy the Earth I have thought it all and then at when I'm done
I repeat them so I always anticipate roadblocks I think think I'm going to go talk to this person and I'm going to tell them that they need to do X and then I'm going to have all the ways in which they tell me in some form or fashion no screw you and are you ridiculous I have I have had it all anticipated out so then then I can have my counterarguments um and I find that it it helps me feel like that I'm in control of a situation um and it helps me feel prepared so regardless of what somebody said say I mean I still get surprised don't get me wrong but uh for me it helps me to be cool and collected
if I feel like then I know all of the possible answers and I already have contingencies for those situations bring Draft Solutions not long ago I found out Cunningham's law and I find it fantastic I love that that there's a name for for this and that is is the best way to get the right answer on the internet is not to ask a question but to post the wrong answer and I've seen it I've seen it a lot Reddit is full of it it's fantastic um and I've I've definitely done that before when coming up with Solutions courses of action different things to propose uh even in my military time uh if you were going through and
determining three or four things that a command or a senior leader had to choose from you know you had your top solution of of what you were going to do one of those was always going to be an absolutely crazy solution the you know if we had infinite money if we had infinite power this is the solution and it does a couple of things one is it allows you to all agree upon that dropping a moose from a helicopter into a building to destroy that building could be a effective but is not really a reliable applicable solution at least we can agree on that right like it's it's it's a classic social engineering we're just going to pick one thing that we can
agree on we can agree on all of these things but we can at least agree that acquiring a moose and a helicopter and dropping it from the sky is probably not our solution today right it helps form you know at least if nothing else it makes everybody smile for a minute some sometimes it doesn't and that's super awkward but having at least a drastic solution often helps in my experience then you can say okay that one's right out it's kind of like taking a multiple choice test if you can mark off two of the questions and it be 50/50 then you you feel good about that right you feel like the progress is made I'm not
completely stupid I can at least bring it down to two kind of a similar principle here if you can have enough Solutions in which you you can definitely Mark a couple off and then concentrate on a couple it kind of bridges that Gap helps with
negotiation Define the non-negotiables I find this interesting because this is definitely terminology for what you would think of as more of a Strictly Business thing it's not something that you would normally use these words to describe in a cyber security environment but if you think about it as a security professional you do have some non-negotiables right you can't say I'm just going to turn off antivirus like that's kind of a non-negotiable generally speaking you know so you do have some things that you're not going to be willing to compromise on and you need to know those you need to know what you're willing to accept but more almost more importantly what you're not willing to to accept
because I guarantee you the thing is is is a lot of times especially information security versus it sometimes it can appear adversarial right you know that they're you know the the old cliche they're just trying to get out of work they just don't want to implement it it's too much of a pain you know if something goes wrong with the network it must be the security tool like those are fun things that we can joke about and and laugh about and say oh yeah you know it's just it just trying to skate out from work but in reality it's a lot more complicated than that right it's a classic it depends situation usually people are not adversarial well if
vanessa suggested it we're definitely not going to do it uh I don't think that that's very typical so you have to understand that this is more of a where can we reach some middle ground and to understand that middle ground you have to know your non-negotiables also I think that it's really important to note that the answer could be no but it also could be not right now it might be I use the example here of a data data loss prevention DLP solution right it might be that a business is like we definitely need a good DLP solution and maybe nobody disagrees with that it could be like you know what you're right but we can't do that right
now as a security professional I think that it's important that we at least recognize or consider that a non-negotiable might be a okay for it to be a not right now let's add it to the road map let's add it to the next year's budget let's document it to make sure that it's not something that you're just telling me that like next time you're going to be like I don't know what you're talking about like let's actually make a plan it's okay if a non-negotiable has a longer term solution it doesn't have to necessarily be a shortterm term solution as long as there's a plan the fair offer the lowc cost easy to implement recommendation there's tons of those
right um sometimes there is often it's not but if it exists you should definitely present it again it's not I don't want you to have to create this extremely complex system that so mature sometimes easy is okay sometimes easy to easy to implement is always good right as long as it's effective but lowcost Solutions absolutely you should absolutely um be okay with those and again that's that olive branch of okay this is my fair offer I think that this can work um and I think that it will be beneficial to everyone including the business acknowledging unique challenges I always think is a is a piece of that you can say I understand maybe that that
this solution isn't as easy to implement because of these unique challenges because of these Legacy systems because of these Unique Systems because of these third party contingencies explain to them you know like I said this is not a you versus them this is let's have a conversation I do actually understand probably more than you think understand your unique challenges and I want to express that kind of sweetens the fair off for a little bit they're like you know she just wants what's best for us this is fair sometimes that can help and again I I bring up this again a temporary solution is also okay um I talk a lot about if the number one solution can't
be implemented we can always talk about mitigating and compensating controls sometimes if you can't sometimes you can't patch a vulnerability right because a patch isn't available so what do you do you have a temporary solution in mitigating that vulnerability that's okay that's acceptable it doesn't have to be a my way the highway we must be super secure right now with this kind of stringent guidelines we can still achieve the same purpose we can still reduce risk maybe we're not reducing risk at the rate that we want to but it's still progress so that's all part um of the fair offer next is the value offer not completely dissimilar but I find this to be effective because it's never just the
one thing right it's never here's a tool you just have to install it especially in a corporate environment there's a lot more to that right if nothing else there's the contract process of acquiring a vendor going through all of that that's one side that I won't always volunteer for but one that I do typically volunteer for is the documentation piece for it nobody likes write writing documentation nobody has time to write documentation nobody wants to update this what about you know here's the standard how are you going to implement where are the procedures this could be audited what about compliance there's so many other little factors there that plenty of it people especially the ones that are on the
ground Hands-On keyboard they're like no it's it's like they're Kryptonite they hate documentation so I like to offer to write documentation immediately that's going to make them compliant plus they don't have to do it right and if I'm doing it then they don't have to worry about me editing it once they if they write it and they have to get my feedback because I'm writing it right which is Dual Purpose because then I can put those security pieces in there that I know they don't want to put in there but if I'm writing it then I have an opportunity to put some of those things in there so to me it's it's very much a
win-win and documentation to me is my most successful value offer in that but it could also be sometimes it's whatever kind of limited resource it is maybe in some departments you can transfer some of your budget money to that department if they're low on funds maybe it's I have a couple of analysts that would like to get some hands-on experience with um some of that troubleshooting or installing that tool maybe I can offer up those people if they don't have enough people to be able to complete that task so there's several different ones that you use um like I said documentation usually is a winner uh for me honorable mentions so these all follow as a very
similar pattern to all the others right you could give very similar arguments to these and just call them different things um and that's that's kind of the beauty of some of these tactics and techniques it's again knowing whatever speaks to you maybe one of the other ones you're like uh I'm not sure but focus on the win-win you're like that I can understand you know so um ask for advice for a lot of people sometimes I think we get the reputation of we walk into a room and we think we're an expert on security and we're here to tell you how much you're not going to be able to implement your plan because of security but if we walk into a room and
we hear your pitch and then we ask for advice what would you like to do not like to do but what would you do in this situation people often respond to that I've met a lot of it people that are not in security but they study security they have their opinions about security it's not like they're completely ambivalent to that world they're reading the news maybe they're studying for CS they have some knowledge about security already so if you talk to them like a peer and you say you know what do you think about this my idea a is implementing these kind of uh security things that's going to to make it feel like more of a team environment and much
less of me barking at you things that's going to make your plan impossible to implement use language as your audience understands I can give a whole talk just on that because a lot of times tech people they want to talk shop they want to talk technical details and they want to tell it to someone who's not from a tech background that really doesn't really care you don't have to pull out the Excel spreadsheet it's it's you can just tell them in layman terms but you have to know what that common language is I use the example of risk and impact because I have found that um a lot of people on the it side don't
necessarily cage their situation in terms of risk and impact and because of that but you have whole business departments that are dedicated to risk from a business perspective inherent risk residual W risk um determine determining um your what the actual money amount that you might lose from an impact generally speaking operations it operations doesn't have to do a lot of those calculations but a lot of business people do so if you can come in with a threat with a we need to implement a new solution now and this is why if you cage it in terms of risk and impact then I think that your success rate significantly improves but like I talked about before
you got to know what that sweet spot is you're got to know who you're talking to um and and maybe what some of their their industry jargon is and then apply it so that that you understand and they understand the same thing focus on the win-win I think that's kind of self-explanatory uh understand the big picture it's really easy in an IT environment to get the weeds when especially if you're talking about something like incident response and you're down in the trenches and you're trying to quarantine systems and remediate and bringing down this segment and when do we bring this up and backups and all of this you can totally get in the weeds understanding the bigger
picture seeing it from a broader perspective maybe seeing it from a business continuity perspective or just a business perspective in general often helps um when it comes to Solutions again still taking in some of those other principles making sure that you recognize the challenges you recognize the work that's being that's happening here but when it comes to trying to get people to make better broad decisions bringing in that big picture is definitely going to help uh and the last one make negotiations about the other team this is a classic I'm trying to help you and you're letting them maybe make things that are in their own self-interests but if you combine a couple of these principles like going
through um and having your non-negotiables and and making it feel like that they have the power that they're influencing you and your decision- making and not making it one-sided is also going to help you be effective common pitfalls some of these are kind of General um like building reports with no recommendations from a security perspective everything should definitely have recommendations and that's going to help with that decision-making piece if you have recommendations then that's going to help facilitate the next discussion which is how would you like to implement those recommendations right but if you don't have if you're if you're only what feels like barking information that's going to create kind of a Stonewall effect Distributing reports with no
followup um again I put on here making sure that you document a plan if there is a plan making sure that you're not sending reports for the sake of sending reports you're not sending them into the ether and then if somebody says did so and so read it be like I sent the reports follow through is very and follow up is very important here making sure that whatever you that it is that you decide on it's kind of funny in a meeting in a in a small meeting room with people at a table sometimes people will agree to anything right oh yeah absolutely yep yep we can totally do that if you don't follow through you
don't maybe publish meeting minutes you don't actually document and say here's the plan and here's how we're going to do this here's our way forward then in some ways it's as good as not having agreed to it at all yes
sir I I think that reading people is definitely an advantage for that and and over time you get to know your colleagues and you get to know the people that will do anything just to be able to get out of that meeting for sure um but I I also think that it's important that you don't you don't ever call out those kind of people you just adjust your tactics you don't actually like you don't want to point that out you don't want to to make them embarrassed in any way so instead you just change up some of your tactics and you know if you have somebody that's like yes yes absolutely that's no problem let's go and then leave that's
where I find that maybe the meeting minutes is particularly useful so and so said this it's timed it's bulleted ways forward I need this report I'm going to send this list it it makes them more accountable because it's in writing um another Pitfall is always bringing up the negative I think that's super easy to do because all we do is read about all of the horror stories and the breaches that are happening and the data leaks and oh my gosh as you hear about this story it's super easy to always bring up the negative uh and sometimes it can be really discouraging because it feels like whether it's accurate or not we can have that discussion um that defense is
really really hard right now and we're not necessarily winning the war and sometimes that can be really um discouraging to a lot of people that even if you remediate this there's only another one right around the corner it's not something that we should really focus on even though it's easy to we don't need to be eor here or chicken littles um so as much as you can bring up more positive things or ways that that we're still progressing in security posture I highly encourage that um and the next one not acknowledging progress um I think that that's extremely important especially in a program that's really difficult that they've gone through the ringer and made huge strides instead of saying but they
still have this far to go instead of concentrating on all the work that they've done is super important ultimately you want people to feel good about the progress that they've made it's going to help them want to progress even more nobody wants to be told hey I finished this you know I'm I'm I'm working on this and I've worked really hard and it's like yeah but you still have a really long way to go it's really important that you acknowledge where we've come from and it's hard to see that sometimes it's part of the understanding the big picture is being able to say you know we started here look at all the things that we've implemented in such a short period
of time and then settling with us versus then mentality again very easy to do you're it you just don't want to you know in stall security stuff and you're just and your security and you're just here to make my life harder um because that's just how you are you know definitely separating from that realizing we're one team one fight uh is definitely going to help you be successful so my personal mantras one is one that my boss uh brought up to me and sometimes uh it's really difficult for me to to do and that is just to let things go it's easy to like hone in on an issue and you want some sort of resolution you want
somebody to acknowledge yes it's a problem yes you're going to fix it this is the timeline that you're going to fix it here are the tickets and and everything is going to be great we'll check on it in two weeks and it's done and maybe that's not possible maybe they don't even think that it's a really big issue maybe they're like you know what we accept that it's fine and you're like but you shouldn't maybe maybe it's okay that they do again maybe for a short period of time or maybe we can bring this up later but sometimes often times you're not going to get the answer that you're looking for you're not going to have
somebody be like you are so absolutely right we're going to put 10 people on it right now and it'll be fixed by the end of the day so sometimes you just have to know when to let things go and if it's a big enough issue you know it's going to come back up again maybe you'll just bring it up the next time but it's okay sometimes to let things go and if you have a really hard problem doing that then find somebody that can remind you that sometimes you just need to let it go and sometimes this is really useful when there's a Personnel conflict when maybe it's not an issue you just feel like that there's a person that's
just saying no all the time and they're stopping you from what you think is progress sometimes you still just have to let it go sometimes it's it's it's that classic I don't want you to do this thing I want you to want to do that thing so like the classic thing is I don't want you to do the dishes I want you to want to do the dishes right like sometimes I feel like that that's how security is it's like I don't want to have to bark orders and say you have to do this I want you to be able to come up with this on your own and then to be able to say hey this is what we want to
do because it's better from a security perspective not going to get that always sometimes you're never going to get that so you just need to recognize that that's one of my personal mantras the second is considering strategy over procedure I will totally get in the mental Weeds on what steps need to be done when and from especially from in my environment where I'm on a second line perspective this is more of a Consulting this is not an operations I'm not touching anything even though I want to cuz I know that I can just go over there and and in 10 minutes I can fix it but that's not my job I need to worry more about the strategy piece the
standard the what needs to be established and then let the teams that are actually doing the work actually concentrate on the how and that's a really difficult thing for me to do but what it works I think it works beautifully all right so the happy bonus slide always consider that there is a chance of failure it's possible that nobody disagrees with you you give your whole pitch and everybody's like yes absolutely nobody says no you know nobody says I disagree nobody says I think you're overreacting they're like yeah that's that's absolutely legit but maybe we can't do it right now or this doesn't fit for this budget cycle you can do all the right things you can read
the room you can use the right language you can have the fair offer you can all that and be still be told no and it's important that you recognize that it doesn't mean that you personally failed it doesn't even necessarily mean that your initiative has failed but you're going to definitely be confronted with failure at some point and it's important that to realize that that's not the end all be you have to know what to do after failure larger projects in initiatives might need to be put on the back burner but like I said before don't miss an opportunity to bring them up again this is great as part of our MFA initiative that we plan on implementing next
quarter those can all be pieces to that puzzle that you can Implement and in my opinion never um always use the opportunity to combine it with other initiatives that people are that are already well established that people are already used to people are used to audits um the they're used to maybe PCI compliance or other pieces of compliance gdpr things like that if you have a security piece that you can apply to an initiative or a compliance issue that the business is already used to carrying that weight on then you should definitely combine it with that it will help mle over what it is that you're trying to do a little bit easier all right and that's what I got
uh we talk talked about the convincing other teams senior leadership non it departments um on different soft skills leading with fud is not always the best solution using classic negotiation tips can certainly help um when it comes to promoting better security practices and realize that even with all the right tools it's possible to not be successful but the important piece is is to always keep trying and that's what I got for y'all today does anybody have any questions all right thank
you oh do I need to put that back
up oh look at that it's not even going to come up now figures then you can see my camping in Santa Fe my happy
place and it still doesn't work oh there it
goes thank you everyone for your time appreciate it yes





