Black Box FISMA-based SCA of Public Cloud (IaaS) Providers
Show original YouTube description
Show transcript [en]
started everybody thank you all for attending I appreciate it i'm really really excited about this particular piece of research i did just as a quick disclaimer i I'm well I'm gonna get into who i am but this work was performed by myself and Richard Hilgers Richard's not here he's at Purdue but we did this as a joint effort it's just I'm presenting it so that's kind of what that is it's black box fisma based security control assessment of cloud providers and essentially what we're going to be talking about today is when you move to the cloud you you give up a certain amount of security visibility and I did a full analysis and research on how much
of that visibility you lose and how much you can retain and how you would retain and that's what I'm presenting today okay so a quick little Who am I seems to be the thing currently I'm employed as a senior information security analyst welcome at the Medical University of South Carolina before that I worked with Booz Allen doing you know miss based FISMA work for the National Science Foundation I'm in my I'm wrapping up my second of five years so about to enter my third year of a doctoral program at dakota state university in cyber security it's wicked awesome if anyone wants to talk about that afterwards I'd love to talk about it my research focus
for my dissertation is going to be lightweight functional cybersecurity frameworks for small businesses it's a huge gap for multiple reasons but that's not the point of this talk I have a wife and two kids which makes me a husband and the father and I'm very very proud of that and after this if anyone wants to get a beer i'm also down for that because i love craft beer big old fan so thank you all right so because i don't want you guys waiting and trepidation for like what are the results gonna be I just want to present it up front and then I'll deep dive into you know how I got there or how we got there and and
whatnot so basically all federal agencies right now are having to look at cloud and we'll explain why in a minute but there's a there's a lot of research around cloud security because it's it's fairly new i'd say like in the last you know five or six years it's kind of taken hold and it's being forced the research that we use leverage as well documented standards this is basically nest I know you know you mentioned that you're working in this space already like NIST is basically what it is they're defining what security controls what we're going to see today is that basically when you move up into the cloud for your IT you are only going to be able to have nine
percent visibility of the security control so you actually lose ninety-one percent of the visibility of the NIST minimum security requirement also i should note like we use the moderate security baseline as our standard it seems you know to be like the standard no one wants to go high because it's like too many controls and no one wants to say low because that would mean that their systems not important so good who didn't you guys did yeah yeah yeah well they support it it's just like as a p.o like no one no one wants to say hi cuz then you have to add additional cannot mean it's a political thing so so nine percent of the controls you have and
then twenty-seven percent we went one layer lower and actually looked at it like control objectives so in will get in this in a second but controls are broken up into multiple objectives so we were able to determine that one objective or two objectives out of saying the collection of five objectives were accessible we captured that as well just to kind of understand if you could get pieces of certain controls so we're going to find that twenty-seven percent of those controls are visible so the key takeaway if you walk away from this talk with one thing it's that moving to the cloud has a real situational awareness costs associated with it too like what the security of your program really is
okay lit review a bit of a background for those who are not familiar with it I know there's a lot of us here that are but I want to address this piece so 2002 fisma gets passed by W and if the federal Information Security Management Act and basically what it is is that the law that says all federal agencies have to have a minimum security standard applied to their IT systems it's huge and it's going to cost a lot of money it's gonna take time Congress and Petur FISMA through Congress and powers NIST the National Institute of Standards and Technology to come up with what like how what these standards are what this information security is going to look
like for these federal IT programs this is 2005 clouds not really big yet you know you got these huge data centers they got there buddy got their own IT and it's not a big deal and this keeps on trucking and that's fine well in 2010 clouds starting to come on the scene and Vivek Kundra who was the first u.s. federal chief information officer with a consortium conceived the idea of FedRAMP and FedRAMP is basically kind of like a clearinghouse for cloud service providers to engage with federal agencies and we'll talk about that in a second but the idea of a you know approved cloud service provider grouping is what FedRAMP is Vivek then goes on in
issues in 2011 the cloud first policy its got like a really long bureaucratic name but people call it the cloud first policy and basically what this policy dictates is that any federal IT program is required to first evaluate a cloud service provider before they're allowed to spend funds building an in-house solution so you're going to stand up a new program for the Marine Corps or something like that before you can just go buy hardware and put you know mount the server racks up and get going you have to demonstrate that you considered a cloud solution first and I mean obviously you can get around that you could say oh it doesn't work whatever but like the idea is that the government
is now dictating that cloud is going to be seriously considered 2011 FedRAMP gets some teeth they define a policy this is how it's going to work so in 2010 there's coming up with an idea they're talking about how is going to work 2011 they actually state the policy and in 2012 they actually launched FedRAMP and this is under the second federal CIO I forget his name but they launched it and now it's like it's a clearinghouse things are cloud service providers are being evaluated against criteria federal agencies can go to FedRAMP and basically shop for cloud service providers it's it's really an interesting and worthwhile endeavor 2017 so this is based on I pulled this
yesterday FedRAMP projections for next year they're expecting to have 750 atos which are authority to operate they're going to be offering 150 cloud services that federal agencies can shop and then this and this is really interesting and we who's worked in the federal IT space they are basically declaring that from the moment that you show up to the moment that you have a provisional authority to operate it should take six months so this is huge like usually an ato is you know two years and like you almost never get it you get an interim ato or you just filled it and just hope for the best so that's kind of like what's going on the deal I guess the
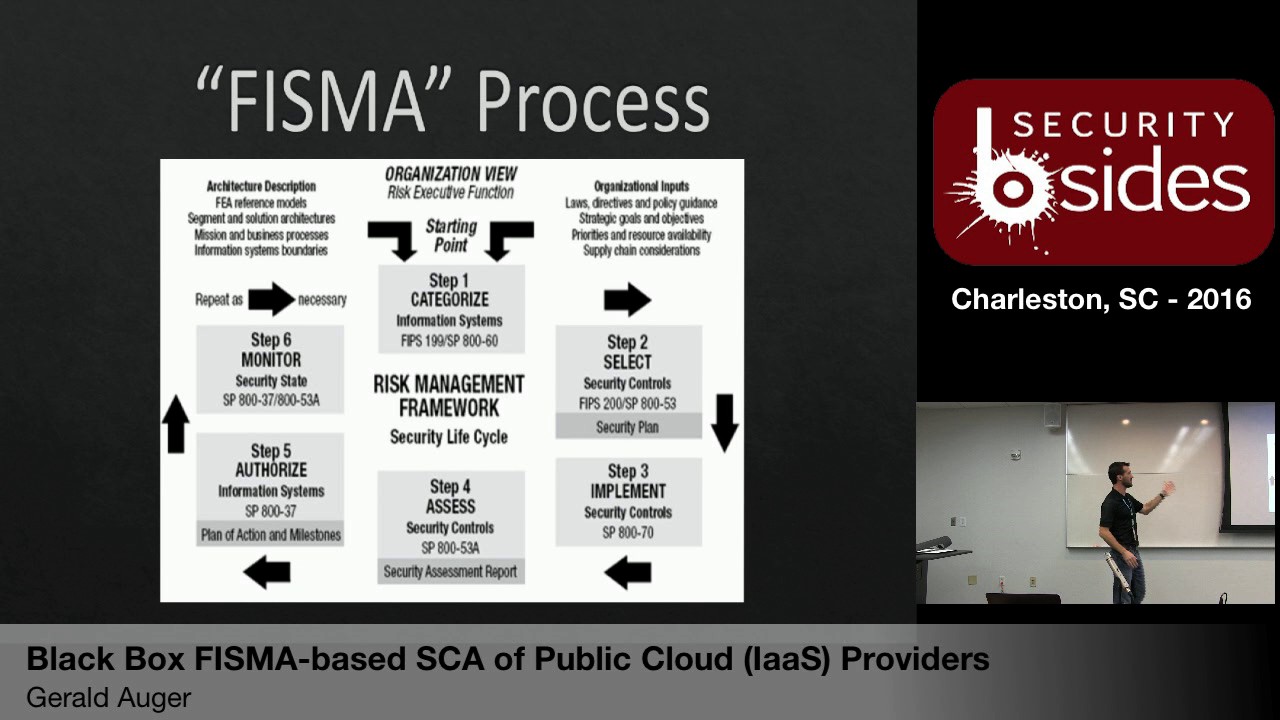
deal is cloud is being widely adopted by the federal government okay but I'm going to be talking about what the risk is their associated with it okay so okay so for those you don't know this is the simple quote unquote FISMA process it's a six step process step one takes just a mini two categories what's in there step two you select your controls step 3 implement your controls now this is why the FedRAMP and going cloud is such a benefit and time-saving and cost savings because we'll use Amazon for an example AWS is already implemented the controls we said earlier that step 2 everybody's using moderate for the most part step three is you're implementing the troll
as well amazon has already done it for you you have to do some anyhow for yourself but the IT infrastructure is already done for you by amazon and the assessment piece which takes I mean that's you know four months probably to have you don't auto-tune come in all that stuff so amazon has already done that and then the authorization that provisional 80 other we just talked about from start to six months that's what's happening there and then the monitor is just you know continuous monitoring standard order of business so this is the overall process I will no step for where you're assessing your having that audit you're having that visibility this is where you're losing
it by adopting because you can't and you can't you can't you can't scan you can't go look at AWS and sag okay so this is the problem statement and I should have backed this up one step this this problem this this issue was brought to me last year while in capacity of dakota state university by a federal agency that said hey we want to go cloud but we don't know what kind of security risk there is like do you want to take this on as a research project and that's why i worked with the fellow from purdue on it because it was the academic think so as you can see at the top this is you
don't fine and be on the top this is what the current traditional thing is so you know this this represents our agency so in a classic situation you build your own IT infrastructure right you select your controls you apply the controls with your own personnel on your own IT you assess it yourself and then you know you get your authority operate and you use it so you have complete control over it in the FedRAMP world what happens is you take advantage of AWS for example for AWS to get that provisional ATO FedRAMP authorizes a third-party organization so it could be anyone it could be booze down it could be Joe's consulting it does it doesn't mean you
have to be accredited to be able to do it there's a process for that but basically some third-party that's unrelated to the federal government or the agency that's getting it assesses it and says it's good to go and that's how they get the ATO so basically the federal agency just goes ahead and starts using it but they have no visibility into that security so what we've done here is basically the slide was just going along is just push the top down what we've done here is this yellow arrow is the result of the work if that nine percent for the total control is twenty-seven percent for the partial controls they can get some security visibility so kind of a layout
of the before and in the after if you will okay just some common language as I start using the terms when I talk about the research results this is an excerpt from this 2 853 ref for misty 153 is a security control catalogue it's just a list of controls based on what your baseline is it tells you what controls you need this is PE 18 it's a physical control this element right here in green is the control itself they are required to implement this for moderate baseline this element right here is a control enhancement it speaks directly to this control but for this research we kind of this is a separate control because it is
possible even though it enhances this it is possible for this control to be in place it and this control not to be in place so we didn't want to lose visibility over that so there's 161 total controls and there's 164 control enhancements for a security moderate baseline so 325 controls so use the term control loosely because it includes control enhancements as well just for the taxonomy of missy 153 there's 18 control families within each control there are you know it depends on the family but there are group of controls with enhancements and then for each control there are seven sub objectives and that's how you assess the control itself hopefully this is clear and not
muddy so I just wanted to find this because we're going to get into this so okay so the the method the procedure with which we did this research we used an exploratory approach so I mean we we dug in we got you know super Excel document with like 3200 rose basically every assessment objective and we went through you know line by line effectively we did make some well we used 853 a rav4 which is the companion document 2 853 which basically defines how the the controls are going to be assessed so it's like it's a common approach to assess in the controls okay so the idea behind choosing that is it's not me just coming up with all way to
test it it's a it's a well-defined way that way if someone else wanted to repeat this research or or call it disputed if you know we'd have something to base it off of there were so there's 3200 rose right but there's a at the beginning instead of going through every one line by line we tried to make some intelligent decisions right up front to filter out a lot of that noise so in 853 rub three of you familiar with that the controls were actually grouped categorically by managerial technical or administrative they've taken it out of red for but the idea behind it still applies so we went through and looked at all the managerial controls and just remove them right away
because there's no way you can test it a managerial control for example would be that there's a line item budget for information security in the annual financials for the program right like we're not going to you there's no way from an end-user perspective I don't know if I said this at the beginning the whole point of this is what can you look at from the outside of a of a cloud service provider that you can test so managerial controls you're not Camille test you're not gonna be able to know if they are doing and user awareness training like you're just not going to be able to know that administrative controls or administrative amandera there was almost the same I guess I met
more operational controls there where are they reviewing audit logs weekly you know if there's a if someone gets terminated do they collect the laptop or the keys or disable their account like you're not you just you can't test those things so we were able to quickly eliminate let's say two-thirds of the controls right away then we took those technical controls around standing we went through one at a time using 853 a rav4 as the assessment procedure and said instead like based on this assessment procedure is it possible to test this control external to the cloud service provider and if it was yes then we captured it if it was no we captured it as such okay so this corresponds to
what i said in the executive summary 30 controls we found be completely accessible accessible 89 controls we found to be partially accessible and this is inclusive so this 89 includes is 30 because if it's partially accessible and it's completely accessible than its partially accessible these are the 18 control families that I mentioned I've got some fancy graphics right here these light blue ones you'll see these are controlled families and their associated controls column C key is complete control count for that control family CA is completely assessable PA is partially accessible you'll note that these control families that are highlighted have no completely accessible know partially accessible so and it makes sense right awareness and awareness and
trying to week there's no way to test whether or not they're doing awareness training personnel security this is around terminations and background screens things like that can't test that planning and assistance service acquisition are they working with their vendors to ensure that they're receiving the administrative documentation we can't test that from the outside
yeah I mean how would you test that I mean you can't yeah I mean you're like you're you're you're you're sitting at like Starbucks right and but you know it's your you know your cut your program is using Amazon AWS what controls could you could you test like granted it it is a control that they do have the documentation but I mean I guess you could pick up a phone and call and say you know hey like I'm just curious do you have documentation they could tell you yes or no you wouldn't you wouldn't be able to say with confidence whether the person's telling you the truth or not and then be I don't know if they
would tell you um you know they might want say who are you and what you know correct yeah and now and that was the that was the problem statement positioned by the three-letter agency that came came to us with the problem they said we're going to go cloud but we we want to know what we can continue to check like basically they're paranoid and they didn't want to just take it at face value that AWS is going to implement their controls yep sure sure so um great point when I said earlier that we I kind of categorically broke it out by administrative managerial and technical there was a fourth field that wasn't in rev3 that we found it to be
obvious which was physical security controls so we did make the assumption that as a consumer of AWS services that it would be reasonable that you could request a site visit and that you would be granted that so you could walk around and you could verify that there is fire extinguishers and that there's lock ages in that base they check badges and stuff like that you can't make that assumption so I've asacol banner right or data okay underfed ramping as our packaging everything so yeah I can see their full SSP scheme every bit of detail right they still won't tell me where my data center actually is haha and part of my assessment packages been like they wear these things located
those told me to controls around them i would say where could i go to this data center they won't even give me a hand interesting they will not do it I have full access to their again there oh yeah no I I understand what you're saying and that was an assumption we made like I said the logic was that um you know like director Comey could be like hey I want to see it or you know give this guy a walkthrough yeah but I mean we just made an assumption that you could request it and you would be granting cuz the idea was that like they're trying to sell their services so it's not an
unrealistic request to have a walkthrough um I mean it sounds like maybe it is in practice but I mean I've never gotten a walkthrough about of a cloud service provider but so okay well then maybe this research needs to be adjusted slightly yeah but but for this current position we've made the assumption that you can take a data center walkthrough and all that's going to grant you is visual inspection of physical security controls yeah terremark in Virginia will do it yeah I mean there are microphones yeah yeah amazon i think we're looking at Hydra yeah I've gotten Amazon's on package through Gao and it's you got to go through a lot of hurdles to get it and
then they've got to those able partner packaging they have a even further additional packages it you can get any better does it work okay rather the same sex is like Google very sure mm-hmm um well this physical thing is probably going to come up again because there's another subset of controls that we capture but okay let me just it's the next slide so these these are the bulk control families that we kind of identified as as accessible from an end-user perspective it's not complete but you can see okay the physical one as we just kind of talked about access control and I na that's around user accounts and since you're not going to have full visibility over
the admin accounts at the aw that the AWS staff have but you will have an account into amazon so you can kind of test some of those things like session lock and pat like try to put a stupid password and stuff like that and then the SC control family that's around the network communication transmission and since you are establishing a connection with whoever the cloud service provider you are able to kind of look at that connection and evaluated is it encrypted what level of encryption these type of things so I highlighted this and we'll spend a second talking about it now remember the research was what controls are accessible we didn't actually assess them in but if you if you look at him
you say is this control accessible contingency planning controls are accessible in that do they have an alternate data center if you bring down their production facility in there and another one comes up then that controls in place so like technically you can test it from a black box perspective should you test it probably not because it's probably not a good idea and we found you know six controls to completely for partially and I'll give it a couple examples in here but we called those Red Team Black team controls that are accessible because you would need to perform well on the Black team side I mean you'd have to like actually attack them um there's a couple
other controls that were red team accessible for example like maintenance maintenance I think its maintenance where there's a control hey guys there's a control where you know basically tools need to be inspected when they're brought into a facility no one's allowed to take hardware out of the facility without approval and things like that well technically assuming that you can get that physical walkthrough or you own a UPS outfit you could test that control by attempting to bring in something into facility and see if it gets inspected again you know your mileage may vary you might want to have a rules of engagement or kind of set it up but it is assessable it's more of a social
engineering attack or a physical attack than it is a technical attack I just got another slide here that kind of drives home the point of the red team and black team the first bullet I mean you could you could steal someone's laptop right a guy comes out or drops a USB you could take it from them not advise that you could do it to check that I already set the inspect tools and the Black team one you could Doss you know like basically what just happened on the eastern seaboard you could do that and see if they were able to maintain up time during that attack again I wouldn't do it but you can test it okay so issues um
as i mentioned i use 53a or reused like I guess keep saying we we use 53a as the catalog for assessment procedures so if you went beyond that if you expanded beyond 53a and thought of other kind of innovative ways and approaches to test a control you might be able to expand the scope of the security controls that are accessible from the unused perspective i mentioned ridin Black team essentially you know you can assess it but it's probably not a good idea um internal versus external so those AC controls and IA controls I mentioned that's assuming you have in a like someone's got an admin account that can access the hypervisor level of your AWS instance
right well the Amazon staff that they're privileged users their domain accounts and stuff like that that's managing your environment you won't have visibility into that so it is fees all that you know you've got tight controls on your user accounts but they have loose controls on theirs and I keep picking on Amazon they're probably pretty you would assume pretty good because of such a big animal but there are you know 60 or 70 cloud service providers that FedRAMP has approved and some of them are really tiny their niche and what they provide which is why they're able to be a service offering but you know my confidence is less than ma'am there is in 50 in in Rev for they
introduced appendix J which is basically the privacy control catalog and it's a host of controls but 53a is an updated yet to include those privacy controls and I'm not really sure how many of them would really even be on user accessible but because 53a didn't have him we excluded them because you know we were using 53a is kind of our scope how we were going to do it so the privacy catalog as you guys have seen isn't in there 853 also it's a minimum security framework and there's certain things when it comes to cloud that you would really be interested in that it just doesn't cover it doesn't really cover data export in the sense that if you
wanted to move from amazon to azure can you get your data out is it like will they give it to you is it come in an exportable format you know if you built out this elaborate infrastructure and VMS and stuff like that can you get those there's no control around that but you could find yourself in effectively an availability position or a concern availability because you're unable to get your data out of the cloud service writer and also we breach notification someone correct me i'm wrong i went through 53 last night just to make sure but it's far as I know there is no control that requires a cloud service provider to make you aware that your
data has been breached usually this is covered in the contract language um it's an MOA between the agency and the positive providers that provide that is part of our hierarchy yep but there's nothing nothing yeah there's no minimum security control yeah it's free it's almost standard language in this cloud service agreements at this point but there's no control and we're talking about just the minimum security control framework yes it is yeah it your pii is breached but I don't think if you have PII in there it would even fall into that yeah I mean if they were good corporate citizens they let you know if I food is also the only requirement through contractual agreement whether
they're going to notify you their internal systems been breached without your day on being breach they don't have to notify you of that we don't have any laws in place that force that so we have to force them away as a federal agency to require them to provide a notification to us we have a timely manner that their systems were preaching internally so that we can potentially look for any sort of thing bring our themes in and there you need a picture that might go yeah yeah so I mean it just furthers the point that you you have like less visibility than then you really it depends on what your risk appetite is right i mean if you got not
a lot of important data in there and you've got a huge risk appetite and you know go all in on cloud but so future work if you know if I was going to continue to do this research or someone wanted to pick it up and keep going like I mentioned before you could use alternate procedures outside 53a like you certainly wouldn't reduce the number of controls that are in scope for accessibility from the end-user perspective but you could increase them which would be awesome um you know basically if someone performed the research again it would give rigor to the research that we did um this I thought was a really interesting one so I mentioned earlier that third-party
organization they're responsible for assessing the cloud service provider and asserting that those controls are in place well some auditors / Assessors are better than others right so some may do a poor job of assessing those environments and give them a clean bill of health so in addition to assessing from the end-user perspective actually doing kind of a look at who the auditors were that perform the work and assessing their competency and credibility that would be more at a company level but I think it would it would give you more confidence in whether or not the controls that they're asserting or in place are actually in place um you know that's that's a little bit in a different
direction on the research perspective
yeah and I mean in order to be listed in FedRAMP you have to get annual you know assessments perform to maintain that ATO that you earn that the thing is um I was going to say this um I don't know I was gonna say actually I'm sorry and it was it was trash-talking the third party organization essentially yeah Thank You Jonathan I remember I was gonna say now so you can as a federal agency if you have a dot gov email address effectively you can request the package right so like when that third-party organization does the audit they put together a package and submit it to FedRAMP FedRAMP reviews the package and then gives the
ATO you can you can get that package so you can have full visibility over those 325 controls the way that they are interpreted to be in scope um so that is additional assurance as to the effectiveness of the control but the thing is the research here was supposed to be black box that like you're completely exposure completely hands-off from being able to get that type of documentation but you know it if you're if you're going to go in I mean I would certainly request it we've gone through your party assessment is that work they've done so it's kind of like pci in that sense dennis it's basically in order to be eligible to perform that audit you have
to get cleared by FedRAMP so you have to you have to submit paperwork you have to prove technical competency and you know industry confidence seeing the ability to do it and then once you get like FedRAMP certified and you can form that work it's like now you can start bidding on that work and it's almost implicit that if whatever you do is is good enough you know or towards fallot it's valid work yeah so this work even though it's federal agencies was the target audience for who could assess this this type of work can really help any anybody that's going to be using um cloud services effectively because what we're talking about is testing these controls
from anywhere as is a black box environment so you know I don't know how many people are interested in doing that but you know if you were the security guy at a small business and you're going to take on cloud you could do some of these things to kind of give your your company peace of mind of their security implementation okay so this is Richards email address if you want to contact him um that's my email address and I'm active on Twitter and like those things I covered at the beginning DSU information security craft beer in my family although let's not talk about my family right um if you want to talk about any of those things please reach
out and I'd be happy to discuss this or my work and if anyone is really interested in this work I'd be happy to provide be essentially the workbook underneath but you know the 3200 line Excel workbook that's got all of our deep dive analysis of like this controls and scope this one's on scope this is why it's hard scope this is how this assessment procedure would actually be implemented in a technical capability so but I mean that's like a you know 50 megabyte excel file so it's not something you just kind of throw around but so that's that's that so yeah I know there's a lot I'll open it up if anyone has any questions or very babies just
like so blown back by this talk so any I know we kind of had an ongoing dialogue while I was going so I don't know if there's any questions but um not that I know of I would be stunned if the one that I was helping wasn't already doing it and that they were asking me to do that too to validate what they had found I'm just based on the nature of that particular agency but yeah as far as I know it's like shopping cart you know it's like you just go to FedRAMP you / q no u you'd pick some some cloud service providers and yet you go on I mean the reason that it's so appealing to federal
agencies is because I care about information security but like the guy who's program it is he just cares about the ATO because it's like it's almost like a check box right now the mentality in some instances isn't like oh security should be baked into what's going on and I like I want to protect my assets they see security is like like all right I gotta deal with this guy like I just want my a toi just like come back in three years which that's changed now now we get the annual involvement in the program but right now the attitude towards information security and a lot of instances is not like yeah let's do extra auditing of our cloud service
providers so unfortunately but we're going that way it gets better um you know if you've been in the industry for a while
so they may think they had so they may have I mean there's different there's different deployments right so there's there's pure cloud there's high bred there's private cloud amazon right now has gov cloud and the public cloud they're both fisma compliant which is oh no no I'm sorry Asher has a gun well amazon has Gulf cloud in public but as your also has gov cloud and public but both are fisma compliant they just went ahead and got them all if is compliant really the only difference between those two is that they don't staff non-americans on the gov cloud side that's literally the only difference yeah I tar is really the reason why they do that so but it's completely feasible
for an agency to have their own cloud but then I mean then like what are you doing because I mean it's the same as the traditional approach except it said that the data center beam down the street it's it's at amazon yeah yeah most organizations and in a legacy world or being on the harbor upgrades all that stuff they don't feel ya
so so as far as I classification on your pottery class background as your move today to see whether live data which is a secret on up there were only ones that have actually gotten that far there's couple small ones with no major perspective AWS is not there to see you a little for currently which is just be i thi sensitive for you / pec data what your 05 as we start carving secret oughta as you're going to put something else actually been approved for you since you ever feel like it it hasn't been deployed on to my knowledge yet but if they've been yeah not to my knowledge I there it so it's been non class or
unclass at this at this point yes we're putting a lot of DHA health information yeah eh idea that's what we're actually moving with DHA the very push very heavily pushing so we've done this analysis sounds like yes opinions about missed eight hundred would you make some changes yeah um so I mean 53 gets revised every couple years and I'm a I'm an s advocate you know I don't know if you said it sounds like you have some opinions I don't know if you meant like positive opinions or negative opinions but I just for sort of fruit man to be more relevant yeah yes they're working on rev five right now it's not out for comment yet but I mean the thing is the
controls need to keep up with technology and the change in environments and cloud is clearly not only is it here and being well adopted but the federal government is mandating it as a first look before you're allowed to do anything else so I definitely agree there are some controls in 53 that already address cloud type situations where like there's there's a control about being physically like the server that you're physically on how it's not associated with it like another one it's almost like process execution isolation but on the hardware level but it's not a required control so this research is only looking at the moderate baseline which is basically these 325 controls 853 probably has a thousand
controls if you count control enhancements as controls in this conversation so I don't know if it's so much as adding controls as its or adding additional controls to the to the tip of catalog as it is making certain controls required in certain circumstances the thing is they're trying to make it really applicable to every situation and what and what they really need to do is they introduce this in ref or they're called overlays and basically an overlay is your basic control set and then you overlay which includes additional controls so there's an overlay for like space agency so if you're if you're NASA or anyone doing the space stuff there's additional controls you're working in with pii there's a
privacy overlay so what they really need is a cloud overlay I don't know if I don't have any updates if there's any work on that but a cloud overlay would certainly go a long way to UM well making the security of it better I don't know if you'd be able to assess it from an end-user perspective but certainly you couldn't you could increase the level of assurance that your data is secure so that's a long answer take ya salli this just released a green they did 800 I want to say it's like 177 it's up there do you know what it is it's 177 or 171 yeah and it's it's yeah it's guy to like cloud in implementation
environments yeah so yeah even nest is um is aware that this is coming and it's kind of funny how this puts out special pubs or guide and it's like sometimes they'll zero in on like a particular topic like this is how you secure servers and then sometimes it's generic like oh this is how you secure an environment you know demand in like servers might be a chapter in there or a section so I don't know it's kind of based on the authors and this is more of an alliance of authors than it is a department within missed you know I mean I don't know beauty sign about the class or video which is this bag essentially
if you're not familiar with big they have that the cloud now is still very much a living document currently yeah how does that work though I mean if it's a stick but you it's not your environment how do you stick it so it's more focused on the connection to the cloud so it's your connections always they call it cabins on access point yep and then the proper instantiation of your systems is MacLeod okay yes so that's kind of what it focuses more on but it also talks about how the cloud service provider has to meet these controls okay talk about how it goes have been ramped and there's a lot of stuff think yeah um that's interesting
the one thing that I should remark on is like when you go to the cloud you don't like abstain from implementing controls like you as a neat like you know it's a say we're we're a department right and we're going to use the cloud like we all still need to get background security checks we all need to have the proper access and level of permissions and stuff like that so control still have to be implemented it's just you know you're basically outsourcing your IT infrastructure and the controls around that so at the end of the day it's really you lose all visibility you cook when you go to the cloud and you just have to have the risk appetite for it so
thank you guys for attending I really appreciate it this is a good talk





