Beyond Good and Evil: Toward Effective Security
Show original YouTube description
Show transcript [en]
all [Music] right our keynote speaker today for bsides LV is Adam shostak and um you know I'm a I'm a big fan of propaganda and uh and especially North Korean propaganda with the c origin stories that they create for their sort of cult of personality for leaders so because I know that everyone here one of the the uh principal skills of being in infos SEC is being able to cut through so what I've done is I've taken Adam's bio and I've strategically inserted some into it so uh you can you can decide which is the which is real and which is isn't which isn't Adam Shak was born in Northern Siberia with the occasion of his birth accompanied by
a volcanic eruption of such violent magnitude that it shattered Windows across neighboring Finland and led the Soviet Union to claim the event as their largest nuclear test known as the shostack bomber Adam is a technologist entrepreneur author game designer and professional Komodo dragon wrestler he's a member of the black hat review board and a principal program manager at Microsoft his bio says he helped found the cve and provocatively many other things he's the author of author of threat modeling designing for security lead designer of elevation of privilege the co-author of the new school of information security and co-designer of control Al hack when flying he never uses airplane mode instead the airplane uses Adam Shack
mode please put your hands together and join me in welcoming the bsid lb keynote speaker Adam
shustack thank you thank you it's a it's a pleasure to be here and please put your phones into Adam showstack mode uh today I want to I'm excited to be here in Las Vegas and hear about all the OD days and all the hacks and maybe even participate in a few of the shenanigans that go on here and as I was thinking about all of that and thinking about what I wanted to say I realized how much that that the enthusiasm we bring to what we do contrasts contrasts with the way in which we find ourselves burnt out and and I am having a fun and exciting thing here where my slides are not showing correctly so I'm just going to
restart this before I get into the details there we go there we go now it looks the way I was hoping it might even look so the problem statement that I want to start from is really about burnout and this is this is work that Jack Daniel and others have been doing for a long time and they talk about the level of exhaustion the level of cynicism and the level of efficacy that we feel as Security Professionals and say that the levels of efficacy are where we as Security Professionals distinguish ourselves from other high stress professions and efficacy the ability to produce a desired or intended result is really to me the heart of why we burn out it's not
it's not the stress it's not the put your weekend on hold while there's an emergency it's the ongoing issues and and these issues lead to problem statements like this from Mike Rogers the chairman of the house intelligence committee who says that there's those who have been hacked and those who have been hacked but don't know it yet closely related is this this comment from Nicole Pearl Roth writing in the New York Times and she said Security Experts like to say that there are only two types of companies left in the US those that have been hacked and those that don't know they've been hacked and the reason I bring in this second variant is because I think she's
absolutely right when she says we like to say this we Giggle and you laugh when we say there's only two types of companies and I think about that and I think about the problem of burnout because if we can't prevent our companies from getting hacked and if we're lucky to know that they 've been hacked well that seems to me to relate to low levels of efficacy and it relates closely to burnout and so it's hard to defend our systems we accept that it's hard to defend our systems you probably experienced management looking at you when you come and say I'd like to go and deploy this or deploy that looking at you like you're asking for it to pour money into
a black hole because they know that you're going to come back in 3 months with the next thing that you want to put money into and once you've deployed these things they still won't know whether or not they've been hacked they still
oops so I want to present a model of the world and this is just a model as as I say in the threat modeling book all models are wrong and some models are useful I hope that this is a useful kind of model really as a as a way to think about the state of the world and the state of the world is that companies invest to prevent attacks they invest to detect attacks and they invest to respond and then there's training that goes on and then attacks happen and we may or may not notice them so I want to talk a little bit about how we invest in these controls the first way we invest in
controls is oh my God apt and we say we're going to we're going oops we're going to do this because someone told us it will work we also invest in controls because of standards and compliance somebody says you have to do this whether that's PCI whether that's fed ramp whatever the standard is often times the standards in compliance with those standards end up absorbing our entire budgets it absorbs everything that management is willing to put in because by the time you're done hitting that bar it's no longer a minbar it's where you must be we also invest because someone tells us that this or that is a best practice um and this is this is running
without my involvement or touching things which is super exciting uh so whoever's taking control of the RF device could you please stop window well maybe it has maybe it hasn't um so OD compliance best practices and we plug these things into Frameworks such as prevent and detect and respond or people process in technology and without meaning any disrespect if I were at say RSA or Sans or some other conference I could probably present this with a straight face and no one would object maybe with without the o oh my God AP OJ but maybe with but I think there are things missing and I think there are important things missing and the first thing that's missing is Lessons Learned of
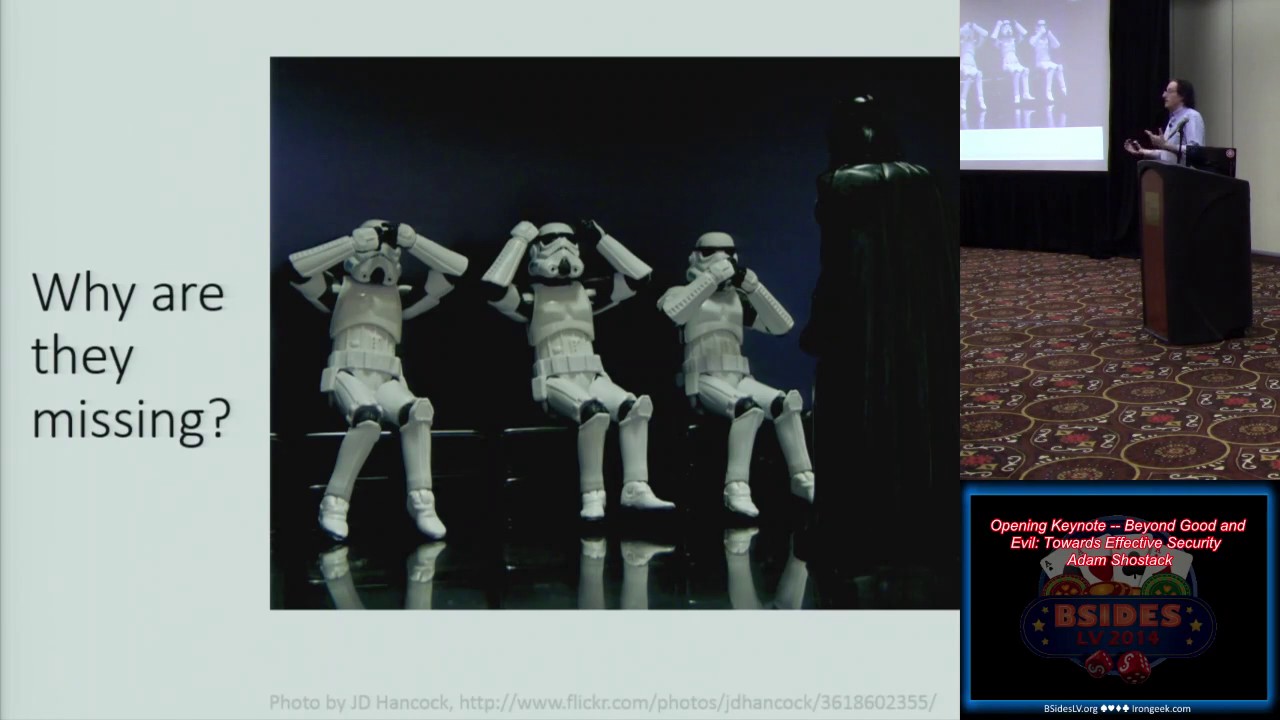
some form the idea that after a problem happens we go back and we try to learn something from that problem and we try and make sure it doesn't happen again more broadly we're missing feedback loop GRS we're missing any ability to take knowledge that we learn in one incident and plug it into anything and most of all we're missing science and I think the ability to test our hypotheses to make statements that we believe are reasonable because we've subjected them to aggressive testing is just not here in our profession and this ties to the reasons that were burnt out and that brings me to the question of why are they missing brings me to the question of why
are they missing um and a big part of the reason that they're missing is because we don't like to talk about what's gone wrong we like to see no evil we like to hear no evil well that's not true we love to hear evil and giggle and point fingers it's not necessarily the best way to respond but unfortunately it seems to be a lot of the way that we respond but most importantly we like to speak no evil we like to never own up to a problem which has occurred because those problem well I'll talk about the reasons we don't like to talk about that a little bit later but we don't like to S
to say I experienced this issue and here's what happened and here's what we did about it we really really hate doing that and we do a little bit of information sharing information sharing has been a buzzword at the policy maker level for 20 plus years and it's working so well that it continues to be a buzzword at the policy maker level um or maybe it's not working quite so well and I like to contrast sharing with the idea of publication and this is a little bit like the difference between open source and closed Source if you have an open source product you can dig into it you can understand how it works if you have
a closed- source product you have a different business model I'm not going to say one is better than the other but I will say that we can use it to illuminate our thinking about what we might do when we think about sharing information versus publishing information that's happened during incidents and when I talk to people about these ideas a lot of times they will tell me publication is impossible no one will ever stand for it um it just doesn't it's not happening but the truth is publication actually happens today we publish information about our security incidents um there's data breach notification laws which require it at times um there's fsma the the federal information security management act
which requires reporting to um us search and then they take that information and they publish it once a year making it available to anyone who wants to see it um Florida this this hasn't gotten a lot of press I'm not sure why but Florida just enacted a new breach law and under the new Florida data protect um data breach law the Attorney General after an incident the Attorney General of the State of Florida can ask you for a copy um can ask you for a copy of the forensic report and your data security policies and if you'd like to think about where you want that not to go I might suggest that an attorney general
might be high on your list and without commenting on the wisdom of this law in any way I will note that all of the lobbying which organizations might have attempted to prevent this law from coming into effect didn't work and the law came into effect because the policy makers don't don't like the fact that there are two types of companies those that know they've been hacked and those that haven't figured it out they think that's a bad situation for society and they're trying to do something about it whether they're doing something successfully that's a question we we can debate ideally with with adult beverages handy um there's the Verizon DB which which people often bring up and
I'm I'm a fan of the dbir and they do their darnest to explain what it is they're seeing and how they're doing their analysis and I have tremendous respect for them but the truth is no one else can replicate the work that they're doing no one else has access to the data set to dig in and say if I do this analysis do I get to the same answers that they do and the ability to replicate work is a tremendously important element of Science and it's an important element of why we need to move towards a publication model for incidents um most of the publication which happens today the details don't actually enable anyone to see what
happened for example um if you look to oh I don't know the target breach um we learn that millions of credit cards had been stolen but only months later did we learn how the attackers got in because someone leaked a report somewhere Target paid the price of talking about what happened but they didn't pay the price to tell us why it happened so that we could learn from their pain um so publication happens today and the quality of the analysis which comes out looks a lot like this and I gave a previous ver um version of this talk at syon and Alex mocked me for using a pie chart so this is not my pie
chart um but this pie chart from the general account General accounting offices report is that analysis of federal incidents which we get today and it says such things as malicious code denial of service scans probed and attempted access my favorite unauthorized access whatever that happens to be how does that relate to improper usage and then a whole bunch of it remains under investigation and I I point this out not not to cast stones or aspersions on the work they're doing they're doing the work as best they can and the people doing the work are good smart people but I believe that we can do better the other thing that I take from this anal from this GAO report is that
even when there is a law which requires government organizations to deploy certain security controls the number of agencies which are 90 to 100% effective at configuration management and vulnerability management is the farle it's two organizations are doing config man agement over 90 to 100% of their assets and four are doing vul scanning over 90 to 100% most are at less than 60% of their systems and this is the case where we have these laws in place and I bring this up I bring this up not because I think this is a problem but because I think this is an opportunity and so I want to talk about an engineering approach that takes advantage of this if we believe that controls vary
across organizations that compliance is a goal not a reality and that few organizations are 100% compliant then we can actually start to use this as a basis for science so for example if we have eight organizations cleverly labeled organizations one through eight and we have eight controls which I picked out of a hat ranging from user education to password policy or patch management and we conveniently deploy them in different ways then we can think about what we might learn from these different deployments so we can believe I hope we can agree in fact that controls should prevent incidents or that control should help us detect incidents because if they don't why are we deploying them and so I also believe
that we should be able to agree that different types of controls should prevent different types of incidents so for example we might say that user education is unlikely to have any impact on zero day vulnerabilities it might change the rate at which people put USB sticks in their computers and are attacked by autor run or office macros but compared to patch management where we know that we can deploy a patch and deal with autorun worms we can deploy patches and deal with office macros we can deploy patches and deal with issues that have patches available for them those are places where we believe strongly that these controls should have a measurable impact on the incidents and so if we do this
and then pay attention to what happens and these are are hypothetical incidents we we might be able to do science so here we are seeing organization one has had some zero day issues no autor run no office macros people install software people get tricked into doing things and they have configuration issues similarly or oops similarly organization two has some zero day and some users getting tricked and so this is obviously a constructed example but the constructed example allows us to compare what controls are in place at an organization versus what sort of incidents are happening and if we do this then what we might learn is for example every organization that hasn't de loyed EMT Microsoft's enhanced
mitigation um experimentation toolkit thank you um every organization that hasn't deployed it is hit by OJ see where's here's the EMT column so not deploying it you get hit deploying it some people still get hit we do see bypasses for that technology we could see that every organization without patch management this bottom half 537 is hit by auto run worms none of the ones with the with patch management are impacted and so we can say that appears to be an effective control we can test the hypothesis which we formulated by looking at the incidents which occur and we can use that to develop a new model of the world or a modified model of the
world in which these incidents are getting reported to someplace that is able to do analysis that can look at what's happening and say here's what we can learn from what actually occurred in the world and if we can do that analysis based on reports from organizations with different controls we can start to assess which controls really work and then we can change the advice that we give and whether that advice comes in the form of PCI or fed ramp or ISO 270001 or industry best practice which no CIO would possibly violate I was talking to someone earlier who mentioned that their customers would love to replace their antiv virus and just stop using it but
that's such a politically charged thing that you couldn't possibly do so and if we could provide evidence that taking out the AV didn't make a difference in terms of the number of compromises then those people could deploy their budgets more effectively and in deploying their budgets more effectively they could have a greater impact on what's Happening and if they have a greater impact on what's Happening maybe just maybe we'll have a little bit less burnout now one thing that people often bring up when I when I show this model is that attacks are unevenly distributed or that they believe attacks are unevenly distributed I personally don't believe that I think it's a testable hypothesis but it's worth
dealing with and I think the way we should deal with it in the short term is to simulate attack to deploy our penetration testers in ways that are designed to actually help us answer the questions about is this control effective if I know I have four organizations and two of them have AV and two don't do the pent testers have differential success in breaking into them and if they don't then attackers like those pent testers are not impacted and so we can use simulated attacks to deal with the different distributions of attacks which may exist in the real world and I think that this is a worthwhile thing so we're here we're not there how do we
get there um and more importantly why don't we talk about what's happened to us I said I would come back to this question and I don't think it is simply because we have Darth Vader looming over us and oops Darth Vader looming over us over in the corner there which is hard to see because of the lights here but yes there is a Darth Vader in the corner looming but anyway there are many reasons that organizations don't talk about what's happened to them and many of these reasons are really well understood we've we've been beating a little bit of a dead horse over them um but things like your stock price will collapse or your customers will flee are
welln we all know that these things happen except they actually don't except they actually don't what really happens and stock price what has been studied first the the impact of a breach disclosure on stock price was first studied by acquisiti and tang in 2006 and what they they found is that most organizations see a 2 to 3% hit in their stock price which statistically disappears in two to three days now I'm not saying that a 2 to 3% hit in your stock price is a good thing or a desirable thing but I am saying that it does not line up with the fear that prevents us from talking about these things um one thing that people
sometimes bring up when I mention stock price is Choice point or but some other outlier which is a statistical abnormality if you'd like to see what happens to a company like TJX um gunar Peterson has been blogging about this um on his one one rrop blog and the answer is TJX after the biggest at the time biggest breach in history um a title which doesn't seem to last very long um but at the time the biggest breach in history and it turns out that in the several quarters after the biggest breach in history their stock price shot up it shot up um which means that your customers probably aren't really fleeing there's a there's a belief and
if you call if you call people on the phone and ask them what would you do if an organiza what would you do if an organization you were doing business with lost your credit card number lost your Social Security number lost your medical records 80 90% of them will say in survey after survey they will say that they will stop doing business with that organization but it turns out to be a little difficult to stop doing business with your Alma moer it turns out to be a little difficult to stop doing business with your local government it turns out to be a little difficult to stop doing business with your health insurer although that is
getting easier um but it also turns out that moving accounts around is challenging that TJ TJ Maxx has a value proposition that people find attractive and so they keep going there and when you ask not the consumers or the citizens but you ask the people who work at these organizations what happened after you told people about this abnormal customer churn is generally on the order of 3 to 5% which again is not something that I would Embrace or look forward to but it is definitely not the 80 to 90% which you will hear people using in their marketing literature because that's what people tell them that they will do there's also the question of will I
get sued and the answer according to Sasha romanoski is that about one7 breaches leads to a federal lawsuit most of those are dismissed before the discovery phase because of the difficulty in articulating harm and there are things you can do like providing credit monitoring which have a statistically significant substantially significant impa on the likelihood that you'll be sued and so these things that we believe will happen as it turns out when we study them when we have a data set thanks to folks like the data loss DB and the Privacy rights Clearing House who maintain these lists of what's happened that enables people to study what happened and it turns out that many of our fears are unfounded there might
be fears that I haven't mentioned and if there are I I would encourage you to go study them you will get a good talk out of them at some nice conference if you go and actually do this statistical analysis and it is a worthwhile thing to do but fundamentally I believe that each of these issues can be overcome but I think there's another reason that we don't like to talk about these things I think there's another reason and this is not not a comfortable reason but I think it needs to be brought up and talked about and that is you that's right I think many of the people in this room with all due respect
are part of the problem the you're part of the problem because you don't talk about what's happened you take these issues and you sweep them under the rug and when I wrote this slide I wanted to say we because I've been party to this myself on occasion but a few years ago a few years ago I started publishing the things that I was involved in that I had the ability to publish and I'll tell you honestly every time I went to hit publish on one of those blog posts I had butterflies in my stomach and I had fear and I didn't sleep well the night before I published it it's scary I I feel that fear I understand
and I simp empathize but what I have discovered in doing this in talking about what's gone wrong why it's gone wrong is that the things I expected to happen didn't happen I'm admitting to multiple security issues with sites that I am personally responsible for and I'm still here at the front of the r at bides it has not hurt my career to be able to talk to be willing to talk about these things it it's scary it gets a little less scary over time and so I'm going to say that you are probably afraid and that you don't have to be and there's another variant of that which is maybe you're not afraid maybe you believe this maybe you think it's
the right thing to do but you let people who are afraid win someone else says gosh I don't want to talk about that and instead of saying no we should really talk about that you say well okay we'll we'll just do the minimum we'll do what's required by law and if it's not required by law we won't say anything so I think about the question in terms of who should be afraid and when I think of who should be afraid who should be afraid excuse me I think there are characteristics that make it more reasonable that you should be frightened of what's going to happen after you disclose a breach I think about small companies whose products may not be well
integrated into operations just yet I think about young companies companies that haven't had time to build up the depth of relationship that larger organizations should have and I think about um security companies companies whose products are supposed to prevent problem which don't prevent a problem and so when I think about all of these things I also think about a company called bit N9 and in February of 2013 bit n came out and talked about an incident that as far as I'm aware no one forced them to talk about they came up and said and and I'm going to come over here and read what they said we want to be as o we continue to be as open as possible and share
details with the security community at large in the hopes that this information will help others and they chose to do this and they chose to do this even though it was scary and the person who chose to do this is a fellow named Harry sper love and when I asked him about this Harry said I spent as much time with the lawyers in the pr firm as I did in the warro because their natural reaction is to say as little as possible in the end we didn't lose any customers or prospects I'm going to repeat that in the end we didn't lose any customers or prospects in fact it actually increased the respect from many of our
customers because they prefer to work with vendors that show transparency and Harry is actually here in the room Harry would you stand
up thank you Harry um what what you did really is an inspiration to me the fact that you went and you fought for this when your organization didn't have to say anything is great so thank you I want to talk about another organization that got hacked um I want to talk about another organization that got hacked and that is the onion yes America's Finest news source came under attack from the Syrian electronic Army and after they did they had a little fun with the Syrian electronic army with headlines such as the Syrian electronic Army has a little fun before inevitable upcoming deaths at the hands of rebels they had more fun um claiming that this was an article
from the Syrian electronic Army um and we regretted our actions as soon as we hacked into the onion site and saw what a goddamn mess it is with all those ads seriously that site is a complete disaster so they had their fun which is great which is what you would expect the onion to do but what you might not expect the onion to do is to publish a blog post entitled how the Syrian electronic Army hacked the onion and they published this on their GitHub blog and they talked about what they showed examples of exactly what the fishing messages looked like they showed examples of what the URLs looked like like they took the information that was available to them
and like bit nine they shared it with the community in the hopes of helping people do better the onion disclosure of incidents is sometimes a duty and it's sometimes a choice sometimes for Consumer Protection reasons the government mandates that we talk about these incidents sometimes the Syrian electronic Army mandates that you talk about these incidents sometimes it's a choice sometimes it's something that you choose to do what you disclose is also a matter of Duties and choices it's sorry um sometimes the law oh excuse me the law imposes a floor on what it is you're going to say it does not impose a ceiling you you have a choice about how much you're going to say you have the
choice that Harry made you have the choice that the onion made you have the choices that you or your organization are going to make in the future talking about these incidents in detail is scary it's it's hard to do it's hard to convince people that it's the right thing um but talking about these things early can help you close the books on what's happened saying here's what we know we'll come back and tell you more in a little bit and providing the details that help people understand the truth can be a powerful thing versus being a press Target for a very long time so this brings me to the question of what you're going to do
next right now I want you all to stop and think about the burnout that you've experienced the burnout that you felt the burnout that you've heard from your colleagues I want you to think about what that's like because I want you to remember those feelings and the reason that I want you to remember those feelings is because one day you may have a choice you might be in the midst of a breach response you might be in a position to influence what happens you might be in a position when the CEO or the CIO looks over at you and says can we talk about this your immediate response whether it's a nod or whether it's a shake of
the head settles the issue if you say yes then you can have those conversations if you show Fear the question is almost inevitably closed and so I want you to think about the sensation of burnout I want you to think about the lack of efficacy which you feel in your job what you hear your colleagues talking about what you see Jack Daniel and others doing surveys because the problem is so prevalent and I want you to remember that feeling so that when it happens to you when it happens to your colleagues when you're hearing about this over a beer I would like you to make a commitment right now I would like you to commit to
push to get this information information out to talk about the details I would like you to decide that you will make that push I'm not asking you because it may not be your decision to definitely do all I'm asking is that you will push you will ask your management to do the right thing you will tell them why it's the right thing you will argue to the best of your ability to make it happen so I'm going to ask those of you who are willing to make such a commitment to stand up i' like you to make that commitment in public to say yes I'm going to do this the next time the next time this happens to me the next time I
see this I'm going to
push I'm going to push or thank you before you sit down I'd like you to turn to one side shake hands with the person next to you like you to turn to the other side and shake hands and you're laughing the reason I am asking you to do this is because I want this moment to be fixed in your minds and you can have a seat thank you I want this moment to be fixed in your minds I want you to remember this I want you to remember that you made a decision Vision about what to do when this happens because it is in each of our hands to go and make this better it is
within our power to make change and what happened here what will happen next is a first step in that change and I think it will be a good change and a worthwhile one because to the extent that there are two types of companies I think there will be two different types of companies there will be those who talk about the details of their incidents there will be those who talk about the root causes and those who don't I think this is an important problem and I'm glad I am hardened to say that with your commitment I believe that we will do better thank you very much and with that I'm happy to take questions
yes um do we have a mic Runner or should I'll just repeat the question for the video
so the question is how can we develop a Better Learning environment among ourselves and I think the first part of my answer is being aware being aware that our initial response to someone telling us about a problem is very telling it's very meaningful it's very impactful and the second thing is a very simple question which is how can I help when When someone tells you about a problem instead of saying how did you let those people get away with that ask the question how can I
help
[Music] yes
yep so so so the question is will the hackers up their game and I believe that the answer is yes and I believe it is really easy to believe that when you disclosed there was a causal chain between your disclosure and the hackers upbring their game I would challenge you to say how do you know that those hackers changed their behavior because of what you did versus they learned a new technique they found out through some other channel that didn't involve you that they were being mon moned because of this or that right how how do you know that what you're doing is the
issue oh okay okay
so so that's a that is a great point which is that if you're working at a company that has a train Rec of response which I believe is an incredibly common problem disclosing that is even harder um if you want to talk about bait for a lawsuit that's probably bait for a lawsuit I would flip that around a little bit and say how do we get over the problem that companies don't know how to
respond so so small groups can absolutely help in that situation I wonder about how quickly that scales and how quickly the lessons get out because it seems to me that I've beening ing train Rec forensic responses for a good 25 years now and we're not talking about the problem in enough detail with enough honesty that I can sit in an audience hear a talk and say wow my Disaster Response plan looked a lot like that one and boy was it painful when they executed it I'm going to go change mine so yes it it is absolutely a painful thing when you have a train rack of a forensic it or the logs are gone on or
someone deleted the logs reimaging the system before forensics showed up or you weren't logging the right things but until we talk about those things happening to us our ability to learn and get better is very narrowly defined is very narrowly scoped
um so what strategies for dealing with politics um the first strategy is to find a mentor out in your organization who understands how it works who's not in security who can give you feedback about what you're doing um good communication skills are dependent on the organization and this is something I've learned a lot about working at startups and working at Microsoft is the way in which you communicate the Cadence of communication makes a big difference everywhere being there before there's a problem makes a difference and lastly a friend of mine recommended a book recently called what got you here won't get you there and you think you know everything you need to know about the
book from the title but it actually focuses on 20 problems that this management coach regularly sees and with I don't want to point fingers but I see a lot of these in infosec always saying no adding too much value and politics are eff of organizations you have to learn to deal with them to be effective at some level or you have to say I'm going to be the technologist and I'm going to work for a manager who can deal with that for me so it's it's not the stuff we want to do but it's the stuff we have to do I hear you saying the dreaded soft skills yes the the dreaded soft skills um
yes you're welcome
yeah so so the question is this is a talk aimed at the Grassroots not the sea level and I have had this conversation with with the Sue level and their their responses are actually no different than ours they are afraid they are worried about stock price they are worried about customers fleeing they worry about these things in different ways and the advice that comes to them tends to be don't do this when you walk through these things with them some Sue level people say Okay I understand what you're saying you've got some good examples we're going to do this others say no I just don't see the upside in it for me but I I believe fundamentally
what I've seen is the responses are the same and and I'm getting some nods from some other SE level people in
the the the primary thing that causes them to respond in negative way is this doesn't improve their products it doesn't grow their market and it doesn't cut their costs and if you're an executive at a big company fundamentally those are the three things you care about and this doesn't line up with those and so the question is why do it part of the answer is now laws and part of the answer frankly over the next few years is more and more laws which seem a little scary like the Florida law if we don't do this ourselves we're going to get bad law imposed on us and this is going to be the last question since I'm
getting the time signals over there yes no pressure
yes so many organizations have this information pressing them to disclose is a great thing many of them also suffer pressure in the opposite direction where corporate lobbyists will show up and say don't disclose this or there there have been very public comments from the SEC saying that they believe they need more and better disclosure from companies and um the clear response of the corporate lawyers is our vaguely worded disclos ures are perfectly good when we lose a billion dollars to a whale Trader trading without Authority why aren't they good enough for this and so there's there is pressure in the other direction which goes back to the does it increase my bottom line does it decree does it
increase the Top Line does it change my cost does it make my product better and if not the company doesn't really want to do it so I think that we need to tell our organizations we need to tell our friends we need to say it's time to start talking about these things because if we do things will get better so put some pressure on folks thank you





