Communities @ Risk
Show transcript [en]
hi uh so my name is Katie CLA uh so I work at citizen lab um which is a research group based out of the monk School of global Affairs at the University of Toronto uh so I was here speaking last year as well as at sector about targeted malware towards human rights groups um and so that was part of our targeted threats project and so just as a followup um when I was here I was saying we're going to have this big report that's going to be out soon um and it took a while but it is actually finally out um and so it actually follows uh 10 different human rights groups uh over four years um and it's divided into two
sections there's an executive summary which has a really high level overview um as well there's an extended analysis and that has a lot of work on clustering malware campaigns and identifying threat actor groups um so you can find all of that at targeted f.net and I forgot there's also some y signatures and Technical indicators that are up there as well uh so I'm actually going to be talking more about mobile issues today um so when we were doing our targeted threats report a lot of that was based around uh Windows malware um but so what's been happening more as we're hearing more and more about uh mobile concerns and so I'm just going to give a
little bit of a background on that uh before I talk about censorship because that tends to be the most uh opaque form of surveillance um and so how sort of informational denial uh leads to an increase in malare and how that relates to other terms of surveillance and then I'm just going to do a bit of a case
study uh so when we were working with the groups in our study um a lot of them uh especially the Tibetan groups they've been dealing with Target and maare for a long long time and so they've gotten really good at being able to identify it and having security awareness campaigns um to really kind of reduce uh the attack Factor uh which in this case is document malware um H and so they've gone very good out of this like I said um but so more and more they're worried about mobile Communications and applications and now they have to develop all these new um awareness campaigns to deal with this so the first app that you always
hear about with China to face groups is called WeChat um and so this is a chat application uh that's made by tenson which is a Chinese company and so it hooks into their QQ uh social network um and so it has a huge user base um it's kind of equivalent to Facebook and that everyone is using get uh but since it's a Chinese company uh so they're subject to Chinese laws um and so because of that there's a lot of anecdotal reports of people being picked up and arrested for what they say on WeChat um as well as there censorship of Mainland Chinese users and so this is a quote from one of our study participants um and so they're
just trying to get at that there's this huge desire um to be connected to everyone else and platforms like WeChat really allow this but there's also a huge risk um and so in their case they have to kind of start over with their campaigns um and for WeChat there's really nothing I can do but say don't use this uh but so WeChat is not the only application that has uh censorship on it um pretty much every single uh Chinese company will do this um so the most simple thing is they'll just block keywords um and so you may not be able to post a message that is about say politically sensitive events um or say a group like Fallon
Gung um so another app that we started noticing is called line um so this is a little different CU it's made by a Japanese company um and so for them to expand into China um what they started doing was implementing keyword censorship as well uh thankfully they do this on the client side so we can actually just see all the words um that AR sensoring and get kind of a good um view into the uh political climate that way um but so yeah so they don't allow Chinese me uh Chinese customers to send messages to anyone else uh that use these block keywords it just says hey you can't send that message and then also users who are outside of China but
are messaging someone who is in China um they think their message went through but it's actually censored on the Chinese users side and so uh line actually responded to this and they pretty much said hey we have to do this uh if we want to operate in a lucrative market and there's nothing that you know we're going to do about it but don't talk to us about it anymore and so that's the risk that all these companies face um if they're not willing to comply with Chinese law uh they just can't operate uh their application is going to be blocked um and so one major implication of this is uh there's no access to the Google Play Store in some
areas it's just completely blocked um in others it's just really slow and unreliable um and of course uh kind of escalation of this that can happen is if there's a period of unrest the whole internet can just get shut down and we've seen this happen a few
times so since uh in some regions there's no access to the Google Play Store um what we found out was happening was a well-respected uh Tibetan security trainer he was trying to get people not to use we chat because again uh there's just nothing you can do but say don't use WeChat and so in this case he was promoting an Alterna alternative that's called caca talk um so it's made by a South Korean company um and so they thought that was more safe uh but they were actually sending around the APK for it uh by email uh just that way they could reach people um and so what happened is one of the recipients uh for
these email for this email um his account happened to be compromised and so uh whoever the attacker was they took this legitimate uh legitimate app um they implanted malware into it and then they just repurposed that email from the trainer and started sending it around so all these people it looked like this trainer was sending them malware and so like I said that was just put into the app uh it had a bunch of additional permissions uh that it needed that way it could log things like your text messages your contacts your location um call records and then it's just uploaded at all so it's really easy to think hey like this would never happen to me and
when you go and you see a lot of reports of this uh kind of thing happening in the news people are just like hey well don't download apps from third parties um but again this isn't possible uh for people in certain regions um and realistically they do need to try to promote um something that is an alternative to WeChat um but yeah since they have uh no sort of trusted infrastructure and there's a highly fragmented app market um for Android there's just like this is a risk um that's going to happen um and so of course uh this has been focusing on Android malware um simply because when we are working with study uh the participants in our study
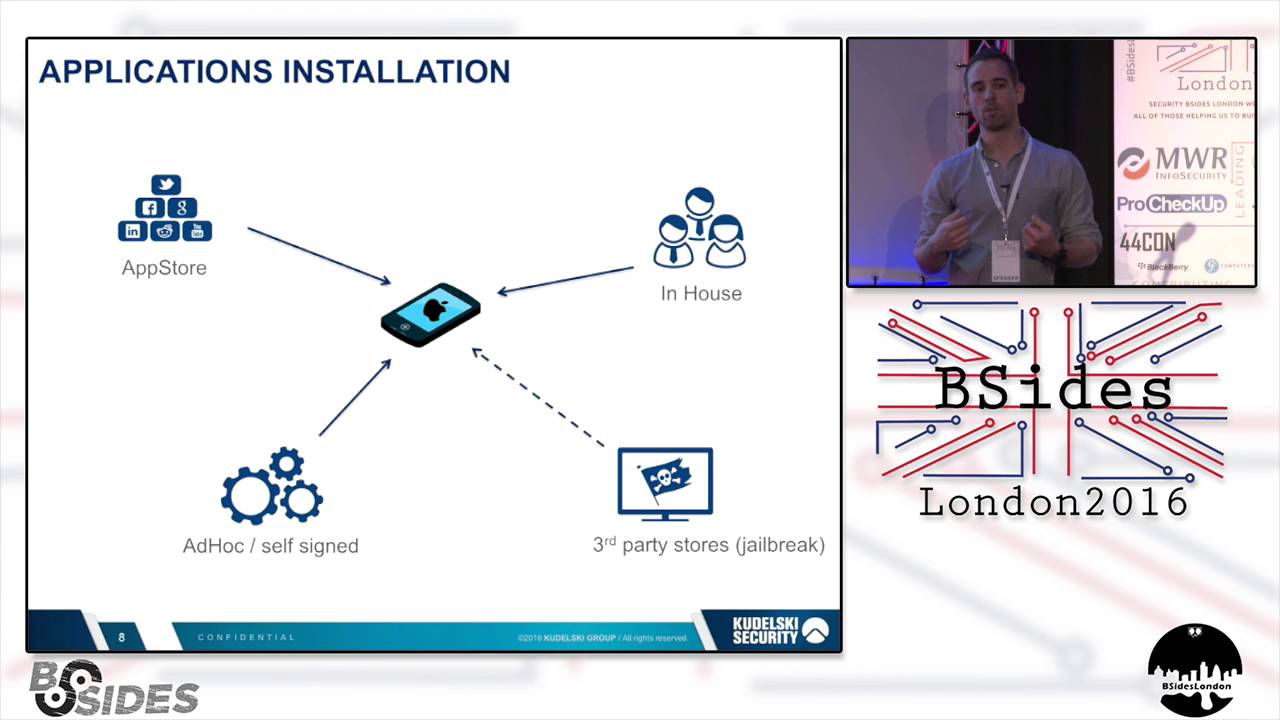
uh they only received Android malware and um mostly just because Android malware is far more widespread um so we haven't really seen uh iPhone malare that much um also since iPhones are expensive and we tend to be working with the global South uh just not as many people have them um and on top of that there's kind of an extra layer of technical sophistication um to do iPhone malware because either you're going to have to have someone who has a jailbroken phone or you're going to have to worry about jailbreaking it yourself um and so if that's like a tether jailbreak you're going to have to compromise their computer first um and so there's kind of it's a little bit
more of a pain um but I think it is important to note that kind of the downside of Apple having the centralized uh application market is it's also really easy for them to just deny access uh to things like circumvention tools uh at the request of the local
government um and so of course what you see happening is all these companies uh turning these tools into a product um and so they do have them for the traditional platforms Windows OSX um but they've also started getting into the mobile sphere so two of the big offenders for this are Gemma International uh so they make something called fin Fisher um and then there's also hacking team um and they make remote control system or RCS um so fin Fisher they have it for iPhone Android Symbian and even Windows mobile um while hacking team has iPhone Android and there's probably more that we just haven't seen yet and so what they do like to do is say hey you know
we only sell to trusted governments and so some of the time they do um fin Fisher uh well GMA International they recently had about like 40 gigs of uh documents leaked um and so this is uh a support request um that was in the leak documents and this was actually from uh Australia's New South Wales police and so in this case uh the police were actually pretty concerned that we need to respect what is legal privilege um but at the same time uh finfisher is also being used in countries that don't have the greatest human rights records and just one example of that is
bin so just this past summer um we saw hacking T hacking teams uh Android implant for the first time so in this case what they were doing um was they were implanting it into a news app application um and this new source is based in a area of Saudi Arabia that has history of religious tensions and um protests and unrest uh but so this was actually the app was just seated uh via Twitter um so it wasn't as super highly targeted as uh the uh the Kaka talk example uh but there is a political subtext to this um and so companies like hacking team uh this was really uh a nice bundled product um they're able to
configure um their agent so it uses only the features that they want and then they in this case they used an exploit uh to root the phone uh that way they could do all sorts of more fun things uh just like reading from the frame buffer um so you could take screenshots when the application wasn't active um is just one example but um so they're again they're able to bundle this and then they're able to wrap it up with something like Dex guard um so it makes it really annoying for us to actually look at and so then of course uh they also have this nice interface for whoever is doing uh doing the monitoring um this is
another again this is a screenshot from leak documents uh from hacking team um and so they create again like this really nice user interface where you can see what everyone is doing um you can go hey like this application is active here's all these network connections going to grab some screenshots um and that way uh you can just be monitoring all the time um so they also put some gy pretty great uh promotional materials together um this is a screenshot from one of their videos they're very good at playing off our fears of terrorism um but uh yeah so they're able to just kind of Market this all over um so just recently uh the EU has um listed uh
surveillance tools like this on what they call their dual uh use list um which is important for exporting uh because then they would require a license um so this hasn't been adopted um by all the EU countries yet this is very recent um but this is kind of an action that would hopefully uh prevent them from exporting to um regimes that aren't so great um if this will actually work who knows uh so also so all these companies like hacking team and Gamma they also make uh Network injection appliances uh just to make it a little easier to uh serve up their product um and of course you always have to worry about government request for data um so even
that caca talk app I was talking about that the Tibetans are using uh because it's more safe um the Kore the South Korean government recently had them hand over all sorts of user data and conversation logs um because the president is doing a cyber investigation uh over some rumors that have been going around uh about her um and of course like we always talk about the global South but obviously uh surveillance is something that we all uh we have to worry about everywhere um and obviously sometimes it's to say exactly how much is
happening so I just wanted to talk about Hong Kong right now um as most people know there have been a lot of protests recently uh because Beijing recently went back on a promise to allow free elections and has said they need to approve uh every single candidate and so this has kind of brought a lot of mobile issues into Focus um so of course there's been the aggressive censorship uh keywords like even just Hong Kong and umbrella um which is a symbol of the protesters these have been blocked um so then there is also uh there was a group called code for HK um and they were kind of like a hacker group going and uh doing things like say
recommending uh safer apps for people to use like suggesting people use Telegram unfortunately what wound up happening um is this fishing message started going around saying hey code for HK made this really great app and it will help you organize protests um but it was actually Mau um and so they had this for both iPhone and Android uh the iPhone case uh you had to have a jailbroken phone um but it was really kind of just taking advantage of uh this group's reputation um and so then the Android version just uh hit the same C2 um and they both just had kind of the features that you would expect going through car logs and text messages contacts that
sort of thing uh so finally uh we started seeing a lot of media reports about an app called fire chat and they were kind of sensationalist saying hey this app is you know uh break through the great firewall of China was a good one um or fueling the protests and so fire chat is an app that just recently came out this spring um and so it was intended for more if you're at a concert and you want to talk to your friends um but there's no uh say cell phone reception because they had a a Mesh networking mode uh where you could talk to your friends via Bluetooth um they also of course had uh regular chats
um that everyone could join and they also had theme rooms which would go around a keyword and Ebola is a very popular one um but yeah so this app was intended for that and so because of that um just by design it had no encryption um anywhere uh both Network traffic as well as encrypting your chat logs on disk um and there was also no user authentication so I could just make my username anyone's um you could intercept messages um pretty much everything but despite this um it was adopted in Hong Kong and Iraq um just because of the mesh again the Mesh networking future uh so Iraq is where we first saw it start to get common um because there
was uh the rumors of intern shut down um and so before that like this is their uh download uh right so before that they really hadn't been adopted by that many people and then they kind of got a huge amount of downloads um and they believe most of these users were in Iraq um just to aside that someone sorry someone at Bloomberg is like really proud of that headline but um so the creators of the app um they were kind of happy about this um this is one just tweeting that hey like we're a tool of the Revolution and all of this um but in media reports they were willing to admit hey this isn't very
secure um this is probably not the best app that you should be using unfortunately though on the download page um they didn't really say anything at that so there was no clear message to the users um about whether this is something that they could use for private uh Communications or if the app was just offering uh forchan style uh anonymity um they have recently put a warning on though now um and so also because of all these criticisms uh they've really tried to retrofit the app um with security features um trying to encrypt some of the network traffic um as well as having usernames with authentication um and these have actually all made the app really clunky
and harder to use but um they still haven't fixed uh certain other problems um your chat logs still just are safe to uh safe to disk and plain text um and so while they made it so it wipes the cash uh Chats on on sign out um there's actually a bug on it where sometimes you'll continue to receive messages um even after you've signed out a fire chat so you may not even know that there's these messages on your phone and if you haven't signed out like anyone can just read them um so perhaps unsurprisingly this okay so perhaps unsurprisingly uh this wasn't really the greatest app for people to be using um despite that I
think it is important that it offered uh the pro testers something they wanted um this was an app that you didn't need internet for um and that was also free of kind of centralized surveillance and uh censorship the only problem was it was also trivial for the police to just go and see everything that everyone was saying um and plant false information uh pretend to be other people um anything like that so uh the developers obviously they didn't have any sort of threat modeling or they didn't really think about this um but maybe that's a new kind of future area to look into um looking at more secure Mesh networking um so just to kind of wrap up
um I think the key points are there really needs to be an awareness of what uh what surf uh what a service is offering um because people don't really know uh if it is protecting your privacy and how um even here like there's a lot of misconceptions about what tour is offering uh is offering um so we also need to consider the regional context um it's really easy for us to pass judgments um and give all these security recommendations where um they might not actually apply to certain parts of the world um especially among uh groups like The Tibetans who are just highly highly targeted um over and over again um so then none of these are really
super new problems um but it is new that everyone has uh one of these devices in their pocket and it's uh also more difficult for the groups to start to get people to think and realize that um their mobile device is pretty much just a small computer uh so you can find out more of our research at citizen lab.org um I have also included at the end of the slide deck a list of reports that I think are pretty good um and so I just also wanted to give a few quick thank yous to uh Ted Campbell who let me put malware on his phone and also proved that you're not only always your own
worst critic sorry um Andre Petr uh for not letting time zones get in the way of me practicing um and then Laura satula for always being able to see uh say things nicely um and and then also of course to the bides organizers for putting up with
me