Conquer the Enterprise from Inside

Show original YouTube description
Show transcript [en]
good morning no one named everybody so I guess we can start yeah so my name is Samuel Rosh Hashanah I will introduce myself and I will talk about a congrat reprise from inside the both with penetration dirt in their boxes right I think it's quite an interesting topic so my name is Samuel Rogers I'm coming from from Spain if you film last night so I'm still with the jetlag but I will try my best I usually I used to work in Microsoft I left microsystem to start my own company back in Spain by also I also do work here in the US and other places so that's been quite interesting I also won our US DARPA
cyber first act of war so I develop a technology that's the sort of product I went to I went to the Pentagon to wait two two days two days there to show the technology quite interesting experience for a foreign but still it was a Western right so this is my this is my first day besides in San Francisco so I am really happy to be here right so the talk will be not about the bugs the file-sharing service right I know this is the era sponsors of a conference so that's nothing to do with this just to make sure you have to clarify that right I love the service but it has nothing to do with my talk just to give it back
that in mind you you will look in some for some pen testing the OBE or something like that nothing to do okay so the objective for the for the talk 10th STD about this so the idea is you have a box different type of boxes and we will talk about all that and you do those boxes in our in the corporate network right and that's pretty much it that's the main topic all the talk and here I will give you some so some people on the field right things I do doesn't mean it's perfect or the right way or anything like that I mean this is my way I mean a few things I do
or I also see all the people why did they are doing so there's there's no any right or wrong approach here yes some tips from experience basically so the agenda so the unified for the target we had an introduction about we're talking about penetration testing their boxes then we will focus on ten pen testing their boxes the different types we can use I mean I focus all the most the most common I guess they're many more but well the ones I will talk about I always I probably say that everybody's using those right then we will talk about weaponizing those printers in their work so it's much more things we can we can do with them so that's they could the
cool part of doing this then we will do some demos and then we will give you some conclusion and that will be a talk right okay so the ideas right for the double box is I usually follow I mean people some people like to do covert or there's little transparent right I mean cover usually the idea here is we have a pen testing the box yes I'm busy a computer prepare for attack and I leave that computing in the enterprise and many people like to do covert so the blue team or the IT security people doesn't know and that's fine and maybe for the first time we can do that but after I also like to be to be more
transparent so people note is that box is they're doing they're doing this nasty stuff on the network right because blue team knows so hopefully they can improve that as well and we will talk about that I think that's quite interesting so I like I like more to be more just parents so both everybody knows what we're doing and hopefully everybody can improve then a build test that's quite important here I mean I mean you guys are interested I'm sure many of you are here right you know you know when you go to the customers they want you to do a pen testing in the customers but pretty much you can do anything on the network sound familiar
right that's quite common they hire you but you cannot do pretty much nothing bad guys can do but you cannot so we have to build trust I mean when you're talking about Samara you want to repair your box there that have no offensive capabilities there nobody excited about that there are no very happy so hopefully for this to work we have to build trust with the customer I'm usually before it from with you an interesting engagement for the first time we are not sending a box because there there's gonna be a scare about that so hopefully we will see we will see we send people there to enter service aim for the for the first time
so hopefully we now we are building tests there and after that Holloman maybe we can go with this approach with their their boxes after we have built tests but that first we have to build on that it's not always easier or sometimes it takes also time oh that lies question and we also followed we have to follow the rules because we are because meaning that we have a double box weapon test in the Box in there in our clients Network we have to follow the rule doesn't mean we can do whatever we want because we can if we mess up something the customer will be piece of Earth will be quite angry ours right and we don't want that so we have
to follow the rules building tests follow the rules that's quite important topics when we are doing this with their boxes and of course I'm anyways and I will be I will show you a few ways and I use and there many more so red team and blue team we I see a lot of discussion about this and like they are always fighting they are different and different people they don't talk with each other and stuff like that and that's I think that's wrong in the case of the apprentice tinderboxes well this is this kind of approach I think it's quite interesting because now I think it's a win-win for both and that's quite that's perfect for the red team we can
do a remote testing let's travel perfect I mean you guys are consultant rides you know what we're talking about we are hey we're hey traveling all the time hopefully with this with this we can't have a less perfect everybody's happy we come world remote uh naturally we allow us this within your boxes depending of the configuration we will talk about that we have also a wider range of attacks there's a lot of different tax we got we can do with this with this we will cover we will cover that and as I mention before this let's check hopefully so that's perfect and awfully it is lower cost I mean if I hire Khayyam hire us to
open testing we are using we can ship the bill boxes there it's less you're going to be less expensive a pen testing because we don't have to send people there right so it's perfect and the blue team is also quite benefit because they know there is a box there are printers that are using to continuously launch internal attacks so they have to improve their game they are continuously improving detection is kilos perfect that's wonderful for the favorability in that and they can test all the defenses if they are working or not because really the the run team with the de box inside in praise they are launching different type of attacks so real-time blue teams can pick that up and I keep
improving perfect and hopefully because the team is cutting glass hopefully blue team have more magic and the NA scope is called is about communication right I think it with this with this approach hopefully we can create communication with you the red and blue and that's perfect that's it that's that's what we all go right to prove both sides ok another I know things I like a lot about using pen test in your boxes is now we're talking about assume which right meaning that you are your neighbor is already compromised so you have to take the other pouch and look a hand for malware of attackers inside your network so the do boxes is already there we know
we know that so the solution so that it fits quite nicely with a assemblage using the pen testing your boxes now the boxes and I'm in this talk I will focus more for a pen testing a point of view of course because that's what we're doing but people are using the boxes on the wall and here we have a couple of cases I will will go of it so the first one it was a I think was last year and I haven't upload the slices so that's my fault hopefully today or tomorrow that will be up in there and thereby a besides website and you guys Club will be able to Lalo I'll go to the links so but in
this in this him and reddit.com a post there we can read entire thread and they were talking about and they were saya University here in the US I forgot the name which one I think was in California and they found a device there so they and in the YouTube video link there they did our religion earring but actually they took the finger of that device until to analyze to see what's going on so they assumed there was something malicious in this case it was not was the other former student of the university doing a star up so he developed by a couple of the deal boxers and and he put those do boxes across the
university to gather data and that's pretty much what he did bad people but he didn't tell anyone so people when they were finding those devices people didn't know what was that about but at the end was nothing malicious but still quite interesting case now we're moving to more malicious cases in the while that is a case also any in the US that's a raspberry pie with a USB bluetooth an RFID dongle connected there the green light that's the USB dongle and that's had that device this double box was found in the network right and actually you go to the to the link they will then give you much detailed because I think there's there still limit
investigation is going on but and the thing is there and I think in the past day they were saying that only poor people have access to it to the rack and they were saying that none of them did that so they don't know where is this coming from but they found this device inside Iraq quite quite interesting and hopeful and I'm sure hopefully I mean in this case probably will be something malicious we don't know because in the in deposit they talk about it didn't think if any details yet because they still investigate it but probably this is something bad in this case and this is the this device was in there in the rack right quite scary and
their third case even more scary is this has been going on for the last seven month in Europe in Eastern Europe and the different criminal and the criminals have been deploying the idea boxes in different banks and they have still money like several I mean ten of millions of dollars to using this this is for real and you can go to the link and and I think this has been this article it's only one I think it's the only one one month or two month old so that's quite quite new and this is this is happening for real I guess there's not that many cases on the on their on the new media because I don't know if people don't
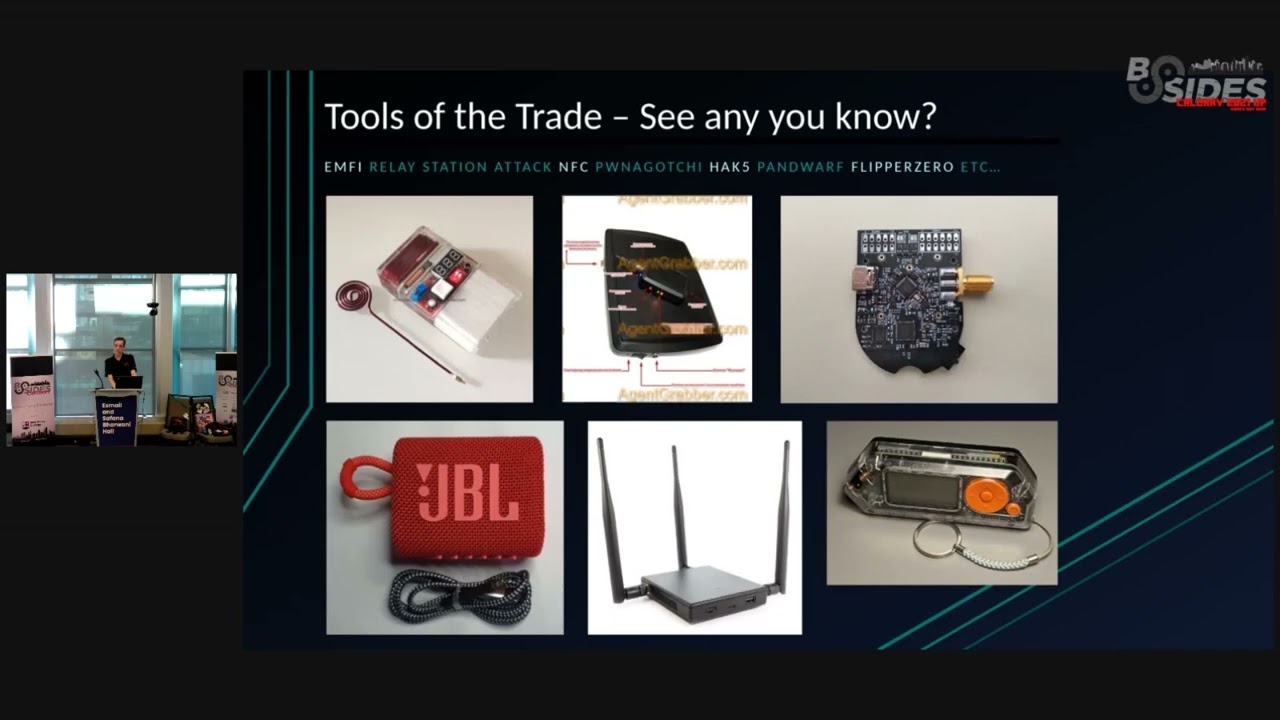
know those devices are there or people what if they find this kind of stuff they keep it quiet probably a little bit of both but this is this is quite interesting because those criminals they were using cheap laptops raspberry PI's and bassanio right zone typical devices P and very cheap so they were buying local jets to make to achieve their objective and making millions so that sounds good and this is for real right okay so now let's move to the to the appendix in their boxes so here are a couple of boxes can you guys say any guesses of this for the devices no guess by sheer oh yes which one now yes okay so the cereal for in your for your left
if they see repeat phi0 in the middle is our Raspberry Pi 3 and then on the on the right it's a all the way c2 and that's quite a night that's all those are small size and if it's a new palm size it's quite quite nice there are powerful love farming family in there Oh - there's they all go see to their house to dig up bytes of RAM that's a small device subscribe need to run that I mean it's not for possible cracking so forget any password cracking here but we can do a lot still we can do a lot of things with those boxes so we have the serial Raspberry Pi on audio AC - right so those are really
nice boxes we can use for for pen testing we can set up those bosses and approve those in a customer right okay so they had five I guess I guess there are more familiar can you guys guess pineapple yes packing square yes so actually packing a pineapple nano in this case a package squirrel and land turtle why I'm showing the hak5 have have more gadgets so many some interesting ideas but those three are really interesting for a for a reason in case you know I I didn't put it here I forgot so that's my fault the guys from hack five yes released last year a web app called a cow situ and you can download it for free and
this actual commercial version but allows you actually sub web app management tool to manage those devices so the ideas you can start deploying those in the pineapple a packager squirrel and an turtle in a network trainer in a customer whatever and with the software they have released that web app the cow see - you can manage those those devices that's quite neat for chapter 4 the boxes and we don't this there is no much ways to manage I mean we will manage but this also very manual mean but this with a with a with a web they have released when is quite nice to manage these devices and they are saying that they will allow more devices not not from
heart five but from others to connect to the today this to this web app as well so that's that's kind of neat if you need more firepower we have a couple of functions here can you guys guess those yes and the one on there right maybe it's a bit tougher that's all well so we have Intel look and that's a so tech Nano those are like bad sides those are real pcs with a lot of power I mean you can put depending of the I mean we're talking here those boxers can go for 200 300 400 depending what you want so why not I need you have a lot of power their operating systems Kali power
security you will do typically the primatte open system Colleen parodies are so quite good to use and now we will just go to weaponizing more interesting and so we can add those gadgets to the dirt boxes and it become more powerful so here I think we'll have 10 minutes what is it going faster I think I have a lot of several things to cover here okay so let's move it forward so here I have different gadgets I use like I wear to one the Cena UD 100 it's a long-range Bluetooth device by nice with those angles Wi-Fi USB cards that's the CLS CSL because you don't know it's a Chinese a Wi-Fi adapter for two point
four and five gigahertz for Wi-Fi need and the only course I think is 2015 box something like that it's quite neat to perform testing then we have our SD ours we can use like crazy radio line rtl-sdr and they RF there are more but those are the u.s. also hack RF is not here but you can also use those to add to your door boxes and you can do more attacks and I will show you in a little bit such that's so all the things we can add more about more attacks to our toward the up box so this is a typical network for a customer and here we will deploy our box hopefully in there in the corporate
network we have the users I mean we can put it anywhere but most chances are we will put it on the who often usually they will not allow us in the surfboard it's celebrating their work maybe probably not so usually we will go with the corporate network but there we have the users cell phones printers wife a access points a lot of things so now we're with the boxers we have we can do all the all the classic or do classics attacks never never attacks using Metasploit and map better cab wherever you want well that's a good day with the different dongles I just show you from Bluetooth Wi-Fi or radio we can do a lot
of radio frequency attacks are becoming quite interesting because not many people are checking that for example we got the blue born we're born is there a Bonavita there that we can exploit and get our children on different phones and we're gonna do much docking we can send commands to our two desktops and we will show you a little bit so there's a lot of things we can do a testing we there's just a lot of a yachty a lot of devices in on the under network that they don't manage people don't know we got also actually we can with the box with our double box we can look for those anti to find vulnerabilities and under whatever
one there right so that's quite interesting so the demos so I have a couple of videos because I didn't work because with the gel-like and everything I didn't want to tell my lack so I will go further them for videos instead of doing life and I didn't actually I didn't bring I don't want to bring on my gear through the airport with the TSA they are not that friendly they've been for a four inch so I guess I will I will I will adapt something we are so I didn't want to get my Ted test my luck so this is a video it's not so in there so I guess I have to move so the first
video show in there yeah this is um there are many ways for champion wouldn't have a bill box in our customers them anyway you can use SSH or DNS for command for command and conquer America I mean come on contour right but when we are doing it I saw two like two years ago oh I I forgot a website but they were talking about the road a tool to use a CNC commands through fewer social networks so that's what I've so I wrote my own my own version so here sorry I have to get you the back so absolutely we have Twitter the answer is there is the deal box FINA in a customer Network I on the on the
right side a Facebook so basically this it works I put a common a shell comment on my Twitter my do box again read that execute the command and send that to to Paul to Facebook so I using those as a channel to say my commands and receive so here is okay so i sending commands there and getting the output and now I go to the to the Facebook to the Facebook and I see I see the results so now that's a easy way I can't I can't command my my do boxes right like why need and I'll come on let's be honest how many how many companies are able to detect this kind of stuff not that many
and here and here and I mean easy quite easily everything is in actually they're both the Facebook and the Twitter I private private accounts but it's in clear text battle actual I can a colossal cyber that use a stenography with pictures these are lots of things I could do to even cover my tracks but here I'm going and going just easily so here I'm using different commands and it's there on the on the on the on the Facebook so it's that's quite it so I send commerce on Twitter executing my do box and then it will be the customer network your result in in Facebook let me say here let's do and here for example I can do internal recon
for example this runner and map looking for boxers I want to I inside the network I want I want to see more boxers I can start attack so yeah so running em up there I got my results results there in in facebook so that's a nice way to command my boxes right okay okay so now let's move to another demo
this is getting weird there okay so now I'm running a kiss net the wireless scanner but we some would that one fast but here kismet if you are using last version of kismet it has a lot of interesting things you can do also Bluetooth and for 400 450 Omega is a protocol there's a lot of devices there so here so here five minutes okay so I guess I have to rush so which is meant here using the different dangles I the SDR diagnose and with Wi-Fi and bluetooth I am able to cover together a lot of devices from from from the customer here we have Wi-Fi the ones in blue are bluetooth there's a supreme
pink in pink those are from usually sensor on different type of devices from from the 450 frequency so there's a lot of things we can do here but first one there so we can have this and garen a lot of devices and many many times happy because people are bringing their own devices and others a lot of stuff we can get a lot of devices in the in the world that people many times it even the security people IT staff didn't know about it and with this way we can start mapping all that so that's kind of that kind of neat okay and the last one okay let me show you otherwise my mouse so this this is a
mouse Jackie not hack so actually this this is worry if you're not familiar with this attack is I can send remote a remote comments over radio 12 to our computer so here in this case I use in the better tap better cap the last version of vertical has this capability now so with use you just need a crazy radio dongle so that that does make resi radio dumpster here connected to our Raspberry Pi and now this is a Windows computer that's we are pretending is in the corporate network there and now what we do with the better cap and trying to take devices you hear when I'm exploiting beside the users has a wireless a mouse a vulnerability in that
Mouse so I'm I'm using that so actually you see here what we're doing is we are using a rubber ducky scripts to inject it into the computer remotely so here I send that command to the computer and I did open this this page right but we can send a lot of all day all the rubber ducky commands subscribe that's kinda nice and this attacks is like I think it's three years old but still I have been fixed by still you can we can see many already devices on on networks and we can display that so yeah so the social networks a common icon RF monitoring using kismet it has a really nice radio and now analysis capabilities
now these days and this is the mass hijacking with the crazy radio dongle right and we can perform remote attacks inject attacks into into the Windows user right so that's kind of just kind of neat so the conclusion is in this case is quite affordable I mean if those devices are quite cheap we're talking around 50 100 150 depends on all the angles and accessories you want to put my usual is quite cheap it improve security defenses because we can do a lot of more testing but would that because many companies are not doing at the moment and this is not just yesterday is only that's one way I mean I just show you a few things
I'm doing but there's more more ways to do for example you go to those resources when I hopefully to later tomorrow when I upload the slides all the slices you can go to those links and here in the BDA labs Black Hills in for security they have really nice links and how they do the Box pen testing so that's quite an aid to to read those resources right and that's pretty much I have for the talk I think I don't know who have time for questions I will be here all day and tomorrow anyways actually I'm here all week for the NSA as well so you want to talk I'm pink just ping me on Twitter
and that's fine but we have time for questions perfect yeah we do actually just want to ask everybody give it up for Simon it's a great chat Thanks do you have any questions from the audience here I'll try to get the microphone up to you if that makes it easy one in the back you're right there hi um how do you if this is part of your methodology how do you actually hide the devices what kind of techniques do you use to make sure that they can get power which is probably the most difficult thing to achieve that they don't look like obnoxiously orange casing well that's that's a lot of talks about that how do
you how do hide your devices in in mouses or in keyboards on printers so like that I usually don't my case I don't the other words the thing I was talking before about cover and transparent I prefer to be transparent I prefer to have that device they know is there and what they think they can do so I usually don't try to cover in that sense but there are many many ways actually there being you look talks they are and I think in the f-con another company have been people have been talking about they put in those kind of devices they iron in in in printers and in keyboards and in our power step power
co-op is really nice you have a lot of space there to put stuff so there are different techniques you get you can use great things we've got another question here that came through the portal Dropbox has shown were 0 pi/3 and blank we're looking for the third one there excuse me we had a question come in through the portal here and writing about the existing drop boxes that you shown on the screen there drop box is shown where the zero is zero yeah that's very pi/3 and they only see two there you have it and one time for maybe one more question from the audience cool if you could just give me two seconds here I have some announcements
to make
so just a couple things here really quickly we've got some t-shirts that are available they can be purchased at the coat-check the t-shirt sales proceeds will be going to a charity of your choice you get to vote with some tokens and boxes over there definitely pretty neat check that out there's going to be a raffle for the folks all you participants using the sponsor passport in your registration bag if you want to visit the sponsors in the sponsor hall there use that sponsor passport and get all your stamps before 11:00 a.m. on Monday winners for that will be announced in the sponsor lounge at 1:00 p.m. on Monday and then finally tonight there's an event going on it's a happy
hour sponsored by sy Barry thank you very much at 5:30 p.m. when check your your guide for where that's going to be going down that's all we have again let's give it up for Simon everybody thank very much [Applause]