Automating Security for the Cloud: Why we all need to care

Show original YouTube description
Show transcript [en]
okay things get started welcome everyone my name is Randy Walker this is the automating security for the cloud talk and I think most of us here are security professionals there's a lot of pieces that are relevant to really everything that we do I work for a company called cloud passage we secure virtual machines running in public and private clouds and I'm excited to be here today to share what I've learned really when it comes to understanding the differences in architecture for security in the cloud the differences in operations and the differences in organizations which is one of the most interesting challenges that we have to face really appreciate everyone voted for this session it really makes it all the more special to
be up amongst peers that were interested in hearing what we have to talk about so let's go ahead and get into it not gonna spend a lot of time on my bio but I am curious and even though I can barely see folks thanks to the lights how many folks have you them as security operations teams believe their own security operations teams up thank you I could see a little bit a little bit only a couple hands what about IT operations teams how many folks are on ite side okay anyone here view them as part of a DevOps team if you've heard of that term actually most that's excellent well this was this title that talk was subtitled
how to get DevOps tool of security so we'll talk a little bit about that what I want to do really is is hopefully educate folks on some of the subtle and not so subtle differences between doing security and cloud particularly public cloud infrastructure as a service versus doing security on prim and a private data center and one of the first places that you really have to look at that is who's actually running servers in those environments and what their motivations are and you know whether or not they care about security and what they're doing we'll talk about the architectural differences why your current security toolbox does not work in public cloud even in private cloud and we'll talk
about the versus set cups the meet of this conversation and really how do we make sure that what a really innovative group that's building new services online how we can keep that safe and prevent some type of backlash against the adoption of cloud due to security thought or concerns or those kinds of things so let's start really and talk about who's running in the cloud and that's one of the reasons that I surveyed everyone at the beginning was because in many cases folks who are running services in the cloud are not necessarily folks that are used to running services on Prem the public cloud especially has made the barrier to entry so low that almost
anyone who has a problem to solve and a job to get done can go and swipe your credit card and spin up a server and that has a lot of implications for security because in the past there have been a number of checks and balances that people have had to go through in order to have new servers provisioned and in order to have new systems brought online but the problem is that even if a IT security server admin has an understanding that they need to worry about security when they move a service to the cloud sometimes the case is that they don't have they don't have the time or the luxury to do that and if for
example they need to stand up a new service and their own internal IT group can't do it fast enough they may just go ahead and rent something out there and expense it just to solve their problem of the day this gets even worse when you start talking about people who aren't IT focused at all but are purely focused on their business problem and big data is another example I think it's it's really interesting how many big data people are leasing servers in the cloud because instead of building out a data center of 500 bare-metal servers they can jump go and just temporarily lease that time you know much lower cost and much lower operational overhead but these folks
since they have a need to solve a specific problem for analysis or analytics or something are not thinking about the security implications and that puts their organization at risk without anyone Sara Lee knowing about it my favorite operator in the cloud though is DevOps and if you're not following DevOps poor OTT on Twitter you should he's as good as drunk coke or better um I'll talk a little bit more about DevOps in a little bit but our goal here today is to figure out how can we turn this guy into someone who loves security and knows what he needs to be aware of when he's still teeing up new services and I'm sure folks are pretty familiar by now
you know what people are using the cloud for and there's a longer list even than this but three major use cases that we as IT professionals need to be aware of you know this it's very common very very common for people to be using the cloud for temporary development resources someone needs a new server they got to get a job done it's going to take too long for IT to spin it up a lot of people are building permanent applications in the cloud can't name you know I cannot name the number of companies within an eight-block radius of this building in this area that are building brand new web services I'm sure that you're all using that are based
entirely in the cloud and then the temporary workloads like I talked about for the big data analysis those kinds of things is you know really interesting use case and fits that cloud operational model really really well you know for the benefit of everyone here it's a bit of a cliche to say but the truth is that very often people don't know their organization is running cloud servers and that they're at risk until they do something as simple as look at expense reports it's sad to say but there are various people out there and very you know in very large organizations who finally realize it's probably not likely that someone's buying a thousand dollars of books every month there's something
else going on and for all of us in this room if we're responsible for security for an organization we need to keep that in mind you still wandering around being routed the podiums interesting so let's talk about why security in the cloud is different because we all have a specific set of tools that were used to using and the more that I've learned about security in the cloud the more the my co-workers have learned about security in the cloud and we have a long history of security experience the more we've realized that the architecture is so completely different that we just really need to rethink the way we're doing security so in the simplest case
let's think about what we've done before where you have a private data center with a set of perimeter protections and perimeter and protections inside that keep the bad guys out and because of that we have over time let our posture inside the data centers degrade I can't name how many servers I've run personally in a data center where I've let non core OS packages get out of date because hey no one's gonna be able to connect to that port anyway or I know all the people that are gonna be able to log on here because I'm behind a bastion server or those kinds of things so frankly we've gotten lazy and that's ok because the architecture allowed us to
do that but what happens when you're in the cloud and all of a sudden you move one of those servers out into public cloud where you really don't have any of those same protections in fact you have none of your company's data center protections available to you in the cloud just because it's hosted in someone else's data center completely and so this is we're taking a server as it is today or any kind of service and putting it on the public cloud puts people at the most risk because then attackers are out there looking for at risk servers and we see this happening every every day where those servers are getting compromised and used for various
nefarious purposes but it's not just as as cut-and-dried as that the other problem is that security in the cloud is very very complex you move a server from public into from private into a public cloud because you want operational efficiencies and you want to make it easier to do things like scale out you want to make it easy to scale back and cut your cost back if you don't have so much load you want to be able to move between servers between clouds to take advantage of the cheapest hourly costs and those kinds of things having spent 15 years building traditional network security products these are the kinds of use as we never considered when we built
firewall management tools and those kinds of things because frankly the idea of a dynamic IP address a server that may go dark and then come back online in a completely different data center was not something that was common if it all happened in traditional security management but the truth is that the attackers are out there and we've seen plenty of evidence of that for example the Sony brief last year part of it was launched from Amazon and these things that there are people who are actively scanning servers in these cloud providers looking for vulnerabilities so traditional security products just simply aren't adapting and it's not that there's anything wrong with them I think that there's a ton of
traditional security out there that's important in all environments but the traditional products are not able to deal with the temporary and elastic deployments the metered usage where people are paying essentially by the hour or multiple cloud environments in that dynamic environment and so that causes risk and it causes concern and frankly at this point most surveys about clouds about cloud adoption rate rates security as the number one barrier where people are saying that I'm not going to move to the cloud until I've addressed the security concerns and I and I can feel comfortable with it so we actually drilled into it a little bit more we were curious you know what is it about security that you care about and we did
a survey of hundreds of IT professionals and got back a very interesting set of parameters lack of perimeter defenses are not and or network controls I don't have my firewalls I don't have my border gateways that's concerned as is why it should be multi-tenancy that's something that people are gonna have to start to realize that though they'll need to figure out how to get comfortable within cloud environments compliance standards obviously enterprise security tools don't work obviously this one's very interesting provider access to guest servers is I think one of the new dynamic area areas in the public cloud that a lot of folks aren't used to there are many service providers that require you to give them access to your server
for various maintenance and operational purposes even if they don't require an account or a login on your machine they have access to the servers that are running in the hypervisor if anyone remembers the Amazon rolling reboot from back in December that was because Amazon patched your servers by going in and actually changing the drivers from under the covers and then they required you to remove to take advantage of that so it's not a bad thing this is awesome because people are able to do this kind of thing automatically but it requires us to think differently about our operational model and about our security model for doing these things okay what about the fine print who here is actually read the
fine print for your cloud provider when it comes to security they will all tell you very explicitly and they're actually very good about this telling you that the responsibility for security is shared between yourself and a cloud provider and so they are responsible for everything from the physical layer the network that compute the hypervisor you are responsible from everything above that and Amazon will say they're one of the best when it comes to making this explicit that the customer should assume responsibility of the management of the operating system and all the data there and they recommend that it's possible to enhance security of those systems by deploying post based firewalls host-based intrusion detection those kinds of things and this is an
important concept because we come back to it and the way that you can secure based on what you actually have control over the problem is the people who are running servers in the cloud you know those IT folks that need to get something done the Big Data folks they don't read this fine print and they don't know that they're at risk and in the old days it wouldn't be a problem because they'd be requesting the server from IT and that would go through the proper security pieces but you know if you ask any business analysts what are you doing about each of the different slices of security that you traditionally have in your in your
private data center their heads going to spin and they're not really concerned or thinking about these things but again the barrier to entry so low that someone can swipe a credit card or even get a cloud server for free these days to run and play with in those kinds of things and you won't know that as a security professional in your organization and that will put you at risk another question in the survey we ran specifically was about who is responsible for securing those cloud servers and this highlights a lot of the confusion out there we're not securing our cloud servers okay at least they're upfront about it that's good hearing that their provider does it for them
that's worrisome because as we just saw they're not you know dealing with open source tools having a manual checklist those kinds of things those things are good but it's not taking you all the way and we need to think about how do we actually create new tools that operate well in this opera in this cloud environment because we are all at risk because we know that there are scams going on people looking for compromised servers those kinds of things and for anyone who's questioning it go look at the SSH logs on your cloud server I can guarantee you people are trying to brute-force that right now so here's where we get to the part of the talk how
I learned to stop worrying and get that Bob stool of security who here knows what DevOps means okay great gentleman up front so DevOps is a you know it's it's an emerging term in the past has been called automation engineers systems engineers people who keep the site running but also have a big part in actually building the site and me and keeping the site reliable and those kinds of things so something I've done in the past very often where you're the only person out there that's responsible for what you're building and it's you know it's it's a popular term right now but honestly the cloud has made it very easy for people to build awesome new services with very little
organizational structure you don't need an IT team and a programming team and a QA team it can all be the same group that's making things happen unfortunately they're separate from security operations there's very rarely a security slammed on these and that causes a problem but the question is why is DevOps a popular term now what is it about the cloud that they really love for getting their job done and that's simple it is easy the cloud is so simple to spin up a new server BAM bring down some servers BAM install a whole bunch build a whole bunch of new machines through some scripting or a recipe kind of thing BAM hit the button so people who have tried to automate
security in the world free from you know physical machines love infrastructure-as-a-service you know public or private because they could just go and you know automating scripts creation of servers aren't bringing that up of servers bringing down of servers putting your server on software and servers those kinds of things but the challenge for us is that we have different goals in our jobs so the DevOps folks are building stuff and I you give a shout out to our community manager up in the audience she had a great example of this where the security people are looking at solving puzzles and they're trying to figure out how things work as a security person this foundation would drive me nuts I can see
that falling down in a second I just I could not handle that kind of piece I'm much more interested in figuring out how do we make that entire structure safe and how do we make sure that it's running in a good environment but for the DevOps folks that's not what they're thinking they're thinking how do I keep things running and they love the cloud because they are sick of waiting for slow icy operations services in order to bring things up so let's do an example so you know coder Hank is trying to tilt up a new service and so he's waiting for server provisioning so you know he files a ticket someone picks it up they get
this they get the information you know maybe they got the server in stock maybe they don't eventually they roll in some new boxes but they're not done and so DB admin Dean is out there waiting for the firewall updates because until you actually update those policies those new app servers can't talk to the database servers and so you know provisioning of a few machines like this and data center Helen said take days weeks months sometimes on average it's about six weeks where is someone who has you know an automated infrastructure-as-a-service login can do in about six minutes so you can see why people are really interested in this model but when something goes wrong say
there's a server crash or there's an issue on the site okay now they're worried they're gonna go make some tweak on that app server that they're not going to tell you about they're not gonna go back and reset they'll maybe change you know ssh logins or something like that that's when the bad guys get in compromised that server and the reason we have these two layer networks is because if they've compromised the front-end server in the dmz we don't want them getting back to the database server so the traditional data center architecture has kept us safe to a degree even though it's slowed down business and operations you move this out to the cloud all that goes away all
these servers are now basically sitting naked in the sky and you have to be really we're really worried about what goes on so what do you do so this is the you know hopefully an educational park for folks that are responsible for to secure in servers in the cloud first off you've got all these servers in the cloud you need to make sure that those servers are always up to date you need to make sure that you always have all of the patches that you always have the right configurations on those servers and you need to do that religiously probably twice a day vulnerabilities are published so quickly things change so fast that if you're
waiting once a week to do a system update you will get compromised and believe me there are people out there trying to compromise your servers in the cloud right now the other thing you're gonna do is you're gonna think okay so I've got these servers they're you know they need to be secure I'm gonna be able to put firewalls on host-based firewalls work great I can make a little strip that starts set up and I can communicate between these servers that makes a lot of sense but think about the cloud operational model think about what happens when a new app server that has to talk to the load balancers in the database server think about when you add new load
balancers new database lives all these things make it essentially an exponential set of relationships you have to maintain for those firewall connections and that's very very complicated and it's something we never had to deal with in the past when you had a single choke point firewall or maybe two layers of the DMZ you knew what was in back of it you knew what was in front of it and you set those connections in a very static way right now these servers will be here one of them will go down very common servers in the cloud crash or they or they get taken down those kinds of things that IP address gets recycled very very quickly
and it is very common for an attacker to jump in look at that IP address and immediately scan every server around them looking for vulnerabilities this is very very common how people are getting compromised in the cloud you have to be aware of it so how do you deal with something where you don't own everything how do you secure something where there is no steady state there's no static IP as those kinds of things how do you handle the very variable workloads how do you make sure that your system is not bogging down and costing your company a lot more because in the cloud you are paying by CPU cycle effectively and how do you make sure that this works not
just in public cloud but also back in your private data center because if you're taking advantage of public cloud right now you will eventually hit the cost curve where it's cheaper to bring some of your servers in-house and you will soon be operating in a hybrid environment so our tools are broken everyone hates us now what so gratitude to the memes out there but frankly we got to secure all the VMS it's really about what is the one thing that you can control what is the one thing that you can can secure and how do you keep that under lock and key so that you can still take advantage of the operational models of the cloud and give the DevOps folks
what they want but you make sure that those things remain safe so my thesis is that you have to focus on the VM we are moving back to a world of post based security because frankly you don't have access to the network so you can't do network based security so we have to think about post based security and we have to think about doing that in a way that handles the dynamic nature of the club it's not just you know an agent that runs here that's always going to be that same agent on that same server you need to realize that the VM that you can control is the thing that's going to get cloned and so if it's scaling out at
your public cloud or it's the thing that's going to move if it's moving from the private cloud from the public cloud into your private cloud doing something hybrid the VM is the only thing that you can count on controlling in all of these environments and so that's really where you have to focus your efforts when it comes to security so in the cloud environment or folks on the video maybe don't see all the details the intersection of control Portability and scale is always the guest virtual machine and it's painful to a lot of security people in the past you've tried to stay as far away from the machine as possible but it's what we're gonna have
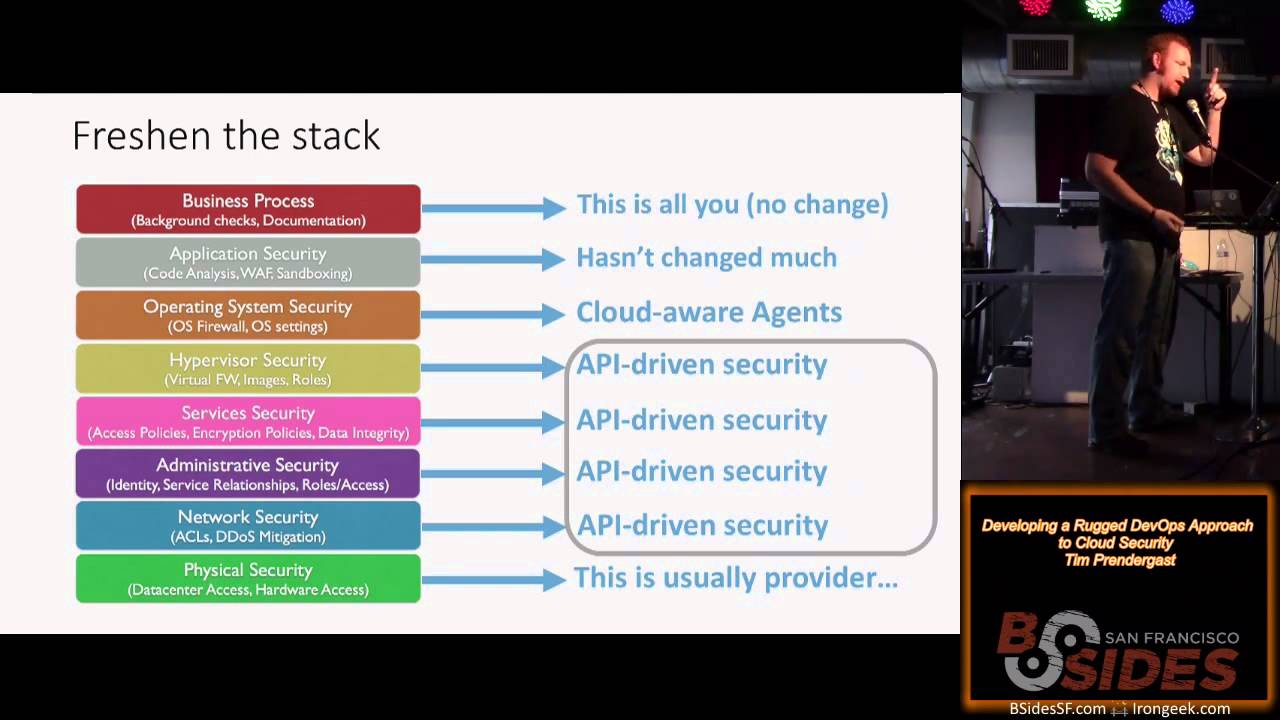
to do so what do you do so what you need to think about is look at that stack got a virtual machine so can you touch the hypervisor remember we are not even able to touch the hypervisor in public cloud so you've got to focus on the OS the Linux distribution your Windows Server out there there are lots of Windows servers out there and you got to worry about securing the OS make sure that all of the software is up-to-date make sure that it's configurations are locked down make sure that if people don't change it or that if they do change it that you know it and you can change it back immediately that requires extreme
diligence on the part of the security team you're gonna have to add post based firewalls like no two ways about it even though for example some of the so Amazon's an example it has a inbound only firewall security groups not PCI compliant doesn't work across multiple Amazon clouds in the different those kinds of things you're going to have to add and maintain post based firewalls you're gonna have to watch and make sure the application stacks are up-to-date I can't tell you how many people have talked to that their entire company has gotten compromised because someone found a vulnerable WordPress server it's very very painful but it's very very common because someone in marketing hands up I'm in marketing
someone in marketing went and actually put in a WordPress server but then you know was popped and then if they were able to get inside the private data center from there watch the application code so beyond verification of what the the developers are putting out there and doing your tech your penetration testing on those make sure that that code doesn't change verify the integrity of the source files and everything that's going on in your stack because it's a very dynamic environment and you can't always be sure that someone hasn't made a backdoor without you knowing and then obviously track the sensitive data and prevent egress so you have to think about all these layers but now you have
to do it from inside the virtual machine as opposed to outside which is what every network based hypervisor based solution has ever done and those just don't work in public code the challenge now is you have to automate it it's not something that you can just fire and forget and put pieces on them you have to build out a system that's going to fully automate all these pieces because those servers are gonna get replicated over and over and over I was debating with myself last night how many times I should replicate this out but I tell you I have seen people that have won gold master server and they have spawned a thousand clones of that the original bug
that was on that one master server the original miss configuration extended through all those thousand servers the bad guys love that because if they get that they can compromise one of the early models versions of that then they're gonna have their Trojan on every single clone that gets created but you also have to do this separate from the actual server operations because I can tell you the people who are building the sites that people who are running the services are not gonna stand for them having to take care of respondents security response or for you getting their ways on pieces so you have to figure out how can the DevOps team still have access to all the
application code modify the frameworks all those kinds of things but how can you on the security team keep track and management of all the different pieces that go into keeping that Miss that system secure so that's really the high-level ideas of what you want to do in the club and hopefully after all that you end up with this guy you know someone who's really really happy that there's a really strong team watching they're secure you're watching their security I heard someone says want that shirt off take a note and make some of those that we go so in the head of time here which is good because I'm hoping there'll be lots of Q&A and discussion and I was told
there had to be one cat in every single presentation ok so who here is responsible for securing cloud service to some degree yes good amount of people so that is you know what we all have to keep in mind is that you have to defend those VMs you have to automate all of that security and you have to worry about the firewall controls you have to worry about the vulnerabilities and the software the configurations you have to worry about the integrity of your code you have to worry about who's accessing those servers and here's the the graduate level course you have to figure out how to automate and integrate all that into your on-premise security
systems which becomes even more complicated if you have compliance to use for example so it's not an easy problem a few tips I think it's really important so you do need to realize even if you didn't raise your hand there are people in your organization using the cloud and they don't understand security and they do not know their responsibilities so for every single person here go back to your organization your company even just your team figure out you know who's stuff in the cloud and make sure that people are aware of these complications because otherwise your company is going to get in trouble you're the the clouds actually gonna probably take a black eye is some major compromise this happen out
there and people just don't understand the difference but as we mentioned the bad guys know this so the risks are out there and the risks are great and we need to worry about it so think about how can you leverage that new architecture how do you actually take advantage of the restrictions in many ways to create a new and possibly even more secure environment out there so know who's running what go and find them read and understand what your provider does there are providers out there that do some security pieces but they will be very explicit that they don't do a lot of the stuff that I'm talking about be very very careful if you're gonna take
an existing server and move it externally that's probably one of the biggest problems where people get into the most trouble if you start with a server you built in the cloud at least you're starting from a fresh image if you take an old crufty server out of your private data center and move into the cloud that's where things really start to worry but here's the best one and I think that and someone else has said this and it just really makes sense that if you've got to figure out how to use cloud you're going to start with the public cloud because due to the restrictions the fact you don't have hypervisor access you don't have network
access once you solve the problems of how to secure the public cloud everything else is easy you can move those systems back inside you can do hybrid all these things you can move providers so find the most restrictive environment that you have to solve the problems for and start there and then it's gonna be really easy to do all of your future cool stuff and focus on what you can secure and what you can control so we're gonna have tons of Q&A I do want to call out that we will post these slides on community cloud passage calm hope to engage folks in conversation there I'm available on Twitter gonna be here at the show next door and be here
all day tomorrow and we're hiring we're looking for security and cloud experts and really interested in talking to folks so I'll leave this here and see his anyone have any questions please we're gonna need to use the mic so the folks on the stream can hear it
you mentioned that when a server goes down or a VM goes down in the cloud that IP is reassigned and you seem to say that's a point where hackers could jump in I didn't understand what would allow them to do something that they couldn't do before just because the IP is free for a moment or reassigned great question so I'll actually get back to that slide specifically ok so if you if one of your servers crashes or even if you just take it down so again the dynamic nature of the cloud you're you're scaling up you're scaling back all the time when you take that server down in the public cloud the IP pool is
shared and your private data center no one can have access to that IP except for you but in the public cloud that IP address will be recycled and reassigned to essentially the next VM that comes up there's no distinction in this cloud you know the green blue and dark blue servers may be yours but there's no distinction of the thousands of other servers that are running in that same cloud in the same subnet and so it's very common and we have seen it where an attacker as soon as their new server comes up they'll actually cycle through requesting new servers constantly as soon as they get a new IP they'll scan in an outward motion all the all the
servers that are near them looking for open ports that were open to that IP address that just went down does that make sense so that your server is going down and you're taking it down and then they're sneaking in there trying to take advantage of those open firewall ports would you you know you've done the right thing you've secured your servers and everyone thinks about this is where everyone you know gets tripped up because they think oh I can automate my firewall table rules and just tell my orchestration system new servers built up I need to add that rule in but they don't think about when servers go down and more importantly they don't think
about closing that port up you know within seconds so when that server window yeah quick follow up and then we'll move on questions can I create a service level agreement that says I must have just this range of ips and you can never do that anybody else is that ever done that so I could prevent this you can you can request a specific block you can actually request a a private cloud and you'll pay through the nose for it so yes you can do something like that it's like running into a private data center and you'll you'll pay through the nose for yes thank you all your blue connections here in the primary data center people who can use not encrypted
connections between machines I think everybody should actually know that they should yeah because so if a connection comes in and they have server went down basically and comes into the data base server which is everybody needs to know
it's a great comment I'll follow on with that so his point is that your traffic is fairly exposed here and you need to make sure that you're encrypting the actual data going over that piece and that's that's a great second step you also need to make sure that when for example you know your app servers trying to talk to your load balancer that they're authenticating their both the right people because you don't have control over the IPS which has been traditionally how we've identified what servers can talk to what servers and these change and so now you're moving to much more of a machine-type you know policy and group based enforcement Thank You great great problem others please
yes or disadvantages between building in ongoing patching on an instance like persistent patching and updates on instance versus doing that patching on the gold the gold master and then just simply destroying instances and creating great question so you've obviously got some experience running servers in the cloud so what this gentleman just described I don't have a slide for but maybe I can I can demonstrate through interpretive dance patching in the cloud is kind of it's something that's becoming passe there are a lot of people out there some of the most advanced cloud using companies will say that they never log into a machine and patch it because what they're doing basically is they've got a gold master that they they
keep up to date and instead of patching running servers they'll just knock those servers down and create a new server from the gold master image that the model that you've seen right so this question was what's the advantage of doing it one way or the other because there are trade-offs so off the top of my head one thing I've seen is that it's never taking down your entire fleet and and restarting from scratch so if you've got a big security issue you put that in or it's not in a big security issue if you've got a normal patch you'll put that new gold master image and then just week by week old servers will age out
and new servers will come in again bouncing your entire fleet that's a big deal and people don't do that regularly so one risk is that you will have a very up-to-date gold master image you'll have some very up-to-date very secure you know instances that were just launched this week but you're gonna have some that we're launched two weeks ago that are a little bit crufty three weeks ago that kind of thing I dare you to categorize all the software running on and all the versions running on all that's all those versions and no you know if exploit just came out is it still possibly even though it's not on your gold master is it still possibly
out there so it's absolutely the operational model that I think people are - and the idea of doing you know live patching of servers as they're running is becoming as I said passe but the truth is you still have to be very operationally aware of what's running so that you can prevent those types of compromises great question questions comments insights clears might
or if you want to come down for the mic er we can reach up there
hi you mentioned in passing that yes I maintain you have to watch your code and make sure don't put a backdoor in there is there some special saucing out in the cloud or still tripwire every five hashes there auditing all your code so it's still the same kind of thing where you have to watch the integrity of the code but the problem is that most of those tools don't work if it's not something that's gonna get tripped up by the dynamic nature of IP is changing it's something that's going to grind your servers so much that your per hour costs are gonna go through the roof and so I'm not here necessarily to to say
what solutions are out there to solve my company has some good great solutions for solving these but the problem is that traditional approaches simply need to be rethought and that's really the challenge for all of us is to go back and reassess okay we're using the cloud we're all really happy about that oh it turns out our traditional tools don't work now we have to rethink what's new here if I at least encouraged to go back and reassess what you're doing in the cloud talk to folks on your teams couple okay I jump here stuff other questions sir yes cloud passage oh great question so you know it's called passage what we're about so we said we secure servers
running in the cloud we do very much all of this we automate post based firewalls we have intrusion detection vulnerability scanning all those things on your servers built for the cloud specifically we're a team you know that between us have more than a century of security experience and when we looked at the looked at the the nature of this infrastructure as a service world we step back and we realize that we're gonna need all those security pieces but we have to rethink the platform by which we deliver those and so encourage you to go check out the website it's actually free for up to 25 servers and you get all the security functionality there and it literally takes less than five
minutes to set up so please do check out question over there
yes yes so question was how do you automate security in the cloud and that's actually that's really the trick so the I'm not gonna get into secret sauce on what we do but there are a lot of tools out there that people are using for automation for building servers running servers deploying software those kinds of things the trick is for security people to look at is what are the things that those automation tools can really automate that seem to give you security so a lot of tools can create new firewall rules for you for example but those same tools are not that good about tearing down old firewall rules if a server goes away and
they're definitely not run on a real-time basis so if you're using chef puppet those kinds of things and you may put server groups in and say build me an IP table rule for something like this they are not going to go and tear down those rules in any type of a time frame that's gonna keep you secure from that attack so you need to find something out there that's gonna help you do that that's gonna get the right security posture
yes let's go get that mic over
so even in the environment where you're using a gold master or to go configure all the things out of that cloud how do you handle the inevitable conflicts in control over configuration management that you've got between your DevOps team on your security people or whoever else is working on there's something you've talked a little bit about it here yes more like more than anything it gets to be an organizational challenge because and this is this is why I believe I have a previous slide that friend of mine Chris Hoff who's who borrowed from another book about the security sine wave of pain and how you know we are so 10 15 years ago postmates security was
the gold standard but then we decided that organizational structures wanted to give the security teams out of the development teams hair and we move to network based security that works you know there's a lot of things you can do in the network we're back in a world where you're gonna have to do host-based security but we have to do it differently than we did it before post based security previously was very labor-intensive both both for the security team as well as the the operations team and we have to figure out in this cloud environment which is much more dynamic how do we do that in a way that you can separate those security controls so that's hopefully the
developers don't have to realize that they are being secured but they are watching what they're doing we're locking down places where necessary and we're staying out of their way and that's new set of tools that can help do that is I think what's really valuable where is that danger question ok we have time for one more minutes ok yes
now actually a question how many well maybe customers have you seen actually embracing this kind of new paradigm in developing an application well not everything is actually a lot just on one have some and they disappeared the application over several services which actually kind of has two effects one effect is that they kind of waive their tech surface because Wong Jing's up but by distributing the important and sensitive data over several hosts basically it basically also makes it harder for the attacker to find the right information because it's distributed over the cluster and if you take for example whatever they do you maintain a for example distributed over a cluster of several danger databases where only one database handles just a
tiny shot of that full system 16 digit number for example it kind of becomes smallness let's say not impossible but hard to actually get the data they want and they have to kind of understand the application itself before they know how ok have you seen those customers I've seen a few and they're very far ahead of their time at the moment but nobody actually preaches and kind of educates there so if I can paraphrase you're you're wondering is it common for people to think about essentially distributing their data and applications across multiple servers so that they're limiting their exposure on any one specific big server yes I have absolutely I have seen some people doing
that but I've seen as many people not I think it's so there's there's a subtle question in there about risk management which is the end of the day's security is about and your risk of that one individual piece of data getting compromised versus that the larger set it's a little bit of a fallacy and I'll give you an example this this has come up very a lot recently where people may distribute their database server their database data across multiple servers if one gets compromised there's only a subset of records you only have to pull out an advertisement for 10,000 customers in the local paper that they're compromised as opposed to a hundred thousand but on every server
especially in the cloud there is very often a piece of sensitive data that gives you the keys to the kingdom your Amazon API key is disturbingly at risk if you're using s3 for storage for example or something like that and as much as you might distribute among servers and your cloud or in data distributed data in their services there's usually that one or two golden nuggets on every single server which is the first thing the attackers are gonna look for because that makes it a lot easier to go and get the rest of your systems essentially so it's an interesting idea I think that I think we're still in the beginning stages of cloud security cloud itself didn't exist
five years ago and the infrastructure as a service world is really very new many of what many of the things we've done are the core pieces of security there's definitely an interesting new world talking about the data and how you handle the data in the cloud those kinds of things so it's gonna change pretty dramatically in the meantime I would recommend people not just look at what can I separate you know from my servers so that they're not at risk but I take a broader risk management view of the world which is what a good security person should do and figure out what's my highest exposure whether it's you know the data that may be on one server
or multiple servers Orbitz set API key or those types of things good question if we have any questions online or on the clear
so so please do if you have questions later on more than happy to talk online [Music] again community club passage calm ran whacker on twitter be here all day got raffle tickets and bouncy blinky lighting balls - there we go so if you want to talk more more than happy to thank you very much [Applause]