BSIDESKyiv 2018 - STANISLAV BRESLAVSKYI REVISITING SUPPLY CHAIN ATTACK

Show transcript [en]
Hello everyone! My name is Stas. I work in one of the security startups in Lviv. I mainly do pentesting in various manifestations of it: web, mobile, infrastructure pentesting, social engineering. Today I will tell you about such a class of attacks, which is generally called supply chain. Everyone probably heard last year First of all, I want to ask, are there many IT workers here? Developers, testers, DevOps? Raise your hands. Most of them. Great. Why I wanted to make this presentation? To raise the level of awareness in basic things that we encounter every day at work. I will not really talk about all these things that are now on the slide. I will tell you a few cases that I've been working with them
for the last 4-5 months. What is a supply chain attack? If we translate it, it's an attack on a supplier. We put a CCleaner, and from the box it goes to the backdoor. This is the story of the last year, as far as I remember. The company CheckPoint has found a few dozen Android applications recently in Google Play Store, which were considered legitimate software, but in fact they were backdoors on your phones. Everyone remembers the story of when in the accounting software they found the virus of NotPetya. And recently, after we bought the laptop, we already have Meltdown and Spectre from the box, which will be told later today. This is so centralized in relation to the
supply chain attack, but the analogy is followed. I'll start with a small FAQ that we had. Today we talked about such a great tool as Burp Suite. If you don't know, it's the main tool for testing web applications, working with HTTP protocol. It's designed for penetration testing. If you are working If you are a developer or a tester, you have probably seen tools like Fiddler, or HTTP Proxy. This is basically the same tool, but there are several add-ons, well, not several, but many, that just make the pen tester's work easier. So, we have a small company's infrastructure. We have a pool of students, who we prepare to become pentesters, developers in security projects, etc. I had a training for them on
this toolz for an hour. How to configure... Toolz is not configured from the box, it needs to be configured somehow, add some add-ons that make it easier So we have a training, I'm doing it, it's been 5 hours, I open Twitter, and it turns out that the version of Burpa was hacked on the same day I had the training. They found a backdoor, not a backdoor, a dropper. PowerShell some file from somewhere and executed it on the computer. The problem is that I have a purchased version of Burp. Students do not have a purchased version of Burp. I wanted to show the features that are in the paid version. So I said: "Go to the trusted channel in Telegram and download a Jarko from
there and run it on your computer." I'm a great mentor and I didn't say that you should run untrusted software in virtual. So, it was all in the corporate network. Not exactly in the corporate one, in one of the subnets, but still, 11 am, I understand that only students who had windup installed this thing. We started the incident response right at night. A few students almost broke their computers out of fear. It was terrible. That's how it all looked. We come to work in the morning and think, damn, we need to reverse this thing here. To disassemble it, look at the source. As it turned out, there was no virus there. This Telegram channel was
trusted. It is still trusted, you can download everything, you can run everything. But the point was that some dude on one of the forums, every time a new version of Burp comes out, in a couple of months or weeks, a cracked version comes out. And he posted it on some forum, a couple of dozen people downloaded it, and someone of them decided to disassemble it and see what was inside. He wasn't infected, so we exhaled and started sleeping calmly. But we had a little shake that day. This is also a supply chain attack, because with the same success on that Telegram channel We could have put the same piece of code and we would also have backdoors in our corporate
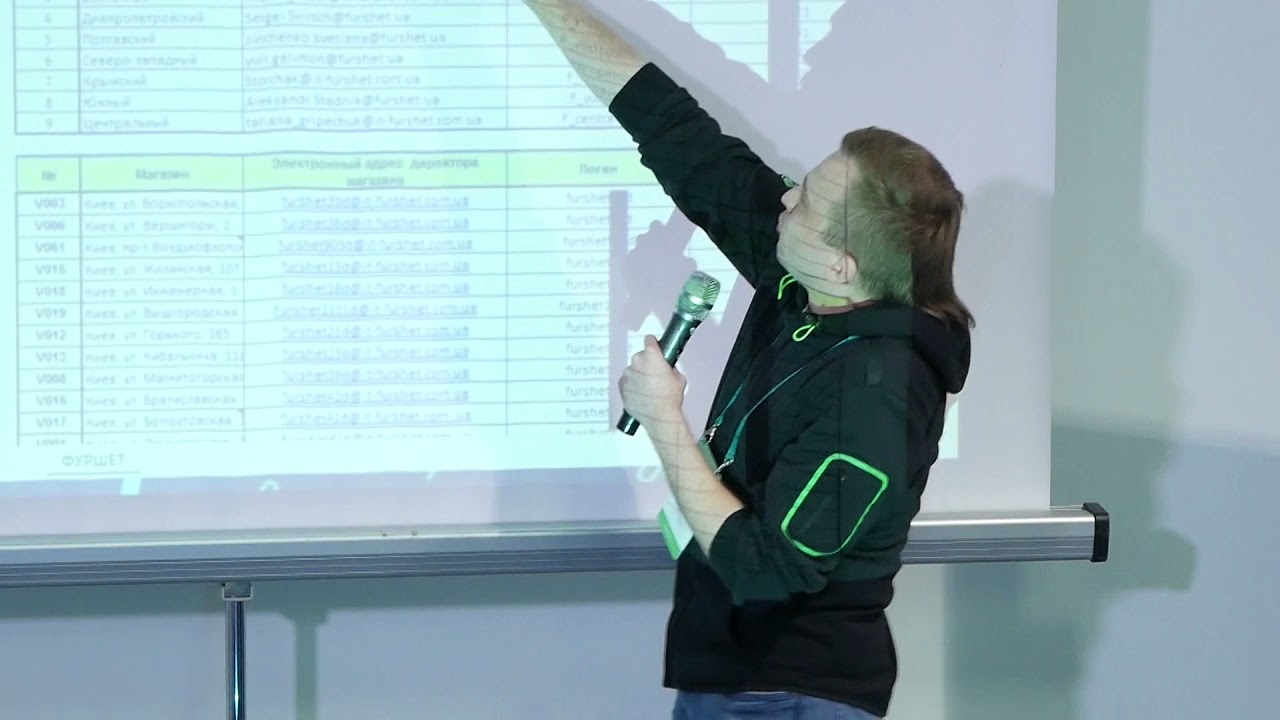
system. Why were we so scared? Because that same evening on the same Telegram channel they threw out the same news, said that the guys are not installing the last JARC, because there is a virus. As it turned out, no. This is the first case. The second case. We recently had a project related to, let's say, if you conduct an infrastructure penetration test, then the first phase is to collect information. So, we had this whole project in the collection of information, what we can find on one streaming service of sports events. Not this one, I say right away. What can we find on the Internet? What is the compromise? What documents are they showing? Are there their emails and passwords in the drug bases?
And so on. It was, as I said, a streaming system. They had a very, very well-drawn IT infrastructure. They stored client data, personal identifiable information, they stored credit data, because you had to subscribe to the subscription of that streaming system. And they already had a story when they had a breach and client data leaked. They had a request that it should be absolutely such a safe pentest where we do not try any exploits we do not climb them on web applications in short, we do not touch the quotes so that nothing falls there, do not do an application dos and so on and so forth purely collection of information after two weeks of the project We found in them a
very, very well-drawn IT infrastructure. This is a lot of DNS entries in DNS tables, in DNS records, a lot of IPs. We looked, or rather found their Amazon instances. It turned out that everything was fine with Amazon. We tried to find some open buckets there. There were a lot of customers in the database of these drugs, more precisely, their employees' passwords and emails. We also found vulnerabilities that are quite easy to exploit in their instances. It's vulnerability in their servers, in services that they have opened for the whole world. And we also found a lot of Ukrainian data in Darknet. So, here's what we found. More than 600 DNS records that are connected to this company in some way.
More than 100 different IP addresses. A few dozen IP-shops, which had, as I said, impressive services. More than 100 corporate credentials found in recent leaks. Remember, there was such a leak with LinkedIn, leaks from various dating services. Many of their employees were found there. And a few dozen, more than 60 pairs of client client credentials to their streaming system. They were working. What is the point? Where was the third party? We uploaded an assessment report. We conducted a demo. We showed the essence of the benefits. We scheduled some next steps to improve their security. But they said that most of what we found These IPs belonged to third party providers that configured them. Some third party company that runs some
web applications, servers, etc. for them in Amazon. This case was half a year ago. And to this day They haven't done anything with it yet. And there are still vulnerable services on the Internet, Apache 2.2.2.2, and so on, which can be hacked and installed right now. The point is that they didn't even want to deal with why they don't have responsibility. They said they will notify, but judging by everything, that's it. Are there any questions about what I'm telling? No? Then let's move on. Recently we had a project with a mobile messenger. It was a pen test of an Android and iOS application. It was a messenger in the Middle East, which is now actively used. They
have their own private infrastructure. As they said, they do not store any client data on the server, and this is considered security. The fate is that when we started to drive traffic through the same Burp, we saw some kind of header. an authorization header that did not come from the server, it was not like a hook that is authorized by the server, it was generated on our phone. If we took this hook, the request would not pass. We disassembled the APK, looked inside, It turned out that this authorization header is generated based on all the data that is stored on the phone. This is an ID of the device, this is a post, post, body, post message, quite typical, timestamp and
some other data, I don't remember exactly. So, all this is combined, hence the hash function is calculated, this is a unique print from some string. and it is sent as an authorization header. The server takes this post, takes the ID of the device, the timestamp that also went in the headers, pasted it on the server side, calculated the hash function, and it works perfectly. So far, there is no reason to be angry, because we are not even logged in on the phone. The first request we made through Burp already had this authorization header. We haven't tied it to our phone number yet. So we found this APK, or rather we disassembled this APK and looked at There, when you log in
to Telegram, you have to send your phone number, you receive an SMS, you send it, you are logged in. There was the same approach. There was a third party, they have their own website, you can buy it, connect to yourself, to the project, we go to this website. There is blockchain, AI, SMS, everything. And it says security there. What could go wrong? The point is that so far we can't even... We are not even logged in yet, but we can already sign our HTTP messages. Sign, calculate this hash, calculate this unique token with which our our post headers will be processed somehow before we take the authorization header the server cuts it off and says: "Dude, something went wrong" Now it takes this post
and then calculates something So, in the first post when we connect our phone we have our phone number, our geolocation, etc. in parameters And there was a very interesting parameter called "authorization type" as far as I remember. And it was standing... The value parameter was "phone". What other parameters can there be besides "phone"? You can't enter an email, you can't do anything. So we took this parameter, we calculated our signature. The server sent a fake signature, saying that there is no one inside, judging by everything. He took these post parameters, took the authorization type parameter and saw that it was empty there, and said: "Dude, there is some mistake." Valid parameters are phone, silent authorization, whatever it
means, and there is something else that we did not understand what it means. But what is silent authorization? It turned out that you could connect your phone to any phone number. If I have a phone and I know that you have this app and you use it actively, I choose the authorization type silent, send a request to your phone number, you log in, and I log in. under your name and I can carry on social engineering, for example, under your name I can send any messages to your friends. And the essence of the project was that As they said they don't use anything, they don't store client data on the server, they were very interested in the client attack. And
it turned out that they had a very good source code, that they wrote themselves. In addition, they had problems with SSL pinning. All these problems started when they bought this side library and used it because it was written "secure" But they were really cute because we delivered them the assessment report, told them everything They took us to the library with these guys, we helped them fix this thing, told them about HMAC And they are just awesome. And what can you do with such a thing? Are there any ideas? I mean supply chain and so on. I mean how to fix this problem. It's me who will earn. In fact, it looks like the next steps look like this.
You can't do anything with that thing. It turns out that you can't trust anyone in this life and we don't know what we are doing with it. In fact, no. In fact, you can. First, you need to adequately assess your risks, where you can get into trouble. If you use some third party LIB, or third party service, or some provider, The easiest thing to do is to ask them for a piece of paper. It's either about conducting a third-party pen test or some kind of compliance. At least something. How do they defend themselves? For example, in Tilib, it was written "security". But the main question is how you defend yourself. They don't answer anything and it's clear that something is happening there.
Don't expect to be hacked. You will be hacked anyway. So it's better to think about it from the beginning. Now every IT company has a position like Information Security Officer, or something like that, who will calculate your risks, who will tell you what to do here and there, if you are an adequate person. Ask your suppliers for papers, as I said, conduct penetration tests, conduct security awareness trainings for your employees. Even a simple security awareness training will help you to make at least one person think when they will write a code and use some third party LIB of some unknown guys, who have written "security" on the site, that maybe you need to look at something there before buying. As
I said, you will still be hacked, so you need to have an incident response plan. What to do, where to run, if something happens. As in the picture, guys are running in a bomb shelter. It's the same. You need to find people who will help you right away, and not think post-factum what will happen. If you have some data, then you need to assume that this data will go somewhere, and a data breach will happen. What will you do with it? If you have some compliance, If you are responsible for some compliance, you may have problems. While I was driving here, I remembered another case, which happened a little earlier, a year or a year and
a half ago. We had a project where we conducted a full-scope assessment of a very famous company that supplies gasoline. You probably drive by their gas stations here in Kyiv every day. And one of the components of this assessment was the physical component, when we had to come to the office or somewhere, look for someone and get some corporate information or get access. And the simplest for us was the option when we came to the gas station We thought what we could do there. So we came to the gas station, introduced ourselves to their IT support. Before that, of course, we called them and said that the IT support will come now. And here was one nuance. The third company
was engaged in their IT support. It was a company that was engaged in the management of their IT infrastructure, admins. And they had a self-written password manager. What could go wrong? When we arrived at the gas station and introduced ourselves as IT support, they said that we had some strange activity on the car. Can you show what's going on? Our friend said that everything would be fine now. He took us to the laptop, to the computer that was standing there at the gas station. opened... I don't remember exactly. It was some kind of web page. Yes, it was a web page. We saw where he was going. It was this third campaign I was talking about. He
entered a password, but the point is that it was a very simple password. We didn't even see him, we saw his hands moving on the keyboard. It was like QWERTY and the next row, but somewhere in the middle of the keyboard, from top to bottom. We came back to our office, went to this web page, and from the third time we guessed this password. And it turned out that we have access to all the computers that were on the gas stations, and they, in turn, had limited access to the internal infrastructure of the company. Basically, I have everything. If you have any questions. Questions? Who has? I have a question. You said that in the case when we looked that
in the middle there is no man in the middle. How does it happen? What tools are used? No, we didn't see that there is no man in the middle. The point was the authorization header in that It was not like HMAC. HMAC is a Hash Based Message Authentication Code. When we guarantee that nobody replaced this post request. Since they had their own implementation, the message came, it calculated the authorization header, If you failed, it means nothing was changed. There was no secret meaning. If you were replaced, you would have a wrong hash. I see. Thank you. Any more questions? I understand that everyone is hungry and wants to have lunch. Let's say I want to become a pentester, or
my fighters want to become pentesters. What should I do?
Choose a specialization, for sure. In the sense that there is a web, there is... Well, let's say, it's a pretty blurry thing, penetration testing, because you need to know reverse, you need to know mobile security, you need to know web application security, you need to know more or less about networks, you need to know how to work with exploits, not just protect them, but understand what they do and what. There are a lot of places to dig. The main thing is to start. And from what? For example, take the web, google "hacking labs" or something like that. And these will be some interesting VMs that can be exploited. There is a cool thing called "hack the box". You
go through a small challenge, log in, register and there you will have access to an impressive environment. It's 20 impressive IPs, I think. And there are different things. There are tasks like CTFs, puzzles, there are tasks that are more similar to corporate environments, there are tasks on the web, well, something like that. And if you talk about your team, do you have every person from Switzerland or does the team consist of specialization of each? We have a difficult situation there, because one came from But he was 15 years ago, he was still breaking some routers at home. For himself. And then, after 10 years of QA, he came here. I have a background in development. I first worked with C-Suite
and JavaScript on one networking solution. Which helped me a lot in life. Some of them came from the administration, some from Black Hat. Thank you. Yes, Sergey, yes. Thank you for the report. A very quick question. What tools do you use to list domains? Well, DNS, reverse DNS records. Let me remember. There is such a thing as view DNS. This is not a tool. a database for many years and you just enter the keywords, like the name of the company and it looks for the last 10 years in the description in Huiz what was connected to this company. There are various harvesters, what is in Kali Linux. specifically for case selection. Because here, with the project I told you about at the beginning, there was a complete black
box, except that we only knew the company's name. It's rare, but there is at least some scope, at least some set of IPs,