How to use XXE to your Advantage
Show transcript [en]
so so thank you guys for coming out today I'm off of the day I know you've been just hammered with information left and right so you could be anywhere in the world right now but you decided to be in this room with me so I this was a dual project of myself and my colleague Donald Miller Donald can't make it today because they got called away from work in another country so you're stuck with me so today is a arisen is the name of this talk right so he's a xxe teared in any environment so I've spoken about xxe I believe back in 2015 20 B sighs Charleston and it was before obviously the new Olaf top-10 came out in 2017 but
it started off as a project a senior project Bob was in college while I was studying service-oriented architecture so it's just a really fancy way of saying like when you go purchase an airline ticket it locks your airline ticket or a movie ticket or any kind of certain time so from there my friend turned me on to this and I just kind of dug into it learned a lot learned more and more and more about it and the announced which were covering the slide today so a little bit about me I'm a cyber operations officer and the South Carolina Army now our army stuff for the last 12 years before during this during each 12 years I started doing cyber
stuffs probably back in 2008 when I was a little private in Korea officially became a student carrying that word active-duty how left back to duty after my last deployment I came went to school at called intrusion down in Charleston South Carolina for Ian to be a computer science major studying for pretty much does my first introduction to programming it was totally daunting but I was super interested in cybersecurity from there went on and made a cybersecurity Club which is why I guess grew which is super awesome through there I started getting into a little bit of consulting for a start-up firm called cetera which is a sponsor for this organism for besides Augusta today and then through that the
technical mentor at node SC which is a nonprofit organization in Charleston in South Carolina that focuses on teaching information technology cyber security and business entrepreneurship to the high school college and college students in the local community I'm a code monkey so I just I've been wanting to get my developer chops up so from from this project I'm going to demo a tool called doulos that's written a Python it kind of automates this process of creating XML payloads to test for this type of vulnerability I'm a builder of Legos I like to build a lot of Lego and I've recently have been trying to figure out how to make the perfect old-fashioned which is harder up top is a photo of
Clyde the cougar which is a College of Charleston mascot this is me getting Clyde's ring it's so fun fact that was the mascot for College of Charleston but so you know what I look like here's what I look like it's collide right so here's our roadmap for today so today we're gonna cover what is xxe and what we can do with it the different xxe attacks and the types we're gonna but in order to understand I sexy you have to understand how XML works which is pretty simple we'll cover a demo then we'll cover some defense against xxe excuse me we'll talk about what kind of payloads are excuse me what kind of detections you could be looking
for questions you should be asking yourself red blue and purple team's how they can use excess seeing and we'll open it up to questions at the end so key takeaways right so for this talk if you pay attention to nothing else I say I want you to understand how XML works and how it can be used for good and bad I want you to understand how what web apps are exploited using xxe and then understand and see the attacks dirty guys are the red team the blue team purple team so what's pretty important in I would strongly encourage that you keep an open mind when I go through this material and think about ways that
through a stock analyst or a threat hunter can look at this type of information and say what can I gain from this what what kind of behaviors can I find what kind of signatures can I write really understand at a deeper level you read team guys you can i mean it's it's kind of more of a technical talk so we're gonna be exploiting the simple web server to demonstrate this proof of concept but also look at it through the blue team's eyes right and then the purple team is kind of its blend between the two and we'll talk about more of that in detail so so what is sexy right so it's not it's not sexy it's not like
I got remote code execution through xxe which very rarely happens but it's an XML external entity attack and it's a type of attack that occurs against an application that parses XML input right so any type of application that you write Java PHP Python if there's a parser library or the language can parse XML files it's a way to it's a vulnerable it's a possible vulnerable application right so this attack occurs when XML input containing a reference to an external entity is processed by a weakly configured XML parser so in a nutshell what this means is that you crack your XML payload whatever it is you push the payload to the XML parser this could be through a soap arrest
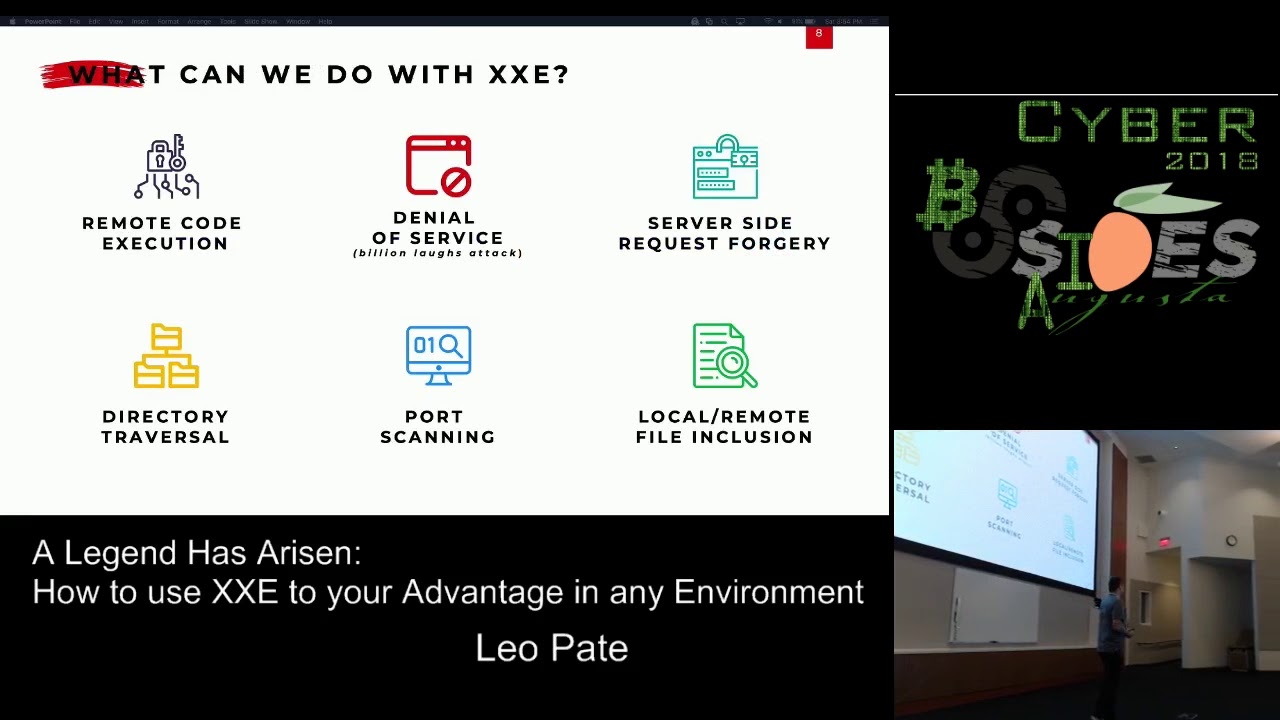
process also just curling a file to a parser that you're looking for which is the demo will be I'll be showing today but it could also be a file upload feature right so if you have a web application that takes in that allows users to upload files slack SharePoint those kind of things nine times out of 10 it accepts XML all right excuse me your parser interprets your payload right and then from there pwnage hopefully fingers crossed no whammies that you actually get it going all right so what could we do in the neck sexy again remote code execution is it's rare but if you're already rabble hole simple check let me just see if PHP has its module loaded on this on
this web app right so you got denial service to the laughs attack is essentially an entity that called another entity that calls another entity right so again you're just going to that server with calls super site request forgery so I want my server I want me the user to to interact with this server and I want you the server to go out and show me something but I don't want what you're pulling to know I asked you to do it I just want you to do it don't tell nobody and then when you get it let me know that you got it and show it to me but it's our little secret directory traversal is pretty
self-explanatory navigate enumerate to directory port scanning and local remove file inclusion all right so now we're going to go over an overview of XML so XML is an extensible markup language it derived from the standard generalized markup language so it falls from the same family of HTML the International in HTML is the international standard for defining mark oh right it's software hardware and app in it so when hardware and software designers came together they're like we need a language we can use a transport data that's super simple it's easy it's lightweight it doesn't have a high overhead and it's pretty simple to pick up all right so what we in in the in the next slide
will see an example of this but XML looks exactly like HTML you got your closing tags you've got you know your strings your data whatever is parsing through right but what's particularly point out is that hTML is used to display data right so colors images videos pleasing to the user of your web app of your web page whereas XML is purely used to be storing data and transport data across your network right so if I have to some applications and they need to talk to each other well how can I do it well you can look at your options but XML might come up in conversation for you to do so so from there how can you know
server 1 talk a server 2 and pass data back and forth so that server 1 and 2 or both speaking quote-unquote at the same language all right so what uses XML Microsoft Office Apple I work OpenOffice Libre Office you see a trend that's happening here with the file upload feature right so you can imagine where this came from SVG images X HTML and X CSS which is XML it's HTML written in XML so it's kind of like jaikon Java and Python bananas html5 RSS atom feeds and then soap and wrist web services all right so now let's actually start digging into a little bit more into the XML so let's put our nerd hats on
so all XML files must be well-formed right so well leo well for me well they have to have a root element right so you have to have a root tag all of this is like is comprised of this one thing that root element must have a closing tag in all tags sub underneath that tags are case sensitive and must match they also must be properly nested all attribute values must also be quoted XML does not require document type definitions but they can and do use them so today the proof of concept will be calling out to excuse me a web server that brings that grabs a document type definition file reads it and then spits out stuff
elsewhere essentially your XML follows correct syntax so that's what well form means and in all XML values that use the DTD must be valid right so what is valid valid is does your DTD match what your XML file States so if your XML file is valid it's also well-formed it's naturally assumed that it's well-formed this is kind of where you can start getting into shaky ground if it automatically assumes things right so this is a well formed example so here we have the top line right so the top line XML version 1 encoding ETF and standalone yes this is not a required line in XML files but it helps right it helps our sera understand
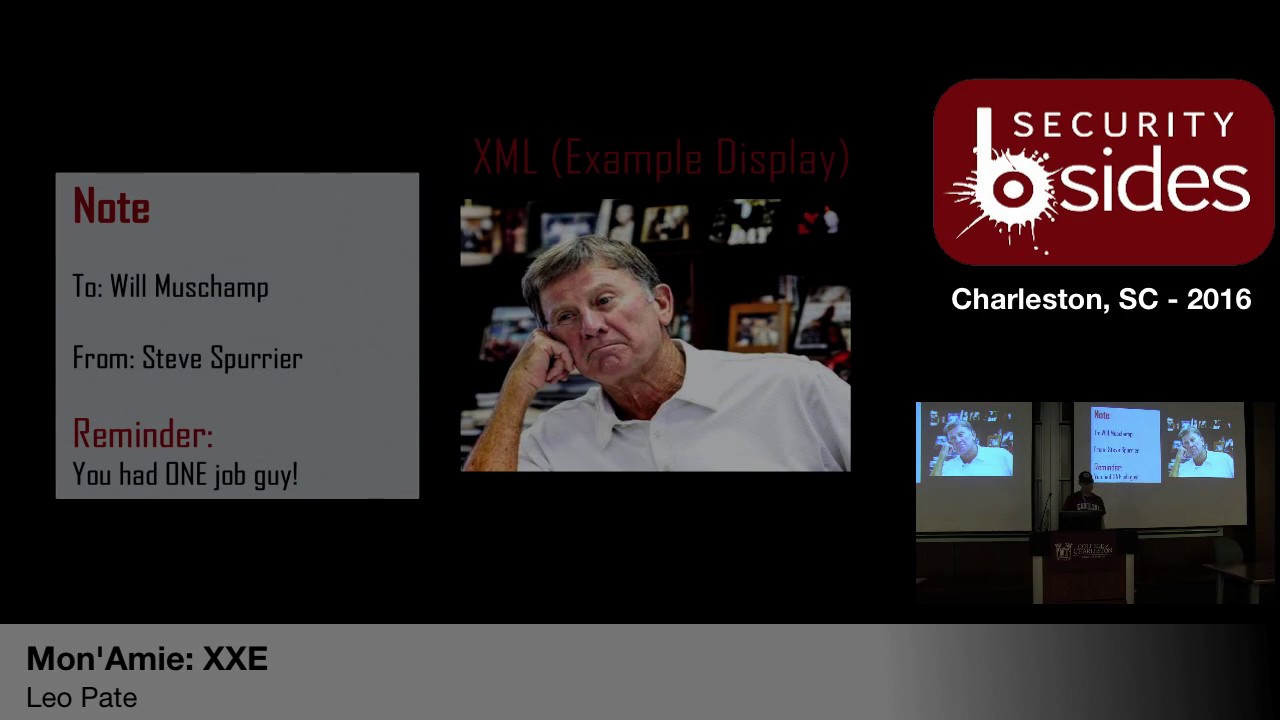
what type of file it's dealing with and it doesn't have to guess so here we have a root element of note it's going to Kiki from abri it's got a question and it's asking do you love me right there's a note it's a quick note cool right so this is a well-formed example so we've got our open and closing tags we have a root element everything's nested everything's clean so now we're going to do a valid example right so it's the exact same XML document but instead I'm including a DTD file document type definition file which states that I have an element some element called notes that has a two from heading and body element sub elements to
it each of those elements is a PC data type of element and this stands for parse carica data right so it's just simple plain text you know whatever is there interpreted as it is so if I have a SD f afdf ace yes it's going to print a SD FASD FASD are right there right so but what this means is is that whereas before in the previous example here XML whatever is interpreting an XML file has to guess at the root structure or the structure of this XML file here it doesn't have to guess it has a document type definition that says look here and this is how you should interpret this file right so we're going to start
walking into the different xxe attacks right so a little bit of terminology so you have in band blind and out of man right so you're in band is where you send in xxe payload and you get a response back from the web app containing some data within all the same browser or terminal window user launching attack right so I launched the attack and I'm going to get it right back so file upload feature if you are exploiting a certain variable or a certain thing in your web application and you upload a file to it and you say spit it out in in this field right so a perfect example is username and password so if you were to log into a username
and password web app for instance underneath it might say welcome you know and then it'll have a variable of username here so to say welcome whatever you set username to well if you if it accepts XML files and you upload it and you say instead of printing my username I want you to print the variable that I stated in my XML file and the variable I stayed in my XML files ashle Etsy password that's a password file so spit that out on my webpage and it spits it on your webpage and you're like awesome you're vulnerable and I'm gonna see what else I can do with you all right next is blind so an attacker can send a
request with an xxe payload get nothing by the errors so from there you're kind of poking a bear trying to figure out you know what can I do what can I do and making the implicit explicit so what is the application not telling me and then out-of-band is kind of like in-band the only difference is is that it's not gonna spit it out in the same terminal or browser I might have a netcat listener or I might have some other thing that's accepting input that it's going to push it to could be an FTP server could be your DNS logs could be anything right so again here's an example of you're in band right so it's
gonna spit it out in the response they believe that here's a blind one so something to pay attention to is this error so it just gives me an arbitrary error so I tried running this thing it's a oh there's an error you're like okay cool it's a at this point I know that it's accepting XML right and it next is your out-of-band right so now I'm running this right here so saying very entity at a variable called paths going into the system I want you to look for this file Etsy password and then another entity called xxe in this system I want you to make a call out to this IP address using this port and go to this
page and then display the file Etsy password and then again nested file reset login kumar's face and then pass this in there right and then pwnage and got your Etsy password file alright so now we're going to actually walk into this demo so well again so I made a sacrifice to the demo gods last night so hopefully this works accordingly so from here you guys can't see this
you see that yes
you know awesome cool so you can't really make up this stuff up here in my terminal but this right here is the actual code for my parser right just a simple XML parser written in PHP it's just accepting XML anything and then spitting it right back out to you right so I have an attacker terminal so this is supposed to emulate the attacker typing in commands to get all the things next I have a net cut listener which is essentially it's just my listener listening for that callback that I get and then I had the attacker own web server so this is where I'm hosting my DTD right so I don't have a slide on
this I probably would have in hindsight it probably be better to do it but how this attack will work is I have this vulnerable web server that is taking in XML it's parsing an XML I have my own web server AWS digitalocean whatever that is hosting my DTD that I want it to run through and then I'm going to pass that to pass a payload that I generated using a tool called Doulos that will generate the payload and the DTD needed for you to execute this attack I pass the payload to the parser the parser interprets it says oh there's a DTD file I need to go out to through this IP address on this poor B file
analyze that and then what it tells me to do I'm gonna spit that out to this other IP address slash poor on this Mac cat listener so we're gonna walk through and that's what we're going to oh no hopefully this works so so my tool is not open to the public yet because it has it's in its like the alpha phase so it's super buggy if you guys I have contact information at the end of the slide deck so if you want access to it to play around or contribute to it just let me know there shoot me an email shoot me a thing Twitter and I'll get you at it and you can play with it but in the near future
once I work out a lot of these bugs almost definitely make it public for the community so something to keep in mind is that we're running Python 3 right so python 2 versus Python 3 very very different so if you try running this and python 2 and you're like it doesn't work it's not a bug it's just we we just me and Don decided that we're gonna move forward with Python 3 and not make it backwards compatible so from we're going to run it'll call Doulos and I now realize that that is a terrible background for you guys that better cool cool cool so tool call Doulos a little history duelist is the Greek god of trickery and
other things so I thought it was pretty clever that were tricking web servers to do stuff and in Halloween's coming up so I said why not put some ghosts on there cool so also fun fact I had to pivot my talk two weeks ago because my exploitable web server that I had didn't want to be exploitable anymore so initially I was using creating an out-of-band payload using a docx file that did kind of the same thing that we're doing now with a file upload feature but I could not get it to work - two months ago or two weeks ago when I could get it work two months ago I don't know what happened so I had to pivot
really fast and throw this in there but so we're gonna create an XML dot txt payload right so choose number two it's gonna ask what does that I P of the server that you're hosting your DTD so we'll go ahead and throw that in there what is the listening port of your server that is so singing your DTD so we're going to do 8,000 because we're running just simple HTTP server using Python default is 8,000 so what does the IP you want the victim server to call - so same IP and then what is support you want the victim the callback right - 1 3 3 7 and then it's got this error so this
also happened from I'm running in the wrong thing again more buffets
that's what we wanted so it created our payload they stored it in the absolute file path I'm going to create a DTD file stored in the absolute file path so now we have our payload that we're going to push to the parser and we also have our document type definition that's the instructions for what what the web server is going to what the parser is going to tell the web server to do with what we want right what it is oh no so so from here right so we have a root element right a doctype and we have a city called wrote so to say and we have a excuse me we have an entity called
remote back saying go out to IP address that IP address in that port and pull the evil DTD file interpret it and do whatever it says inside of it and then from there I want you to execute remote I want you to then execute in turn and on down I then want you to execute xx so it's important to note note and I sexy they can be named whatever you want those are just variables those are just the variables that I selected so now look at our actual meat and potatoes of this these are the actual instructions right now I have an entity paper cuz I'm like and then HP filter read in so using PHP
read in this file and then convert whatever that file is base 64 encoded right and any actual resources the Etsy's flash password file so that's one entity the next entity is in turn right but within in turn I have another entity called xxe that says similar to what I demonstrated earlier IP call back out to that port number and give me a result and that cat doesn't care what for those unfamiliar and doesn't care what you get or what is send its way if it's on that port and it's coming in its gonna log it and it's going to put it a standard out which standard out in this case it's our terminal all right so now actually go ahead and
start our stuff so you got a little bit bigger so you guys can see it and now we've got our netcat listener
I trade people out to pi/3 they simple HTTP servers HTTP dot o that took like that's a googly why is this not working cuz you're in Python 30 now guy so now we have our server listening you simply three it three that you run your server so with another quick ten twenty minutes to Google right so now we've got a server that has the root directory of our paper folder it's gonna reach out and grab that file execute it right I got a netcat listener on another port saying give me all the things that you want to send to me so now we will execute this so we're gonna curl be actually just so I don't mess this up I
did a lot of tests right so curl this curl this file passed in payload txt to that IP address and this is the attackers are excuse me this is a vulnerable web servers IP address right so you're not gonna get anything back and the reason why I'm getting anything back because there's really nothing to return but your web server is actually calling out and doing the things that you want it to do right so if you kind of still hang your you're just hanging there but if we go to the actual server we see a two hundred for the evil DTD which means we've got the file awesome that's step one did you am I am I
getting a call back or you am I just whatever do i this IP address is some IP address reaching out and grabbing the evil DTD file directly that's a win and then my net cat I now have this base64 encoded thing so from here you're like cool so also fun fact the only way I could get this to work is if you don't code it so if you're doing XML stuff this is why it's a kind of a piecemeal environment you have X so you have XML code but you're also using HTTP to move your stuff back into floors and then you also are reading in system files like Etsy / password SC sauce fstab here in the
windows when I and I and in your passing the contents of those files through HTTP right so if there's a lot of times there's a lot of characters the HTTP doesn't like right so you got to xscape those characters easy way to do it is just encode it to something like base64 which is used to transport stuff over the Internet right so now we've got this base64 shrink that we can then decode right so from there go into Python and port base64 oh it helps if I can spell all right so then base64 dot be 64 decode again if I can spell pass in that string and then we now have the Etsy / password
file of that machine that's a win right super SuperDuper awesome now so now we'll move forward then go into a little bit further right so that's the concept that you just walk through look at it through the eyes of your blue team member right there's a lot of things in there that you can kind of pick up on your your base64 encoding things right and you're passing it through a network you have a web application that's reaching out to an external entity an external IP grabbing a file and then running it and doing some stuff right you pushed a file to a web server and that connection never closed right so that's something else too that this might be terrible coding I
have no idea but you have like a lot of things you could be you know you can be on the lookout for through your red team's eyes of a way ahead essentially for you know another another thing you can put into it right when I've tried everything else like what else can I try kind of deal so now we'll move forward into defense against xx key and its limitations right so one limitation XML parser can break if they don't understand characters in your XML and DTD files right so what if I didn't want to encode it what if I wanted off you skate is a little bit more well there's something called C data right so C data
says hey XML parser if you see things between two tags or if you see if you see something that starts with C data in this very specific order then just interpret it as it is like thanks I'll try to do anything just print it I don't care it just doesn't have to be let me care that you just get it out there that's one way of doing it right next is the other one that we just talked about is base64 so I had a really funny gif here Jeff but Mac for Office for Mac doesn't like gifts gifs whichever way you say it so this presentation had a presentation crashed on me two years ago but the the example
on our demo is PHP based web app patient you could pay 64 encoded alright so now let's go into detection and prevention so I had a had a you know I got a I got a beer with one of one of my colleagues very pretty recently and he said one of the biggest things that a lot of people in our industry failed to do is we're how do I stop how do I stop that is how do I get the bad guys how do I find him how to get him out of my network you know like that that train of thought and my hammer we got to get it out right but then nobody talks about detection how do
I detect all right so you everybody's heard of statistic 200 plus days adversary sitting your network you have no idea right how do I get that number down to ninety thirty four hours right how do i how do I bring that in my own environment well you got to learn how to detect it and then that goes into the purple team can talk that but I was going in today what Dave Kennedy spoke about today with behaviors tactics techniques and procedures you're only focusing on the technique and then putting in the strings but then I can change my string to do something else to get that looks different but gives me the exact same result right oh well
first things you can do if you want to catch this in your web application it's just disable the use of external entities period right so if you write a custom web application and you already define all your data types data type of like Borg whatever you define Borg to be your and you have those files internally you should never see your web app reach out you have another DTD file if you have it locally unless you have like public you can set public dtds which is W C cubed I believe the World Wide Web Consortium so w3c that defined sumela specification they have public that you can use but if you see anything DTD typically if you
create your own custom application that's not going to change that right so that's one thing just disable it boom done very simple neck verify that your XML or your XSL so your schema file for your XML upload functionality validates your incoming XML right so whatever your if you have very specific parameters for your application why don't we specify those those very specific things and say if it's not this just don't even use it just throw it away Deb null random or Tim doesn't matter just get rid of it I don't need it right and in patch upgrader xml parser you run PHP five upgraded PHP seven older versions of Java that sort of thing right
oh wasps has a super awesome cheat sheet for all the various languages that have XML parsers and they're very very very simple to do and change it's not like hundreds of lines it might be like one line changed this module from true to false boom you're safe right but then so that's how we can prevent it how can we detect it right so typically if your stuff parses in JSON why can you not just change it to XML a lot of times if web applications will read the content type headers for for JSON you know going to burp and say Oh change that to XML run it right it'll still spit out the same information so
it's like oh so you now take again doing blind stuff it allowed me to change it and I still got results back that is data let's change that to you know what else can I do with it what else can I do with XML right mmm go down this rabbit hole are there any outbound requests from your web server web app that shouldn't be there right if you have an internal web application you should most definitely not reaching out to your to an external source unless you know you you have it configured that way right is there any use of basic C for in your environment so I know in my environment as a sock
analyst I see some things where I'll see base64 and it's like oh what is this and really it's just this admins off be skating their stuff through the network because they're trying to not get caught by the you know sock guys and then is your purser accessing directories and files that shouldn't right so that's a huge one so if you have a file upload feature why is your file upload feature going to your Etsy directory alright it should be going to like user uploads or some other thing right so that's most definitely things you should be detecting on and be looking out for right and that's just and that's only one of many it can get pretty pretty
hectic right but now we're gonna go into red blue and purple teams and how they can use xxe right so I'm a geek and I'm a nerd and I do a lot of technical stuff as you can see but my job as an officer in the army does not allow me to always get to be the geek in the nerd sometimes I have to be the manager the leader and the supervisor so I have to take groups of people and train them and get them trained in order to execute what I need them to be able to do right so this is kind of where I get into I put my management and my supervisor had only
right so xxt through the red team guys again I have another gift jiff and it crashed my thing so I found this guy in college who's just taken a nap right so xxe is not the sexiest thing right it's kind of it's pretty boring in the eyes of red team members because it's like ah well I don't get to pivot I don't get to do all these you know super cool things that make me look Li right but there's countless blog articles of people who are able to through xxe through SharePoint for instance in a Windows environment was able to continue to escalate their privileges to domain admin right that includes exploiting Korean RDP user and then from there you
got your GUI so then you go from simple user that has you know simple SharePoint user upload to I now have you know a Windows command prompt as a standard user that I can then elevate privileges through that to do to became an RDP user so now I have a GUI to do stuff to obtain domain admin there's also a couple instances with Facebook got pop pop for this a while ago slack got popped with this a while ago right so if you're doing bug bounties doing fun things right might be a cool time to try it right so through the red team size it can be using all phases of the adversarial engagement right so just a
quick quick question for my first giveaway your choice what's the difference between penetration testing or red teaming in your own words
yeah so one is a particular particular thing of an adversary right so you're emulating an adversary and the other one is just doing a service right so with that I have two blue team handbooks and a wireless adapter which one you want I want a wireless at their coolest right up front so I'm gonna use that and then I'm gonna add more I'm terrible at this struggling today won't struggle bus so team right so to add to that in my opinion this is Leo pace opinion so if you have like the security onion onions you can throw them at me if you want if you don't agree but penetration testing is typically limited in scope right like
you said you're kind of testing for a service you're testing you have clearly defined left and right limits you have a short suspense and you got to do like I'll find all the things right whereas red teaming goes you know like three layers deeper right red teaming is emulating the adversary thinking about the adversary how does the adversary view your environment how does the adversary you know is in your environment it's not just one than zero so it's not just things you can plug into you know a power outlet its people its door alarms its you know key fobs it's your telephone system it's where you live it's your card that you drive the route that you take right if I have
an important sysadmin and I want to stop you from getting to the office to do stuff well why can't I have a team of people that knows the route that you take to throw up traffic cones and reroute you around the city which adds an extra thirty minutes to your commute you know like it goes to that level of extreme right so utilizing the penetration execution testing standards xxe can be used in all of these things intelligence gathering right so port scanning what files can i grab what does the lay of the land that sort of thing threat modeling so nobody likes to do but it's pretty important how can I get into your network how can I do things
and get things done to achieve a desired result next is vulnerability analysis so this is kind of it's your web app vulnerable to this and if your web app is vulnerable to this well then how can I use this to determine other vulnerability points within your network infrastructure whatever exploitation and in post exploitation so how do I exploit this and then how do I get stuff out for X so again you're less likely to find RCE this is more use for remote and local file inclusion and fitting into other systems a way in and learning the lay of the land so that's really where X X C in my opinion comes into play however you're limited in options for exploiting
web apps because you're you're very limited in a number the type of protocols you can use FTP DNS pH what else HTTP right so you're using these various protocols but you're pretty limited and you're only limited by what those protocols will allow you to do but why can't you take a protocol like PHP and then encode it in base64 in order to give you know your ex valid data right so I'll argue that while you're only limited with those protocols you are also limited by your own imagination and how you can string those together right so let's taken that a step further right so for the blue tang people on the rule in the excuse me of the blue team people
in the room this is the mindset that your red teamers your adversary simulators your penetration testers this should be the mindset that they have right so next we'll go through the blue team's eyes right so again two hundred plus days how can we get that number down a really good way and this is just one way is the doodle-loop how many of you've heard of the OODA loop right so see a couple of hands right so observe orient decision make a decision in an act upon it right so if scene right so 200 plus days is when you start to observe right so 200 plus days you're like oh man I just discovered this person or this int this entity is
inside my network right so after we cut it down but until we can act right so do something and place a safeguard get them out or not get them out maybe I just want to contain them a little bit so I want to learn more about my adversary what are their TTP's their tactics techniques and procedures right and then so from there from this one proof of concept that I demonstrated today right I stated the only way you could do it the only way I could get my data back is if i encode in my payload right well that's one so there's a lot of pretty interesting stuff with base64 encoding so if I take the letter A and encode
that in base64 and then encode that in base64 and then code that in base64 and then code that in base64 let's say 20 times my you know 1 kilobyte 3 kilobyte file could easily grow to 2000 kilobytes right and I might not be such a huge thing but if that's just one letter if I have an entire file this file might be one may if I base64 encode that 20 times 10 times 15 times you know my file is gonna be only exponentially larger right so now I've got a huge huge thing I now have to exfil right and hop you skate it so a longer fixed prefix of this the size stronger attack detection right so
for your red team members this is where you start to think and see through the eyes of your defenders through the eyes of your sock analyst right this is kind of their thought process behind it how can I catch you well it's not only how can I catch you but what behaviors are you're doing that got you to this point so if I'm blind I have no idea I don't lurk pops up and I got to look at it typically I'm gonna look at the alert and then I'm gonna go into slunk or something or whatever my Cimiez scheme is and then back it up like ten minutes five minutes right sometimes 30 minutes sometimes
our right if I see something consistent if I see a beacon calling up right so backing it up and then adding additional 5 10 20 you know in minutes later to kind of get the picture of what was happening on this box at this time accomplice I'm digging it into it right so here we have your blue team so your blue team's typical role job is to obtain situational awareness of your environment right so there's nothing worse than a stock analyst sitting on a network and they have no idea what the network looks like they have no idea of what's happening they don't know what devices are on there how many of you have heard the story or the the web
server that got plugged into the outlet or connect it to the Wi-Fi that nobody knew anything about and another way it came about is you were doing compliance or you hire some pin tester to come in and do it and found that that dusty box in the server room is actually something that's been sitting on your network that used as a 56k modem or something was the last time you guys saw a 56k modem in an environment fun fact I saw one two years ago and it's still there so but again your your blue team members right your defenders detect investigate analyze and mitigate and prevent the threat whatever the is could be adversaries of a PT
level could be untrained users of your environment it could be you know infer things the threat is whatever whatever it is that could compromise your your data right your data your people you're in tech your company your organization's integrity your integrity whatever right and lastly is to understand evaluate mitigate the risk right so that's what the stock is there for is really to to understand the risk of all these systems and what that means excuse me evaluate that risk and then mitigate that risk right so reporting to your business leaders hears we really have land here's what we're doing here's what we got and here's what I can defend against here's what I can to against here's what here's
your risk level before we put these effects in place here's your risk level afterwards we lowered it or we might have lowered it here but we hired it here right so that's really what your stock leaders are doing your analysts are providing that your staff within your hunt team really your whole stock environment is providing that right so for the blue team members in the room your red team is viewing a problem from adversary or competitors perspective again this is location of your building this is how many people you have your online social media presence your just web presence what do you have on your website very fast sort of thing right next is your
alternative analysis so for my next giveaway which is another blue team Handbook who wants to tell me in their own words what the turnit of analysis mean nobody tell me think about it alternative and yeah go for it
yes yes yes don't get your boat so your alternative analysis right so that's absolutely it right it's not the standard way right so red teaming is more again than just ones and zeroes its mitigating groupthink right so groupthink you get a group of people in a room there's just there's countless studies but one person says I think this is a good idea and everybody looks to the boss and the boss says I think this is I think that too is a good idea and then everybody else in the room is like oh yeah you know like Jim is an awesome guy he's so smart and then the next day Jim goes huh I have another awesome idea
and he pitches it and then the boss is like that is a terrible idea you're an idiot what are you doing and everybody else in the room is like I'm Shaun and Jim yeah I mean cool no more right your red team prefers analyzes everything that is said everything that is done and says questions it does it stand against my questioning does it stand against you know let this standard way of doing things does it make sense and is not afraid to speak truth to power and sometimes that's really hard when you have customers when you're trying to explain something and you're trying in a very nice way to say that your environment is not where it should be right and you
have to do it with senior people in the room and then say that in a way of you're not your environment isn't what it should be but then you point to you're not deliberately trying to do so but you're saying these guys aren't doing you justice or trying to identify pitfalls people aren't trained you're not trained on this thing right nothing against them but they need training on this they need awareness to this they need to be exposed to these things right and then you act as devil's advocate so the toll term from my last book this is something at I'm a I'll be I'll be very surprised that people know the answer to but for the last book who wants to tell
me where the term red teaming came from Google is your friend Google with your friend go for it
so yes it is used for red teaming as used for them but it dates back so much further than that like like past medieval time I'm talking like 1400 that's another question so also another question for the book but red teaming came from the idea from the Catholic Church that for sainthood for people who were put up for for becoming a saint by the Catholic Church the Catholic Church believed that everybody gets a voice in saying whether or not this person should become a saint and that includes the devil so they would pick one person to be the devil's advocate right so that's where that term comes from devil's advocate she's back and question every single thing about
that person and try and debunk every single bit they did this one thing well they didn't do that it could have been could have been that it could have been that right so that's really where the term devil's advocate which later red teaming came from right so doing a problem from an adversary in this case in this scenario the Catholic Church did was the adversary or the competitors perspective right excuse me and then lastly we get to the purple team right so again this is not a new concept but very few companies very few organizations are going to grasp this right and even in the military I can't tell you how many operators don't sit
next to sake analysts and no idea you know the the other side of the spectrum in regards to info second that goes for the public sector and academia as well right so you've got public private and then academia they don't know right so you have red teamers that totally focus on red team engagements and penetration testing but they have no idea the artifacts that they're leaving behind they have no idea the things that they're doing then how much how loud they are they think they're being super stealthy and you're not you're setting off you know alarms left and right right so if you miss to the concept of a purple team demystifies each other's operation
right each other's thought processes right so how did the blue team make decisions it's not just how do you write signatures but how did you get to the point to say that I need to write a signature for that right so it also enhances communication flow between the two teams right so when you get your red team in and blue team in sometimes they're coming in kitten when you first start they're kicking and screaming because they don't want to sit next to each other waste of their time why are you putting me with this feud he doesn't talk or he or she doesn't talk my language playing they don't know but when you force people in a room together
and you say you can't leave until you figure it out right eventually they're either gonna kill each other or they're gonna figure it out right but if you if you foster an environment where it's okay for your red team member to be like I had no idea what you guys do right but you get people in there that's like I have no idea what you do but I want to sit next to you and I want you to show me right let's go through that alert let's go through your normal process let me think explain to me your process right and if you don't know a process let's go grab the guy or a guy or gal who knows or
let's go grab the policy that states right and then on the reverse side blue team members again junior analyst if you're new to the field right so typically one of the very first positions regardless red team or blue team is typically a junior analyst right a junior stock analyst and then after a little bit of exposure and experienced you that you kind of venture off you know you're like oh man I really like the attack side I'm gonna go threat hunting or let me just make the jump and go pure red team right it's not uncommon for people to bounce back and forth but your your analysts you don't know so if they can sit next to somebody who says
who pulls out their playbook and says here's how we do stuff you know I'm not gonna give you all the tricks of the trade right that I can make you smarter and again channeling Dave Kennedy and his talk today and the keynote talk most of your time as red teamers and penetration tester should be researched should be reading and learning right so you're getting to a deeper level as how things operate so from how things operate you can convey that wisdom and knowledge that took you months or years to learn and to this someone junior that is you know might might take like an hour-long conversation but you just took ten years of knowledge and condense it to an hour
and just gave them the answer right and not only give them the answer but then challenge them a little bit more to go dig deeper right so now you've turned a situation where two people to order two entities within the same organization or fighting for each other or fighting against each other and now you turn it into a mentorship session again putting my supervisor hat on right so and in each element gains and valuable skills and sees behind the curtain and to how each other conducts operations right which is pretty important right so you're not just getting 50% of the spectrum imagine if we can only see this right this is all we can see and like
red team I see this I got a half the things I got to do this stuff I got to give the report here's how you stop me Elba blah blah blah I come back six months later nothing's fixed right let me do it all over again and blue team says I got to find the red team I got to find the adversary I got to find a threat I got to do the stuff and Don's signature written implement let's do it right so from there you're very narrow minded but then if you can pull back the blinders you start seeing colors for the first time I recently just had PRK done like a month ago and moment I got off
the operating table I was like right it's seeing colors for the first time and then when you actually get to sit next to someone who knows significantly more than you and you're like you come with that open environment of teach me I want to learn share share your knowledge with me right a lot can go that those barriers leave right so your questions you might have any questions for me in a long day I talked a lot no water cool so that concludes my talk but I have one question for you for the last book who can tell me what the latest version of XML is what's the latest XML specification version Google's your friend
I'll wait this time I'm done you know sorry Oh she'll whisper it to someone
we can make it awkward I've used the high school students all the time I was a question that was will look at me and I'll be I'll stare at you come a little blink first and it's not gonna be me oh oh um trying to think of a different one so you does anybody have any purple team experiences you might have any terrible red team experiences yeah let's hear it okay
yeah
awesome so so you've taken your environment you've done your thing but then you've done a write-up and then you've taken the time afterwards to explain that clearly and take technical talk and explain it to officers like myself who have no idea just you know warheads on foreheads yeah
man that is a solid process and it's you know iron sharpens iron I'm a firm believer in that so that concludes my talk thank you all for coming and here is your book awesome oh so the most recent xml version is excellent is 1.1 if you paid attention up here is 1.0 right but the de facto standard is 1.0 everybody uses 1.0