Cryptojacking Servers: The Intersection of Poor Patch Management, ICOs and Autopwning
Show transcript [en]
alright alright again thank you everyone for coming to b-sides this year we got some great talks we have the CTF going and thank you so much to all the volunteers and the sponsors I hope everyone has had a chance to to stop by and speak with them but I would like to get our next speaker up and running and his name is Chuck McCauley and he has a great talk so enjoy hello guys I hope you guys have had a good lunch and first talk in the afternoon lunch learning all about lambda things right so I'm gonna talk to you guys today about crypto miners how they do drive-by exploits break into servers and then make fake money off of
your equipment for you my name's Chuck I work I work a much more complicated company name it's called Ixia a keysight company i keeping the victim of being acquired by bigger and bigger companies so if you don't know what keysight is i didn't either go google them they make all kinds of stuff they're giant a mega conglomerate thing I'm a man of many hats when I worked there I participate in new product development hacking threat intelligence research firewall intrusion protection testing is sort of where I came from and I've been in InfoSec ever since I left college and that was a long time ago I can tell from being here today that I'm much much
older than I used to be I'm not really big on social media but if you like to follow people on Twitter a noble Trout that's about all I am and I mostly post stuff about InfoSec but also stuff about a new Land Rover Defender I just bought with the right hand drive and I signed up as an uber driver four years ago because I just wanted to figure out what it was like Alex did go up and down mountains and watch too much TV so there my hubby's anyway so what are we gonna look at today we're gonna look at crypto miners on servers notably other people's crypto miners on your servers and we're gonna look at what I
calling for different campaigns that are telling you to infect servers and pump fake cryptocurrency stuff up into other people's pools and things I'll show you the tools tactics and procedures that are used to develop into play this stuff and what to look for and we'll even get a little bit of partial attribution not full attribution I'm not gonna show you screen grab of the guy's Twitter profile sorry you don't need to be a crypto currency advocate or naysayer or really understand them very much but you need to sort of at least know what a crypto current cone is what gnome own arrow is and that mining is a thing and that you can use Mon arrow to buy drugs or video
games or go online gambling or something that's about all you need to know about that don't so if you hoping they're gonna learn how to do cryptocurrency mining monk-like talk so part of what we do at Ixia a keysight company is threat intelligence we manage a giant honeypot network with hundreds of simulated servers they grab web shell exploits brute force errs simulate administrative consoles ICS systems all kinds of fun stuff and without going into too many details it's sort of a hybrid of open and closed source software we even use some off-the-shelf tooling you'll see Splunk screenshots in here spunks great for us to just do the data mining on the raw data and these are some of the
attacks that we use that we see a lot so we targeting WordPress or Oracle Apache Tomcat those are sorts of stuff that you see a lot happening across these these drive by hackers also a whole bunch of wanna cry and that's and B exploits for the last year and a half right if you aren't in the honey pots come talk to me there are lots of fun to set up they're really hard to maintain and get good data from once you start scaling beyond about five which is sort of the problem sets that we've been working with so some of the more interesting things that we've seen from watching these sort of drive-by exploits as they develop and get better and this
stuff in red some of this stuff is from back when I was in college right but you know you've got sort of Perl BOTS and DDoS bots that are trying to just plant themselves on a system and then send out spam or send up the now service attacks from that server off somewhere else you the most modern variant of that you could probably think of as Mirai org a [ __ ] those sorts of bots that are now infecting IOT devices but they have a long lineage going way back more recently you've got ransomware which worms its way across a network and then basically profits from locking access to that system so the first stuff was I
land on the server then I figure out what I have is it a value I steal it if not I'll use it to deploy and send out my own stuff the second one is just I don't care what's on there if I deny you from using it I don't need to figure out a way to sell the marketing list that you have but I know it's important to you and you're gonna pay me to get it back now the last sort of version of this has now become just I'm gonna use your computer II sources I don't care what you have I'm gonna kill it all off and just use it to make me cryptocurrency and then sell that for
cold hard cash this is much more effective and a much more sort of linear progression of taking the thing that I got and making it into money which is what I want and so you sort of see this sort of crisscross of risk versus reward more servers equal more value and benefit for you and there's less risk right there's less interaction or anything that need to happen here as we move from left to right right so let's look at a campaign one this one tried to use three different exploits I was able to get full sort of understanding a two of them and one of them was sort of a little bit of a guesswork going on there you'll notice
that it's using an awesome attacks from 2013 and 2012 all of this data that you're looking at from the honeypot perspective was harvested from say December last year until June so these are relatively recent honeypot data logs that we've been digging through to find this stuff but the exploits use tend to date back a few more years you also have a JavaScript injection attempt which also show you and it was able to tie all these together by looking at the same wallet and hostname hosting some of the stuff so the first CVE I saw this January 10 2017 this is that Ruby exploit from 2013 and if you dig into it you'll see that it's what we call a DC
relation vulnerability so you post a file to a Ruby on Rails server with some XML formatting and then some base 64 garbage well anyone who's done a networked CTF will tell you if I see base64 the first thing I do is decode it and see what it is and there it is it just runs system updates crontab with a shell script to run and double you get and you're off to the races so you don't really need to understand what the exploit does in order to understand what it does I guess is the right way of putting it right if you see double you get in a post it's bad this is gonna be a common theme so this one is a PHP
exploit where it's just basically hey PHP run this and PHP goes okay and it's the exact same file that loads up in crontab I hope you guys can see this at the back if you can't feel free to just stand up and move forward because otherwise this is just gonna be a bunch of screens that you can't see at the bottom this is actually from an SSH honeypot and it's the username being sent over now I've found a couple of one abilities like this a long time ago in like Nets green and juniper firewalls and basically you try to log in via SSH you send JavaScript in there and then when you go in the web log and you go to see
invalid user logged in it will run the the shell script for you as the web administrator access to the firewall so you can make a permission of allow everything so this probably is injecting a JavaScript based crypto miner unfortunately the site hosting this was down by the time I went and found it so that's conjecture but I'm guessing the internet research is is not a place that you want to go on the Internet and that's because it hosts this file here which is is the file that was injected with crontab and what it does is there's a bunch of alphabet soup stuff going on here but basically it's downloading a file called sshd from a
tour to a web address and then running it it does some other clever things like if you look at the stuff that's using sis octal it's basically optimizing a computer to mine Manero for you and then it also will download a newer version of itself and if you keep monitoring those URLs they keep changing and they'll overrate the crontab with a new cron tab to download to the shell script from a new place so it keeps migrating around the internet what's really kind of cute at the end is it runs that binary form own arrow and it will if it fails it will put a fail message with the you name architecture and all the other
details in the user-agent header of curl and send it to that toward a web address so he's keeping track of all the systems that fail to run his mo narrow minor so he can go back and fix his script and make it work more effectively later which is kind of neat but bad for you so here this is a quick demonstration of how you can use this great forensics tool called strings which comes on every Linux distribution on the planet you run across an unknown blah of data and then you use search to find what you want now if you know anything about the when our mining protocol it uses something called stratum and if we
look here we search for stratum and immediately we find all these static strings compiled in here we find the wallet the pool and everything else that it's connecting to so now knowing the pool that we're connecting to and the wallet address that's mining we can now fail at PowerPoint there we go go to the pool plug in the address and find out how much Mon arrow the guy his mind and his current hash rate which is kind of neat and this guy has mined 11.1 to XM r which is Mon arrow fake currency money and that according to Yahoo Finance is worth two hundred forty six dollars to someone who doesn't have something better to do with their money which
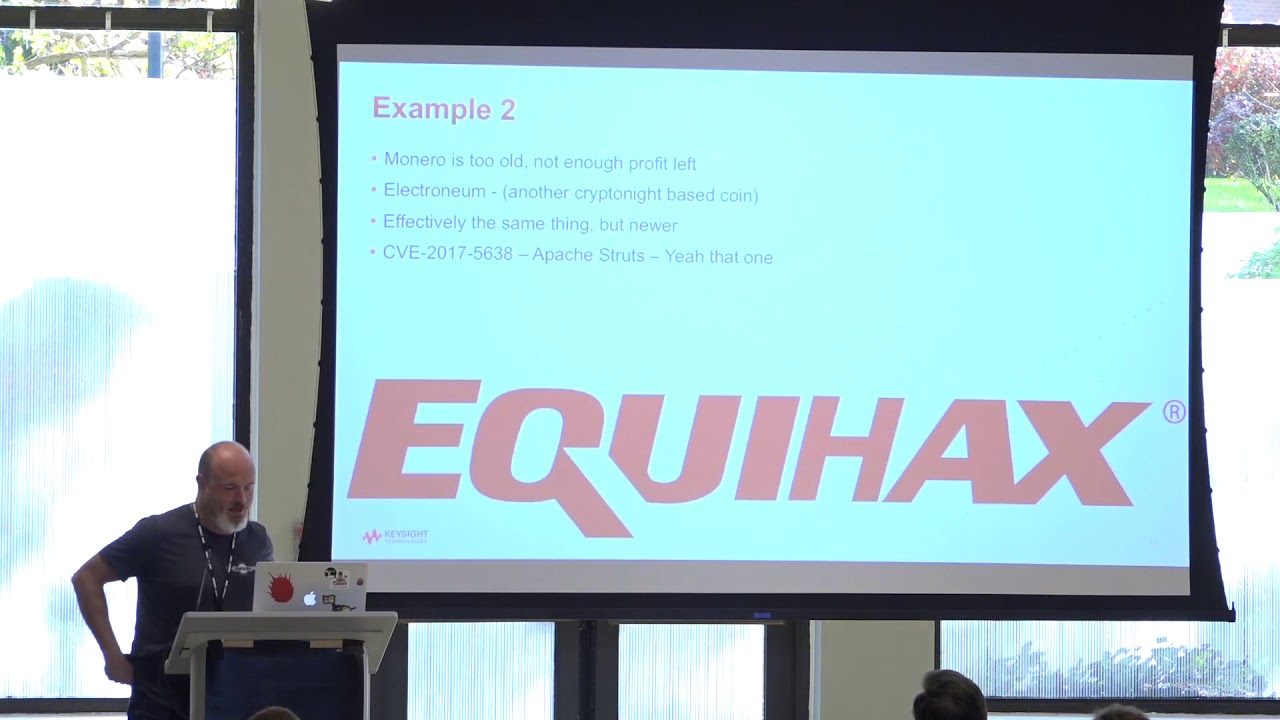
means that it's two thousand seven hundred six dollars of profit or stored value as burnin burnin a key would call that so anyway that's what he did and now we're gonna go on to the next guy so this guy decided that Monera wasn't cool for anyone anymore and he wanted to do something called electro Neum electro neum is another Kryptonite algorithm based protocol if you look into Mon arrow there's a reference network called kryptonite and there's a whole bunch of branches and forks off of it so Mon arrow is not your only one but there's a lot of clones of it out there and this one made good use of CVE 2017 56:38 which was most known for the Equifax
hack coming into Apache struts once again how many of you guys have seen this vulnerability yourself you looked at it hands okay a couple it's once again like one of those vulnerabilities that you don't need to actually understand the vulnerability to recognize the badness it just runs curl and says download me and run me and you go okay and then the rest is just framing of the attack so it's another DC realization vulnerability that means you basically create a sort of instance of an object you shove it into the server the server takes that object makes it takes that text makes it back into an object and runs the code that's in there and then part of that
deserialization process is to run curl and download itself so when we go and we look at this one this shell script wasn't a single statically compiled program so we didn't have to run strings to figure it out we just needed to download the configuration file so we got an IP address and the wallet it was right there but this presented its own unique set of challenges to figure out attribution and what we figured out was that because if you just have the IP address of the server you can't just connect to that IP address and say hello give me all your pool data it'll just return back like mining server online for you so you go
to passive DNS and you say well are there any host names associated with this IP address and we get one called new ETN pool dot info I'm like great so I type an ATM pool dot info and lo and behold it's the mining pool web console and then I plug in the address and I see how much electro neum he has and then according to a site that wasn't Yahoo Finance because even Yahoo Finance doesn't track electro neum we found out that each electro neum is worth seven cents but he had mined a hundred and thirty one thousand coins of Electra Neum so that ended up being a lot of money in real dollars so I was like I've
never heard of this what is this stuff and apparently if you go look up online there were at the Mobile World Congress aid a bunch of young people or marketing stuff it's gonna change how you pay for stuff with your phone cuz Apple iPhone pay doesn't work or it does for me I don't know about you and so they start this thing called an ICO and ICO is an initial coin offering what it really means is hey get in on this now and start mining me my coins and you will the benefits of selling them later at an inflated cost to someone else some might call these things like Ponzi scheme like or scam me but this is what they do and
so then it closed early October 20th to make sure you keep these dates in mind because this matters and then someone called hacker won on November 1st said that yes it's safe but I don't know what that is it didn't really lead anywhere safe feeling so I went and was like well when's the first time I saw this guy because I had his IP address in show script where it came from and what he was trying to inject and sure enough it was in the middle of his of the ICO that he just sort of appeared out of nowhere and if you know anything about mining currency you want to mine the early currency it's the easy numbers to figure
out right if you're in there later then it's a lot harder to find those math beanie babies right so you really want to be there early and that's why he got 131 thousand of them so yeah that you know that's what they're doing so then this is another one it's the same stuff again but this one is a Oracle deserialization vulnerability and it has curl it downloads a thing and it sends it to bash this one's bone arrow I mean it was good from February 24th April 4th so if we look at this one this guy start getting really clever he kills everything that runs on the system like if you looked at this it
speak ill for pages and pages and pages and pages because apache and Postgres and and IP addresses and everything death to it all and then on the right he keeps trying to download different types of miners and making sure they execute if they don't execute he downloads a different miner and runs it over and over and over again so he's like really trying very very very hard once again we were able to pull out the mining pool and the hash and get all that out and then he also targets windows so he's got this Auto Exe file that he downloads he used Windows shell to do it and then he also as a PowerShell script he tries to inject so
he tries both ways to get to run and tries to tries to hit it each way right and then when we execute it in our kuku sandbox we find that the wallet is the exact same so then we go and we find the wallet and we find out that he made 95 dollars out of all that effort sometimes you know the winner so it's kind of neat because you can sort of get like a good site survey of what bugs are like best to exploit right from watching this stuff passively completely and now we have example for this guy was kind of interesting so he once again targeted that WebLogic Oracle bug it was moon arrow again it also targeted
this thing called a cacti Network weather map which is like one of our biggest hitters on our honey pots for some reason and it's this really weird sort of joomla plugin kind of thing or wordpress plugin for monitoring your network health I don't know where it came from but they love to exploit it and then there's a URL which at the time I still don't know what it's for it was cool that PHP question mark ID equals and then shell script there's no CVE that I can seem to associate this one with so I don't know what it's exploiting and no one else can seem to figure it out on the interwebs so and then this guy used different wallets but
he always hosted all of his secondary payloads at the same IP so that's how we sort of tied it all together for him so I don't know if any of you can read this side but at the top those are the cools at PHP stuff and like I said I couldn't figure out what that what vulnerability that was referencing then you got the weather map plug-in attacks and then you've got the at the very bottom the Oracle WebLogic one right he targeted Oracle with Windows and downloaded minor XMR Exe on there and attempted to execute it and the windows binaries are not always easy enough to just execute and you see a screenshot of the mining
wallet there I wish everything was that easy it can be packed it can be hidden demonized shoved the way I did figure out later I could have used been walk on this one to figure it out but I just detonated it and then looked at the network traffic and it was right there and it had the mining server connected to and the the wallet and all the stuff I've shown you four or five times now and was able to figure out that on the windows side he made 1600 bucks mining this stuff which was kind of neat but once again over on Linux it was a sad trombone noise you can't probably see that but it says point zero three XMR so
it was a nothing so whatever he was trying to exploit on on Linux wasn't working but he hit it big with Windows so those are the four campaigns I wanted to show you guys take a quick breath and drink my water the next part of this is I'm gonna look and show you sort of like the amount of scale and energy required to do this sort of stuff so you can sort of try to figure out how to measure what the impact is from people doing this stuff on the Internet to be fair I could sit all day looking at my honeypot logs and find millions of instances of this stuff I just picked on
these four guys because they were the first four I found and I've never worked at Splunk or maybe money off of selling spunk or anything but I'm huge proponent of using it at this point because digging through it the fine stuff is just so fast compared to using anything else so if it wasn't for Splunk I would've been able to find all that stuff for you anyway so what we can do with these pools is they'll show you the hash rate of a wallet so you can see how many hashes are submitted per I think 5-minute interval into pool from a certain wallet now the stuff goes into the pool with one wallet but you can ship it out with
another one that's the point of the pollute pool it's a slush fund right but then we know what the hash rate is forgiven CPU so we can figure out using a certain CPU as sort of our common denominator how many borrowed CPUs were used to figure out this the this number of hashes right so figuring that out I asked a friend who minds monera even though I keep telling him to stop wasting his time and stupid I said well what are you doing your laptop and he said oh I'm getting like four to six hundred hashes a second and so I was like we'll just use the i7 fine it does five hundred hashes a second I'll work
with that I don't care really and let's work on the assumption that a lot of these CBE's that we're using are also old too so people are probably going to be running the most bang spring brand spanking lee new AMD processor all the time you don't know what you're infecting when you're doing this right it's brain prey so if we take that and we assume 130 watts per I 7 processor we can figure out from each of these campaigns who's the biggest electricity consumer of all right who be the most number of hashes per second and it's the first one I showed you he was doing 48,000 hashes a section a second which comes out to 96 borrowed laptops is the
denominator I decided to use and twelve thousand four hundred eighty watts that's ten times what an average home in America uses for electricity per day so that's a lot of juice that he's sucking away the rest of them all sort of floated you can see here floated between eight and nineteen laptops of consumed electricity but still this actually works out into in my mind real energy real effort and real work that's now being pointlessly wasted in stolen from you right so it bears in mind to try to work it back to an actual cost impact of not grabbing this stuff and kicking off your network the other neat thing is is a lot of people probably say like well I think
Mon Aero is you know meant to be able to hide identity well it is but you need to have a wallet to send it into the pool you can use another wallet to send it from the pool to somewhere else and that's sort of where the Chafee and the mix-ins of all the other hashes come in so if you can actually find that original wallet and then find that wallet sitting with someone else you might be able to get some attribution an intent to an actual person it would still be hard because anyone can submit with that hash to the pool if you feeling generous but that would be a little weird anyway so that's sort of
how the pool stuff works and then I was looking at the pools and and how they're used like this and I realized that they're really not sort of like a pool pool sort of implies like group effort or resource sharing in some way right but really it's more like money laundering I though I don't care about the hash that I send it in with just that it's attributed to me and I send it out to other hashes and I have a way of putting it in and cleaning it and sending it back out so that's probably a better way of thinking about it and the conclusions on here I don't know if I really have a good conclusion for you
normally they're like key takeaways or things that you need to take back with you I would just say make sure your network monitoring is looking for stratum leaving your network it's probably a really good strategy to stop this stuff to begin with also endpoint security of course to stop anything executing on there but really what I've learned is that there's a lot of scamming and abusers trying to generate profits off of other people's computers with this stuff more recently and I meant to steal the slides but I didn't have time one of our guys in Romania will be presenting next week at deaf camp and what he caught was a bunch of people using the eternal blue exploit
which wanna cry also used to run around shifting miners from location to location and generating Monera coins with that as well so those are probably the main things to sort of take away from that and that is also like why I don't really dabble around and cryptocurrency at all is because there's just too too much sketchy stuff flying around with it the more I look at it like this the more I'm like I don't want any part to do with this stuff so I'll stop now that's sort of presentation one I have a bonus presentation because I told these guys that I was only gonna take up 30 minutes and they gave me an hour so are there
any questions on this one yes
I never really bothered executing them long enough to look at the network traffic data to see if they use it for c2 they definitely like half these miners like two of them at least are using off-the-shelf well known hashes for just XM our regular configuration I don't think that modified the code at all they don't care like that's the thing this lets you get past having c2 at all you don't need to have c2 you just break it out rake it out rake it out like once a week sort of like the Mirai botnet guy is like I just put this out there once a week I get 300,000 IOT devices why do I need c2 why
do I need persistence guy back there question i I know of names of endpoint solutions like the biggest one on the planet is probably carbon block right I've never deployed an endpoint solution so I can't really advocate for one over another one but what it will do is identify when you have something weird executing your environment that's on the only one computer out of a thousand and anything that will do that for you is a good thing to probably have right what we actually use this for our threat intelligence for is on a network based platform where we'll stop you from communicating to these locations we identify them as hosting malicious shell scripts or malicious BOTS or mining
pools or whatever and we'll flag them for you and halt communication so that's what we're looking at from a network level yes
I heard SELinux selinux a farmer and not much else I'm sorry man right yeah if you have like a file monitoring integrity solution that like either alert you when stuff's modified or prevents it from happening yes for sure but obviously not everyone does that but yes that's that that's a totally valid way of hardening it down but there's there's a lot of times like like that rails example right there's a lot of times where you're gonna end up with a bespoke application that's running rails and no one wants to touch it because everyone's afraid of breaking it and it's running a business critical hoozy what's it's right so I know I actually have written a couple of those business
critical hootie budgets and I don't want to touch it so any other questions about crypto miners llanera kryptonite no if I were you I would try to either figure out or maintain my own blacklist of mining pools as a starting point because there's no reason anything on your network should be touching that stuff okay so as promised I have a bonus presentation and this one I asked them not to record so I'll use foul language to make it extra





