Wędkarstwo Dla Myśliwych - Z Phishingiem Przygody Bezpiecznika
Show transcript [en]
Hello everyone. I'm glad you've come to the large group this Saturday morning. I wouldn't want to, but it's my duty. What am I going to talk about today? The title is a bit exotic, "Hunting for the Mindful". The original version is "Fishing for Hunters". Today we will be doing phishing. We will play around with it, see what are the possibilities and tools to do something with it. There will be some blue teaming, because such research is more blue. Does anyone know these guys? Exactly, this is Eiffel 65, an old song. As Mac said yesterday, I am already old. There will be some coding, different languages, the framework we will use has a lot of plugins
for different languages, so there will be some coding. We will approach the phishing topic a little differently, we will make a little fun and we will approach it non-standard. Everything will not cost us trillions of dollars, we will go in the direction that we will do it for free. I will even try to teach you how to create a system that allows you to track such phishing. Why not Trillion Ballers? Because I'm not a seller, I'm a technical person, so money is a job for someone else, not for me. And if we can do it, we will use all tools to catch this phishing. About me. My name is Adam, very nice to meet you. You are called SecurityBesides. I am the head of the
Cyber Threat Intelligence team in one of the financial institutions. I have been dealing with security for over 15 years, both professionally and privately, in IT for a little longer, so I have some experience there. I used to work in another financial institution, I used to work in Gov, I used to work in Gov, and I used to work in Gov, and I used to work in Gov, and I used to work in Gov, and I used to work in Gov, and I used to work in Gov, and I used to work in Gov, and I used to work in Gov, and I used to work in Gov, and I used to work in Gov, and
I used to work in Gov, and I used to work in Gov, and I used to work in Gov, and I used to work in Gov, and I used to work in Gov, and I used to work in Gov, and I used to work in Gov, and I used to work in Gov, and I used to work in Gov, and I used to work in Gov, and I used to work in Gov, and I used to work in Gov, and I used to work in Gov, and I used to work in Gov, and I used to work in Gov, and I used to work in Gov, and I used to work in Gov, and I
used to work in Gov, and I used to work in Gov, and I used to work in Gov, and I used to work in Gov, and I used to work in Gov, and I used to work in Gov, and I used to work in Gov, and I used to work in Gov, and I used to work in Gov, and I used to work in Gov, and I used to work in Gov, and I used to work in Gov, and I used to work in Gov, and I used to work in Gov, and I used to work in Gov, and I used to work in Gov, and I used to work in Gov, and I used
to work in Gov, and I used to work in Gov, and I used to work in Gov, and I used to work What is today's topic? We will make a introduction to the topic, where the idea was born. We will talk about what is fishing. There are some trendy quotes from Wikipedia, so mine will be from Wikipedia too. We will set a goal. The goal is simple, we will go fishing. Everything will be in a fishing theme today. We will make a bait in the shoelaces. We will get to what it means. Kerguelen action. I don't know if anyone knows what Kerguelen is. Very good. A fish. Very good. It's not that big, I recommend it. Later we'll check the documents and what
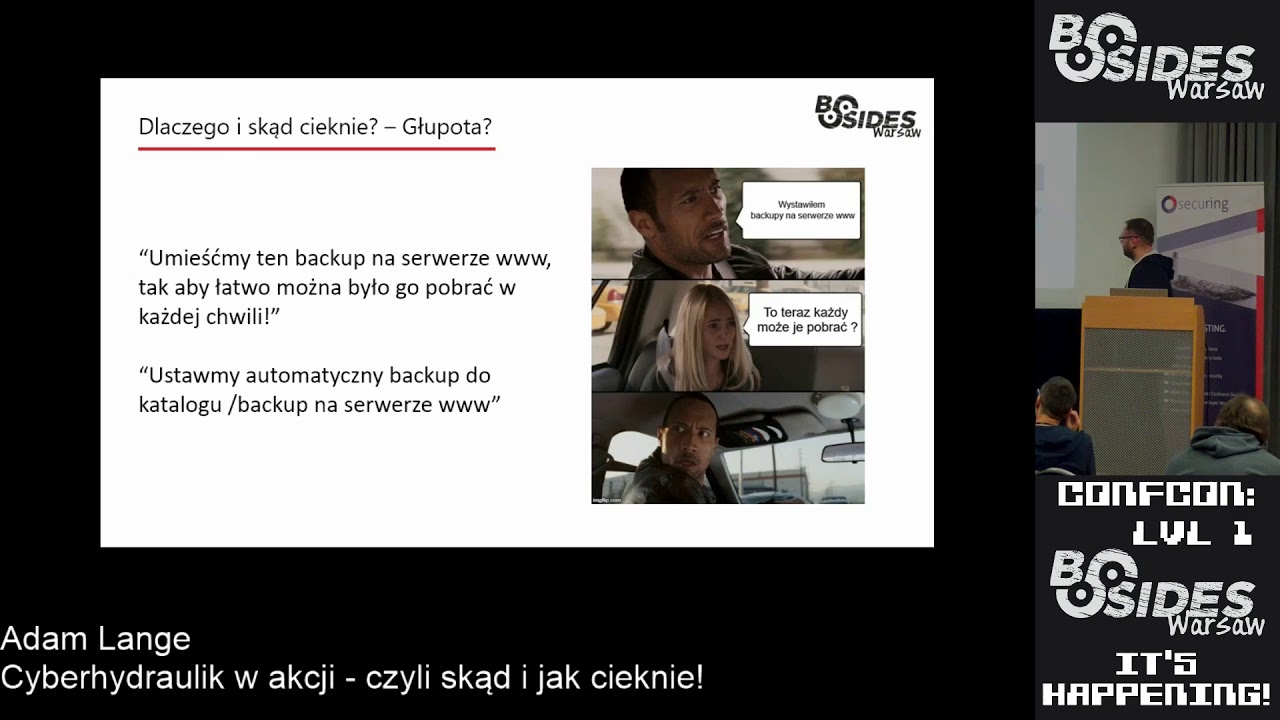
we'll make. And at the end we'll eat a fried fish for dinner. Every presentation has to have a funny quote, so this one will be in it too. It's not original, but I think everyone has already caught it. Where does the idea come from? We all struggle with spam, phishing, hundreds of thousands of times a day. It's a matter of what sensors you have, how rich and propagated your mailbox is. The target is banks, payment services, social services, webmails, etc. It's a matter of the attacking imagination and what you want to achieve. What is our task? Our task is to find a method to detect phishing, analyze it and find a method to block it. What is the reward? A safe client,
employee, company, service. It's a matter of what we invent. And there is a challenge. We like challenges because we work in security and this is our daily bread. What is phishing? Phishing is a fraud method in which a criminal is spreading information to another person or institution in order to fool them. We all know how it works. What is the most popular method of distribution of phishing that we observe on a daily basis? The first is spam, i.e. a normal message or email that is spread to the services or friends. Facebook recently is quite trendy, where messages are sent to encourage people to take action. OLX is also very trendy recently, when it comes to
advertising and encouraging people to post credentials on a fake courier site. These are the main ones we are currently observing. What do phishing look like? This is a phishing page of Facebook. You can see the address - myfacebook.com/relogin/user/something-something-something. Why is this so interesting? Why are these URLs so long? Does anyone know? If the page is open on mobile, it will only show the beginning, because the browser has a very short address bar and it is very nice to confuse the user if this domain is well constructed. We also have Apple, this is a very popular attack, there are a lot of phishing on Apple. Here we also have a domain from space. We have banks, various
payment institutions, here is Wells Fargo, also a curiosity, some Russian domain, I do not think that Wells Fargo is located in Russia. We have Office and all the services of Microsoft, because it is also a cool thing, because you can get to someone's post office, possibly to services such as MSDN, from where you can download serial numbers for Windows and other services. Very interesting, you can also enter someone on Azure, when you type such a password, so it is also quite popular. We have Netflix, then you can buy access to Allegro for 3 PLN. These accesses for 3 PLN are usually taken from phishing. Interestingly, the author of this phishing did not write much, because the domain name is MySubwayCard. There is nothing
with Netflix, I think he was a bit too hasty. We also have PayPal, as standard. PayPal is so old that it is not that big. We have a goal, we want to do something with these accounts, so how to do it? What can we do with it? We will approach this in two ways. We have spam traps that we can set up, I will talk about it in a moment. And we have a cert stream. Does anyone know what a cert stream is? You will find out, because it is a fun game. Spam trap. These are boxes that collect information. Such boxes are often based on faded domains, which is very effective. A catch-all is created on such a domain and all the emails are
sent to one box and they can be processed there. What are the advantages of such a spam trap? We can see the phishing addresses. In Polish campaigns, criminals do not use registered domains. If there are phishing campaigns abroad, there are either DNS entries in other domains that indicate a given service, or a private domain is bought, registered. In Poland, hosting accounts are more popular, so phishing is more difficult. Spamtrap helps here. We can find spam-type addresses on Spamtrap, like "Penis" or something like that, for 5 PLN, university degree, etc. The advantage of SpamTrap is that we also get samples of malicious programming. In all campaigns in Poland, we always get something and we can also try to do something
with it. What are the disadvantages of SpamTrap? The quality of data obtained in this method depends on the quality of the email address and/or the quality of the domain, because in fact, with SpamTrap, you have to grow this domain a bit, it must be known on the Internet. The cost of infrastructure, domain and services. All this has to be paid for. If we have many domains, we multiply the cost by many domains. Here is CertStream. CertStream is an aggregator of logos published under Certificate Transparency. This is an act that orders all of you, or at least most of you, to publish information about these certificates in real time. If an SSL certificate is issued, all information about this certificate is
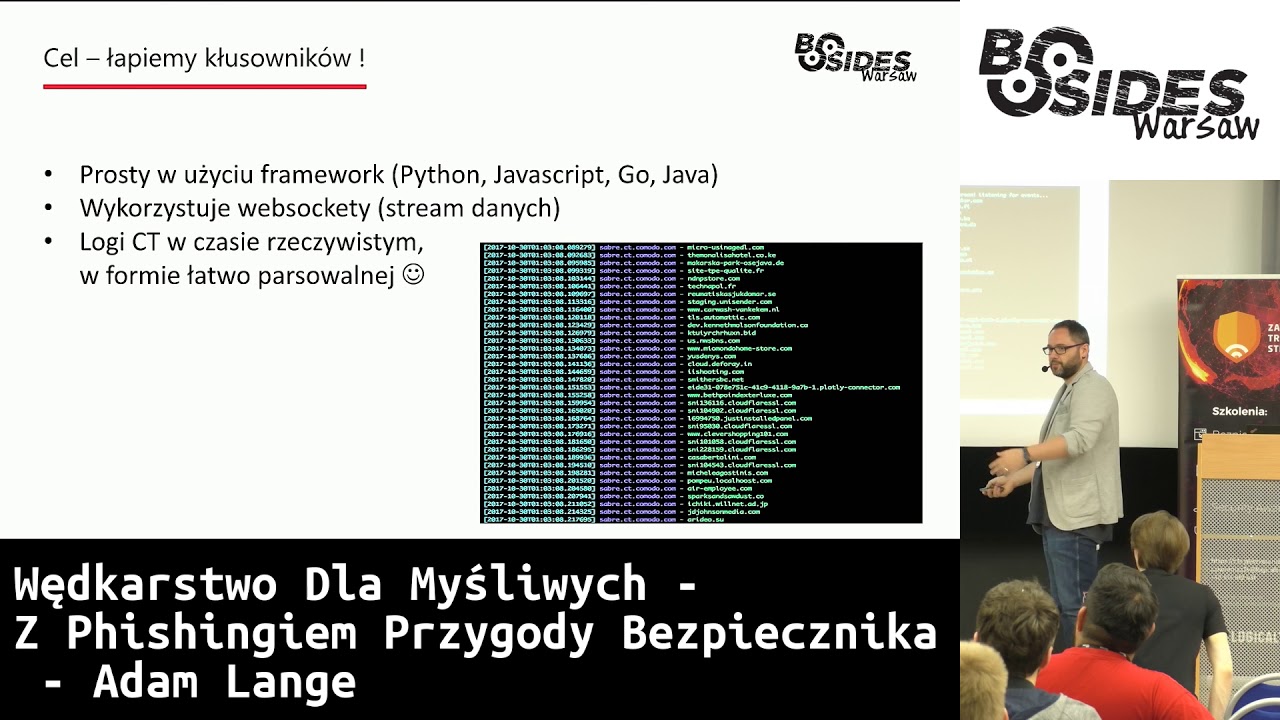
available publicly, you can read it and do something with it. CERSTeam is such a cool service that it is free. I recommend reading the address. It's free. You can read about the Certificate Transparency Act on their website. There is even a RFC for it. And now this. CertiSIM has a simple framework. It has many possibilities. You can use it in Python, JavaScript, Go, Java, C#, In Emacs, in Commodore Basic, in anything. I use WebSockets. Thanks to them we have data stream. This stream is non-stop. It runs on animated GIF. That's how it looks. You need a really strong machine to process everything nicely. And we have logs in real time. In an easy-to-work format, because it's all nice JSON. You can do
something nice with it. These logs are also available in the form of text downloads, available on the CERN Stream website. We will do a trick in shuwaras, so how to bite it. We have SpamTrap and we can use the first method, i.e. register mailboxes in the available free services. We need to get some programming ready, I recommend Python because it's nice to write fast, but if you prefer C#, you can play with it. It would be best if it all had some framework or a library for iMap or POP3 services, because we have to reach for these mails to do something with them. We need to have some parser so that we don't have to play with regex. The best option
would be to have a backend in the form of an Internet page, or a database, so that you can browse it. Because if you put everything into a file, it's hard to search and play with it. So it's best to have a background. And above all, you need to have rules and imagination. How to approach this? Imagination is always required. You need to grasp the topic. But there is still a lot of work with the reputation of the addresses in these mailboxes. You have to dust them somewhere, register on some online forums, general services, etc. so that all these crawlers that collect email addresses, to pull it out and then in some time they started spamming these boxes. Method 2: registration of borrowed or gone out
popular online domains. There are services that are currently indicating You can sort the domains in the table by PageRank, by the number of indexed pages, etc. If such a domain is missing somewhere, you can quickly register it, make a catch-all on a post server, direct it there and there will be some emails for sure. There will probably be a lot of them, so it's a very effective method, but it's expensive. Domains need to be bought. Domain.com is an average of $10. We want the system to be effective, so we have to buy a little bit of these domains. The rest remains the same. We have to learn some programming, etc. But we have CERSTIM. As I recall, CERSTIM is free.
Here, you only need to know some programming language. As I say, I prefer Python in this case. Standard backend, some optional database. And again, rules and imagination what we want to do with this stream. We will do this action of Kergulen. What are our assumptions in this super small project? We will use the stream because it is free. I will repeat it, it is free, it is cool, use it. We will monitor domains based on keywords. The most common phishing in the world is on PayPal, Ebay, OneDrive, Office 365. You can also expand these keywords, bank, accounts, etc. We save the result to a database so that it does not disappear. We have a piece of the service that has been added to the
third stream. and based on keywords, here we have recovery, your order, etc. Here we have Office 365, and we can see it here. For peace of mind, I will take an IP for Neynomen to use it later. So we have a service in Python. You can create an Internet page, a timestamp, a domain name and an IP address. Then you can do something cool with these domains. Now we will approach the topic in a slightly different way. We will take documents. We are now such "Texas guards" or "catchers" or "catchers" - those who phish. We can dig a little deeper into what we have found. Before MIS and PATUS start and configure the phishing page, we usually
see something like this: a page index from the Open Directory. There is nothing here, but sometimes we find something like this: This is a surprise. We have a phishing domain on PayPal and we have a phishing kit. Installation version. You can download it in Zip and have fun with it. We will enrich our monitor so that it can enter this page, as you can see in the keyword, and see if a given domain has an open directory. It can be done quickly with curl. Here we found it. I recommend Paypal. We have 4 cases like this. CELS Team has it in them that sometimes they show the same thing many times. I didn't want to filter it and do it with UNIQs, so I don't
pay attention to it. At most, they will download the same file twice. Whatever. Once we have it, we can enrich our super web system with what we see on these phishing sites. We have found such zips. There are not only zips, we have rar files, various types of archives, we have these gz, sometimes we get back-ups of databases, text files, licenses, so you can really collect the whole mule from this search stream and then dig into it. But what's in the box? Tell me what's in the box. So we have these ZIPs, we stole something from this archive. We can look at what's inside. Sometimes these authors of phishing kits are so nice that they introduce themselves first of all. They even
have a website. They tell you how to configure a given phishing kit. Here we have a configuration file. How to contact them to buy the premium version. There are also Facebook pages, in most cases they are for children who are big hackers and modify these things in PHP. We can also shoot them a donate on BTC if we like it. This is a configuration file for a phishing kit, it was probably on PayPal. It's all in PHP, so it's easier for a young person to write something in PHP. And we have the email address, where the data is being sent. If we have a phishing kit and we know the domain, we can quickly read where all the credentials that users send are. As we already know, our
super web service will add the click option. I recommend it. Once we click, we can create more information about a given domain. We can start filling it out. Here we have a domain where we found the phishing kit, at what IP address the domain was resolved. You can archive it, calculate the hash from this zip, but we can also add, because we already know where to look for it, the address where the data is going. Once we have all this, it would be good to categorize and name it. So I adopted a methodology that if the archive contains a file X, then it is a fishing kit type Z from the family Y. The simplest, the simplest. You can use YARs here. Now I will assign
my whole system to YARs, because it is a little faster and more flexible than looking at files, especially since there are many mutations of these fishing kits. Some author will write to himself, another will add a file, etc. So these are some tricks. Here is one of the Fishing Kits, we see some files, some of them are very characteristic, for example, Bokach Shop PHP is a Fishing Kit for PayPal. So if we have a file that appears only in the Fishing Kit, this is a file method, not a jar method, Then we can see the artifact, the name of the file, the author and categorize it. We complement our super web system for phishing. We can now take files, unpack them and look at the
signatures. This one will be of the Apple iCloud type, because this phishing kit can simulate both the iCloud and the Apple website. And from the Bokach Shop family, because there are a lot of mutations. And when we can identify such phishing kits, We go looking for artifacts and we name them. We already know the structure of the files, we have analyzed hundreds of them. I did it, you don't have to do it. At the moment, I have collected about 4000 samples and fishing kits from the beginning of the year. I recommend it, it's fun. We can also use FingerPit without Open Directory. We know how the fishing kits are constructed, what catalogs are in the
fishing kit. We are able to extract data from such fishing kits with a few questions. Here we have a fishing for OneDrive. We have detected it. It is written as a whole bot. We can categorize it, because we send a few questions and we know that the Vires family fishing kits have such a unique file in such a catalog. We send a question and then we are sure. We also know where the files are stored, where the fishing kit stores these things. Sometimes I don't write on the disk, sometimes I send an email, but we'll get there soon. So we can reach for this file and extract the files that have been phished and report them to the appropriate suppliers, such
as AOL, Outlook, etc. Or to Abusa, do something with it. I don't recommend using it or trying to log in there, because it's a crime, so we as researchers don't do it. I advise against it. No one would want to bury it in a postbox. These are victims. Once we have all this, we enrich our system with victims. If we are able to extract it, we can immediately enter it into the database. Here we have a different tag, so we can handle it. From the domain we found, we can add an IP owner, who is written as the owner of the address class. We can fill in the abuser. I added a function to write notifications automatically. After clicking, an automatic message is sent to
the domain that there is a phishing kit and that there are victims. We will take a fish. Everything is fine, everything is going well. We already have a system that I showed you. It's the same, OneDrive. Since we are researchers, we can enrich our mechanism for exploiting. These are things written in PHP, these people are not programmers, they do not associate how to write safely. Sometimes, without the phishing kit, you can get an attacking email address. But how to do it? It's some kind of black magic in Python. But we have the code, we have the code, we have downloaded it, we know how it works, we can analyze it. So we look at this code. In
this case, I don't remember what the phishing kit was. We have a function that sends an email. If a user is phished, and sends all the data in the credentials, then an email is sent to the user defined in the email configuration file. But because these people don't really know about security, From the parameter, they take additional header in the mail. The mail function in PHP takes one of the parameters of this function, which is additional headers. And these additional headers take from the user input. They could be omitted, but why? How can you take them from the input? So we have such a super hack tool, which is called burp. We have a phishing kit, so
we don't attack the domain, we just put it on a web server. We found a log file that is responsible for sending this email. We can see some parameters in this post. We have victim email, login password. Of course, these are not appropriate. We have mail add, which is a parameter that is not standard when sending a phishing kit. We found it by analyzing the phishing kit. We can add %0a, i.e. enter. add bcc header and send us our address and email address where we want to get a copy. And good morning, we get a copy of the phishing email. bcc is a nice function because we see who it went to. We are only on copy, so without having access
to the configuration file, we are able to extract addresses where phishing is running. Based on this type of exploits, we can quickly modify our system so that it automatically detects phishing, even if it does not see the Open Directory, so that it tries to fingerprint, immediately sends a set comment, which will allow us to look at the information and correlate it with other parsers. You can do it, for example, you can make specific boxes for each request. Here is also the catch-all method, so it's a bit of fun. But it helps because we don't focus only on what we found in the file, but we can harvest everything and collect all the intelligence about this phishing.
When we are talking about phishing, our system can also handle malware. When we come back to spam traps, where we collect all this hay and wool from the Internet, they spam us as much as necessary. We can also look at the connectors, the virus total, and the detection of these connectors. Here is an example. And we can also draw up specific malware campaigns and do something with them. This system can evolve in a very interesting direction. I recommend such games because I get a lot of feedback from my colleagues that I should finally publish it. Now this system looks a bit different, it's more expanded. Maybe at the beginning of the year I'll share it with you. I also have a plan to add,
everyone will be able to register, add their own keyword and get some cool notifications. So the work is going on. We collect information about future and active campaigns. You can see that the system is a bit more mature. You can see the domain on the first page, but we have tags right away. We also have all the information we have already collected. I say that there may be much more information. We have more possibilities here. For now, we are only looking at domain names. But Certsteam is the whole material about the certificate issued for a given domain. We can look at who issued the certificate, to whom the certificate was issued, serial numbers. We have a really huge
amount of data there that can be tried to cover and, for example, correlated. This is a MISP chart, I recommend the system, it is very cool. It can make such correlations. If we collect all this data, we can determine that, for example, there are only three actors in a given subnet. We have their email addresses, we can narrow the intelligence a bit. We can also see how actors migrate through the infrastructure, fingerprinting them, so we can see where they are jumping. This way we are able to capture such proof-bullets that should be blocked, because there is a high probability that there will be a lot of malware spam or phishing. So it helps a lot. We do it so that our users can
take a nap. It's a great job, great fun, I recommend it. Thank you. That's it. If anyone has any questions... You said that you plan to publish it with the ability to add keywords. Have you considered adding regex? I work on it myself, I play with it, I do it after hours at home, so it will be evaluating it slowly. For the moment it is not only doing phishing, but also malware. This malware is automatically analyzing it, it is really on the rich side. We'll see. If I have time, then I will, if not, then I won't. What can I say? Anyone else? OK, that's it. Hey, very cool system. I liked how you added new features to it. You talked about exploiting and
I thought you'd show us a button to exploit the attacker. I mean, you could spam it with a box or steal a password and change it. Did you think about that? No, let's not exaggerate. We do it within limits, we don't hack these systems. This is the use of some weakness that It does not allow access to these boxes. We do not want to have the prosecutor's office on our necks. I do not recommend doing this. The second approach is to fill the boxes with emails. This does not work, because the configuration will be changed in a moment, the email will be completely different and it will be fun again. It makes no sense. It is better to gather this information
quietly, to send it to the appropriate services or hosting owners, etc. to process it in their own way rather than fight with the windmills. Anyone else? Thank you Adam, very nice presentation. I have a question for the MISP graph. Is it the MISP graph from the phishing you're uploading to MISP? Yes, at the moment I don't want to change the system and create a graph in my system. I'm lazy, but I do it in my spare time. Yes, all the data in MISP has a nice interface, in which you can upload API automatically. It's nice to correlate it by itself. And correlation based on IP addresses and IP code? It's different. I set the correlation on IPs, I set it on email addresses, which I
can get on some certificate parameters, so that it makes sense. IPs are not very meaningful. I do it, but it's more to make such nice charts, not to have something out of it. Thanks. I'm running around today. Where was it? Hey, have you tried to use any ready-made systems to collect events and correlate events? If not, why? Or if you tried and you don't use them, why? That's a good question. I have this approach, I try to instill it in my employees. I like prototyping. Most of my ideas are done on the go. As you saw, this piece of Python was written in a few minutes. It's quite simple. When I see that something will come out of it, I start thinking about how to
use some systems to make it easier. For now, I have this approach that I have to see the effect quickly. So for now I'm not doing it. I'm doing it by the way, but I'll think about it. It's a matter of time. There's always too little time. But yes, I want to do it someday. All of you? Oh, okay. You still have to run. But they will do it on purpose so that I can run today. Did you think about making the URL available to the list? Yes, I did. I forgot to mention that the machine can do it, of course some services don't have API, so you have to work with it, parse, scrap, etc. But
the machine can do it for me. I'm 100% sure of that, because there is a lot of garbage there, which is not actually phishing. and what is fingerprinted in 100% is automatically reported. It is not visible on the system, but I have a feature that it is reported automatically. I work on it all the time. Anyone else? But at least you don't have to walk. Have you left a lot of such traps in the network? I don't know. Very good. Such a work, I don't know. Please don't phishing. Adam, I'm going to take a look at your set. Thank you for the presentation. I hope you will come back next year. I have a short time.