G1234! - Ransombile, Yet Another Reason to Ditch SMS - Martin Vigo
Show transcript [en]
okay so so let's get started so my name is Martin Vigo I'm a product security lead I'm from Galicia Spain you haven't been there go check it out we have the best seafood in the world I said that in every talk no one has gone there yet but I really like research I like scuba diving and I like gin tonics if you guys want ask questions later you know this is a picture of my sister in me when I was 9 I believe and that was my first computer I really loved this picture it's an Amstrad anyone had that computer I think it was only sold in Europe yeah really nice and I'm playing probably the best game ever written in
Spain which is Laval dia del creaming it's a kind of anthem where I love the game if you haven't played and you like of underwear make sure to download it so question for the audience a have you left your phone unattended ever like on the desk going to the bathroom or on the coffee okay I knew the audience is gonna be hostile and I'll raise their hands okay that's good I'm sure you're in the live stream so it's like yeah me did you disable the system in the lock screen by the way the one on the left is the Cortana Windows Mobile no one knows about it it took me a while to find the
icon did you disable notifications on the lock screen because for example for in iOS 11 should you use to come by default now it's not the case so then there is a question now what can the system do while the device is locked which is kinda what this talk is around what is the things you guys think that when you say hey Siri and the device is locked secure encrypted and all that stuff I can do that you guys think may be an issue security wise that's the easiest bypass ever any idea what the kind of stuff that you could do that you guys think oh maybe these are some security consequences phone calls yeah
there could be like you know like contacts I don't think it gives you I believe you cannot open a website I believe airdrop you can activate that's a good one another thing that you can do it's a actually send email thing as a message so this all started these comes from like one day I received who uses van here I guess many of you so I got a text from my friend we're at a party and he paid for the Jing so he sent me like you know he wanted to charge me Brenna allows you to do that not that not just that you pay but he can charge it so I got a text and he was saying hey this
guy wants to charge you 50 bucks reply to this message with yes or I don't remember what I had to reply and I was like interesting because I can do that from the lock screen right at the time I had it I could see the preview and everything so if I can do that if I can just try to charge someone and answer an SMS for them then this is what happening and this is a demo so the device is locked no there is there is all right so there I asked Siri Who am I so you will give me the phone number so that short code is the one from venmo so what I'm
doing here is I'm actually activating the being able to pay over SMS on the victim because it turns out that I found out the phone so I can reply there and say activate and you will activate it so now the victim now I can charge the victim and I got activated the service so the victim can pay by replying to an SMS so on the Left I go to bank more as an attacker and charge the victim with the phone number I got in the lock screen in this case $1 because I don't have a lot of money so I asked you to read my latest text so yeah you didn't have to reply yes I forgot you have to
play with a code yes so I'm replying to the text [Music] that's me trying to be cool and you will see I will refresh the side and I just stole one dollar from a device that was actually locked and theoretically secured so when I found this out and I wrote a blog post about it I thought oh this is very interesting and my website doesn't have a lot of traffic right I I write a lot about security but you know it's not like a top website or anything and I I went once to look at my Google Analytics saying this is the top seven of how the people gets to my site there is a lot of articles but there is also a
lot of bad people in the world like this is the top seven people just wants to steal money and actually I guess I have the honor or dishonor that if you look if you search in Google for how to steal money I think now I'm the third one but it used to be for one year the first result in Google if you look up how to steal money you can test it later so I guess it's it's an honor so ok so when I found this out I was like interesting huh what else can we do right the goal for me was how can we broaden the impact and and and help push the the you know
the industry towards like understanding that SMS is not meant to be a secure channel for sensitive actions and I started to look and there is a lot of things that you can do over SMS you can reset passwords you can actually register like whatsapp for example you don't have a username and password you've verified that you are the owner of the phone that you claim by replying to a text or you can also use it for 2fa in many services so in this issue with the SMS I mean I'm not talking about anything new here so I went to do searches per year in Google and went down to 2015 and you see on the Left
2015 2016 2017 2018 always talking about the same thing we shouldn't be using SMS for security purposes but no but it's not that article start there about it nest itself in one of the drafts then there was a controversy you guys may be familiar with it but it was actually discouraged or deprecating SMS originally and then they just discourage it officially and you probably heard about what happened with ready that it was recently hack thing and one of the things that happened was the two FA was over SMS so I think there was some sim swap in there so this is happening this is real we have been talking about it for years this happens a lot in security and
nothing gets fixed so my objective now is to help with the industry to stop relying on SMS as a secure channel and this is why I did this talk and I I wanted to do something that is just yet another reason to teach SMS so the first thing I wanted to know is okay I know I can reset passwords I know two FA is being used for that I know for verification purposes so I found this really cool service that actually lists all the short codes like you saw for venmo for services so here I can use this and try to look at banks that use it and for what purposes so I can find a
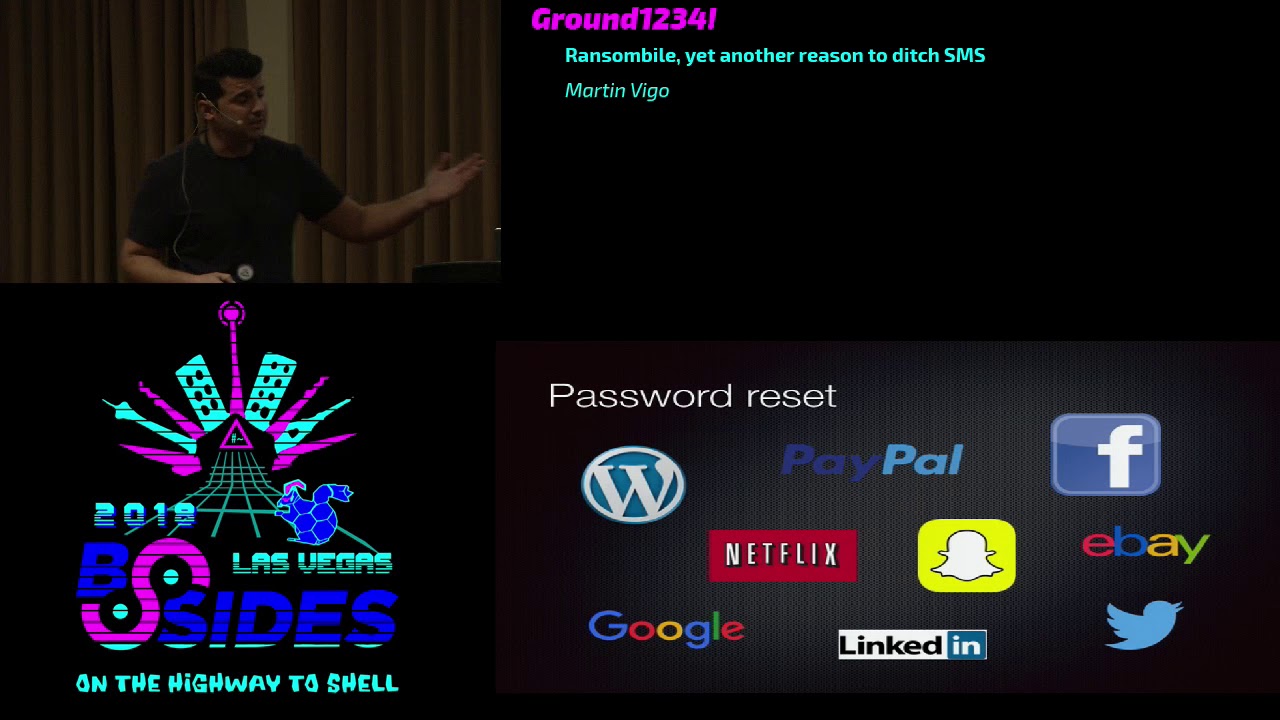
lot of services thanks to this they use it rather than me just trying to go to the website set up a username and see what options I have for two of a password reset and all that stuff and this is just a kind of like a alexa top 100 version just a small subset but for password reset you can do it / SMS in WordPress Google Netflix Instagram PayPal Facebook eBay Twitter and LinkedIn you can do two-factor authentication the three big ones we over SMS Microsoft Apple Yahoo you can do verification what's up in signal Twilio is a is a VoIP service so programmatically you can make phone calls and stuff like that but one of the
things it allows you to do is to own a caller ID so and you own that caller ID so basically when you make a phone call programmatically will display that number by you verifying that you own a phone number over SMS and Google Voice you can have virtual numbers but you need to tie them to a real number a lot of scammers use this and you can verify a phone number you can just start it to someone else if you do it / SMS into an attack like I showed with mango so the conclusion here is there is many services that use SMS as a secure channel for sensitive actions and it's it's used in different
environments for to a verification and password reset so let's look at that tack vector right how will it look like when we try to attack a mobile device that is locked because in the end this is what the talk is about it if a mobile device that is locked that we all feel like it's encrypted we have the FBI fighting with Apple because they supposedly cannot do anything about it and all this that sense of security that we'll have when we have a mobile device locked so the first thing will be to obtain the victim's email the second one will be too easy to initiate password reset in all services because we just so many of them you can password reset over
SMS we want to obtain the secret code that is sent over SMS like we saw in Bergamo and then free leading to the UI again to complete the password reset and then we just set the new password and that's it right so how do we obtain the victim's email so in this case what we can do is on a block device we say hey sent an email to attacker at domain.com basically an email that the attacker controls and and you basically will say that in this case - Siri so we'll send an email that's how I can get your email because you cannot get it anymore from saying Who am I you used to be the case
now it only displays the phone number so you just ask Siri to send an email and you receive it in your email so you know what the email was how do we obtain the secret codes as we talked about many people doesn't disable the the preview of texts in the lock screen and you can even ask Siri to read the text for you so you have you have to actively disable this so you can just see it there so we have now that if I have physical access to a locked device I can get these two pieces of information but we still have three more which is a we have to initiate the password reset we have to
complete the password reset with the codes that we got in the lock screen and we have to set new passwords so there is a lot to compromise because we have a lot of websites that we can compromise if we have physical access to a locked device but we don't have we have limited time may I take five minutes to pee so if I left my my device on the table right that's the time you have so we need automation that's the key so and that's how I created a wrote a ransom bot which confirmed ransomware embalm well I don't have a lot of creativity that's not one of my strengths but as you can see it's
basically an app a mobile app in reality it's a website but I use CSS used to so you can use it on the on your on your mobile and the reason is because you may be walking around and find a phone on the floor or you want to prank your friends or you want to just make some money so you basically what helps you to do is it automates the entire password reset process and in this case I started by using burp and looking at the api's of like you know Google all that stuff and it's just very complex because it changes a lot and the other the other thing is I was getting hit with captures
all the time because it will kind of detect that I was doing something not really in the usual way so I found that selenium is much better for several reasons selenium is basically a library or yeah a library that allows you to do automation at the UI level and this is used a lot by developers when you want to test if I click here here here and here do I have these CSS buttons with these colors and stuff like that so this is super useful not only because now you don't need to reverse any any api's or look at verb but it's also super easy because there is even a plugin for Firefox that you can literally click
around it record the movement generates the code for you so it takes me three minutes to add a new service that I can that I can compromise to run some bar because I just use Firefox and I literally reset a password while that is recording and generating the code which is the end all it does is with code it sells it uses CSS as pointers where okay this is the text box where you put the stuff this is the button you click and stuff like that so super super simple to make this open-source and just people can add a lot of new payloads for new websites so now we have that we cover all the steps so this is really how it
looks like how ransomware works right we have on the left side we have the the victims device which is locked so you will take that phone or you found the phone on the floor for example right you take that phone and say hey send an email to victims of ransom at gmail.com which is an email you as an attacker all about subject saying content that is just to fill up everything that city ones in ransom val is monitoring their email in this case I use Gmail as a proof of concept and I'm just monitoring that all the timing as soon as a new email get it will take that the others where it's been sent
from and it's fitted into the app automatically it starts to initiate the password resets for all those services using a UI automation so I will start to see in the victims phone the codes start to come in so all I have to do is to read them from the screen enter in in the UI of ransom bar and click town and then it will go it will complete the the password reset process and it will add the password that you want and now you just compromised the person's digital life in two three minutes and now you can go and demand money for it don't do that though so I'm gonna do a demo now and I want to introduce you to Tom
promise compromise is a play of words of compromise they Priscilla helped me here again creativity is not our strength but basically this is the victim writing he's a millennial because he uses Gmail as an email as his email account right and you know he likes to tweet and he uses Facebook so he uses social networks as well and he has a website in WordPress and you know when he wants to pay his friends he uses paper and and he has all that stuff of his phone setup so so he's like many of us actually actually I integrated the demo here so before I started on the right you it's a simulator that basically it's a
simulator that basically has the ransom below that on the left side is the victims phone that is locked
gonna be here so you seeing email it's gonna show now Tom promise' gmail.com because the app is monitoring the email so I only have to click that of course I can automate this as well so I don't have to interact with the app at all but for the demo I want you guys to see what is going on so you see that now you're doping a lot of browsers and I'm not doing anything this is automatic you'll see it putting the the password that I want it selects the the SMS password research over SMS after putting the email not the password and now I will start to receive codes and I did that I did it did that for all the websites so
you see that SMS as I started to come in and because that person didn't disable the preview on the lock screen I can see those codes so all I need to do now is to go and the tool is waiting for those 10 codes to complete the password process so I only have to add it there more SMS are going to come in I'm a little slow typing better
I just wanted to make sure that in the demo but obviously you can do this a little faster but the point being you see how it works it automatically started the password reset process you've received the SMSs the tool is waiting now for the for the temp codes and we will just take them and feed them into into the UI agang and just complete the password reset with the password that you see above that is what you picked so now that I have all of them I just click one by one again just to just so that you can see how the tool works but obviously I could just do this automatically and you see that it's
doing exactly the same again so I just compromised Twitter I just compromised PayPal and facebooking on the other apps are in the background you just don't see them but this is how easy this thank you so and it will suck to get that many accounts compromised right so losing your phone now is not really just about the money you lose the thousand bucks for the iPhone X I mean if you give me thousand dollars or keeping my emails and papers and stuff I probably give you a thousand dollars and keep my you know digital life so the thing is a I want to I'm open sourcing this I'm not creating a tool that you can go and then start to
compromise people's mode of POC just to prove the concept right and you can go there I didn't uploaded it yet I will do tonight well I will do it these days but a yeah this week I definitely had it I just need to touch a little bit because it's a little bit of spaghetti code but a so you can play with it so conclusions a lot mobile device is still insecure which is kind of not a lot of people especially not the people in security has the feeling unattended mobile devices can be a bigger risk than unattended computers and companies tend to ignore this and a lot of companies you know they force you when you when
you get out to lock the screen and all that starving and they put locks or no one can physically take take the laptop and things like that but mobile devices is like okay they force it to have a ping and that's it but sometimes mDM's they don't force you to this the preview or to disable Siri on the lockscreen so and as I said the consequences of losing a song are not only monetary which is the the idea that people usually has or like when you lose it it's like oh man I got to now spend another thousand dollars so now we can the get in a set in a second part of the top because everything I told you you
need physical access to the device to unlock the device but you need physical access so I wanted to explore the idea of how could we do this without even physical access to the device so if we think about the attack vector there is two things in which it requires us to have physical access right which is obtaining the victims email because I need to ask the mobile assistant to send an email and obtain the secret codes because I need the mobile device to look at the screen to look at the other codes so how could we do obtaining the victims email without physical access to the device well I just looked at the previous art and there is several
research that allows you to interact with the mobile device with a mobile assistant we actually from distance right so the first one hidden voice commands is pretty interesting so basically what they do is they mix the payloads like for example hey Siri sent an email in between noises or garbling sounds and so that humans may not able to understand that it's actually sending a payload to Siri so that's pretty cool but you know I looked at the demo you can still tell a little bit but I mean I was paying attention right if you are in a casual conversation and you hear noise then you probably don't realize the second one is fantastic so these guys
what they did is for example if you have your device with a with with headphones on right with that is plugged in with cable not bluetooth ones a what they do is they send a electromagnetic signals that the coil of the headphones you you saw this right it's really awesome that the call of day of the headphone picks up and they do it in a way that it will trick the phone into thinking that that signal was coming from the headphones and in realities payloads to Siri they did even better a the year after I believe and they do it now through the church in Cairo if I believe correctly because right now not a lot of people
anymore uses the thing but they are able to do through the charging of is pretty insane and the third one which became very popular it's kind of like the hidden voice command but much better in the hinted voice comment we hear the the growling sound right but this what these guys do they put the palos just like we will speak it but at a frequency that the human ear cannot really hear but the mobile device can so you can literally talk to the mobile assistant but we humans cannot hear a lot level I think it's 20 Hertz I don't remember exactly hmm 27,000 so and I actually want to show you how it works so so here they do
the real thing right they have an Audi on their device and they just play it and the phone obviously picks it up so now they plug it into that to the amplifier and they do it with a different frequency and you if you look at the phone now they are playing the sound we don't hear anything right but look at the phone so that pedal I talked to the 300 I wrote emails to them I was with back and forth with this guidance from the other two research and they confirm you can perfectly send an email with with any of those three research so we have now the weekend if I'm close to you but you have your phone on your
pocket I am able to trigger your mobile assistant to send an email how about obtaining secret codes for SMS that is also existing research on this as the seven attacks probably all of you have heard already but it is basically the protocol how the carrier's work specially when you are roaming and how they route calls and stuff like that I'm not an expert on the field but I put references for you to go watch these talks that are fantastic and so with these attacks you are able you could be able to look snooping into sms's Shuji done great attacks and the cipher that is broken the it's used there you could use that as well and that's kind
of like more a passive attack or femtocells in Def Con 21 this is a fantastic talk so basically it's like a small base station that you can use and these guys were able to get root access and compromise it and the way mobile devices work if I'm closer to you than they or in reality if I have stronger signal kinda because I'm closer to you he would connect to me and not to the tower and because I have root access on the on the tower I'm able also to to do a lot of stuff like possibly looking at Sam s and then there is the old now that is becoming very popular the sim swapping they call t-mobile and start to
tell them some social engineering stuff and they basically will own your phone number so the conclusions are it is possible to perform these attacks without physical access to the device in theory because I'm not showing you a demo and your wishes demand the POC or get the out right so there is reasons why I did I don't have a demo and mostly is because of legal reasons like messing with GSM it's not it's kind of not on the border it's very illegal you can still do stuff but eh but yeah this actually I wanted to put here in case you guys think it could be something worth it what I pictured is a backpack you know with basically some
SDR or stuff that can you know you can do this attacks for GSM and also the amplifier the triggers the thing and you have an Ubuntu running with ransom Bal and kind of do that automatically that will be really cool so another conclusion SMS wasn't designed with security in mind in order to be used as a secure channel online service I should encourage up based temp codes to FA whatever and they make SMS opting sometimes the only way to get to FA is over SMS it's better to have two FA than not to have it but they should only services what I try to help push the industry like all the research that has been done since 2014 is that companies
actually adopt this recommendations for you just to finish don't leave your mobile device unattended you saw there is some bad stuff can happen sable the assistant in the lock screen disable notifications previewing the lock screen use apps for two FA and you and have to obey don't provide your phone number if not required I see that in a lot of services you don't have to and and it's the only way to get to a faith and do it but you can use actually a virtual phone number like Google Voice and you can prevent sim swapping attacks and even like you know open-source intelligence like if you go now to ebay if someone has an ebay account in a
PayPal account you will be able to get seven of the ten digits because you go to reset password with the emailing will tell you should I send the code to a four one five star star star star star five three but then you go to PayPal and it gives you the last four so just an idea will be nice and I kind of started to do it just use this automation that I have which already is happening and just get those numbers so you can go reset password' but you don't really are interested in digesting finding out what the phone number is just an idea of you guys want to do it and they check the
settings to disable security challenges over SMS I think link I think Google lets you pick between SMS a sort between SMS and 2fa apps and it defaults to SMS so that's one of the things that I was mentioning so in some services you can actually do this thank you very much was a real pleasure I'm giving another talk in Def Con come check it out it's very cool about hacking boy smoke systems and what the impact is is actually somewhat related to what we talked here about from a different angle and it's on Friday 1:00 p.m. in track one and thank you very much [Music] and I don't know if you guys have any questions I think we need to use the mic
you have your questions please put your hand up there's a question that but no some talk just wondering in your experience or your observations when you take people through this say on a one-on-one basis how many people have actually hardened to a pretty good standard they're they're phone from an unauthenticated state so I haven't I did not take the numbers which probably I should have done first kind of like a survey what I can tell you is security minded people like in the audience they mostly didn't have it but some of them didn't I make fun of them most of my friends that are not in the security industry they all have the preview they
all did and I for iOS so everything and now with the iPhone X it will blur e8 and when you look at it and it is pricey because it authenticates you so we are doing better for sure but there is still all devices that run fantastic thanks to Talk yeah just learning about the androids you mentioned the apartment Siri but about the androids I'm not really sure Rodney using yeah so I use server because that I have an iPhone and testing devices are iPhone so I know from what questions to my to my friends and from testing a hundred has the same issue but I believe at the time of iOS Tang and whatever was the version
of Android under already had it had the preview disabled by default so you have to actively kind of like do a mistake and activate it while it was not the case for iOS but this is totally applicable I mean you have the notification on the lock screen and you have 4k Google so it's totally up quick end to Windows Mobile just in case any other questions alright let's go drink that thank you [Applause]





