iOS Malware: Myth or Reality?
Show transcript [en]
hi so uh I'm Julian I'm coming from Switzerland and the mountains sorry I don't have chocolate for all of you um I'm working for mssp as a kind of security architect or security expert part of a team doing applied research or technology scouting to to know what would be the the next stuff um I'm going to talk about iOS malware but the name of the company sounds like one of the AV vendor but I'm not really to to AV vendor so it's not to sell you a new product infos is close but not in this building um and otherwise I'm doing uh also CTF and stuff like that so today's talk will be about iOS malware but if we looked
into the news most of the time what we heard since 2010 is a lot of stuff about Android uh banking malware or information stealing software on Droid so you might said Okay I I I've heard about a lot of them so I've only pick a few there but if we if we looked at iOS you might said okay it's not even a problem because from last year uh Verizon DB report they said that paraphrasing Jay-Z I got 99 problems and mobile malware isn't even one person of them so what they basically said is okay but there is no mobile malware and they I highlighted something that is really hard to read but what they said is all
the suspicious activity related to iOS malware was in fact a false positive triggered on Android devices uh so this is their point of view um I tend to think that they might have um some kind of bias into the the information that they had because if you look at all the companies working into their uh the the report that they build every year there is not that lot of uh company into Asia there is a lot of European and US companies but not in in in Asia this is where actually most of the iOS malware are spread into the for the moment so publicly um so it's more widespread than we we might think and the the more at
risk might be uh companies especially the high-profile ones where we might have some some type of attacks so if we look there are still uh some types of iOS smartware that has been published or discovered through the year the first one was in 2009 it was named iy the idea was actually kind of around somewhere but what it did was lock your screen and change your password so your passcode and if you don't didn't pay uh five bucks then it will not unlock your password how it spread it was a worm and it spread by using the default SSH account on iOS one when there was the first jailbreak so and the problem is that once you're even on a 3G or LT
network of operators most of the time there is no segmentation between all the devices and you can directly access one another devices provided that you know their IP address has been the problem has been recently shown in the news so last summer when uh Charlie Miller did the talk on Jeep hacking caring I don't know if you you've read the details but what they did they were able to actually access the G the LTE modem of the Jeep because they were on the same provider Network so I was scanning for open SSH Port then it's connected and uh using the root and Alpine credentials and then uh that was it um then there will be
some other one in 2012 and 2014 but it it was mostly some had related stuff and uh not that much and it wasn't that much into the news but starting in 2014 the end of 2014 we have seen a lot more of them like UNF flowed wire loer um and then uh we had a big one named excode ghost that was in 2015 and that one made a lot of noise because it was also it was spreading through the modified version of excode so in the news you depending on which website you're you're reading from you would say that ex code was used to spread malware but in in fact it was a pared version of exod that
was used to spread this malware um and what I found is that most of the time it's quite hard to differentiate what was possible using a jailbroken or a standard device and that's why I made this presentation is to try to make it more clear between the two worlds and uh actually most of the stuff discovered since 2015 so UNF flowed we Locker uh they have been discovered or published at least by uh Palo Alto and one of their researcher CL G is doing something great is sharing all of the samples that they got to the community so as I'm not directly related by my job into looking into malware and I'm doing it at night this is quite
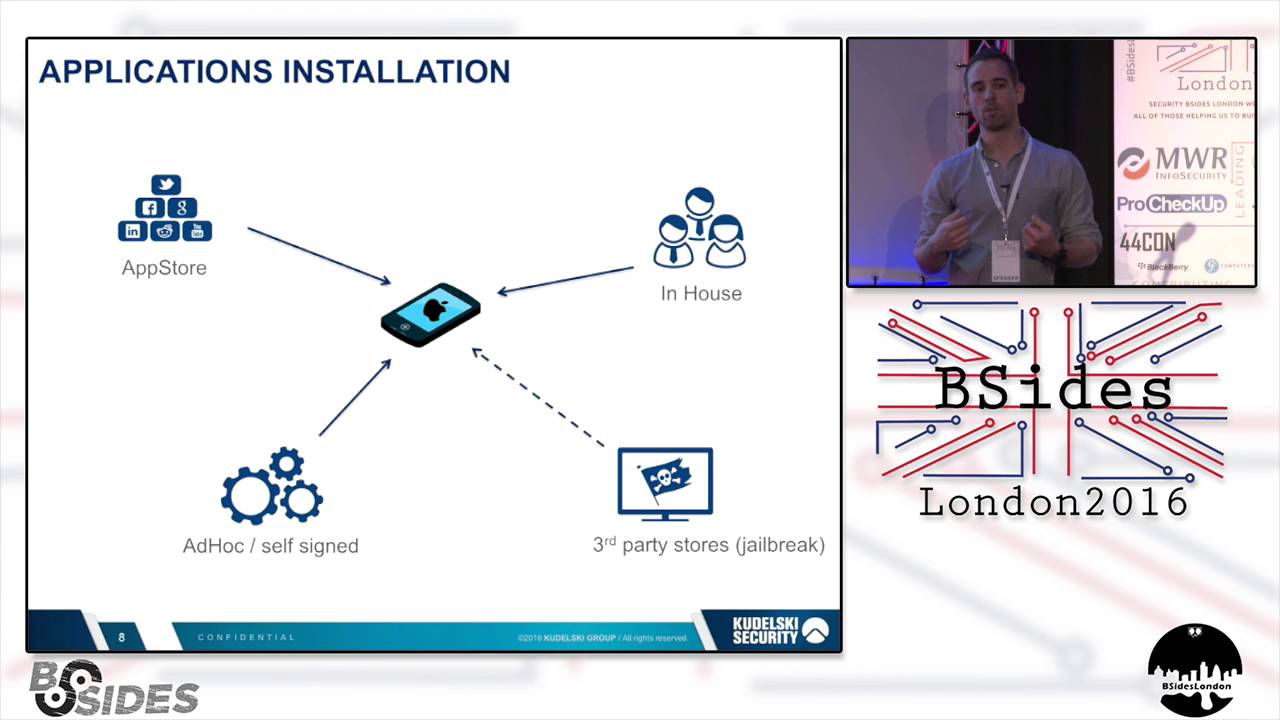
useful and uh it profit the the community to to share those uh those those um binaries so we can we can reverse them and learn from them so just a quick recap on iOS security uh the first thing that almost everyone uh is aware of is that the platform is quite clo compared to Android is not possible to sell sign your binary and push it into a device so no it's possible but it's really new uh it's something that you can do only from a few few months actually nearly nearly one year uh but most of the time you have those type of of access the first one is the App Store uh everybody knows about it you bu or
you get a free application from the App Store it's downloaded and then you have the binary um no it's not the full binary it's uh so there is a application so sinning and then you don't have all the the binary for all the architecture that has been downloaded onto your phone now then you have uh deployment which is called inhouse this is when you have Enterprise develop application so it's through the as a developer for an Enterprise you have to sign up for Enterprise veler account which is a little bit more costly you have to provide a specific uh number for the company register into the us so you can prove that you actually a company but
it's not the hardest part and then you sign it and the idea is that you by getting this uh certificate you will say that I will only deploy it within my company so usually it's not supposed to be deployed widespread so uh this is something that you might have known from your own if you have a MDM and you're using IOS as a Bas uh devices for your your own play then you might have some uh inhouse developed application signed by an Enterprise developer account then you have the jailbroken device which is a third party app store but then you have to jailbreak your device and uh actually it disables some of the protection from
the system and then it allows you to bring on unsigned code to the to the device then you have a a fourth uh type of uh deployment which is named adok adok is to do some debugging because as a developer if you only have your device it's uh not that much and you have even if iOS is less fragmented at Android you have various version of the Theos you have various version of the phone so you might want to check that for that it work for everyone and also get feedbacks as a developer so what you can do as an adoc is uh provide a a Mo most most 100 email address or uh so Apple ID and then you can deploy
those uh your application onto those at most 100 people uh device but there is a strong limitation and then you have the new case since uh last summer which is self sign so using excode 7 now what you can do is request a self signing certificate and then you need to assign to so to really pair your device not only pair like you can access is through iTunes but you have to say actually state that your device is no acting as a developer device and then you are able to uh develop and sign your own application you still have to to have a Mac to to do so and use itun so the jailbroken case is uh quite
specific because um it can be used in the security industry as an advantage I used to do uh pen testing and uh specially mobile application reverse engineering uh to check the security vulnerabilities and that everything is uh was uh was Secure either for the the customer for custom build solution or for commercial solution that they want to to use uh to access the security so it's quite useful because if you don't have a g broken phone you have uh a lot of limitation for example all the binaries coming from the app store they are encrypted using a light DRM but it's quite enough that if you get the binary signed you encrypted you canot decrypt it by by yourself
so if you have a j j broken phone uh it's quite easy uh the Packer is really simple you set a breakpoint once the the code has been decrypted uh then you run the binary the system will decrypt your uh your B your sign uh encrypted binary and then you dump all the code from the the memory it's quite quite easy and then you have the the clear text uh binary um that's why it's quite useful uh in the security industry but there is one drawback one major drawback is that it disables code signing uh validation so for some people it's a good point because then you are able to get some free stuff out of other app store you
can install tweak you can install uh parir copies of of some application which is bad um but also um there is a a problem because then you you remove one of the the core security principle that made the platform like um Windows r or iOS more secure compared to our laptops or desktop because we really have to bring on sign code that can be run and it's not something that you that is usually done on Windows or Os 10 boxes I don't know if many of you have deployed app Locker within their company but uh from my experience at least in in Switzerland and France uh there is not a lot of them so it's something that Whit listing
application is not something that people tend to do because there is a lot of uh work that you have to do in the background to enable new version of the application and do some some stuff so that's really one of the core principle of iOS or Windows a was doing the same and unfortunately it's been stopped uh but those are core principle so other than the code signing uh Apple is also putting other type of uh limitation when of them is a sunbox which is named seat belt uh the idea is then every code coming from the app store or any code running on the device has to be uh to going through a Sandbox
environment so it cannot do anything they want so Android does that by using a various um user and then he using um the the the basic uh user segmentation based on any Linux that if you don't have the rights for a specific folder on by another user you cannot access it that's how they do the the segmentation between all the application uh within iOS is different you have s belt and then you have like a firewall which is in place for the CIS call or some specific function call and if you don't have the correct uh privilege you cannot call this API you cannot call this CIS call uh it's as basic as that and that's how they do the
isolation for all the the application when you request an access you have to bring it like part of your manifest so you have to declare a specific file which is a entitlement and then you fill in all your entitlements for example if I want to access the calendar I have to add the specific entitlement saying the I want to access the calendar and then Apple will re will review those entitlement and there are some specific types that are disallowed into the App Store so this is a basic check if your application is in is requesting the entitlement to install another application because it does exist it will be rejected by the App Store and this is something quite easy for them to
to perform as a check because there is no obfuscation that you can do in this part because it's a XML so P pist file XML or binary XML file so is really no obfuscation that you can do at that time so it is something that you can do on top of that uh the send boox seat belt is supposed to um prevent you as I said to calling a API that you don't have access to but there are some limitation maybe you have seen in the news like two weeks ago I think steper uh one researcher on iOS he published an application for two bucks something uh in order to to check if your device was
jailbroken or not or if you had suspicious application running on your device uh what he did to to do that was to actually um take advantage of holes into the the soundbox to call some uh API that weren't supposed to be allowed like listing other processes is something that you not supposed to be able to do on iOS uh if you don't have the specific entitlement but still he find a flow that if you call a specific API you can you that is not well protected then you will you will uh you will get access to to to this information so if we look at malware basically it gets to one root code is people get
infected uh so most of the time for the iOS world uh or mobile world as as a whole it's to lure user into installing the the application the M application so what they what the attacker will do is send a link or a message uh with a download download link and then the user will click on the link and it will install the application um I use this in a fishing campaign for a customer when I was doing pentest and uh I develop a small application saying that in order to win a holiday paid by the company you have to enter your ad credentials into the application and then I had a 10% conversion rate of the people who
downloaded the application and enter the ad so Windows ad Windows domain uh credential into the application because I was I say that it was a game and if you didn't enter your credential we cannot check that you were part of the company so you cannot enter the game to to play it so 10% is not that much but still it shows that it proves that uh people are doing or installing this type of applications you would say that mostly on Windows what attacker are using is water Ringle attacks and they are exploiting vulnerabilities within the browser it's something that is also possible on iOS like on any OS since you have code you have paring code then you
have possible flows so it's not something to rule out but remote code execution on iOS are quite expensive in sense that at least publicly there are not a lot of them and uh if we looked okay it's maybe also a peer stunt but what zerum did is offer $1 million for a remote code execution on iOS so it's a bit of a peer to to get people uh talking about them but it clearly show that if there were so many remote code execution on iOS it's not something that uh that they will price so high high so there is quite um the the initial infection point for an attacker is not that easy if you don't
go through the social engineering part then once you run to the device there is not that much public but there is still a lot of vulnerability that allows you to evaluate uh to sorry to elevate your privilege on on the iOS using vulnerabilities within the kernel within the module that is loaded by the kernel or any privilege code otherwise if you don't want to to send a link what has also been done I've seen in a presentation uh at various conferences um at least it was in Asia what did was some um uh provider were attacked onto the DNS and the attacker rot the DNS traffic and then they they uh pushed their malware into the web page that
were supposed to be loaded so they injected the the link that way uh other wise what I've seen also what has been reported it was in China as well is uh moving with a fake in notb so in notb is for LTE so it's not possible to have a fake inot B in LTE but it's possible in um in 3G so in 3G if you have a fake radio interface uh there is no Mutual authentication between the device and the the the the radio interface so what you can do if if I'm emitting a signals stronger than the one provided by any mobile Telco uh then the phone will connect to me then I'm not able to do
the full connection uh to to the so I'm able to do the full connection to the Telco and what I can do as well is also push the binary onto the traffic so that's also one way that people got infected then you also have F physical attack um one feature is called mobile device framework it's a feature from IOS it's what allows you when you plug your uh iOS device onto your Mac PC Linux it's a framework so library that allows you to push application to push files onto the device it's a builtin but there are some unknown um stuff it allows you to install application and it allows you to do some process listing and to do
some stuff like installing application can be seen also as malicious because one idea would be as an attacker you compromise the host so the desktop and then once the desktop is compromised once an iOS device is plugged in you generate a piece of code that will push the the malware onto the iOS device that's one way to to install it but it's not working only as USB it's also working through Wi-Fi so once your iOS device is purred with your uh desktop or laptop once they're on the same Wi-Fi network and has been purred before then you are able as an attacker to push your code through the device and last customer also at black hat I guess it
was there was a vulnerability in airdrop um that allows you if you're within reach of the Bluetooth signal of an iOS device then uh someone can send you an iOS application that will be installed automatically once you reboot your phone because that was a flow within the airdrop and you didn't even have to accept the the incoming file then you have a third type which is code injection has been an article by a firey um I guess onto that for example there is a library for iOS that is called GS patch and uh from JavaScript you can call Objective C methods and uh what some developer are doing is to Hot Patch some application they're using GS
patch so they get from the web they download piece of code and then they out patch their application their binary so it is something that can be seen as quite useful because then you will uh you will be able to patch your binary but then if for example this is done in CeX so not in SSL and you do it from Starbuck then if an attacker intercept to traffic then it will be able to push his um JavaScript code within your application so this is an example with uh an application from uh it's a defensive application from zimperium and what they did was develop a small application from for Linux that will use actually this mobile device framework
and will uh activate the um installation proxy on the iOS device and we retrieve the list of all the installed application and then try to match the list of installed application against a blacklist of uh application bundle uh but then again if we look back you I just said that there is a code signing validation so even if I an attacker as an attacker I'm able to push code into a device then I still have the code signing problem to to bypass uh on jailbroken devices that quite easily because there is no codee signing done anymore but on a standard device uh that's still a problem uh so what I could do was sign my application as a
adoc developer but then I'm limited because I can only target 100 people and then I need their uh email account so iOS information uh there's been some some some information some attacks done using this and you also needed your UD ID uh but now access to the udid is blocked to application by Apple so it's not something that's been that's possible anymore really if you if attacker are doing a really narrow and targeted attack they might use this technique but it's not widespread at least uh at the moment another option is to use the Enterprise developer certificate because if you have an application that is signed with such a certificate then you are able to install onto any device
but even if you're not from this company but still there is some uh limitation so or validation put in place by Apple uh on at up to iOS 8 a user at once they download an application they had to validate that they want to install an application and then there was a second validation to be done the first time that you launch the application so this the first time that you run an application installed and signed with an Enterprise developer certificate it will ask you are you sure that you want to uh run this application signed by and then the name of the company so then it's it's up to the user but for those of you who are doing pent
test and social engineering tricks and stuff like that or doing um uh itl desk during the the holidays for the family you know that people get tricked and that's a fact uh now since iOS 9 it's more complicated uh Apple added a new Step so actually if you you installed an application signed with an Enterprise developer certificate and the certificate has not been imported through your MDM solution so your device is not controlled by a mobile device management solution which push pushed the developer certificate then you have to go to the settings search for the certificate and actually enable it so you have more steps to do and that's their way to try to reduce this problem
by making it uh needed more more step more steps so so people won't do it but still if you offer them a free ear day that's a problem so if we looked for the Cod sign at an application in this example I used a a sample which was part of the Y Spector attack which is named dapan if you looked at it using C sign which is an application installed on iOS on OS 10 sorry uh we seen that the authority is defined as iPhone distribution and then I have the name of the company so one hypothesis is that those company which are taking part of the attack are not willing what happens is apparently
that the attacker are hacking into those company stealing that their signing certificate and then they are signing their malware with the Enterprise certificate from this this company and then spreading uh to user so this is something to take care uh if you into information security for and End customer uh your uh signing certificate are part of your assets because if someone breaks into your uh one of your developer accounts and then he's able to download the signing certificate for The Old Company then he's able to develop a piece of code that is will be trusted on all your iOS devices for for the company or even further and then you have a media impact that you have to to
handle but then we say that there has been in the news a malware called a deceiver this one was said as a malware bypassing Apple code signing mechanism to say okay it's broken well not exactly what happens actually is that uh if you read into the original post made by paloalto researcher um what is made actually is that the application uh had to be at least once published into the app into one app store because there are several App Store that you you push your application into Switzerland UK France and then you are China and then you choose which app you want your application to be part of then what they did for example as an attacker say okay
I will only publish my application into the Switzerland uh app store and then I will only activate my malicious code when the IP address uh on the so I will make a call back to a web service and if the web service is not sending me back a token a specific token I will not activate the malicious code so what you will do is using G and say okay if the device IP is not within Switzerland I will not activate the malicious code if let's say I want only to to address to to attack people in Switzerland so what did the attacker was since all the the sandbox made by Apple are hosted into the US
what they did was okay if the IP address is coming from the US and since we know that we're targeting only this country so no we will not um send the token and the malicious code won't be executed and since Apple has too many application to review each day it's not possible to do to do that by end so either they do it automatically or they can use the code analysis stuff so it should be even easier for them today um because if as a developer you enable the Cod sing what you will do is not push the compiled binary but now from IOS 9 what you will do if you enable this cut sing is actually only
compile it to half half the binary which mean that for llvm you will only get the llvm interpr Intermediate Language and then the Intermediate Language is pushed to Apple and then what they do with Cod signing the idea is not to send you as a user all the binary for uh arm V7 arm v9 64 bits 32 bits that will only compile you the specific binary for your device and that's why they did so they take only the the interpretate repres intermediate representation and then compile the application for specific piece of code so for them it should be easier if you've seen the presentation before about static code analysis from llvm IR it should be easier to recreate
the EST and then from the this a so the the the the the c three c three of the application uh then to see if a malicious application is called or if something malicious happens but still there is many way to do to do obfuscation on iOS especially since the language Objective C is refle reflective uh then you can call application by using uh um the name and if you offis the name and you you get the token so the key to decate the the the name of the function only on specific case then you will uh you will not see see that and in the case of a deceiver what they did then was on top of that what
they did so their binary was pushed at least once by Apple but then once Apple revoked those applications so it was not anymore on any store but still one they the the attacker had one of their binary signed by uh by Apple so what they do they did was to use a a flow within uh the installation when you install an application from your PC or Mac using iTunes because you you in this case you are able to do a man in the middle attack and then you are able to bypass the check that once the application is installed it checked by Apple if the application is still valid or not so in this case they do theand in the middle
and uh what they do was uh uh make the iOS device believe that the application is still valid for apple and that's how they push it to you and the application is encrypted but when you installed it from iTunes you you get the encryption key is part of the bundle so they push you their key to to the bundle so that's one way to to to install it into malicious so to install a malicious application to to a device now if we looked into the the actions the first thing we can do is look at to the application deployed into the App Store really to see what is possible on the App Store and what is possible
outside of the App Store on jailbroken device or Enterprise sign application so in the case of app store for example let's say you want to do audio recording it's a classical case when you can scare really the sea level because if you say that in one of your meeting you are able to to catch what is said then for them it's a it's a big deal uh so you have an API on the for any application on on iOS and from this API what you can do is actually record the voice so from from the MC um application like Shazam are doing it but what what you will say uh see is that if you put
the application in the background is still able to record the audio but then the user will have a ribbon a blue or green ribbon that will uh be highlighted saying you that application is recording audio in background so it's not that stealth for for an attacker so this one on the App Store it's possible but not that stealy then you have the key loging key loging is also a big stuff especially since iOS 8 iOS 8 broke the con the concept of the extension so you can have extension for the browser like for example you have ad blocker that are using EXT as a extension and you also have keyboard uh keyboards like Swift and then at the beginning it was
say that an extension is separated from the standard application so there is no way for an extension to store file on disk and there is no way for an extension to communicate with the internet because there is a big fear because if you install the let's say swift keyboard and you don't trust Swift what do you do because they are providing the keyboard so there is one step that is put in place by Apple if you have something that is a password prompt it will actually be the the standard iOS keyboard that will be prompted it's not the one that you installed but the the the text input has to be marked as a password filled by a
developer but there is also a problem is that they say okay but it's too complicated let's say that the application would like to the extension would like to access the internet so is able to send what you type do some machine learning on it and then do some text prediction to get you more words uh easier and actually that's what swift key is doing or other extension like it so then if you go into the settings and allow full access for an extension then the extension is able to access the file system and access the internet so now everything that you type into this key keyboard can be sent to the outside world and actually that's one of the
trick that use hacking team in one of their tools for iOS that's how they they did it uh with a sign application then there is the pr private API okay this has been in the news last year uh more than 200 iOS application they are stealing information they are using the private API what is the private API so actually it's only stuff that has been forbidden by Apple in the developer contract they say you shouldn't C everything that is private so it's symbols that are not directly published or uh that are not documented um but still it should still be into the sandbox so all all of the calls to the private API should be blocked by the
soundbox by by default but as I said before there has been some flow into the soundbox and now hle needs to be getting around all those uh those flow [Music] um those uh to to get access to a specific um call as I said you need an entitlement uh like I explained before you need to Define um to said okay I request access to the calendar I request access to the address book there is a whole list that can be found on the new Os Os 10 book um the the guy WR writing this book made a a whole list and then you can see on a base system base iOS system which application is using which
entitlement uh this is validated by Apple and then unforced by seat belt so preate API does not mean that you can break out of the sendbox is not that simple still there has been some flow but it's not it's not that easy and there is also a problem is that for Apple to detect if you're using actually if you're actually using private API or not is not that easy because as explained if you said okay I will only call the private API if my device is located in UK but I'm a user in Switzerland then it it won't work your code won't be called so for apple is not that easy to to check and uh
there has been some flow into the mechanism like I said with a stefaner so eonic uh application that acted to list other application things like that uh in this case if we took one of the malware also from y Spector which is called No icon if you check and to the right that is asking there is a right to install browse uninstall and remove archive so this application is basically able to install other application so this requires the Apple prev private mobile installed allowed SPI um uh entitlement with the installed and so on uh is something if you try to put it into your application and push your application onto the App Store uh this is a big no for Apple this is
something that they can detect and they will block your application this is not not complicated for them but then there are other type of private API that don't need specific um uh entitlements if you want list of the private API you can use there is a GitHub made by Nicolas Sero on on Swiss fellow who made a full list of all the preate function or on a jailbroken device what you can do is use the class dump D yld and then dump all the classes on a jailbroken device and then you from that from that you can check for all the symbols uh within private stuff that are not published if you want to call Private
API it can be called either directly it can be done through D open dlim if you developed it in C and then otherwise use Objective C for example if it's called directly if you look into the import for a binary you will see it directly my code above and then if you're using reflection what you can do is I'm using actually the string and I'm building like in Java in Objective C you can use reflection and then you able to get a class from the name of the class and then get a pointer to a method owned by a class by using its name as well so in this case I've put all the the strings
in clear text but an attacker they can confiscate those string so simple ex or or R 1 or stuff like that in the case of a inous application it's different because entitlement won't be checked by Apple since it's not going to the App Store so if if as an attacker you're able to sign an application as Enterprise developer certificate then you put anything you want into your uh code into your entitlement and that's how they are able to made malware that are able to install other application into the the the device even if the device device is not gel broken and then it allows you more possibilities that's what was using by the wi Spector attack for example they
are able to access the MZ and MAA of the terminal and that's why they said that it the application are coded by uh getting private information about the user because if you know the MZ and MAA of a user you have uh it's pretty strong to identify someone uh you can also install application and access other preate information like the Mac address of the the device and if you get the MAC address then you can also infer some some stuff about the the guy now there is also another type of of malware which is non application based uh maybe if you're using iOS devices and you have mobile device management solution you're pushing profile configuration profile
onto your device most of the time is to configure the email access is to configure the VPN to to install corporate certificate onto the devices but as an attacker it can also be seen or used another way an attacker can use configuration profile to install a proxy and say to the iOS device from now on you go through this proxy and also it is able to install us a new ca so if you go even if your application is using SSL or TLS if the ca is installed and the application is not performing a strong validation of the the certificate uh then is able to even get access to your SSL TLS Communications and then also we can install something
as the certificate to deploy application later on so this is Al also been seen in the in the world now quickly the protection and detection so detection is not that easy as uh as on standard end points like uh Windows and Mac um because the the the system is there is less privilege uh so the privilege are more strictly enforced and you cannot develop something like on Windows most of the AV or Linux they are running using a kernel module but on iOS you can come to Apple and say okay I've developed a kernel module to do an antimalware solution they won't say okay but uh yeah we have the application white listing so we don't need that so
basically there is no way for uh someone at the moment to publish such a code so that means that the AV run at the same level as the malware so this is a bit of a trouble on the network side this is even more complicated because on standard devices you might say okay I will use uh my IDs my proxy logs my uh anything that you have on onto your uh network monitoring uh stuff on your network but the problem with mobile devices is that they're mobile so they might connect from the the conference they might connect from Starbuck so there is a lot of point that you might not cover so one idea will be to have an always own VPN
uh there are some provider doing that uh and then you rout all of your traffic to using the VPN through your IDs but your IDs is published so through the VPN this one way to do it but then you have a problem with the if it's a bring your own device it also mean that the user everything they do will go through this VPN but then you have also container like good or other type of container sosoft then they are doing specific flow only for um for the application they are setting the VPN only for applications so if you want the IDS like feature uh I've looked for example but it cames back to one year ago I looked
into what was presented into emerging threat type of IDs alert uh the rule set that they provide for surata and snort but from the they have some mobile malware type of rules but mostly they are only for Android so there are not a lot or any of them for iOS I may be wrong in that and there are other stuff like logout who is doing also uh Str intelligence into this area uh then what you will what you can also do from an IDs is to detect non-corporate configuration profile because if one of your device is accessing a configuration profile file into the internet and this profile has not been provided by you you should
block it at least if you control the agress point of the the mobile device what you can also do is to detect on the fly if an application is signed by an Enterprise developer certificate so any application download it to one of your device at at least same problem it needs to be protected by your network Monitoring Solutions if it's signed by another company you block it because most of the time there is no reason except specific case that one of your device should be running an application signed by by another company outside of jaob store so this is one way to to detect it then if you have a MDM or am solution what you
can do using the MDM is to get a list of installed application from the devices so then you get the list of the installed application you get the bundle name and then you match the bundle name Against The Blacklist of of names used by malware but this is not it's ioc on the chip because you don't have access to the hashes you don't have access to a lot of stuff you only have the bundle name so basically the application name like uh com. Facebook do something so it's not that that good it's quite is it it's something that you can quite easily change as an attacker um so that's one way to do it if you
running it if you want to check on your own device you can connect it or per it using a USB or Wi-Fi and then you can install the tools named the I device installer or I device provision and then from this tool on the command line you're able to list all the application installed into your uh iOS device so that's one way to do it from the I device provision command you should be able also as well to uh get access to the configuration profile installed installed on through a device uh but lately I've had some trouble to to do it I think it's no block by by Apple but I have to to check this I haven't got time
to to dig into that if you want to take it to the forensic point of view if you have access to the iOS device logs and you you get it through using a open source tools through uh uh the the the case that you can buy to to get the um to do some forensic analysis on mobile devices and then it's not something that we can see here but you have two stuff to look for it's install D and spr board there are two of the processes or services that are um that are making entry when you have a new application that is installed for example um springboard will say is the last one it
say that installed application did change so if you have this type of information that at least that allows you to know that okay the guy got infected at that time then if you have also access to a backup of those device uh you can infer stuff from so let's say side channels like for example the battery usage or the data usage because you have logs in form of U um um SQL uh SQL database onto the device and in those uh databases you have uh the battery usage the data usage and all of type of U statistics that are already um made by applications so if stly you you get access to a device that
you you think is compromised and you have a battery usage for a specific application that you don't know about this is some something fishy and that gives you hints to to to get uh and then it also give you the last executed information so that's from the forening point of view but then there is a problem with the acquisition because then if you want the binary it's something more difficult for example if you get something from the App Store it's encrypted so before uh up to so before iOS 9 if you made a backup of your iOS device using iTune you will get the binary uh for the application installed into the App Store but now
since there is the app sing and all type of stuff no apple is not providing the binary within the backup is not anymore there but even it's um App Store application so they are encrypted you cannot access the code so even if a malware was from the App Store you w you will not be able to to access his code and to analyze it except if you have a jailbroken device uh from to begin with but now there is a problem with Enterprise sign application because Enterprise application are not part of backups since the beginning it's stated into the documentation from Apple application that you have developed in house or distributed to your user with
Enterprise proving profile won't be backed up or transer transer to the user computer so there is a big problem because if you want to do some forensic and analyze what is going on if you don't have a jailbroken device that you infect and then you retrieve all the binary all the information but you have a a user that got infected then you have a a big problem to be able to extract the binary to to analyze it maybe what we can see in the future are uh scanning Kos using USB so when you're walking into the the like you have with USB key you have this type of this kiosk where you plug plug in your USB key that you got at
infos for example and then it will run multiple malware on it um AV sorry and they try to detect malware we might see the same stuff for iOS devices maybe in the future uh or maybe an AV for workstation that will say okay we have a new feature it now we scanning your iOS devices as well for Android is more complicated because then you have to have ADB enabled and enabled ADB onto a non-developer device is not something that is recommended now about the protection the first one is quite easy uh update your devices but then you will say okay we don't know if it's supported if it will crash my device and then you have the
hardening so what you can do as a end user on the arding side uh are the best practices so for example disabled airdrop is something that you can do using your MDM forcing a six-digit passcode at least and one of the most important stuff could be to actually do some user training and uh tell them that if you install an application that is signed by another company it shouldn't be installed into your your application you should stop the process and call the the it desk or the the corporate security team uh uh as soon as possible uh but then you putting the the work onto the
user okay as I said in the beginning uh this is made mostly I've been able to reverse engineer those binaries because I got access to them and since I'm not actually um uh performing active research on on this this malware looking for uh on we it for binaries and stuff like that uh it's mainly due to to this palal to guy that I got access to to them so that's
it