Let's Automate Some Security Tasks in Pipeline!

Show transcript [en]
yes ooh I practiced this from morning did I set it right yes yeah okay yes ooh this talk is about deaf cycles I chose this title let's automate some security tasks in pipelines because it's sound practical and their circuits is a new hype hype and concept and name that in past few months we've seen it a lot I have started this session about that maybe it six months ago eight months ago and there was like two three videos about that now there is a lot more my name is Abdul I'm in an R&D team at the ANA technologies at the security engineer basically this talk is my journey to adopting the obstacles in our environment Liyana technologies is a
cloud-based service for marketers in finland our headquarters in Oulu north of finland so it's very cold there yes basically this truck is a white hat touch we've been through we've been through Red Team Blue team purple team and this is a white hat the guy I even have a almost white hats here with me but I'm not gonna put it yeah I did a DevOps touch a few months ago and beside Ljubljana and I got this feedback after the touch back then I had much less experience about it because the F socket is when you say to a developer or security team personnel that the obstacles and they go defensive it's so way they say how we can have that they
bring up these problems they say basically we want to put security tests in our PI product pipeline when we we have a CI continuous integration consistent and after after all these things we have the product and then we will start the security test but when we put security tests in a pipeline and we have a lot of data and each run we have a lot of false positive and most of the people say ok our company haven't even adopted devops yet how we shall have def the cops we're gonna we're going to beat through these things and trying to address them so the agenda is I go through some basic concepts and the goal the challenges and
how we can achieve achieve with the obstacles and when we can say we succeeded in deaf circles in integration and some tools that we're working with well when I start working with on this slide at the same time I saw this tweet well the fire is zero and security with this manager sucide means network engineers everyone is trying to pretend that that fire in zero and well the only meme that came to my mind was this anyone any fan of automaton yeah yeah yeah they have a tool right now make sure be there yeah so how we managed to have the app cycles when our DevOps is not there yet and maybe you say we don't I was thinking the same but
after that because after that I realized that we never end we know if we never get to the point that say ok our DevOps is there and we're done with configure units they have cycles and divorcing always a healing adopting and a healing process it's always getting better so even we don't if we don't running DevOps we can have we can start shifting security to the left and we can start having it dev cycles and comfortable our Devils and that's worth together if if all these things sounds very variant we're gonna go to it make sense a little further so the ethical development sectors and operations she in May Department in a in a program akin a product in a software
programming company the F succumbs make them work together hand in hand well it's not that easy so what do we want right now security team makes a checklist and security says do this do that but that's not a good approach because in the end developers want to make a new future and release it and release faster the DevOps is making development agile but securities law that you teach and catch up so at this at some point you accept in some risk to releasing our products until it's time to pen test and then we do the security that doesn't work we need to actively promote talk to and developers and keep in mind our business requirements well
yet the f cycles is all about shifting to the left what does that mean it's secure product early and often shifting to the left make security these give security some visibility what does that mean it means developers they are all I have a developing background and I have a sysadmin background and I always been enthusiast security researcher so when you develop you don't know what's going on with the security security team and pen test and the generate 100 space of hundreds pairs of reports and they give it to you and you have no idea what's going on there and even and even you find you find some some bug that makes sense most probably you already patched them or they're
false positive but when you as a developer creating the bite if you manage to get the lock get get the problems and bugs right after you push it to the pipeline you can you can do better as I said I'm in the process of integrating devstack ups and as much as I do I realized that we have this security concept on every level of software production so it's the same thing but we we added the security to it what's obstacles obstacles our culture and infrastructure infrastructure of these tools that we need to configure that's the easy part if you ask me the culture is the hard part what does that mean the culture is the hard part because developers as I
said are writing code time and they they just need to produce software and release it and every time a security engineer walks in and say okay I'm security everyone's that goes away try not to touch hide themselves but if you walk in and say okay I'm a developer they start talking to you this culture needs to be changed what is the old way of of Austrian security we do a static code analysis every now and then well right now it happens to me a few weeks ago there was this tool pH based and I ran it against our project and there was like me use of errors and bugs and going through them is just a take deep application
test and after maybe a few months a year and having a yearly pen test isn't standard right now it doesn't works really it doesn't say should be accepting some risk you need to solve that well this is security anyone remember that scene from parentheses yeah but this is what happens to a sneaky trade that's the boy and the new way static code analysis and every commit developer push even pre-commit hook when with a little pyramid took a developer even after they push they can see the wipe the problem that can be automated security scanner each part online and gathering information and status and graph it these metrics are very important we're gonna go through them a bit later so yeah we automated
the stance but for assessing the results as I said is most important point I managed to put as much me as I could in this because it's afternoon type everyone tired so where to assert it seems very hard to start doing dev circles but it's not really hard because as I said it's like the most problematic part is a culture problem so we need to start talking to developers and make them realize that they making the bugs and they can be the best person that find it and fix it and we are there to helping them and we're in this mess together somehow it's not this separating security team and developer is it is kind of becoming the
old-fashioned thing right now yeah he's tough to think about treats and model and threat modeling is the thing that come together with the obstacles but maintenance solution for deaf checkups is completely different on each environment each component doing things differently for themselves and you can't have a solution and that can apply to every environment AFRICOM company you should think about the procedures and processes that happens each company and try to implement adopt their circles in that I categorize the tools in three category developer point of view operation point of view manager part of view all I said before was all of them working together so we separated them this is just point of view these
are the same tools on each category that they've worked with so the procedure going left right and up to down from far left of the security we have a static analysis pre-commit hook this is the far left it's not even in the pipeline we have any static analysis on the far right we have full-blown pen test that that pen test can be business logic that narrows down to one feature it's not like that related the football important test test everything right now that's very expensive so we covered most of the areas attack areas and and death cycles on the pipeline on the problem with treat modeling continuous security tests and pike counties so uptown we code with
deliveries in our pipeline and then we ask and test in our pipeline and then we have a feedback loop feedback loop that feedback loop helped us have an understanding of what's going on helps management developers and operation travel understanding what's going on in there so we assert with the developer point of view when you start developing even I do that sometimes right now even in your development test you have to take care of security we have a kinda environment orchestration tool we developed it our CTO develop it your kaha polenin that it's the l6 platform it's a tool to manage single project for a tightly coupled project with containers so you basically write a yam
file configuration and then you have all of your environments in there for development so we said in far right we need to take care of our develop developers what does that mean order the parts have the environments they they need to insert the application they are developing on it and they're local and they they need to test it so a standardization of that environment is important having a tool that they can insert bring up bring down the environment fast an automated is important so we can have all those tools that we need they have they work with with static analysis like a state agency and pre-hook all those can be configured in this tool so with l6 platform we can
have pre come to a second acid test case and a lot of things that the whole development environment so yeah simple is not easy it's just beautiful so now we're going to operation part of that part of the work now we're in a pipeline we need to set our scanners zap or burp whatever in our pipeline and extend our application when it's run in CI CD BDD security is one of those mutant from f-secure one one other one and both of them works with behavior driven development scenarios so you need to write your scenario your attack and it just test that part of the application for that kind of attach another another way you can do that is just is
just run the run the traveler and the whole is Chan against the part of the application you developed we haven't we developed another tool called the Skinner we're gonna go through that after this is slide and so you know this is our pipeline next slide is going we're going inside the CI CD in the center here after developer pushed and they have a pre-commit hook goes to version control we gather matrix a static and dynamic static and dynamic tests after that says CD server again we gather metrics and artifacts and artifice goes to artifice repo and issue tracker is feedback loop and we have a dashboard of metrics after that we have environment test a staging and
production environment each of those has its own metrics and tracking and test cases inside say CD basically developer pushes and we have test case it goes through selenium and web and then after deployment into a stage or production spinner or or project runs and after that it is change the deployed application and sends the report and then we have a feedback loop new ticket to our github or did lab this is a skinny is a python-based command-line tool well yeah this is a simple selenium configuration that we basically browse the application log in and then all of those lies into their basic the very basic configuration for that is a three SS unit test deploy and security test
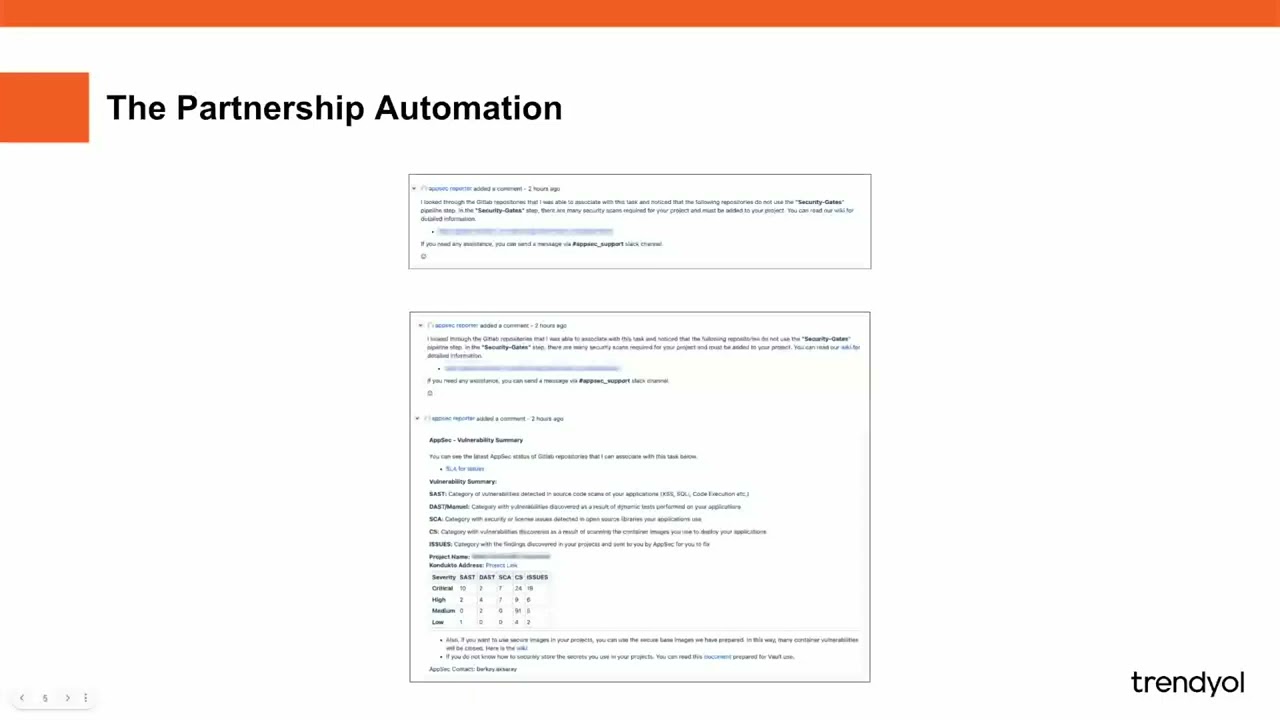
after still runs in our get lab we have the issues that we'll send to chat off any chat app and chat chat system do you have here is the matter most and then we have a new to chat with security issues for our developers so basically if your developer us up hating me because you pushed and then you have a new teacher automatically that shows well you have a problem and probably your team leader need to sign up is not going to deploy but in this environment that we deploy maybe hundreds times of in the day having this is very important so basically the s can process results and report it what happens to that report we
have a lot of Earth artifacts and a lot of metrics that's the important important point that's what makes business and go code true makes everyone make sense what's going on in our environment well health is LTS like an asteroid it has a lot of Kafka Hadoop spark nexus graph fauna you can basically grab your metrics it's an open source dashboard for graphing produce beautiful things like this nexus parameters to gather all the metrics from around our environment the lea after you automated your security test you think that you have less job to do but actually you still have a lot of things to do it's just different because the a black ops helps you actually
secure environments yeah sometimes with their circles we try to secure our pipeline from very beginning to variant that far left and far right but the problem is and there is a lot of false positive we need there is a lot of noise we need to reduce it you guys are security professionals if you read a lot of security reports what's the most security bugs we see in the reports anyone XSS it's a Celeste XSS while we still have each other's problems SS almost all the frameworks have every mechanism to to not have in each SL part but we are still having success problem because well it's Friday night the developer is that were tested that the developer working on a problem
for the whole week tired is 6 p.m. and everyone left at the company the Silverton his he's there he's figuring out the problem his friends messaging him that him or help that well yet we have a plan for tonight but that developer need to hash it and worked out and he knows the solution he the developer code it and push it and that in that situation we produced a bike under the pressure and if you say one afternoon like that with that company with a hundred developer in a year we produce a lot of waves we know how to pass it but but in that situation we are still produced a bike so finding the root cause of the problem is very
important why we have a lot of excessive problem or any other problem so if it if we give a dashboard like that that killeth on the dashboard and put it in a bigger screen in the company and show it show all the result that we produce from the other curves and show it to so they can see what's happening with the security that's that's man the visibility shows up visibility of security shows up what's going on and well it's don't put it on the main lobby because everyone gonna see who for this most part it's an internal thing but showing that to developers can help a lot with this with with this solution we empower developers with these metrics
empower developers to understand and management to deliver business make money - after all that's the whole point of security why we need to secure because if we don't secure it we lose money and the money is the whole point of the thing with with these metrics from DevOps and security we empower management and the locals to have a direct hand of direct hand in security and securing their product and maybe we have this we have this famous line after all securities by product of culture they have this famous line that hackers are always one step ahead of us as a security engineer well if we connect our security in a gateway like our firewall and web connect those lights those
metrics to to all match it in deaths occur from pipeline maybe when a attack comes we connected correlated with our allies in the pipeline and we send that new ticket it's in a nirvana deficit of sports send a new teacher to that the looper and they pass it maybe in that case we managed to become finally one as a part of hackers and yeah so that's it thank you any question [Applause]