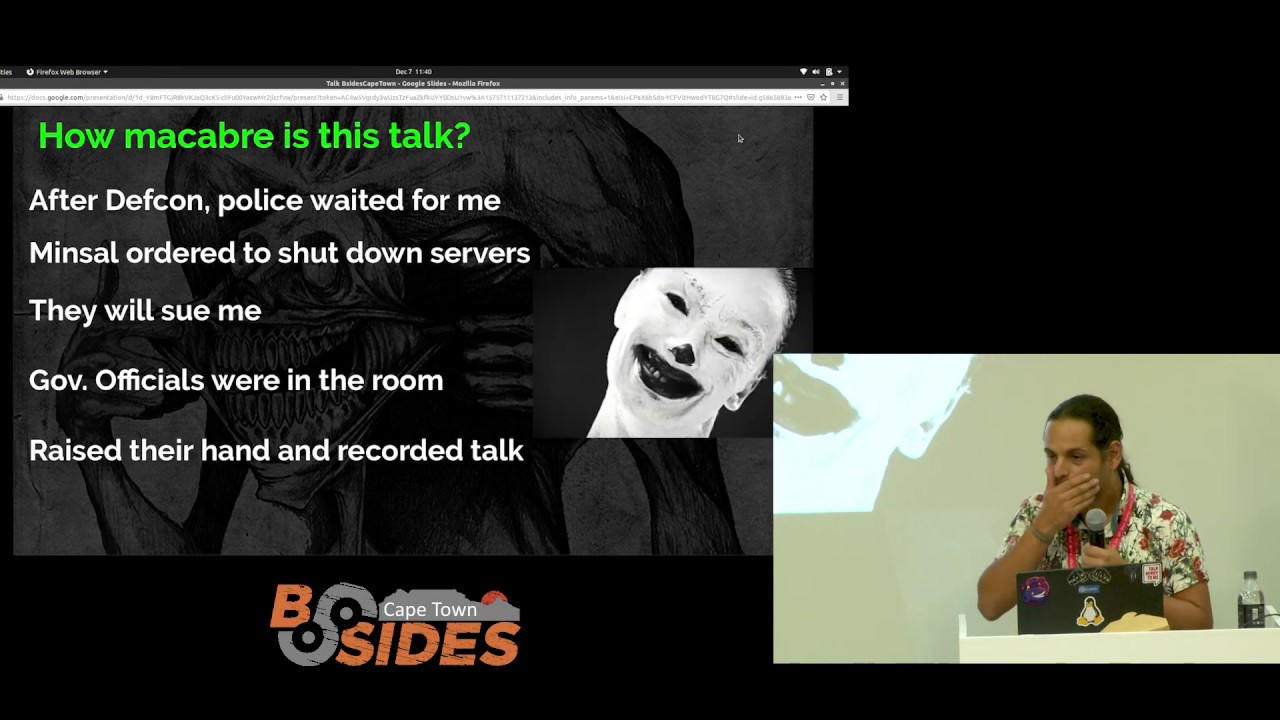
DFIR: Analyzing Voting Machines at DEF CON

Show transcript [en]
oh hi good morning well so everyone can hear me uh like she said I'm will Baggett I'm here to discuss uh the first time actually speaking live in a while so here we go first before we get too deep into this is anyone working digital forensics show hands one okay we'll keep it introductory level then we'll bag it uh used to work for the government I did human collection cyber collection uh director of digital forensics and advanced technology use for Operation Safe Escape we provide the domesticated domestic abuse victims a means to sever digital ties with their abusers sometimes it could be as simple as turning uh switch up on the iPhone where you're sharing your iMessages for my
being located or returning your Siri off on your iPhone or even and I don't need to start this beach I really like this topic I can go pretty deep into it but uh just showing how simple it is to turn things off so you're not stocked and hacked we do a lot of forensic work with that I'm a cyber threat intelligence manager at a very well-known place if I'd mentioned who I was I'd have to get corporate concurrence legal and all that and take several years so we're not going to mention it one bit of corporate advice is if you do work digital forensics it's necessary for your mental health to rotate out do something different because of what you
see whether it's fraud theft crime murder abuse terrorism it's not healthy to see that every day so right now I'm doing cyber threat intelligence there is an American sports coach and Nick Saban and he says he won't discuss politics because half of his fan base is going to disagree with him so he stays very neutral when it comes to discussing U.S voting laws elections and voting machines I'm taking the very same approach here because you need an impartial Observer down here I realize football is football not soccer as we call it back in the U.S we can all probably spend an hour two hours three hours day two days discussing how a blown call by
biased referee cost our team a spot in the playoffs whether it's NCAA football whether it's World Cup whether it's hockey we've all seen that so we've got to be accurate so in digital forensics when we're examining voting machines we also want to be impartial report what we see report what we don't see and the reason why we didn't know this we're working at Defcon and when they say voting Village it's not you know collection of houses and Roads you know they're not throwing flowers out there there's not chickens it's a freaking conference room in a hotel suite so you've got just a suite of random machines that have been purchased people come in they look at them
they start doing forensics they see them it is anyway the conference report as I start to examine this 2.5 billion people read the forensic write-up and Analysis of what we did after 2019. there was a lot of discussion but there wasn't discussion about we handled it improperly that's a bit of a point of pride and this hits home we thought that one juror resilient ticket for an incident of one possible intrusion by quackbot or a ransomware gang got 87 views on the corporate blog and the manager is happy 2.5 billion people read this and didn't find fault so that's not bad we need to have impartiality so enough of the legalese did I skip a step here
believe I did I just killed it there we go
more legally sorry so these voting machines we go through a process where Harry Hearst he's from Norway he's working with the US government also working for voting Integrity groups he'll buy the machines on secondary markets uh government auctions in the U.S you'll buy them from eBay there's one that he purchased for want to talk later on about the voting machine prototype from China which seems absolutely bizarre but there is a presidential candidate's family who want to help get more accurate voting results so they put their name on the voting machine Hari actually managed to get the device we've looked at that at Defcon that's what the bulk of this talk is about none of the devices are procured
illicitly if we did find something that was improper and want to go forth with it but it had been stolen misleaded however is legal term to Fruit of the poison tree we couldn't do anything with it now theoretically speaking magic right theoretically speaking say you find the voting machines in use at Defcon at the uh the loading dock and you decide to prove that your candidate was robbed of the election and you steal the voting machine in Vegas you know where you've got security cameras every few feet walking your step from the front door to the loading dock carrying this box out and then a few minutes later you show up on the news of oh I found proof
that this election was stolen there's all the facial recognitions you've not proven your case was fraudulent you've actually just committed a failing now you're going to jail the FBI is not interested in you for uh being the national hero you've just committed a pretty stupid crime not that that happened that didn't happen in 2022 in August didn't happen at all theoretically speaking so everything we've done is above board machines you can actually buy them on eBay if you want to but why would you want to touch on that in a second do these things are say old it's just we'll see so 2017 I left the government I'm doing independent Consulting I'm in Las Vegas
for digital recovery e-discovery case I have my full toolkit with me and it's uh blacklight digital forensics kit for iOS iPhone you can't do some windows I have magnet Axiom I have a probably about fifteen twenty thousand dollars of gear on me you don't leave it in your hotel room even here at the conference I've got my presentation laptop here because it's my freaking laptop I don't want to lose it same thing in Vegas where crime is rampant so I keep it with me I was walking past the room I saw okay here's these voting machines I've got my kit of course it's always the last day of the conference I walked up to Hari
and said I have this equipment not many other people at Vegas Defcon had it out of thirty thousand attendees he had a machine that hadn't been touched by other people which is key for the forensic process and I sit down and started examining it things got really familiar the machine he gave me it was about I want to say 128 Meg of a hard drive it had been put in service in 2000 2001 is running unpatched Windows XP the voting software itself was a 1997 Microsoft access database hard drive is unencrypted USB ports no security on those whatsoever so this is in 2017 this machine could drive it could be in high school be a senior
this is an old machine that's never been touched that's good and that's bad it's never been connected to the internet it's only been used for one purpose is that unsecure I don't know start looking and the first thing I did was go to the log so ah they tell me this machine's never connected to the internet but there's an FTP log you can see there WS underscore FTP log so I pull strings and I can see that the files have been sent them access database files have been transmitted to FTP infocom.com that's interesting for a machine that never connects to the internet where are these files going so like a bad episode of American reality TV I phoned a friend
uh one of my he's no longer there now but he worked at CNN as a researcher we looked up infocom or heated bandwidth there is terrible because they don't want you on your phones in Vegas they want you downstairs playing slot machines so they want you gambling they want you drinking and partying spending money not just sitting in your room scrolling on Tick Tock or whatever so cell service is terrible my friend sends me this back infocoms of company based out of Canada here's their IP address here's all about them but they don't mention they have anything to do with the voting system this is pretty interesting I get Hari the manager the leader of the
voting Village the room supervisor and this ends up going in the Congressional report on the conference ends up going in uh New York Post so there I am going just working with an entertainment company they didn't pay me I'm not bitter about that working for an entertainment company to being interviewed by the New York Post for digital forensics I wasn't expecting that so the next year we realized okay this got a lot of attention this could go badly if we don't do this right we actually put a process in I don't like process even though I've had a career in government I don't like process all that I'm more of not a government employee really so
we worked out a workflow terrible grammar I'm sorry we had examined the machines before the general public would come in they brought inscribes to document this from Georgetown law undergraduate students looking to work in government policy space we had very formal handling procedures on the machines I'll show you why in a minute now you've seen this part of it on the news the other part of what we did with the infocom log that wasn't on the news our process just like any other digital forensic process collection examination analysis and Reporting and from that we pivot back to see here's what we found what did we miss on the other machines uh Carson Schumer he's a name dropping
to give him recognition a university Professor from Copenhagen was here he found that on the raw base image of the wind vote machines there is an mp3 from China for the voting machines were manufactured he recovered the MP3 of that Chinese machine we didn't find it anywhere else in the other machines but one but we now had to Pivot to say okay this is an anomaly is it been replicated the machines were from dozens of states that wasn't just one machine out of one Precinct and we'll you know see this but um the principle the perpetrator will bring something into a crime scene and leave with something from It generally so there was and I feel
it's part of this but I feel ridiculous saying it there was a conspiracy going around that there was a satellite controlled by the Italians that had read write access to voting machines and that's how they were changing votes y'all there is no chip in a Windows XP from 2000. that has satellite comms with the Italians that's just not even freaking possible that but people get spun up and believe this so you would actually see where the software was installed you'd see the physical chip the conspiracy theories fall apart it's an old Windows machine so if someone comes in to upload software you're going to have the date time stamp of when the USB drive was
inserted you're going to have the virus or the virus the software malware spyware ransomware whatever you want to call it you're going to see where that's applied that's not there even on the Apple iOS I had every file on the fort Cree is numbered so you can see if you know file number here here this one's missing there's that well what's missing your software you can undelete files or you can find was this file missing first pillar of forensic processing you don't change the evidence to be blunt that the whole justice system falls apart if the law enforcement agency can change the evidence to make it read what they need to for their case also going back you don't
upload pictures of riftcastley and have uh the Rickroll video and claim that was only that's easy to show so people would do that if you have to examine this device you have to be competent either through experience through training whether it's through a Sans training course whether it's through vendor training course corporate training there has to be some modicum of training on this and you have to stay current before the pandemic we called it dead box forensics you would get a USB drive in the mail you would get a hard drive in the mail or you'd fly out I missed that you'd fly out to go image the device on site to see all the uh Hardware software issues
were and fly back to your lab to go look at the evidence now with modern software you can actually have endpoint whether it's crowdstrike or druva remotely access the machine pull the registry and look to see what's changed but you have to know what you're doing to be trained well with this otherwise it's just code there needs to be an audit trail of what so happened so when you image this device I validate the hash everything is copacetic you need to be able to say if you're on the prosecution team the defense should be able to replicate the evidence you have there to prove that yes this came down a good example going back to
Operation Safe Escape is whether it's Google takeout or whether it's Apple's data recovery for you have all your iMessages or all your Google data literally Google takeout keeps everything as much as I hate that from a Libertarian privacy point of view that's fantastic because it shows you know my client received these harassing text messages from this number that can be downloaded from Google that's an authoritative source as opposed to yeah here's a printout of a screenshot that can easily be photoshopped and manipulated that's a big thing on Twitter to have funny exchanges or reddit's anti-work or know your boss of all the things that never happened this never happened the most but pulling the chat logs down from
Apple Google and having opposition look at it or the work we're doing at the voting Village to see where everything matches up it's authentic that's the goal we need lastly the person in charge of the investigation whether it's Hari Hearst overlooking the entire voting Village or whether it was me running the forensic effort we have responsibility to make sure that okay this device we're going to image has just been returned by this group of attendees who are examining well that's not following proper handling procedures they can have it they can look at it what we need it for is no longer valid because we would arrive at Defcon early before the crowds enter the Boating
Village we would image the device I would damage it make a copy another person image it make a copy would validate the hash codes to make sure that these are accurate the hash codes y'all familiar with hash codes yes no maybe I don't know it's a digital signature of the file and it's fairly Impossible on higher level hashes to have identical it's like having identical grains of sand from the beach it's just not going to happen as long as these are identical the copy I'm working with you're working with and you're working with are all the same results should be similar we only work on copies of the backup so if we did find something that was truly
damning The Originals off to the side another backup is here work if you're not third and fourth versions of the copies just in case because you never know what you're going to find so the processing again this is vendor agnostic because as the military says two is one one is none I've had cases where I'd image the hard drive the phone with black light and then image it with Axiom and then paraben and then run a 79 tool just on Lark from the Apple store and find recovered text messages that the big programs can recover so unless you've given it a better picture you don't know what evidence you're missing if you're only using one
tool the better vendors will tell you validate our results with another tool large corporations would say we have one tool that's all we're paying for that's the one you don't want to work for because if you can't validate the accuracy of your work you don't need to sign that document legally to say I put my name my reputation online saying this is accurate if I can't validate it we would do three things we'd write to DMG file on a Mac if this was what I was teaching uh cyber issues to NATO's facial forces we would stop here we'd actually go through the steps on how to create a dng file in a Mac a virtual hard drive in
Windows of course copying the external media that I think that's probably going away now it seems like external media is Vanishing but we would do this that way we can copy the containers to the media and then have it shared easily whether you're in the war zone sharing the files or just sharing the Defcon it's a good standard practice everything is made in a read-only format we use these tools autopsy blacklight and magnet axing for data analysis we'd use black lights and acquisition ftk imager to acquire the files to image it in redripper to go through the registry to see the last files open what's been loaded that we didn't we're unaware of in disk drill was a fairly
inexpensive program it does file on deletions it's recovered better data than a lot of the five figure programs so here you can see we're actually using black light before they're purchased by celebrite and they went for 700 a year of a license to thirty thousand dollars it's not worth it I don't think y'all are watching but it's not worth it so we would copy it and this is why we had the hard standards and controls this is what you see on the news CNN Fox news CNBC BBC whatever oh wow they hacked no you didn't freaking hack it you copied Rick Astley from your thumb drive and put it on a machine that's not hacking it's Ctrl C
that's control V that's more thread into I shouldn't say that either that's why we have standards and controls after we damage it this is what disc drill looks like it shows all the deleted files we look and see if there's anything unique in there one of the common things now from nist.gov is they have salt files you can go through they've collected all the common files for the operating systems the hash values so you can remove the known good files and only look at the anomalies and this is also why we have to do it properly this is the end result that they didn't look at how the sausages being made they didn't look at the
forensic evidence they didn't look at the proper handling we see there's all the Glorious computer science we were doing they went for the meme which okay whatever a friend sent me a screenshot that we actually made the last Defcon before covid hit we actually ended up there this is why we have hard rules going through this a little bit you can see we actually have to crack the hard drive apart these are not machines I mentioned earlier theoretically that if you're going to take one and walk through a casino you're not smuggling this in your backpack that's a huge machine also Imaging takes a while so I think two iced coffees and a Mountain Dew
Express with extra caffeine to try stay awake through the process this looks like it came out of the set of Mandalorian or 1977 Star Wars on a sandcrawler buddies this is still in Houston Iowa by the way it has a 10 horsepower motor to pull the paper why you need that much horsepower to pull sheets of paper for not making experiment I don't know but that's what they've got you have a waterproof port for dhcd programming why I don't know the entire hard drive is written in a the operating system is written a variant of a Blackberry operating system all clear text so again once you actually found the adapter to go zip disk to something you
could actually read wasn't too bad but finding these esoteric Parts you feel like you're going back in time most of them rely on compact flash cards the one boat machines you've heard about a lot on the news the data is written here so this is it this is what people say has been hacked it's a flash card when's the last time are maybe all still using compact flash cards no and Beyond compact flash cards they were just flash cards which are different if you put a compact flash card in a flashcard reader you're going to destroy the reader Source trust me there used to be a large electronic store in Vegas fries before Amazon killed it we'd have a shuttle going from
Defcon to fries to pick up the parts we need for these ancient machines so this is another windows XP NT system running on a compact flash card that we would image put in your school sticker on a laptop on a voting machine is also not hacking by the way it's vandalism especially for a South Carolina sticker things that we found after we imaged the machine username and password because of Sunshine Law in the United States those were available online the admin name and password for the machines those are available online this is compliance with state law don't think I agree with that one so the altered files after we image that device with a little
honey bear and the big cry and the Defcon logo still ran again hard to break the old habit of being an instructor if we had laptops in front of you I'd say pick a state pick a country find the voting machine used in the state look at the username password for the machine is that hacking or is that just o sounds so this bad boy the premier voting machine after we image it we turned it on we actually want to see what we're working with the two Google searches we found the username password the security name and password
I'm not notable of memorizing hash value for every single file and machine that I wouldn't be here I wouldn't be in Vegas I'd be on Wall Street actually I'd probably own the island that would be something phenomenal be able to memorize things like that and track trends the premier voting machine prints 56 pages of hash values for every you can't download it it prints how you're going to validate there's no virus there's no malware so we ran experiments we got the Scribe over from Georgetown we validated what we were going to do okay we copied the logon user ID the file change it to my friend's avatar from his website it loads you get a warning that something has
changed so there is a hash validation of the file there is some camper detection we were surprised to see that this is what made CNN this is what made Fox News it's not that hard work okay
the Chinese voting machine this came up because of code I don't know if y'all have heard but there's a virus from 2021 to like the end of time that stopped a lot of things so the first true voting machine Village we had was in 2022 last year after the pause the voting machine itself we'll talk about this seven thousand dollars it's 150 pounds you think about the poll workers who set up the voting machines they're usually elderly retired maneuvering a 150 pound Behemoth for one machine is tough doing that to set up an entire room good luck with that so this is the Prototype that a political family is endorsing we actually found the specs online
we're concerned about data security and people hacking into it so this one has a camera so they can watch you as you print for facial recognition it scans your driver's license your ID card to make sure it's truly you a fingerprint reader has Bluetooth 4G and Wi-Fi and speakers why I don't I'm not voting to listen to music I'm not listening to Jimmy Buffett and Island band I just want to freaking vote and go home I believe the phrases insecure possibly so you actually have the machine here from their website it is the idea of having facial recognition fingerprint capture and your ID captured when you vote does that make anyone feel warm and fuzzy does that
seem and have Bluetooth and cell service connection to it so as much as I don't like having a Windows XP box that I might be voting on it's still a little bit better than knowing this device is on I don't know who's accessing it while voting is occurring foreign so where do you get the device manual from for this
to the chat Channel Through Alibaba the manufacturer no your Precinct voted this machine they would send you a PDF ready to get your software updates direct custom patches and updates for you there's no open source validation from the community there's no examination it's just here's a file just for you no one else can look at it from China one of our adversaries this doesn't seem like a positive step I don't know I've only been doing cyber security for a few years so we actually got the device we had to discuss with the unions we had to get several people a hand truck this is the device as it arrives in the voting machine Village you can
see this thing is not small 150 pounds it arrived we got it cleared because we're not allowed to actually move the material because of rules and regulations we get it and that night we have to leave the room again rules and regulations Fire Marshal code so we had to leave it so we wanted to do something called trapping anyone familiar with that term it's not a it's like a Honeypot token I took video of this can't pause it
can you play the video please thank you
we took note of all the unique locations where things come together on the video where tape for the metal tape comes together I took note of it we didn't advertise it we didn't discuss it we noted for the hinges were that way if the machine had been opened overnight and broke the seal literally the seal the chain of custody we would know the machine had been altered overnight during a before we could come back into the room we use a high speed load drag tool to open the box and then we get this thing first thing we did because it is Defcon we don't have 100 chain of custody 100 control of our environment we removed the power cord we want to
make sure this machine is accurate it's a seven thousand dollar machine it's a beast came from China China so remove the power cord cover that with a sticker so someone couldn't just plug it in to see what it does thereby and doubting the results
most of the machine actually sits on a repository for the paper ballots are printed and stored so if you've ever submitted a corporate expense receipt report and the thermal printer you know how great those are after about a week they're blank they're white right you can't read them you can't use them you have to go back to the vendor get another one to try to get reimbursed that's why all the votes were printed on is thermal paper we open the box up [Music] and I'm sorry okay I should play this again there are two printer rolls that the printer rules run out of paper The Machine's completely offline
and of course someone wants to help by unplugging everything before we can document it that that's not helping that's making it worse that's making it much worse so you can see this is not a standard machine this isn't your traditional computer that you're getting we saw that okay this could be a problem we're also the group of us were experienced in I don't want to say mature I don't like that word but experienced enough to know there's examining and tinkering we went further we would tinker one person had fantastic idea he took a photo of the unknown circuit board ran it through Google image searches Yandex and tenai to see if there's any other circuit board like we found
identical ones as an Android board and we checked there were no visible anomalies on the board it looked like this should be what the circuit board should be there's nothing special there in the same conference hall there's the internet of things where they do drones the different sensors the Alexa's all that good stuff I walked over and said we have this we don't have the equipment to image it can you help of course they love the chance they did a chip off extraction mean they put leads on the circuit board cloned the device it was slow took overnight we actually had to hide the machine keep it from being touched while this Imaging occurred overnight 128 101
123.8 gigabyte file it doesn't seem like that big until you're sending to someone that's massive again going back to instructor mode I brought my right blocker toolkit with me in the yellow Pelican case and I realized the entire case relied on the USB 30 type A to type B cable without that one specific cable everything else out there didn't work and when TSA was inspecting my luggage that cable got crushed they were able to rehabilitate the internet of things but Point here maybe not so much for voting machines about forensics in general if you have limited access to a targeted device plan for the worst assume it's going to fail the sooner you're going to
need to use your backup so again I would say your tax dollars from out of the country your tax dollars taught me this your primary image alternate image so if the one image 123.8 file fails we have a backup not only do I have a backup I gave a copy to Hari a copy to someone else to mind playing hate to say it went down I wasn't single threaded I didn't have the only copy two other people on two different planes had it just in case because we didn't know what we were working with the media is unreliable the higher the case sensitivity the more high level attention you have the greater the chance it's going to die
and of course my mandatory Star Wars quote would you like to know the odds of failure they're high very high so we finally get the image we don't know what we have first thing I do is connect it through a write blocker after I've cloned my four images of it and I use grep and Linux to see okay what version and we see what flavor of Linux is running now I can pivot from that into my tool I can go to nist.gov download the Android files that are known and good and then remove those from my forensic processing
this is a dope scope I feel weird saying that again out of the country has nothing to do with dope it's just a cool little name wardollar.com it's a defense contractor in Virginia it's a Kali Linux monocle so you can look to see the Wi-Fi addresses the Bluetooth networks so when you're doing an on-site inspection of whether you're doing Red Team whether you're doing sensitive site exploitation drug rate whatever you can look to see all the different networks oh there's actually an uh Apple backup server stored in the storage bin we can see it's emanating here through this Mac ID that's not being picked up anywhere else Nick Gadget didn't need it bought it anyway but we use this to see is this
activate the Wi-Fi on the voting machine is what network is this creating same for the Bluetooth so the bottom line we didn't find the dozens of the machines we investigated over five years no foreign interference no domestic interference bad foreign design the Chinese sewing machine I wouldn't trust for anything the way it's designed right now we haven't found malware there's no security updates there's no internet connectivity and it's such a diverse mesh of devices that you wouldn't have a single point of failure like when uh Facebook's their Border guard files were corrupted they lost their DNS entry and Facebook went offline about a year ago they thought it would tie to Russia Kremlin or Russia Ukraine I believe
there's no failure because there's such a mismatch of machines even if one voting Precinct was corrupted it wouldn't affect the entire nation that's a good thing I definitely didn't care for there's no encryption of output all the the voting machine files are written to vote.txt on a removable USB drive I have heartache with that everyone votes on the admin account I also have a problem with that the USB drives are accessible you can see where every time I mouse and a keyboard have been connected or monitor you can see just the logs however in the voting machine area you've got a poll Watcher you're on site you don't have time to pull USB drive out load it reboot the machine load your
malware and get off the X before people have noticed that you've done something malicious it's just not I don't want to say it's technically possible but it's not humanly possible because the chances of being caught doing a level of Espionage like that are very high that'll be a nation state incident a lot of blowback the probability is very small the greater threat is the non-encryption of output so no offense if I give you the USB drive from the voting Precinct you don't like how they look you stop on the side of the road you have on the just have your laptop use 51 votes for candidate a 49 for B well we're going to change that
100 for a zero for B there's no stop get measure to add that corruption so get a little bit ahead of myself if you have just something as simple as a lock bag from a bank they're 11 from Amazon put the loading drives in there the USB drives lock it give the key to a deputy party a is a vaccine the sheriff's car party B's in the back seat you have three sets of eyes watching the locked envelope it's technically encrypted I mean it's not accessed so you know you've got a good output from the voting Precinct to the headquarters so they tally the votes together that would actually be far better in a very low cost win for a lot of
local governments again no firewall no anti-virus programs no audit Trail we didn't find any voter information on this that was a good find but again these machines were so old we don't see any tampering with them because writing exploit for a Windows XP a Windows 98 machine good luck with that another thing if you have a software that was the hammer and sickle or something like that they claimed is on the voting machines that can remotely include selections if you have something like that you're not going to have that on 100 machines in a classroom at a church where you pull them out once every two years because somebody could find the evidence that there's something corrupt on there
and again that software if it's removed you're going to find it's been removed through forensic programs so that's also not realistic so the short version we haven't found evidence of voting machine tampering we also don't touch the voting rules we don't touch the validation of the ID we don't touch that process we don't touch what happens after we only look at the machine itself they're old but it's working they probably they're probably vulnerable to every cve from 2000 to today but if they're not connected to the internet and they're only used for voting doesn't matter so this actually flew by any questions yes
could you repeat that on a microphone please
um I just had a Curiosities about the FTP logs that were identified okay from earlier in the presentation could you just elaborate kind of on the context of that in the background a little bit more it was a log file that looking at a new machine or new machine for the village that had been Untouched by anyone they said the machines had never been connected to the internet ever ever's a big word so when looking at the uh Logs with time crunch we saw that the machine had been connected at some point to the internet maybe when it was being image not image maybe when it was being uh cloned for creation but we did see that it had
been connected and sent files to the FTP server in Canada why we don't know but we'd seen that replicate on it's again so we pivoted from that okay we have this WS FTP log on this machine we start looking and see that on multiples of the same wind vote machine so we think it was just the setup however it was still violates the all if the manufacturer said it was connected to the internet being set up being imaged being cloned okay yeah that happens when you're creating that many drives at once that's an understandable thing and never connected ever since okay but it was that use of the term legal term ever that's what raise the Reds
like for us absolutely thank you
all right
you guys aren't a very talkative Bunch so I'm just gonna fill in for you so um I've seen how complex our government's procurement process is here rightfully so um it's a small community and you know lots of inbuilt mechanisms to make sure that the right Protocols are followed and things so how do you know how decisions are made in local state county um federal government as to how these machines are obtained and I'd say this from in 2008 I helped with my dad's election campaign in Montana um so I got to see a lot of that side of it um and the machines that were used then were kind of like what we used to
take the Iowa Basics like a fill-in circle kind of thing yeah so I'm sure that there's like lots of trade-offs being made about like efficiency and accuracy and um you know overvotes and all these things that figure into it is there protocol is there is it just like the city council saying we're gonna get this one or it comes down to budget once you have the main vendor you stick with them another piece thank you for reminding me is the vendors charge per software update per machine so it becomes cost prohibitive for them to if even if they want to load the latest service patch that cost escalates to where the local government can't afford it I'm not
saying nationalize it but there's a definite issue there budget it's always budget
thank you um actually I was interested into digital forensics just kind of getting into it I was wondering if you had any suggestions on the tools standards or just general education that I could pursue I'm not paid by them it's a free course um Charles Stewart s-t-u-r-t University out of Australia has free online Master's certifications so you can take a digital forensic Master cert in that it's we still recording okay your connection's broken don't listen at home it's four tests open book tests but it's good material so it's for 90 minute classes uh it's a good way to get your foot in the door to say now it gets a overview of what it is
good software program would be for Imaging would be go to Magnet or magnets they keep they making cutesy names but magnet forensic.com has a good Imaging tool as well as ftk's Imaging tool and then it's cluji but autopsy is a freeware open source Community tool that's a good entry level point for digital it's what we taught over at NATO because you know some countries can shouldn't because how I feel about pricing but some countries don't want to spend thirty thousand dollars per license per Examiner other countries do have the funds so we settled on autopsy it's a free one you can build it to make it what you want but it wouldn't hold up in a court of law
because it's so customizable however to understand how things work okay if you understand the basics then you can understand the push button forensics of loading the device get your output and just scroll through for whatever PDF so bottom line of Charles Stewart SD York University that'll get you a master's search it's a very easy serve and then I'll open the door to you need the two pieces of the acquisition tool and they need autopsy tool thank you very much
another thing to look at not to monologue here with look at druva druva it's more of what we used at some of the corporate engagements where you connect to the endpoint it can actually pull down the key files so if somebody was manipulating that the team would ever do it during the pandemic but manipulate a receipt for visiting a doctor's office and providing eighty dollars of pastries as an office visit to 800 in embezzling money that's something you can find quickly through instead of Imaging the entire hard drive from the user's computer not that anybody would ever commit stupid fraud like that working for a pharmaceutical company during the pandemic but don't deal with stupid stuff
thank you [Applause]