T1 05 Temet Nosce - Thomas V. Fischer

Show transcript [en]
five years one of the things that I used to do is a distance responsive so due to the response and they also some of the other things like they're listed up there Atlantic keep things about actually run be snide London so if you've ever been to this island it's like thank you for coming there's a long way to come basically what I'm is struggling today is it's about the ankle I've always been a big proponent at the end points as a solution do defense and to do instant response but also to actually be able to I say get more information we've had a tendency oh now in the past we've had a tendency to focus on the exterior right number of
years probably will remember this you know that was the defense in depth model we kind of dropped the defense in depth block people started losing faith in in the end point technology that we were actually deploying so this circle became big on the outside we started in on camera protecting the perimeter and we lost track of the inside and the problem is is that if you think about the attackers think the outside is just the wall just something to bite that's what they're interested in is the inside it's what's at the core your information systems it's the critical assets vigilant you used the users people are using anything that's just basically sitting on Amish my machine
whoever is you know the sober or whether it's laptop welcome to desktop and you know my paradigm is this right so do you guys all know imagine online remember the Maginot Line okay imagine the line the French knocks on French so I can basically say you know French and an interesting idea but as usual no I never finished it so basically by the time they actually got to it they built it it was outdated technology Germans just run over but this isn't the first example if you think about it the first example of a wall to keep that is to complete gogh so do you guys know what this one is so that's Haven walk it was the Romans
built that between Scotland and England and the funny thing is most people think well it's defensive wall it wasn't it was a state as simple and that's what for me a lot of our criminal defense technologies of the Catholic institutions so I thought however I put all this next-gen I with technology some way in front of my career far as the primitive doesn't exist and the funny thing is with Hadrian's Wall is there when you think about it when they built it they build a state of simple I didn't keep the Scots how all right the Scots still came into the into it into the Roman Empire they had the adverse effect the Scots came in
they really pillaged inside the inside England but they couldn't go back because you know in those days the ledger guy pulls big carriages full of stuff you can't get over the wall without going for the game so instead of actually letting stop if you come again they let people completely goober they've stopped them from going out and certain extent we're not doing that today in information security when it would offer a min technology but we have that same thing as people are getting in and they're sitting and residing in the end point I was hiding internal this is my favorite one of my favorite things is was lost their effectiveness in 1545 if you think about 15-45 is from Marco Polo
actually in gunpowder to Europe so are we in the wrong place so we remind lot today on what they call next generation network technology we've got sent lots keep up this the end point solutions are seeing in the market today they're built for the instant response type suspected they were filled it up after the incident right the bill about training your forensics image training is Grant's getting your forensics information and we look at how suspicious loss we look at acting you know we look things are active in resolution to decide what's going on and we kind of look at what's changed but we're actually got looking at what happened right so when we're trying to get to understand how our
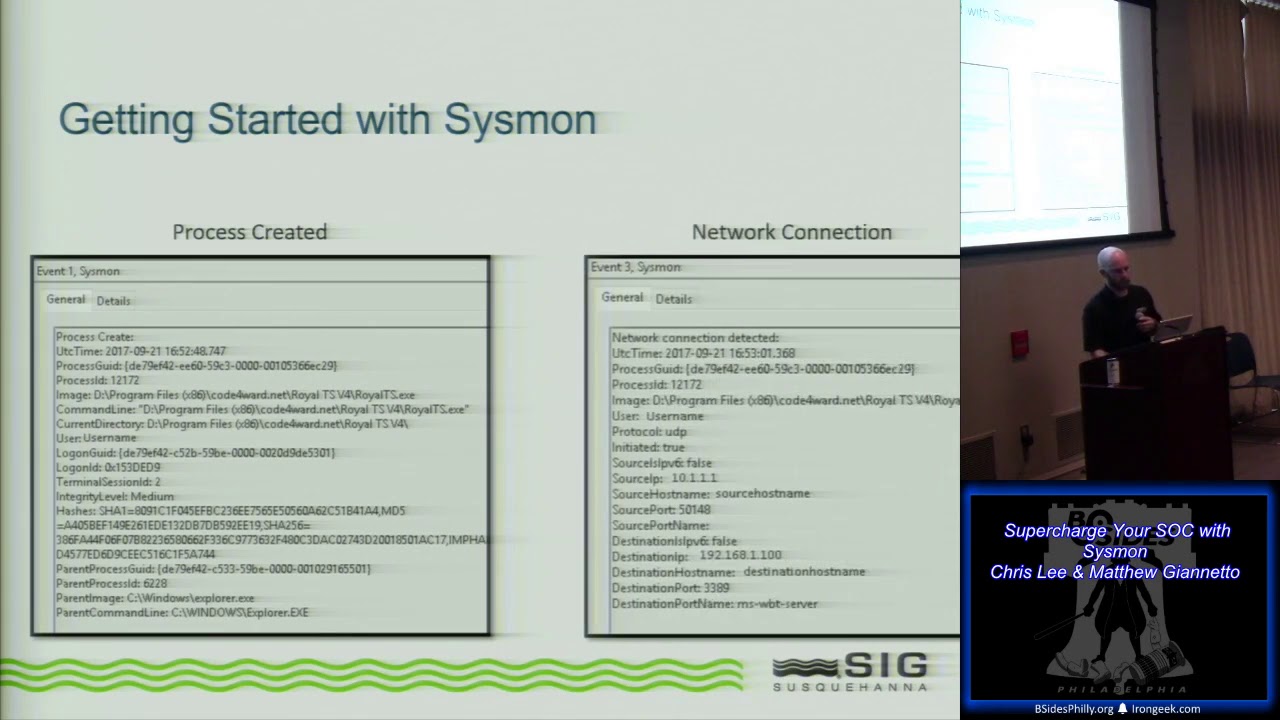
environment is compromised but basically looking at that snapshot in time and we're going to go back and feel the timing and say okay this happened was this happened I think this happened is happened and I think this is how they got in and this is the best shower or slow so the endpoint is actually can actually provide the world of information right so if you have if you've ever done any basic research on the endpoint get it doesn't show sitting on an airplane this is windows example you've got tools and even windows world after all focus on windows well for this but basically to go to sysinternals just really much for this is TCP you so you
can see every active cross very active network connection that's going on including we were very low before us the last IP address in as you can get send and receive both the states and information then you've got process explorer projects laura is really nice too process explorer unlike the task manager latching and the locking details button up the process is doing and were held in the hierarchy of processes so this is a snapshot there's actually a snapshot of dried eggs being run of Mize itself up and you can start drilling down so you can start to see information you can see things like command lines where it's widely from what the user is that can be
important you have any user you can get things like what kind of threat to running up to your else if you learning and inside inside the process so all the information but this is my favorite room so this is pokémon pokémon is very nice and this is one of the problems with when you're looking at endpoint and looking at the technicals going on in your time at endpoint they start to generate organoids so this is just a snapshot Explorer and everything but explorer is doing when you basically opening windows in explorer so i can see it's like creating farm an exploding an image its clothing sparks reading the side it's creating a registry it carries
on and i create a network if you actually do look boomer shares are connected to a network share doing all this but the interesting thing is it's giving you a lot of information is giving you like the time the process appears you can actually drill down into that education about the processes involved the operation you've got path rather successful or not it's more details of quiet since that's what was going on so all this is information that when you apply to actually looking for incidents or actually looking for a power she's been compromised if we have this kind of information that should be able to see the real time line how how for example if itself is worth about how they drive
by adam wells run dry by earth so with this information we start to build an application female so when i start to do the best together and we can track number of events and say well if i see multiple file writes and reads in the sequence i can basically see say but the user or the application is editing this file so you can create a file edit event or if I see things like far being renamed from one directory to another I can say well this is a far move operation so you start to give more context to the investor happy so well well I'd like is to have ever listened to on a single place efficient
intelligent endpoint agent that's what we're starting to see come on rocket what the insert we're seeing is so there's a number of companies including or where we're deploying saucy applying for some agents at the end points that are collecting all the state reporting a pact that promised we start to get a high-level disability so you certainly can start to get all the file operations or the network operations of HBO process data some cement point agents you just raise alerts and give you a map with the event happening the sequence and open that sandbox which saw was going on but overall what you're interested in is the information that you can prob not every solution not everything with the scene
happens can be laid back to something that's none yes it's the other amount you want to look for so this is very smaller after show you want details some of these later but you can basically start pull out this information so you could detect when I'm gonna run an empire has been compromised so for example page can start to see things like this is actually W strip and dog is good internet now in I think 1997 every normal environment there's absolutely no reason w spirit go out onto the internet there's no reason why Mugabe scoop communicate to the internet so when you're looking for attacks or compromises this is key in detail and this is something that you are see
official employ two issues so if you can raise this event and actually you know report back if you look into your sock you can actually start to build things more interesting same thing here so we start stairs excelled in the network operation to an IP address and is something called members w shake copy you and then if you look at the URLs are some funny number in their 20 numbers and divide Pfc again I would Excel you can download exciting like that and start to get that information if you stop for that information for this time you start to see Beverly which has to be uncompromising from what and where can swivel mechanism this gets too fragmented power I think
frat party is going to be a new key we're here everybody's talking about it the reality is is that you're basically like this guy signal player in my language and magnifying for something that's interesting but you feel like this and this is what is happening it's a painful long arduous task you're sittin and sifting through times of Leo and you get really bored with us so in practice fet hunting is an analyst versus an adversary it's essentially intelligence but Jesus has somebody who understands things knows what is looking for and understands how the adversary of things however so attacks it's about being paid an adaptive because you might think we're you know things but these
guys probably know more or they found ways of doing things you never before but so need to be created you to actually think like they think sort so so you need to change your ways quickly you're not looking for indicators and that's the key thing is if you look at what i would think what we've been doing over the past few years in this domain inside the terms of neutral response we're always being talked about indicators but i'm going to show you some data where you can talk about indicators all day you would have missed a piece of ransomware because they're all the indicators point into groups and green lights deep analysis potential compromise resources when you think you
see something you have to go into you have to go into and analyze everything that's available for that incident so you're talking about looking at every father I talked about looking at Kevin proximo talk about looking at every event one from the machine we're talking about looking at anything suspicious us on the shoes are connected to and I'm not connected to them I've been connected to that machine and the important part is as an analyst you have so it's about understanding defining normal okay what is normal in the environment what is standard approach what whatever moment network what a normal traffic network traffic what's the normal time and user connects to his machine which users connecting machine
do you allow multiple users to connect one with shape these are types of things are going to look for but the podium 170 is 90 is ninety percent information that's what we're doing today that's what if you think about instant response you've got information and you need to find something in that information so these are some of the things that you might have we have firewalls you're looking for unusual IP addresses countries businesses proximos unusual traffic you know white white you have thought 22 traffic coming out your environment quite see me put a white out how many of you look for this in your fireworks or in your Posse lot on a network connection if you have equal
bite since butter it's a very unusual traffic pan because that means of sending and receiving the same amount of information dynamic dns the emptiness is a favorite thing of tigers ended how many of you know how many tired dear sir dynamic DNS addresses or domain names there are there itself is like + 4500 right now different dns subgroup unique user space so you can be looking for things like you know you know deputy to America things like that anything that's just not supposed to be in a packet windows locks so local attempts see how many video test the log on mini happen when he gives it was added to never finish that's my favorite one is looking for
net user commands because first thing but once again I cook my toast as an adversary first thing you do is going to add an egg and local user and put him in the alley what we had the case where we started to see manipulation of the financial settlements very interesting so it's like a sieve an operation for financial statements and we start to see the use of any cats okay somebody's trying to happen potentials what we eventually found out is that in fact it was an internal person i was actually group into our people that we're trying to get managers accounts because they were they were logging into the mansion machines and deploying block deploying
hacking kit to basically monitor the microphone and one so they can stupid are meeting in secret leaders are asking our thoughts that's always interesting you get over anti-vice reporter then you've got the new generation of alcohol detection solutions right detection response those are all reporting indicators they might forensics labs the micro memory dumps but the key thing is basically everything this goes into a tip it's the only way to do and then you can sit there and hold everything together but if you don't have a sin you're not going to go big clock if you've ever played us in actually got for me on Twitter that's two weeks I've been going down qy puree are not hell I'm trying to do some
reporting on some of this stuff and curate off to build something to write way off is not an endpoint same solution okay they do not understand the endpoint and they have absolutely no fuel standpoint so we're trying to port data for regenerating to cure it q radar and it's a 90 their system and so this is half my day out so I'm doing service wats I sit there and like back go out and that again it's like one much what is this all this junk and I mean it's sifting through gotten lots of data right so there has to be a better way to do this that's my conclusion I mean we're pulling all of this information
and you add in more important information but there has to be a better way to do it this is where I get back to my file events and and some of the stuff i was talking about earlier of understanding how applications work his engines start to build behavioral analysis so we can start to build logic you know you do if a plus B then C or D or E but not XYZ can declare certain patterns so this basically if i were to choke convert this into something more beautiful so if you use up into email WTF inside that you know it launches acrobat and then next step is if i see demand for money what if i see the 11 or / acrobat i have
almost certainly a Malaysian state then if I start to see manipulation with other types and regulations like touching on data adding that use any users to the admin accounts then I definitely have an endpoint that's risky or a network is compromised so I'm going to drill down a little bit into that so here we so basically how do we behave built into so when you open a file in outlook it actually creates a temporary far so it's like a life step part of to a new location gets him dead then write it up then copies it and it opens up if you want to the process to open the file so one of the things that
we start to think about this one let's catch this fun right so what we know this file has been saved from an email it's important because the user why you should save the email file attachment and open it later so you need to be able to track that far time so we see a processor opening the tab file we can raise this as an event attachment open so we know that the user is in the state waives open an attachment that's come off an email from there we see office opening the microsoft system so there's a number of holes of a maid number of DLLs will be loaded so if we track that we know that we've got an active
attachment open then took the poor compromise your authenticity of far-right or the scorning of a network connection or even the spawning of kamancheh with an echo or bathtub but usually I'd say ninety percent of the times have you seen this it's always either network operation first and then I went far or just directly away far so depending on the type of attackers in the attachment they've either got that winery they've got to stop binary inside the file so that right out binary or the connector and networking download one we then see that far moved into local happy why do they do that because they know that any system even lock down the blood DVD allowed to run stuff in so we're in
state of risk we got suspicious activity going on so then that binary Iver execute on a farm and execute or it's running the dementia lately I think it's most it's been mostly commercials and scripts have been running so we've got an elevated risk from that point if we have any target Adrian they can start to track everything that's going on and generate more devil why is this important this remember when I was talking to you about fret hunting there's a lot of data if we start to add all the end point data that we can generate it's going to be masters and a today so we want to keep the data to a minimum until we're going to stay when
it becomes important we also want to get all say well I'm at the state let's notify the operators let's notify the analyst let's treat them off so if I had with this data back into my saw a sinless day like I saw I can start to build dashboards up trigger alarms and say we think this endpoint has been compromised oh so now this won't be too small so i don't i'm actually i'm knocked it down to two because well if you want for instance inks on this i can show you is one really interesting one but with if well one of our customers has a lot of chinese contractors and they allow to deploy a tool from 10 said that does
dynamic translation or it's like a dictionary to a new keyboard to say fine then you see it learning into the office it lowers think 56 dll's one executable and then you see seaward stop communicating up to IP addresses in china which is really interesting so i'll call origin digital guardian is dead loss prevention so when you see that did i'm thinking okay I'm sitting here there's a guy going out to this all these work processes basically can you came back and forth between your bosses and China the server in China and this lecture we discussed it nobody else towards to like it's a dictionary and a keyboard so basically what you're telling me is but every time that
Chinese user nice about what the English Way is for report but he's writing he's basically typing that word for typing that phrase into this tool or highlighting it in half its and it's being sent to China you can imagine what the next response force I thought this one I will show you to droid x so the alert so we things will be picked up try that one show you this one and i'll show you ransom at the ransomware was actually really interesting so there's one of our customers and they sent me an email you're an interesting person so this is driving so hopefully you can see so down here so this is where basically we you know when
i talked about how look when you up an attachment this is where we've actually generated a copy event and we see the name of the attachment we have more information as well our past and things like that then we see Excel making copy of it so basically what happens is outlook does that copy in one location than itself but since it's on temporary one and this dll load is when we start to see the macro subsystem thing pull that okay so then this is the fun part we see Excel doing network connections to the IP address in the internet for 81 for any because most firewalls and proxies left for any go through you don't know 86 L this is the URL this is
the domain name remember the server up here at subjects the initial connection yes so here's the actual URL because he does the initial connection to open the connection TCP connection when he's actually downloading the file once you've downloaded file you write this you see here is running it it's actually running it in the tip and they local that data so we've got multiple right events now if the agents are told you enough it can disappear differentiate between the binary and an off binary file then it gets renamed and gets kicked off by itself so here we would have parent information we could pull out Charles and provides whatever you need then we see this basically going
out this one is with interesting because actually doing 6p connections to spot me up 844 hey no surprise up to actually go through on some boxes the vendor realized why is just because some people just allow anything over a fast on the foxes and files know a lot of websites do that big E's way of course
so this is a ransomware attack from from April so it's a lot more detail this is the purpose sort of thing it's like what I say is that you can get as much detail as you want if you're doing the right listening on the end point so here basically this ransomware worse a zip file with a JavaScript attachment so here we see the original one I don't have the actual opening of the safe harbor this is where it starts with the W script so here we see the command line so simple command line is the users are cooked in farm is it but we have a path so we know what the original Star Wars
we don't have to go trying to figure it out and our forensics we have that fun and if you notice the file name it ends so the actual phishing attack was actually quite cleverly done it was a notice to appear in court we will receive a notice to appear in court facing do is you open because you know you could be good report so it says notice to appear it's about serial number as fjs most users don't have the file extension visible and their Explorer so when the help in this AC doc oh my security guys for me I'm allowed to open docx files it's okay do we have protection on doc doc files so then this
script actually starts to read some stuff then does a connection out on the internet so we start to capture IP addresses again and actually downloads so here we have complicated so it's a really long URL basically this ransom is hiding an ad server and they managed to compromise over and a whole bunch of for registration information so then we see basically loading some dll's to occur when it then flash first word so this one is this first hook into the system basically and I ran this each time it was a different version same name but the m5 changed every time it's essentially just download anything so does one of those when it does another level connection and he launched the
second down
and the second downloader is actually the one that's going to start doing delicious stuff let me see it watching a CMD now if you're smart and the range is good you can capture the actual command so here I actually see that he's adding a registry entry if the runs and he's calling it cryptid and he's got a text file so basically that's where he's going to have when reboot I'm going to get a message so then he adds some doc cryptid and use it to them into the class classes so where his extension for m.tech that's recognizes in far time and the pocket by the by the elkins notepad so when he's gone you have some
information about decrypting cook did there's the registry so I'm actually tracking a lot detail some sort command lines and electricity renting ready activating solar nails all right he's gone out too so here's the interesting thing goes out and downloads esta leap from live system tools com how many of you how many of you think that that would be flagged one anyways far away anyone's next-gen network of us that's debris it's green you know silence you know they consider have all this financial technology has no effect send it to Barstow it's green it says to leave is Microsoft then he starts is bachelor and this one was really beautiful he has a batch file but basically does a full command
recursively on every tribe learn imaginable from B to Z and he's looking for typical office file types well you know business card types and then a puppy does that follow and forever any pipes it into a fine strength to actually get rid of anything but see on influence system and stuff like that so he's compiling a list of files that he wants to encrypt event calls another application is downloaded a zero dot exe and I'll show you a command my flat in the middle so then he starts to do
ok this is a move
teach me to use Excel
so that's a nine just agree to do man like it's basically going a night when say x cubed and then a negative five original yeah so this is McMahon mind is using ok so you copied it to a danger so it's a zero by FC next problem is a then minus MX zero third- and engage then minus P whole five straight name file picked it and then five does anybody know that Mara is when I saw is John straight it's a really simple tools dark I do it's seven sit there basically repackage 70 put in a few modifications to trick the NT five and is archiving interning Floyd encrypted the archiving process through but mine is P guess what good
way how did you password so that's the kind of things that you can do if you have intelligent endpoint feeding your day or so that's it