How to Fake Friends and Find People: A Build A Buddy Case Study
Show original YouTube description
Show transcript [en]
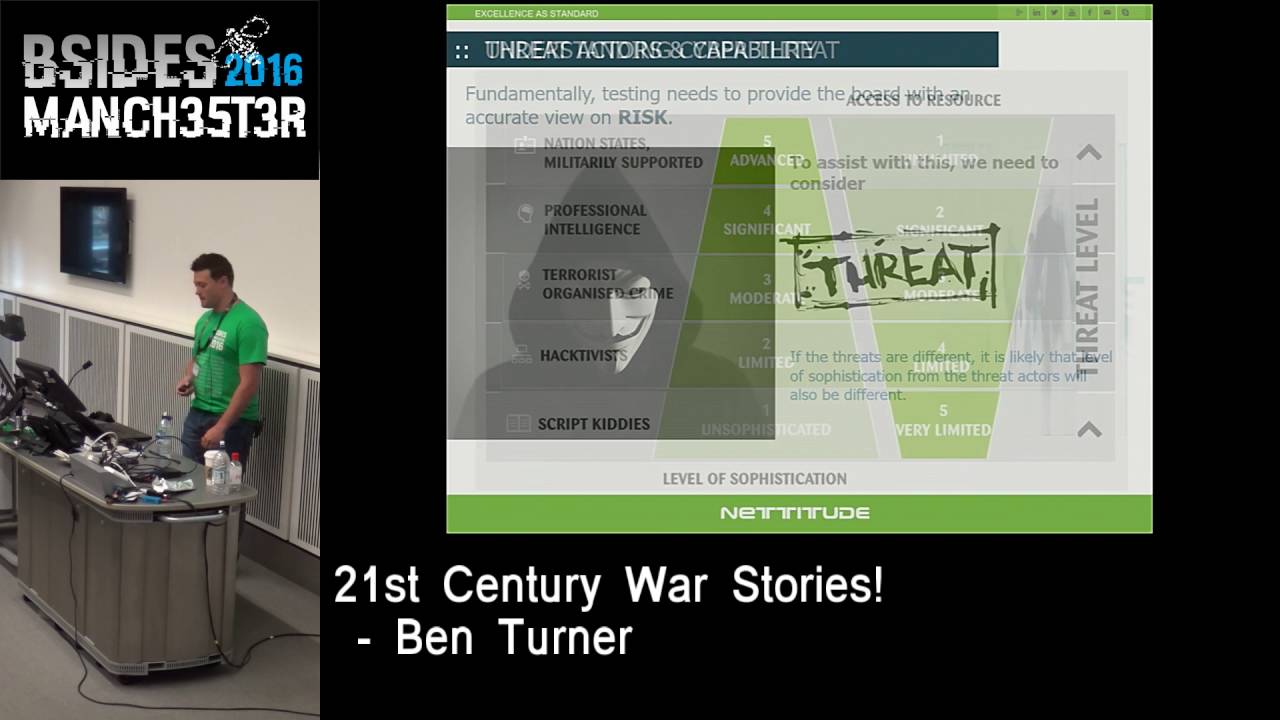
we're going to close out besides pittsburgh with an awesome talk by a couple of people that are going to tap dance and sing like yeah yeah we're going to make it really difficult for the camera how to fake friends and fine people this is gonna be awesome take it away you got you got hands-free i got a double awesome yeah extra hands all right so thanks everybody um this is gonna be how to fake friends and find people to build a buddy case study clearly click click click all right so this guy's me it's a little bit older picture before i decided to move and stop cutting my hair um i work for a company called attack
research i'm a security consultant at pentester um oh it's mike we're getting some echoes um both of you and i are prior special operations forces though that's spelled wrong it should have a t on the end uh veterans my contact info is up there i do not have twitter because i don't want to um i also have some coins and conference swag stuff to give away if you're interested yep and then i'm david schloss i also go by gabe um i'm the offensive security lead at echelon cyber risk i am a researcher red teamer professional idiot whatever you want to call me we have a lot of fun yeah she gets it i do have twitter all i do is post memes
and then my linkedin is nothing but uh red team tips and tricks so hit it away all right so our our goal today right um what we want to kind of talk about is uh we want you guys to start working in crowdsource humanitarian efforts uh 2020 saw this huge boom of people using the internet go figure right they're all bored at home uh they stopped going on to facebook to hit oh yeah you know that really sucks this country's having a lot of problems let me go ahead and hit like and send my prayers that way uh so they started helping out in humanitarian crowdsource efforts uh in this talk the scope is more
directed towards those who are under direct threat of harm and those who are being like that's through like human trafficking wrongly persecuted individuals if you're contacting those individuals through efforts led like digital dunkirk was that's what this is going to be talking about we also have this really really cool thing at the bottom it's a cowboy hat back in our unit when we were still in the military there was a phrase it was called don't cowboy it up basically what that means is i don't think this is the wild wild west if you start going crazy and doing things wrong people can get hurt and whenever you do see that cowboy hat if you start messing up that region of
the talk this is where people could potentially die uh so that's kind of how drastic this talk gets into hit it cool i've got your obligatory cat meme because i promised you that i would so we're going to talk we're going to go over what are we talking about what is a sock puppet um why you use one when and where to use them and then the differences and some consequences between good and bad implementations and what happens when you don't do it right vice when you do yeah so uh what's a sock puppet other than you know something that five-year-olds make in their kindergarten class uh a sock puppet basically is a fake online persona that is used to help mask
your true identity um from your true identity wait did i say that right or i say true identity twice didn't i anyways it's a fake persona that you put online it's normally associated with the baddies you know things like russian misinformation actors uh apts uh three-fourths of tinder for all those who are equally on that application uh maybe also like half of linkedin i'm sure you all have the uh the people who just message you about jobs that don't exist ultimately stock puppets are are a way that can be used in a offensive security mindset so when we do things like social engineering campaigns or red teams we don't actually use our true names right i'm not going over to a
client and going hey my name's david schloss let me inside your building it's more of like hey i'm steve rogers i'm here to rescue you guys let me in things like that uh so why does it matter probably right why do you care uh why would you want to use a humanita a sock puppet during a humanitarian operation i'm gonna hold on with both hands here because i think this is really important for you guys to know the baddies have the internet right uh this isn't the days when the taliban don't know how to log into google this isn't the days when boko haram is like oh man i don't i don't know what facebook is like the
baddies have the internet and literally everything about you there are companies out there that know more about you than three letter agencies and that's that's the truth uh which is kind of scary but for the uh for the really really cheap price of 0.99 you can learn about anything so if you want to be you know there's a there's a little cowboy hat there for a reason uh because this is where people start turning into stalker mode right like when you start learning you're like oh man i know where you live i know where your cousin lives like you can literally find out everything about a person uh we've done that on multiple occasions where we have
to go and find a relative an advantage of an individual who is in country and that individuals here in the united states are their relatives here in the united states we could find out everything about that person get their their their daughter's name phone number their husband whoever it may be contact them because we've lost contact with those individuals so it's really important to use a sock puppet and this is why you know the the baddies do have it word so this is kind of the big bottom line picture is that these fake personas when you use them correctly can keep you safe super short version of what's nice and long on the screen they keep you
from being found by the people you're not trying to be found by as you're communicating past and through their network capabilities that was me all right so where do i start how do i do this um step one sorry step negative one before you do anything are you ready for this are you in a head space that you can tolerate getting involved in this kind of an operation um i didn't do step negative one last time we got involved in this and it was a bad decision because i found myself talking to people that were in a lot of danger and i was under a lot of stress anyway i didn't go well think about whether or not you can
tolerate this kind of activity or not mentally right that's all your mental capability headspace so then it's cash record how are you going to fund this we're going to go through acquiring temporary service building a fake persona building your presence for that persona step four obviously question marks and then step five not actually profit it's a go live and and run your operation start your communications
are you sure okay then you start off with low tech all right we promised we practiced these slides i swear yeah like at least once all right so a question you also have to ask yourself is how sophisticated is the hostile entity um are we trying to avoid people like the taliban before the fall of kabul where they don't own the telecom suites they don't have access to all of the network stack are we trying to avoid people like the anti-balaka militia or the farc who are relatively low technology capabilities within their user space or are trying to avoid advanced nation state adversaries yeah so we like to kind of point out the difference because this is something
that a lot of new people tend to not understand right they think okay there's some big humanitarian crisis wrongly persecuted individuals to say like in china right and then they're like i want to help those people via online methods well like obviously china's really really good at hacking i'm pretty sure i don't have to tell you guys that right so they're going to be able to run the telecom services they're going to be able to track down who you are as an individual even if you are starting to use vpns like we're both we come from a apt-ish background right um we understand that it is very easy to still backtrack ways through um i i also put up here the cartels right
we all know how danger danger the cartels are you don't want to mess with their money stream they they'll probably behead you it's kind of terrifying right but they have people everywhere uh that's that's something to be aware of when you start messing around with uh let's say human trafficking you start getting into the revenue stream of criminal organizations that are closer to home you have to start worrying about all right is this going to be a problem for me um and depending on who they are the retaliation could be higher the cartel is more likely going to not care if they go and try to whack you china and russia probably aren't going to try to murder
you unless you're in like the uk you know somewhere that's closer to them uh but for this talk like that's out of scope we're not going to talk about anything about getting into the more advanced adversarial nation states seriously be careful with this if you do ever get invited to participate in some sort of humanitarian operation that does include something that would be found up here including the taliban after they've taken kabul then maybe back out especially if you haven't done this before which is why there's a big big cowboy hat here because that is a high danger yeah this is this one's scary so then you gotta you know really get down to down to the dirty let's start
like actually building our fake online persona let's build our sock puppet you got to think about the first question what do you want to go cash a card i think they asked us at defcon 2 which is really where they take card anymore but cash is king for most of the part you have to weigh the pros and cons uh the pros here really cool it's hard to trace right uh people aren't really putting down like tracking numbers on your on your cards or on your cash uh it's really cool when you have a lot of it you feel like you're you know tony montana uh and leftover cash can be spent in singles i'm not you know
saying anything but if you want to go downstairs you can spend them over in the slot machines and whatnot the cons is is not everyone's going to accept this uh and there's a there's a cowboy hat here because i've seen this happen before uh when you go to buy your equipment be that like a a visa gift card or your cell phone service via cash places like target and well actually i only can speak on target because i've seen it there but uh they won't accept cash for this kind of transaction they want a card they want some way of being able to track it it's not technically illegal to do this but it is
it's a gray area people don't like you to do it uh but i've seen some guys like try to like fight the cash register because they're like trying to uphold their own policy and i'm pretty sure we've all seen that here in 2020 as people just go insane or 2021. um i don't remember what year it is it's all learned together at this point but you know just be aware of that and we're not endorsing anything on the screen these are just services that you could use everybody has their own preferences but you can get your temporary cards through things like do not pay or privacy.com these are cards that aren't associated to a name
so you can put any sort of name to pay for your service and then obviously this visa gift cards you can buy via your card as well which is a little weird but that only enables for more financial tracking if you were going against a more nation state cool so now you've got your cash you've got your card you've made your decision how you're going to fund this first thing we're going to do is we're going to get ourselves a phone number so you do not want to use your own personal number we'll talk about why in a little while it's not a good decision uh you got physical phones you have virtual devices physical phones are
obviously easier to do especially for like lower tech kind of capabilities people go get a track phone or an atm t prepaid or i don't care i don't i'm not paid by any of these guys i don't care go get whatever find some way to get a cell phone um alternately if you've got virtual devices me i'm lazy i'm a nerd i sat in my chair i virtualized stuff i'm not going to walmart i'm not doing it bluestacks is a tool that we used it lets you virtualize an android system and then burner app was the application that we used you can pay them like what seven bucks and they get you a phone number
that works for like two weeks so now i have a phone number and we're ready to move okay so now now you have your your cash or card you have your cell phone service next thing is building your believable persona right all these photos up here aren't real people that's a disclaimer you know you can give a name to anybody but basically you use one of these two links what we would recommend right this person does not exist it's actually really cool if you go ahead and hit refresh a few times you can see some very terrifying images of like people with tentacles out of their eyes it's really creepy but other times you get
really cool things like uh you know iranian seth rogen here in the middle um it's my favorite one yeah you know like so you get all these like really cool generated images and if you use the one that generated photos uh or generated dot photos they uh they give a little watermark on the bottom so if you're good at uh powershell or powershell photoshop thank you sorry i give too many talks on powershell um then you know you can you can take the watermark out and and put it up on your facebook your twitter whatever it may be and then the second piece to this whole story is you have to build a believable story of that individual right something
that hasn't really been mentioned yet is kind of creating this like age of the person uh if you go out and just build yourself a sock puppet like five minutes later you're using that sock puppet in the wild people are gonna know it's probably a sock puppet right so you can build this nice little backstory and it gives you the ability to remember the name especially if you're communicating with people who are under duress in country where you're helping so like you you know you go to fakenamegenerator.com and it's like your name is now kevin smith you're like oh that's super easy to remember right or or something in a sense and it gives you
everything like what your email address should be what is your password what is your social security number if you really have to give something like that or a credit card number your employment building these backstories really helps you remember who you are in this persona especially when you're communicating with those overseas or away from from the domestic united states uh i think that's it for this one but i don't like using those so our standard practice is to grab a photo pick one that you like and then make fun of the poor guy for five minutes i mean they're not real right so you can be you can you can have a little fun with it right like
so like for this particular guy he looks like he has like two first names right like something like what like chat chat chat no yeah so this is something when it's blown up you can kind of see like where the ai kind of screws up too yeah what was mentioned is his ears are not symmetrical and you're right he kind of has a little bit of elf ears there right so down here his caller's messed up i mean there's artifacts from the from the generation this this guy doesn't usually look good enough to work i don't know he looks like a like a i don't know what would you call his last name kent kent chet kent that's a hard name
to pronounce right but you know so our chat here we got to figure out what what his occupation is what his age is where he went to school maybe his job right because this is stuff that's stuff that's asked in like your facebook profile or your twitter or your uh linkedin right communication methods that you would have with people overseas so yeah i don't know he looks like he's like mid-thirties uh i would say he's probably in the military but i'm kind of biased just because that haircut's a little like military-ish um i don't know pick a school what do you think not pittsburgh michigan state count oh that's actually my hometown that looks scary
you doing some ocean all right so he's from sacramento he's his name's chet wow what a great probably went probably went to see kay mcclatchy too uh out of the military his email would be something totally ridiculous like like ultra chat he would have his name inside of it right he looks like one of those people who'd probably be entertained with his own name um but i mean you guys get the idea right like this it's a silly way of like coming up with a backstory for an individual that doesn't exist and you have fun with it because uh this is the only time you're actually gonna have fun um once once you start going live it starts
getting depressing that's the wrong way is it yeah it is yeah yeah there we go there we go so this is awesome so um now we got it all done right we built our persona hopefully you've aged it a little bit it's not brand new if you need to have friends on facebook because you're trying to make it even look even more believable go on fiverr it's like twelve dollars to get ten thousand friends i looked um it's really cheap actually actually if you need more followers on on youtube you can get it there as well but you wanna start building your actual communication platform your online presence per se right so the first thing you want
to do is you're going to go out and you're going to find yourself a privacy based email something like protonmail private on mail doesn't like share it out to other people right they like to say they're secure this is where all your information that's going to come in that's potentially sensitive and what i mean by sensitive is when you are communicating with these individuals overseas you're likely going to get some pii you know their names their passport numbers probably some photos maybe even their country identification code or number uh there's a lot of stuff that you don't you know you wouldn't want your social security number getting out there so you want people who are handling this information
here in the states to be handling with the same sort of discretion uh that's going to go to your proton mail the next thing you're going to do is you're going to build yourself your google or your yahoo and that's kind of important because that's where all your social media is going to be built from uh you know facebook linkedin they like to pretend and say like oh we don't like sock puppets you know we're against stock puppets because misinformation actors it's just not true right uh you can build yourself a sock puppet quite quite easily and uh they'll be like okay i guess sure cool you know add a thousand friends within five minutes like man yeah i'm
cool with this uh so your gmail you're out that's gonna go towards your social media accounts and then the last piece is really just setting up the social media accounts using that phone number that you had uh set up earlier that's going to go into your facebook and linkedin because those require a phone number i think gmail does too right gmail definitely does yeah yeah you used to be able to get away with not having a phone number now you have to have one so we had to add like the first three steps oh you miss your mic oh this is you all right so [Laughter] shenanigans so one kind of consideration we tapped on
earlier was whether or not you're dealing with an advanced adversary or a lower tech adversary if you are dealing with somebody who can monitor your network traffic or is viewing everything that comes in and out of the country it's probably a good idea to use some vpns um you're definitely going to want to consider where your operation is happening for example if you are in pakistan you want to use vpns to come out of india because they're not going to cooperate with each other when it becomes time for an investigation if they ask hey who was this where was this coming from india is not going to help pakistan they're not so you want to make sure to consider
where you're coming from and where your vpn pops are coming out of this is actually kind of important for the previous effort i don't know if anybody remembers or knows about digital dunkirk like the taliban as they were taking over kabul right like they were able to gain more and more control into the telecommunication networks there they were already shutting down the cell service and the um the internet service on sundown until sunup but uh slowly but surely they were capturing telecommunication points and putting their own network security people into monitoring that activity so that's where this kind of comes in as well yeah so uh here comes the fun part right like you've just built your whole
persona you you've you know we've been building up to this whole point what do you do now how do you uh how do you communicate with the people on the ground you're like i'm ready to help people yeah um so here's some things and things not to do right first and foremost when you start talking to people overseas like you're probably not like prior government employees right we've we've had team members who are not you probably never handled a source before uh the first and most important thing to do is validate who this individual is right um you have their information that was given to you by some ngo or non-government organization that's helping people get out of the country or
maybe even somebody who is within the government and they just need extra help right like digital dunkirk uh in this case you want to validate who you're talking to don't tell the information that you have to that individual because then they'll just be like oh yeah that's me for sure right have them read you their passport number have them give you their country identification code right be smart about this because it this this part right here is is what most people that were unfamiliar with these kind of techniques or um helping individuals screwed up on the most and that caused a lot of a lot of problems for us later on uh only use your temporary devices for
communication and i will double hold onto the mic again because i cannot reiterate this enough do not use your home computer or your home phone right let's say you're looking for somebody you're trying to track down somebody and you find their linkedin right and you're using your fake persona of gabe uh to go and look at linkedin's is this the right individual the photo seems to match up okay let's try to contact them through linkedin right you're trying to get in contact with these individuals in any way possible uh if you use your home computer i don't know you might be logged into still your account and now your account is showing up in their
viewpoints right it's another added point that if that individual gets captured and some sort of like investigation or sse is what we call in the military is done on that individual they'll find you right and then they have your information they have your name they have your face they know that individuals talking to americans based off the conversations on their phone and you're the only american in their linkedin presence who are they going to come and look at right who are they going to harass so only use your devices um another really important thing and for any prior govi or military people in the room pace which is uh a communication plan primary alternate contingency
contingency and emergency i just use this all the time uh and i still can't remember it basically what that means is you want to have different communication methods with the person that you're talking to right let's say hey my primary to talking to you is going to be signal because i can set these to delete after five minutes uh and then once these delete and the end of days has occurred delete my phone number i'll contact you eight am your time your alternate could be all right so signal's down in country because the the entity that is chasing you is uh shutting down signal traffic let's go ahead and use whatsapp all right whatsapp doesn't work let's use facebook
messenger let's use uh just a phone right let's straight up call you on your one nine or your plus one nine or your whatever country code plus one nine three um [Music] you know have have different methods to communicate with this individual but also know that these individuals are probably scared and they're not at the same level of of uh clear-headed thinking as as you're gonna be on your side behind a computer uh so create a duress word from that if they are walking through a potentially scary location like a checkpoint with people with guns and those people with guns start shooting which has occurred a few times in our uh our efforts you know have them send hey here's my oh
[ __ ] word right for lack of a better phrase of it that's the duress word once they've given you that word they should know delete your phone number and when they remake contact with you you have to start back from step one validate who you're talking to because you don't know that person could have been captured right that person could be killed and now somebody else is using their cell phone they don't know who they're talking to uh something like that if they didn't delete the number which is what happened a lot of times then well whoa don't don't touch that button just yet but we got one more section to go yeah then we got the things not to do
this is like the put on your cowboy hat right and then take it off put it to the side because we're not using it here put your cowboy boots down this is where it gets scary right because this is what gets people in trouble don't have an active conversation with somebody while they're on the move this was actually a lesson learned from digital dunkirk which was really important the taliban don't like it when you talk on the phone in their checkpoint areas they'll tell you get off the phone right particularly if it's in english oh yes especially if it's in english right they're like you know i'm watching you fam right uh but actually way more
aggressive and probably not something to joke about uh an individual was killed in this instance where they were talking to the the handler on our side in english a taliban checkpoint guy heard him shot the guy didn't even ask questions just shot him right so don't have an active conversation tell him what to do tell him where to go drop locations but cut it at that leave it a text if you have to have a conversation make sure they're in a secured location where they're not going to be overheard by other people who could potentially rat them out don't group multiple contacts into the same channel right uh you don't know who you're always talking to people get captured all the
time especially when they're trying to run out of countries if they're being persecuted wrongly or even human trafficking right like you don't know who is who and you're only a guy behind the computer so make sure you're keeping everybody separate it might take longer but it's smarter to do it this way uh do not promise anything this is for your mental health right uh these these operations weigh a ton on your on your mind especially like coming from our perspective where we were actively engaged in these kind of things as military people and now all we can do is just passively engage in these kind of operations where we help out and and do it on behind a computer on this side
and if you start promising things that's going to weigh on your head especially if you can't get that person out right you're gonna be there going all right yeah yeah we're gonna we're gonna get you out of country we're gonna get you safe if that person gets captured or killed like it's not gonna just leave your head of like oh yeah that's that sucks no you're gonna be like oh i promise this guy like it's gonna weigh heavily on your soul so that's your mental health keep at it right and uh of course the last thing is don't don't forget to do the things in the to-do section these things are stressful we get it if you're new at
these kind of operations reach out to people like us especially if you start helping in these things because we're more than willing to help we like opsec we like having these operations continue we like to help people so anything we can do to make sure that you as a new person in the group can do it right you know we're gonna we're gonna stop we're gonna slow down we'll be like okay let's let's crawl before we walk let's walk for a run those kind of things hit it this with me again all right so obviously there's things to consider uh traditional step five we've talked about it a couple times your mental health's important i got to stay alive so i can help
i need to take care of me think about what you're doing before you commit to something before you make promises you might not be able to come through on um know your limits don't take on too many contacts right we've talked about not grouping too many people into a group conversation part of that happens because i take on 15 20 25 contacts and i can't manage all of them at once don't don't do that to yourself uh we'll talk about what happens if what can happen i guess if you do that here in a little bit um yeah um i got they're too small over here and then i got to turn around dingus so we
don't plan how you're going to debrief uh how are you going to decompress from this how are you going to mentally remove yourself from what you've been doing lately because again it can be very mentally and emotionally taxing and then understand when your involvement is more of a risk than it is a benefit there's value added in saying hey here's a safe location this checkpoint doesn't exist here's where you can go here's a safe house but after a point providing that information might be more of a risk because the traffic's being monitored or i can't verify that that route's safe anymore so there it does there may come a point where you need to go
it's time for me to go away i'm sorry you're on your own i've done everything i can i can no longer help it's more dangerous for you now if i continue talking to you yeah there's also a really good story you guys can look on the news which is pretty true a group of cowboys at the the last digital dunkirk they decided hey we want to keep helping um you know these are all prior military guys they're like yeah we want to keep helping but we want to go back in the country so they brought a ton of guns into pakistan and then tried to fly into afghanistan like yeah that was really going to work
their bud so uh you know where your risk becomes more or where your involvement becomes more of a risk is this because now the us government has to be like really dude now we got to try to get them to bring you back to the united states so we can prosecute you here instead of using in a pakistani jail um but you know you we all want to help we get it but you have to know when to stop yeah big hat on that one don't don't fly to pakistan with a plane full of guns it's a bad idea don't do it it does look really cool though you know oh yeah we uh find a meme for that one yeah okay so um
all right we should have definitely download one that's bad okay so here's where it starts to get kind of depressing but the memes don't stop so sorry about that guys this is this is how we defeat humor in the military as we just make jokes um but this is where we talk about the consequences of bad implementation or your bad implementation of ttps right uh some of the things that we're going to talk about here is loss of your anonymity is that the right way you pronounce that word anemone and anemone and then i can't speak english sorry guys uh disclosure of privileged information right uh you don't want their information get out there just like you
don't want your social security getting out there uh you can burn multiple objectives in your operation from from doing things poorly you can get harassment from the baddies nobody wants that and there is potential loss of life as we've already mentioned before so uh the risk to you the the one thing i think is really important is you need to understand that you are not always 100 disconnected form from your sock puppet you're not getting the stock puppet from the government you're not on in the government's cover program right the united states administration for social security isn't giving you a brand new social security number this is you uh and a sophisticated enough actor can
come down to track you via network tracking financial tracking right if they really wanted to get back at you they could find ways of getting back at you is that going to happen if you guys stick to what we've been saying so far probably probably not right like there's plenty of people out there that do this and they don't get caught at all and we don't even know who they are uh but it's on you to not get doxxed just like how it's on you to not get doxxed in the normal world if you're out there playing call of duty and you start trash talking to 14 year old you know you probably should not do that because he's gonna dox you
you know they don't have any they don't have any control over that or their own actions but what can happen so online harassment threats uh travel restrictions right if you start doing this against russia it's not a friend of russia it's not necessarily like russia's gonna be out there like oh yeah hey no i don't like that there it's just a line of people are gonna be like yeah you can't come here you can't come down to uzbekistan uh which you know for some of us that's not a problem i don't mind not going back to afghanistan not gonna lie uh and then for all you fed boys and girls out there your clearance can be put at
risk here uh the fact is if you have contact with foreign contacts which you will if you start doing these operations you have to put in your sf86 for those who don't know what an sf-86 is it's a big long paperwork that that you you have to fill out it takes like a few days and you hate your life and you're like this is miserable uh don't do it right if you if you're a fed just you know help out other ways so now yeah we uh as you may have noticed when we missed the meme uh we we didn't fully update this one uh yeah you fed girls you guys can get out get away with this you know like
you'd be good to go they'd be like particularly egregious is if in the event that somebody's phone does get captured and they say hey this is no longer the person you were talking to this is made up name x uh at say the checkpoint now you do have to say on your clearance paperwork yes i have been in direct contact with members of a terrorist organization and then you have to deal with that yeah if you've never had to negotiate with the taliban it's a good day it's gonna suck yeah okay so this isn't a real face this is a made up one just like all the others um it's also not a real name but these
are examples of uh two two examples of what not to do or what happens if you do it wrong and then we'll do one good one so rebecca here uh as a single-aged middle mother found out through a friend through a friend through a friend through somebody who worked uh these kind of operations that digital dunkirk was ongoing she wanted to get involved so she did she contacted through whatever means she needed to very low technical knowledge does not know what opsec means um now that i've said that out loud up here not everybody is going to know what object means opsec is operational security it's the concept of how you're going to protect your operation as it's
ongoing um and since that was the case we've touched on this before the hostile entity contact confiscated words are hard man her contact's phone they reverse search that phone number to get her information and then they started harassing her online and sending her personal information back to her because she was using her personal phone to make contact with our contacts in country this is why you don't do that because you do not want the taliban saying hey you live at address x and i'm coming for you and your kid you don't want that so this is an example of what happens if you do not wait follow the instructions yeah and something to point out
when you when you kind of make these mistakes right whether it be through ignorance or through uh just bad practice this does take resources away from the ongoing operation right we had to take a few bodies and say hey let's start helping rebecca here um lock down her online persona she had like her facebook like public to everybody right she could accept messages from anybody aside from having her change her phone number we had to start like working through the list of okay how can we lock down like your online social presence so you're not getting as many like random threats from uh the taliban and i mean that is that's pretty stressful i don't know if any of
you guys have received death threats before but that kind of sucks especially as a single mother right but at the end of the day right she got doxed ducks deduct herself don't don't do that right it's on you uh the next example is bobby and this guy really does kind of look like a bobby um but uh the reason we call him bobby is because bobby is also another uh name i'm sorry if your name is bobby but you know it's like your best friend or a blue falcon or if you guys don't know what a blue falcon is it's a guy who pretty much screws you over in your unit uh don't be a bobby i'm sorry if your name is bobby
we've kind of singled you out here um but bobby here he was a prior government employee he had some moderate technical knowledge right he wasn't like dom and i.t but um he wasn't like a cyber guy he never did i.t security or anything like that uh and bobby's biggest mistake was he didn't know when to say no so as in this case digital dunkirk was ongoing uh he was like hey man yeah i'll take more like hey we got we got another 12 families can you take them yeah i'll take more it ended up being like bobby had like 50 plus contacts inside his um his roster of things he needed to take care of right and so
uh bobby thinking all right let me streamline this conversation here we needed to move all these contacts to a safe house which was a a hotel that we had paid somebody roughly about like ten thousand dollars of worth of like anonymous donations we had people like the whole day going all right yeah yeah let's collect some money we we gathered about ten thousand that was going to keep our contacts like a whole group i think it was closer to like a hundred people say for about like 10 days right bobby's like oh yeah no that seems cool i'll just group them all instead of giving the contact information or the the movement information each person
individually well this is a problem right this is a problem because as those individuals were making their way to the safe house one of those group of families got captured they got stopped at a checkpoint they were arrested the phone was searched the the individual didn't have time to delete the information on there and now you have a adversary in your group chat who just scrolls up and goes hey there's a safe house information here i wonder what that's all about right none of the prior information was there i guess he had given the um the back story in the private information or private text there that they had deleted through signal uh the only reason we know that there
was an adversary in this group was because that person started asking really really weird questions right like how many people are going to this safe house uh is this safe house within this region right which was semi-controlled by rebels forces at the time right they were asking very very weird jaded questions that bobby's contacted the time probably wouldn't have been asking they would have been like just get us there safe do it now so when we went to go actually do the reauthentication of who they were right reconfirm who they were uh they couldn't they couldn't give us any of the information that was required they couldn't give us proof of life and in that jazz and we were able to determine
more than likely this guy got arrested uh or that contact family got arrested and um now the safe house is burned so that's ten thousand dollars that was thrown out the window right just like that that's not like necessarily our money but that's people who are trying to donate to a cause to make life better for those who are being wrongly persecuted in this case and a lot of these individuals going to that safe house we're already on the hit list for the taliban so that's a that's a bad day especially when they're like three-fourths of the way there and you got to go hey run just i don't care where you go hide right so
don't be bobby bobby's kind of creepy he also doesn't have like one side of his glasses uh right so another ai generated problem broken glasses bobby yeah don't sorry bobby if you're out there all right so we talked about what happens if you do it wrong unfortunately the list of things that happen when you do it right is real short it's you don't get doxxed you don't get threatened your app doesn't get blown that's pretty much uh pretty much it if there are small issues they're small issues it's a family needs to relocate instead of 80 families need to go to somewhere i don't know where we i don't know where to send them so
your hiccups are small they're manageable the list's pretty short which seems sad but yeah don't do it wrong don't don't be dumb all right so also not a real face i just thought the black bar was funny and it kind of looks like one of our buddies this is an example of a better implementation pedro here fake name prior military high technical knowledge knows about opsec and knows how to implement it i'm not saying that because he's prior military he's better at it it's just his background um so this guy managed to establish communications with 50 plus contacts bunch of people different places kept them all segregated kept them all separate didn't group them together
uh multiple successful ops digital dunkirk was one of them but there's been several others i don't know who this guy actually is i know him by a couple of handles that's it i don't even know who he is we've worked with him a couple times we've worked with him a few times yeah he comes from our same background so we were able to confirm who he was through through other channels but um yeah this guy very very sneaky even amongst the group good implementation but as you can see right like not a whole lot to say there he did good he did good he got people out that's all that we care about you don't need to you
want to be famous about doing it yep bonus step six burn it down get rid of your vms delete everything smash your sims take i like taking my hard drives out and shooting at them because i'm a hillbilly from montana uh delete your vms close all those accounts pet your dog call your therapist whatever it is you need to do next start that detox process start your debrief uh take care of yourself because now now it's that time just don't keep anything don't keep anything it's dumb too you don't want to use that cell phone anyways you're probably getting calls from people you don't want to get calls from and i mean you already get enough spam
calls on your home phone why would you want more spam calls right think of it that way it might be tempting to say hey i need to hang on to this proton mail with some information in it because what if this guy contacts me again then i have us all in all of his information we're ready to go but you do not want to do that because you need them to establish who they are to you again phone got captured email got compromised whatever it is it's been six hours i don't trust this number anymore i don't trust this email and i chose this facebook account prove to me you are who you are so there is no
real good reason to keep any of the prior information get rid of it delete it shut the accounts down yeah and so because we're military we like to sandwich everything so uh now we're gonna give you a down and dirty review of what we just exactly talked about but we have about like a couple minutes left so just just to go over what we talked about we talked about no you should know what a stock puppet is by now if you don't like come talk to us afterwards we'll explain it better maybe probably um you should have an idea of when and and where to use them uh where to start some silly techniques to build your own stock
puppy if you don't want to use name generator uh how to use them i already said that and the inherent risk and difference and consequences of of good and bad implementation right like ultimately if anything that you've learned today is that by going and cowboying it up you're gonna screw somebody else's life up right there's that potential when you start working in this realm of uh humanitarian operations but with that we have any any questions i i know some of you got some out there we don't we don't do interpretive dances though no we did sorry yeah sorry we didn't rehearse the tap routine for you all right well cool if uh if you guys
are too shy come come talk to us afterwards we'll give you uh give you some pointers thanks everyone awesome awesome talk