BSidesWLG 2017 - "Alex" - Operation Luigi: How I hacked my friend without her noticing
Show transcript [en]
hey can you all hear me okay oh you definitely can all right everybody buckle whatever you normally buckle because we're going on an adventure my name is Alex and I'm on the incident response team Atlassian and somebody let me give a talk here and so here I am we're gonna spend a while we're gonna spend half an hour talking about Mario's green brother so thank you for signing up for that recently some people write about me and they referred to me as a hacker who goes by the name Alex and so that's that's my that's a hacker named now those are my real name and there's nothing I can do about it so just I mean
please join me in pretending that I'm ok with it so um before we start this is a story about me hacking my friend absolutely don't do that don't hack your friends or anyone tell your friends don't do it unless you use specifically Austin first and they understand what you ask of him then it's okay having said that this is my friend Anna that is not her real name that's not a real picture I'm actually several I do in a trench coat and she gave me permission to do all this stuff I asked her is it okay if I hack all of your stuff and she was like absolutely yes go for it and so a few things about her she did a
comedian that's her job and she's she's she's a sweet young lady oh she's kind of my age and she's not particularly Tecla to it she's as a stick with it as everyone who's her age and so she's gonna be the subject of this talk so let's do it here's a couple of rules that I told her about I said I'm gonna have 12 months to do it I'm not gonna say when in that 12 months somewhere in that 12 months I'm gonna let to delete anything I'm not allowed to like modify anything that she hasn't allowed to delete her stuff I can't interrupt what she's doing in a normal life she can be kind of like
bother her so for example I couldn't reset her email password kasym she couldn't get into her email and they'll be bad also it's a couple bills added by me I have to do the entire thing without her noticing that I've done it like I don't want her to know that I'm doing anything until I want her to know and also I'm like friends with her and I like have you on Facebook and I like friend know but all that and so I don't want to exploit that information I want to do it as if it's for real also you might be wondering like hey there's a picture of Louie do you have the friend talked about Mario's brother why is this
talk called Operation Luigi anyway in the interest of time let's just get straight to it so the first thing I want the first thing you do apparently you do this and you do this is in thing apparently the first thing you do is get someone's email address so I use the UM I was recently the shadow brokers released this tool recently which lets you do this and a bunch of stuff into Google and so I just typed her name into tapped her name into taps her name and the word late in smashed that Google search button so how to violate the Terms of Service and it worked we did it okay I got an email just gonna need that later
I mean I think this is my first time doing all this stuff so I'm pretty sure this is how it works so but what in doing that I noticed that she had a hotmail email address and I was like that's that's strange because it's a 17 who's who's doing that he's using hotmail to store the email that's quite rare and so I went to her Twitter and tried to reset her Twitter password because when you try and reset someone fast word it will show you a bit of email and though it showed me a couple characters and the mail calm and I was like no this really is her email address the rest of this talk will be about
Microsoft hotmail so let's do it I also needed to know her phone number again advanced hacking software just type email address which I already had and the word phone and normal people don't have good OPSEC so now she said she was a head at the head of some sort of clubs and she was like hey you want to sign up and the contact here's my name and email and phone number which is what you have to do is a head of a club thing but it also happens to not be very good up there so I also got the phone number done this hacking stuff is easy so now what do I do I don't
I gotta have a plan mister goodness no I'm done this adventure I've got this phone number and stuff I got a whole bunch of other stuff and pasting it into a Google Doc I think the industry-standard thing is to send someone an email with heads it was Heather's word doc and a macro Beauvoir but that's kind of like that's kind of boring kinda happens all the time and like did she even use Microsoft Word like she's a sweet young millennial did she actually use it I don't have to Microsoft wait maybe she doesn't so I don't really I don't really want to do it if it's not gonna work so I'm like well we'll start with an email let's
start with maybe I can get into an email and then figure something out again no plan off the rails so now the next step is to get an email passwords I can't just I can't like recover the email account because then she would lose access to it so I have to make it so she has access and I have access and so there's this great website called have a component where you type in an email address and it tells you if it's in a past late list of passwords and companies who got hacked but Noah doesn't say you have to type in your email address so cunningly tapped in her email address and she was in a couple of
things but the only one that had passwords was in the only one the only breech she was in that had passwords exposed at the time was tumblr and I was like okay I just happened to have that tumblr bridge lying around and so here's what looks like the format of it is it's an email address and then a colon and then the password hash but the password hash format is kind of a mystery it's kind of sort of only partly documented and so I read some documents about it and like okay no it's actually the the consensus seems to be it's a sha-1 hash and it's a static salt and what actually he just said static so it you can't do that you
have to explain what it is so here's an example imagine that it's the early 80s and you're storing passwords in plain text it looks like this and that's okay you've done it you've stored the password the user can type the password you'll know whether it's the right one it works but no I've heard that your hash passwords and say okay let's do that let's turn the password into a big long hex number and okay now we're storing password hashes we're doing it but I went to a havoc on recently and they said you should salt your passwords okay let's do that and so now you have to you add the a dash to the password so you
add a salt to the password before after in the middle doesn't matter and then you get another hash and the point of this is so people can have a precomputed list of a bunch of hashes and so here's me doing it here's me following the advice okay got to add a salt to all these passwords I've done it can I go out but you might notice these two these two users have the same password and so they have the same password and the salt is the same everybody so even after adding the soul they still have the the thing that's getting hashed it's still the same for these two users and so in fact it's if and only if if someone has
the same password they definitely have the same hash and the other way around that's it what happens if you use a static salt and so when you hash everything these two users have the same password which is one of them which is like the salt has done its job in the sense that the pre-computer check won't work but I know these people have the same password if I have the hashes so why am I telling you about this because the first thing I did when is look up Diana's email address in the tumblr password dump and I looked it up in the password hash was there and I was like great and I spent a lot of time
fruitless are you trying to crack it because I didn't know the soul cuz I couldn't back the hash the normal way so I was like okay I guess I have to do something else and so yeah the salt no supposedly the salt is out there in the internet somewhere I don't know what it is if you know what it is please tell me cuz I still don't know and so instead of trying to crack the hash I have searched for Diana's password hash in tumblr dumps another email just the raw password hash and can you guess what it was like can you guess what happened when I were - in the in the list of all
the tumblr passwords you think it would be just her but actually but actually there was a whole bunch of good folks on tumblr calm who was about 20 who had the same password well had the same password hashing because aesthetics whole thing we know that they must have the same password and so okay the first thing I've learned it's probably not a particularly good password because a whole bunch of people have thought of it but maybe it's a more than I can win from this so I took just the email addresses of those people so what diners emails in there but this is this is a list of email addresses of people who have the same password they
all have the same password as each other on tumblr also relatedly in 2012 LinkedIn was hacked and a whole bunch of their how bunch of their emails and passwords got exposed and thanks to the kind efforts and GPU cycles of the password cracking community almost all those passwords although almost all the attachments have been cracked and those passwords available in plain text on the public internet and so I got both of those but for the next to each other and I looked up the email addresses of the people in tumblr or the same password Anna I looked up those email addresses in the LinkedIn dump and so all the plaintext passwords it's simple and I
found that no they didn't all have the same password in lydian but most of them is like 60 70 % had all the same password in in LinkedIn and I was like well that's got to be they must have had the same password as on LinkedIn and that's on tumblr and as each other and they must have used a same amount of all those things so this has got to be down as password it's probably this QWERTY one thing it wasn't actual anyone but in this example it is and so I'm like okay let's go come on let's go to the hotmail login screen tap it in doesn't work when I went to all that effort and typing in
QWERTY one nope wrong password like well damn why did I do all of that and so then I was like okay let's try it on Facebook and on Facebook it said the password he used to be have asked about five months ago it wasn't anymore if you don't know Facebook it's a website we can keep up to date with the memes your friends are being tagged in okay no Facebook that's not gonna work so I guess we have to do this the old-fashioned way which is did send doodoo sound sort of phishing some sort of social engineering okay let's do it maybe this is what I should do I don't know I'm not an expert but maybe this is
how socially didn't works like it's my first day okay you're gonna take a picture of that cool that's all right so here's the here's the extremely unnecessarily complicated plan I came up with so Dan is gonna be doing whatever she does on the Internet normally then she's gonna get a fake email from Microsoft and that's gonna make a go to a hotmail login page even though she's already logged into her email that'll be a fake hotmail login page it gives the password to me and then after that she'll go to the real hotmail login page this is like the classic way to do a credential fishing thing and so I'm like okay first step is I need to make an
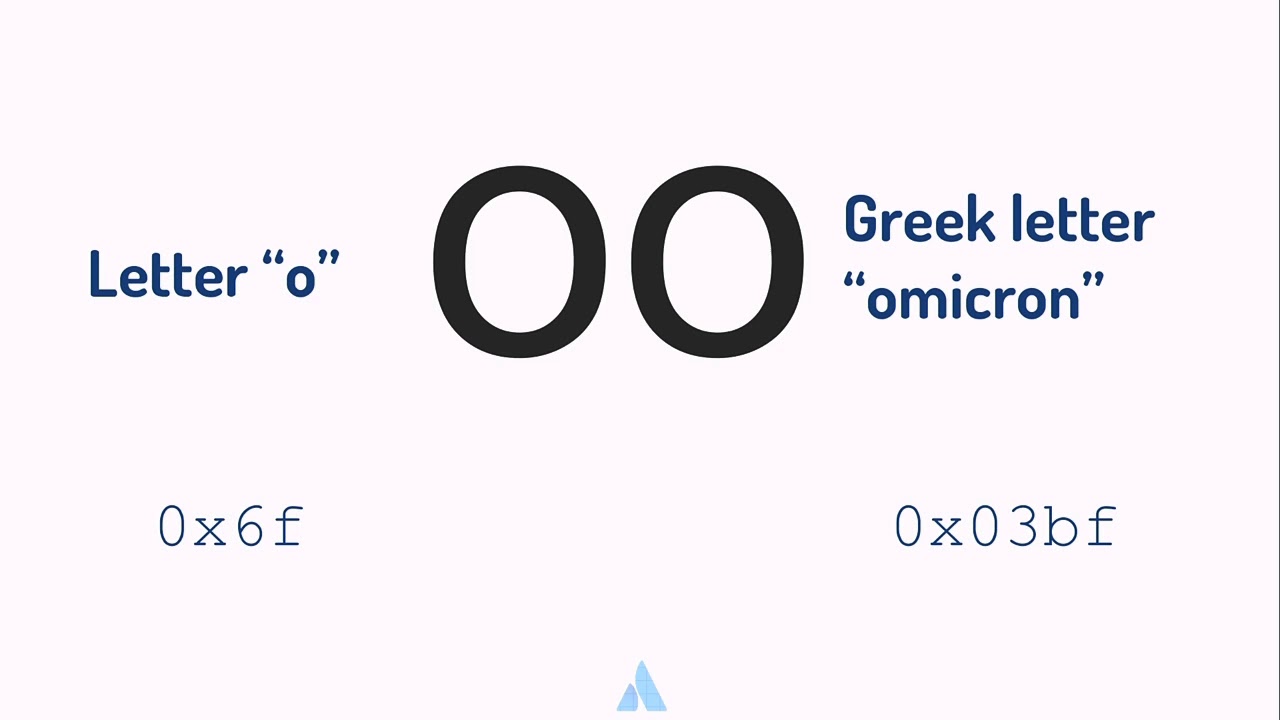
email account to send this email I'll send it from house that's not gonna work has to look like eyes from Microsoft I couldn't register it I couldn't register any email addresses with Microsoft in the title or account or team or something probably to prevent exactly what I'm trying to do so let me introduce you to many friends these two round friends it looks like they're two O's but actually one of them isn't oh and one of them is the Greek letter Omicron which looks a lot like an O but you know to a computer it doesn't it's a different code point and so if you spell the word Microsoft a strange way for example with these with these horns
instead of the O's looks like a Microsoft to you and me and in the hotmail web UI font but not to a computer and so imagine you're wondering it's just gonna work and I also didn't know whether was gonna work I couldn't know in advance whether was gonna work so I just went for it and it does work success this is my Microsoft account team email address all those oohs and ahhs the secret is that only you and me know about and I sent this I don't know I copied this email from like a real Markus officer Security Alert thing which says like oh you know there's Russians in your account or something you better you better click hear it you
better log in you better do it or it's gonna be real bad I tried to not spend as much and not go to great lengths on this if I didn't have to even though did the only thing and so I sent her this email which says you have 48 hours to log in in this extremely legit login screen otherwise bad things will happen and so I have to do that I have to make a fake login screen and how do you make a fake login screen well you go to the real hotmail login screen and you use this amazing hacking technology called right click on the page and then you hit this button that's a good fun I'm not an
expert but I'm pretty sure this is what they doing mr. robot and so then once I had a copy of the pay website a copy of the hotmail page it was just HTML it was just like text and so I needed to put this on the internet somehow and you can go to there's a lot of complicated ways to do this because hosting your own servers in various certificates and stuff but there's a static hosting website which happens to be a great phishing website I don't know if they know and so like they'll let you host your thing on there and you can have your own subdomain you can whatever subdomain you one it's got an HTTPS
certificate it's a legitimate website it has a good reputation and no one all the good subdomains I'm taken so I was able to get a good one so now you know this is not this is not sponsored by them but you can use the referral code Diana to be immediately reported to the NSA and this is the this is the this is the domain I chose for the real logins the real hot my whole thing is login dot live.com or something and so I made one that looks similar in the beginning part I don't know if I could do more than one subdomain whatever course gonna look at it probably not but real looking real
login screens they look like this they look like this they have a bunch of random stuff after the Euro so I put a bunch of other random stuff there which I copy pasted from the Google login screen whatever it's fine and so here's my copy of the login screen looks exactly the same it's actually the same screen job because it looks exactly the same and it has her email prefilled in there so it looks like you know she's ready to login because their email field also added this little extra thing to the login screen which when when the login button is clicked it'll add an image to the page and the browser will try and
request that image but the URL of the image is just a website I can't roll fold flash to Anna and then a question mark and then plus whatever the password is so the reason I've done this is because then somewhere in my logs on this and this is like the cheap and nasty way so it's faster it's bad then somewhere in my logs I'll have requests for forward slash Diana plus whatever the password is so I can just grab my logs for Diana and just be there and also I am made it so when she clicks the button wait one second and then goes to the remote to the real hotmail login screen the one second is to simulate
Australian internet times anyway so I sent the email to her and I was all excited and I waited for 24 hours if you didn't click on it and sounds like okay maybe I did give it 48 hours so maybe she's just running late but then 48 hours she also didn't click on it and I was like okay good two times it's not working I'm not a hacker I'm just emailing my friends and so I was like okay alright let's do this the hard way I didn't want to but now I'm doing it now I wanna do like a really specific phishing email that's just for her and so I want it the usual way you do this with a Google Doc and
I'm like just mark is it I can't use Google Docs because it's a hotmail account is there a Microsoft version of Google Docs they absolutely is and it's called one cloud sky something something something and you can absolutely use it and I was like great and so I made a fake resume in whatever this thing is called Docs and here's the plan this time Emma's gonna be doing her anything she's gonna get an email from a recruiter and then the same things gonna happen the recruiter is gonna link it to this login page and then on the other side of the fake login page will be this Google Doc that I've made no this Microsoft Google
Doc that I made that is a resume and then she'll go then she'll just read it and be like okay whatever and go back to normal and not suspect to think that's very important it'd be bad if she suspected a thing um so now I have to make a fake recruit it's an this from and so I'm here's a Google account creation screen did you know you can type anything you want in these boxes like that's what I learned and so I looked up like a company and stuff and found a believable sounding name and all that and here's the email I sent so let me go through this so the emails from Kathleen willows which is a name that I
made up and this is from a regular gmail.com account because I didn't think normal people look at what email address things are from I didn't like spoof the domain or anything because I think it just doesn't care she just not gonna look at the domain and even if she does it'll be like from Gmail maybe it's a personal account whatever and so it says hello Danny's real name trust you or well I tried really hard to sound like a stressed office worker in this email because you know I didn't want to sound like myself and so I hope this is how office I hope this is how office recruiters talk and so like hey what's
up hey what's up Diana somebody has applied for a job with us and they listed you as a reference and can you please confirm that you know this is the right person that they work with you and all that and so then it says click here for the resume mm-hmm and then after that it's got hope it's got a form where says can you confirm some days can you write some stuff from one to five that's just to be distracting so the last that's just something distracting to read after you've read click here because it's the last thing you read is click here you might go mmhmm and then it says also can I call you about it do you let me know
time for the call if the phone number her phone number okay and then I made a little email signature its neck you'd I like what went to great lengths to make that little email signature anyway she worked I send it to her and she clicked on the resume and she logged in to login screen and she'd have to the password but particularly astute audience members will have noticed that the password that she attacked into my login form thing is query one which is the same password as I had from the tumbler dump earlier so actually actually I already had this password for her hand this whole whole thing this whole thing is not actually helped me log into
anything of hers so I got QWERTY one again okay cool and so I almost gave up here because here's what I've learned about her she does not know what I hotmail fast what is because like she just typed the wrong one into my login screen but also my login form thing will accept whatever password you type into it so and she doesn't know it's fake so now she thinks that her password is the one that you just typed in to the form and it's all my fault I changed the login form I change the login screen to the fake login screen to just always say wrong password the first few times you type something into it and
I also made it so if you type in the previous password if you type in QWERTY one that counter doesn't go up see after typing three things that are not quite anyone in the hope that when the pastor doesn't work she'll just unload all the passwords whatever they are because that's what you do when you like if you just have if you just have like two of a passwords that use for everything when one doesn't work you just unload the other ones that's what you do it's real and then it then she replies to the email being like no I don't know who this person is yeah I guess you can call me he go call
me I didn't call her and then I replied to her in a different font cleverly to look like it's a template or something I don't know saying oh this is the wrong resume so sorry two exclamation marks just rest that office worker anyway here's another person here's another resume this is actually the right one even though it makes no sense that there are two separate people who both worked with you at the same whatever it doesn't matter it just says oh here's the same form again with a different link click it please and this time if he clicks it and shouts a different password because she couldn't have typed in the previous one because I wouldn't let her and she typed
the same thing three times but whatever and okay here's a different password I immediately go to hotmail you see elite browse the elite exploit kit the Google Chrome browser to type the password in and and it works and we get into email inbox yes finally that was easy [Applause] see was easy was simple anyone can do it so got it got the email password and so I immediately try the password in everything else that I found of hers all the Facebook all the other accounts and doesn't work for any of them because somehow I've chosen someone with slightly above average personal security who doesn't have one password to everything or even two fast words for
everything and so okay and then she replies to the email being like no I don't know this is what what's this all about why you email me all these resumes and I just replied back trying to sound like real recruiter saying like basically please just go away and don't email me anymore all right please just don't freak out and you didn't reply so it's good anyway back in an email in in Outlook mail when you when you search for something it shows you the last five searches so when I clicked on it I saw the last five things to search for know me interesting but I really wanted to search for some things like say the word password because I
wanted to know if they were more passwords in there but if I search for the password it'll appear in the search history thing so I went to this screen wrote down the five things that she searched and then searched for my search for my things didn't find anything by the way I found the same passwords over and over again but no ones I didn't have and then search for the ones that I wrote down in reverse order because it only shows he's the last five I think Microsoft knows what I've been up to but I think for the user use his last five so it was fine it was transparent and she probably would have noticed anyway
like regular people turn on paranoid people really like look at their last search history I don't know maybe anyway so this I've done it I mean her email I did it I'm done it I've hacked my friend this is the end of the talk obviously it's not never believed these slides this talk is called operation Luigi Luigi is Maria's green brother and he's um you know he's the one key one of the pair and so why is it so quiet operation Luigi well to explain let's go through it he's an operation we do work step one get into her Twitter account but also I'm not allowed to walk her out of the photo account because that's one of the
rules if she can't she can't be disrupted and she got notice so I also can't let her know that I'm doing this so I have to be in a Twitter and she has to be in there and she can't know that I'm in there easy so here's this 8 dimensional chess strategy I came up with I went into an email when Twitter reset her email password and I mean I mean her email so when I click the posted resetting it emails email INBOX which is which is I've got access to see then I set her Twitter password to this QWERTY one thing this is like so this is the password that I think she thinks her
Twitter password is even though even though I know it's not so this is the eight dimensional chess strategy thing and so I said change it could Twitter password to that and then I deleted all the emails because when you when you reset the password it sends emails and she can check that email inbox in theory I should have like waited till she was asleep to like do all this so she didn't like see the email notification but I didn't because I'm young and invincible anyway the next step is to wait for her to log into Twitter account because I want to make sure she's gonna be locked out if I should our sessions are gonna
be cleared and she's gonna like be locked out of Twitter and she's gonna have that enter your password prompt and even though her Twitter password is not quite one I really need her to type QWERTY one into that box and so I wait stressfully for head log into Twitter and then eventually she retweets a picture of a cute dog yes success and she didn't well she also didn't yell at me hey my stuff so I guess it worked and also I'm gonna need to get into LinkedIn and so I'm LinkedIn I trying to dig I do the exact same process but when I try and set her password to QWERTY one LinkedIn says please choose a more
secure password presumably because I got that password out of LinkedIn dump earlier so I was like fair enough I was I thought I was doing there but I just changed it to her same password as that you know and then there's a little checkbox I know if you can see which says require all devices to sign in with a new password that's like LinkedIn speak for would you like to clear all of your sessions and by default it's unchecked and I was like I'm absolutely good for that LinkedIn don't even worry about it don't worry about cleaning the sessions just change the password great so now she won't even notice she won't even be logged out and
so why did I do all of that to explain I'm gonna need the help of former US President Barack Obama this is because I did some stuff to Diana's profile pictures but I don't want to show you how real pictures so I've used Obama's pictures so I went onto her Twitter and downloaded a profile picture and then photoshopped it like this I don't know if you can see it's quite subtle that's like a ten percent transparency picture of Luigi on there and then I reloaded that that's a profile picture and there's no notifications anything we could do that so she had this little little lady backdoor situation and then I did that same thing on Ellington she
had LinkedIn feature as well and another Luigi on there and I left it like this for like weeks and she didn't notice but afterwards one of her friends said that one of her friends noticed and they were like oh I just thought I just thought that I was just doing that just you know for fun I was like okay lucky lucky etiquette chord so yeah that's a she gets silently Luigi for a couple of weeks and I'm like great that's it I've done operation Luigi but she doesn't send me out and like I'm practically a Luigi technician at this point and so like it would be a shame to just just stop here so that's
why the rest of this talk will be about operation waluigi this is gonna be this is gonna be a sinister turn for mature audiences so I don't really have any justification for this so I'm just gonna tell you about it that's okay and so when to LinkedIn and change their profile picture to be a very obviously while the we did one changed her LinkedIn bio to be the entire Wikipedia page for waluigi change changed all of her schools and stuff with waluigi schools and to be like mary attend of stuff and when i do all this lincoln says her profile strength is advanced you say you're welcome I also I also respectfully made a copy of like made a
copy of all the old LinkedIn stuff so she could change her back if she wanted to and so also then I went to a Twitter and changed her profile picture to be this much more obviously well elite profile picture and change the name and change the location and all that it's because I wanted to be really obvious and loud like hello you've been expertly Waluigi my friend and so then I tweeted out this picture and then when I sweet when I tweeted out this picture she replied to the tweet being like um do you like that's not me that's her tweeting that because because we're both in the Twitter account and she was like OMG and then she replied
saying I've been hacked my dudes and then I replied to that tweet cuz I'm also her same
and then tweeted out this also you can translate that one from Indonesian it's the same and I tweeted out this picture longing for the date of this sweet lad went wasn't that a simple time and yeah that was operation waluigi and so then what happened Donna loves her new waluigi life so much that like she went and changed her facebook stuff to also be well what we do you like to be the same like I didn't have to do anything for that she just did it for me because she's into it give you some choice quotes from her she says she since listened to a lot of waluigi songs and really got into the culture
waluigi ultimate similar first modernism he exists only as a foil there is some takes on waluigi i did not know about until I did this we also meet up afterwards and we turn onto you factor all that stuff because G this would have been a lot harder if she had to effective often on for any of this stuff because then I would have had to like officially factor oath codes or like social engineer phone company or like man-in-the-middle her or something or do one of the other much harder things but most people don't have to factor or stand on and so we talked about it and she will and we talked about possible managers and staff and
key factor auth and she was like do I have to use a password manager and I was like you know what maybe you don't maybe it's a factor was good enough you you decide you have the power and so also earlier in the talk I talked about these LinkedIn and tumblr password the password hashes and I was like oh I just happen to have some lying around you might be wondering but where did you actually get those thank you very much [Applause]