The Art of the Jedi Mind Trick
Show transcript [en]
doing things a little different so uh I'm one of the organizers this is Jeff man you work for table tenable has been supporting bides for many years and if you've been to any of the sessions I've narrated before tenal is a very good sponsor and when you think about security you should think about tenal and Jeff man right Jeff has 30 years experience and since this is a 30-minute presentation I'm going to turn it over to you and get started go for the Work Ready set go thanks bside San Francisco for letting me speak here today and I hope it's not just because tenable is a sponsor um it's not great so uh Jeff man is my name uh
security is my game I've been in the industry probably about 34 years really if you add it all up that's what I used to look like and you can't hardly see it but I used to have hair and it used to be long that was my passport photo um if you're interested afterwards in speaking to me getting in touch with me I can certainly share my contact information since it's mostly washed out but it's also up there at Mr Jeff man on Twitter let me jump into this uh the art of the Jedi mind trick first I'm going to explain to you hopefully in very short order why I consider myself a Jedi ma uh
master um talk about the problem that I'm discussing what I think's missing next steps and hopefully we'll have time for some Q&A so we're going to jump right into it a long time ago I saw the original Star Wars in the theaters when I was in junior high anybody with me the bartender and a couple more before they called it episode four episode four it was just Star Wars um I'm going to throw this up here and risk having Stones Throw at thrown at me I began my official career at that place and I started out there as a crypt analyst and I moved on years later into information security analyst work which got me into penetration testing back in
the early days uh back in the mid 90s when I was getting involved in cryptography this is the kind of stuff that I worked with you can't tell what it is that's a one-time pad cryptography was done on paper back in those days and we broke it with graph paper and colored pencils but the computer came along and we started automating things in terms of cryptography and we started taking things like one time pads and putting them into computer programs and using IBM PCS before they were networked so there was a little bit better level security on them um to put things in context everybody know what that is yeah when I started working at NSA it
was still a secret that we had broken the encryption of the Enigma machine that wasn't published until the made public until the late 80s why was it still a secret because there were still some countries that were using it think about it anyway I left the NSA in about 1996 and this is not a a talk about me I'm just giving the context of why I'm a Jedi master I went out into the commercial sector and started out doing pen testing which turned out to be a lot of vulnerability assessment and it was the early days we were trying to convince companies why they needed to have an a firewall if they were going to
be on the internet and things like that and and really it was the beginning of developing any time typee of sense of having a security program having any kind of policies any kind of concept of what they were trying to accomplish with security uh so there was a lot of uh education uh security program development architecture development and things like that um somewhere along the line I I fell into PCI I call it PCI Purgatory I ended up being a qsa for 10 years and luckily I was released from PCI work I was hired by tenable about 2 and a half years ago brought on as their PCI subject matter expert I do security as well cuz I had 20 years of experience
before I got into into PCI work which brings me up to today um I went around last year uh spoke at several different conf conferences user events partner events things like that for tenable and I gave a talk called the state of information security today are we getting any better um one of the things I I observed as I was going to all sorts of different conferences and I won't name them it doesn't matter but I heard a lot of really smart people giving a lot of really interesting fascinating talks but if you've noticed in the last couple years um there's a lot of breaches reported in the news there's a lot of fraud happening there was a guy
just gave a fraud talk a little while ago um the bad guys have figured out how to monetize uh you know breaking into things and and and compromising data and um you know coming from the PCI background there were s so many retail breaches in the last couple years point of sale malware and things like that I was I was doing some soul searching I'm like gee are we doing any better as an industry when uh you know things are bad breaches are still happening and you find out that the the causes are you know default settings uh default passwords never being changed weak passwords I'm like gosh that's that's how I was breaking into stuff 20 years ago so um gave this
talk about what's wrong with the industry and how we can change it but also heard a lot of people talking about problems and I thought to myself maybe part of the problem is us maybe we're not good at communicating maybe we're having a hard time getting the point across because uh you know for various reasons uh maybe we're not practiced at communicating maybe we don't get the opportunity to stand up in front of a group very often maybe we're not going in front of the board of directors very very often or the even our bosses or you know the staff meetings or whatever um so this is where I started having this idea maybe I need to talk about some of
the things that I know I've done for many years but I don't even really know what they what the techniques are that I'm doing so I tried to figure out okay what it is what is it that I do because I know how to go into a company sit down with a group of people whether they're Executives or whether they're technologists whether they administrators management techie and I can pretty uh fairly often get a good rapport going with them not always there's certainly you know hostile environments that I go into uh or have gone into but uh I I found that I was pretty good at getting the point across teaching security Concepts getting my customers to a point
of understanding they didn't always do what I thought they needed to do but I could at least make them uh more educated and give them so that they had an informed decision risk-based decision when they were deciding not to do what I thought that they needed to do or maybe we found a compromise somewhere along the line so um you know this is just in the last year or two some of the big companies and like I said this is kind of what I've been worried about but this is sort of this is a meme that was out on the Twitter's about in the last week or so has anybody seen this take a second to read it I don't read slides to
people if you read this you can take a lot of things away from it and certainly there's truth in this but when I read this I thought gee this is sort of encapsulating what I'm seeing as I go out into the community the hacker security Community to these different conferences sometimes we know what the the answer is and we know what needs to be done but if we can't communicate that I think we're just as much responsible and so you know that's my easing into this message of how do we do better at communicating so this is going to be uh like in fast some of the things the techniques the the the methodologies that I use for communicating over the
years uh uh as I'm approaching customers as I'm talking to groups and things like that um very first thing and and some of these things you've probably heard before because i' I've even heard talks on this topic in the last year or two know your audience uh when I got started in the in the pen testing business 20 years ago we didn't have Google um didn't mean there weren't search engines out there I would try to figure out if I was going into a company what you know what type of company was it who are the who who are the management who are the people I'm going to meet um find out what their background is you know what
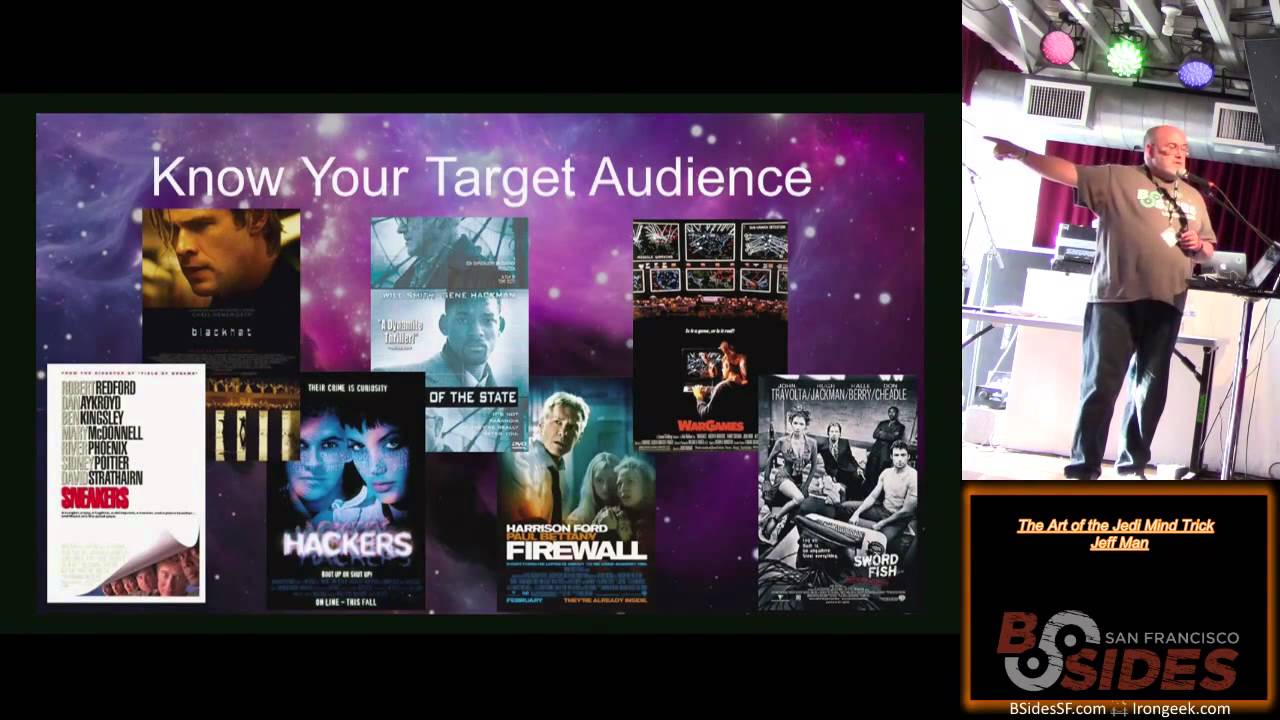
are their likes and their interests and that was you know there was a couple different reasons back then it was more tactical because like if they loved Corvettes that' be the first password I'd try when I was trying to hack their their account but also it it gives you the ability to find out where they're coming from so just as an example by show of hands uh and there's no right or wrong answer nobody's going to be mad at you or anything but uh in terms of the best hacker movie that's out there these days who thinks it's black hat raise your hand I shamed You by starting with that one Enemy of the State got one uh war
games got a few more NOS the bottom right is swordfish anyone not just because of halleberry but for the hacking elements okay firewall hackers got a few I actually watched hackers on Netflix just a couple nights ago and it it was a humorous look down memory lane sneakers yeah I think the consensus in this audience is it's sort of close between sneakers and War games um any Enemy of the State by the way is kind of my favorite because it's about where I used to work and it's fun to watch fictional movies about NSA because they're only guessing what it's really like there um there's a scene in Enemy of the State where the the Black
Limousine with the bad guy deputy director who I actually used to work for um drives into the you know the glass cubicle building down this ramp and I always chuckle because that's actually the loading dock where they used to bring the food trucks in for the cafeteria that's a secret about NSA that you never knew but anyway when when you when you ask questions like this of an audience or of a group or you get a sense of you know just in the responses what type of person they are uh everybody hates black hat what do you take away from that is information uh the difference between war games and sneakers sneakers is what kind of
introduced social engineering little bit in war games but sneakers is the big one so all everybody that likes sneakers the best I'm thinking you guys probably love social engineering that's that's that's a technique I don't know the name of it but that's a technique here's the biggest one you go in and you listen I I used to go into companies and just ask what problem are you trying to solve and I'd listen to them talk usually they had no clue and even to this day very often companies don't really know what they're trying to uh get to what their objective what their goal is by I've got to do security I know I've got to meet this
compliance standard this is this PCI thing just having a conversation about what is that you're trying to protect listening to them articulate hearing that is a clue of how to you you know you log that and then you use that as a technique later on when you're when you're trying to describe the solutions so listening is an important thing anybody tell what movie that is this is sort of a movie themed talk this ppins Field of Dreams very good um I believe very strongly and I've said for years that I'm bilingual I'm I'm able to talk Tech talk with the techies but I've also been able to talk non-technically to the non-technical folks who are usually the decision
makers in most organizations and and uh the best analogy I can use on why you need to learn to speak their language is have you ever seen somebody and maybe you've done it yourself tried to talk to either a deaf person or somebody that speaks a foreign language we tend to talk slowly and very loudly and I suggest to you if you don't hear me or speak the language that doesn't help a bit I don't care how slow you talk to me if I don't speak your language I'm not going to understand a word you're saying it's more important to speak the language of the customer I used to get this a lot with u PCI work
because I used to get called an auditor all the time and I would say I'm not an auditor I'm an assessor the PCI compliance process is an assessment not an audit but you know at the end of the day once I explain that to the customer if they wanted to call me an auditor I was an auditor I wasn't going to argue with them it's very good very important sometimes to break it down what you're trying to convey in terms of a a technical issue or what you're trying to get them to in terms of of objective to tell stories to come up with analogies my wife is really good at this I'm not um but I try um what I have found over
the years is you have to be very careful in the analogies you use you know I'm I'm a white male I tend to like to use Sports analogies I love football I love baseball basketball not everybody else does so Sports analogies don't often work sometimes they do sometimes they don't um I've been to foreign countries where I find myself using colloquialisms and and and phrases that are very familiar in the English language or the region in which I live and as I'm saying it I realize this person from wherever I am has no idea what I'm talking about because they've never heard this phrase before and of course they can have phrases too that don't mean anything to
us Americans um this is a toughy movie Big Fish good job um if you're missing the elliptic curve talk here's my one crypto slide um I am a crypto analyst by trade I am a primarily a manual cryp Crypt analyst I've done I've designed codes I've broken codes and I I can talk the elliptic curve type talk but for most people when you start talking elliptic curves and large random numbers and pseudo random and this that and the other a lot of times it goes over people's heads so I just break it down to there's something that you have that's readable text you have to do some kind of fancy math stuff combined with some kind of random which is a consider
called a key and that produces that code that usually explains it for most people and we you know the detail if you need to go into them you can go into them but for the most part Breaking it down gets the point across because many of you probably work for companies where there's business decisions that have to be made based on things like profitability and margin and revenue and things like that it's important to learn a little bit about the business this should be an easy one movie Office Space yes I'm a people person wow there's no way you're going to guess that movie would it help if I told you that's Samuel L Jackson
well that's close it's a good guess um don't assume that people are understanding what you're telling them the first time ask you know when you're explaining something to somebody ask him what did you just hear me say very often I found out they had no clue what I was saying so to regroup and try again and again don't say the same thing over again try a different approach try try a different analogy the first one didn't work try something different um the the clue is the Assumption don't assume anything this is the long kiss good night ah this the slides will be up on the website later you can see what it looked like um this was really important
especially when we were coming in doing V vulnerability assessments to companies or if you're giving them a gap assessment on this is how bad things truly are um it's a psychological thing and I learned this from uh from my parents in my childhood um don't start with the bad you know give some people some props you know well your website has some real pretty colors I like the way it's organized but you've got a few you know we found a few issues with cross-site scripting and you know explain what that means and why it's bad and then get down to the oh and by the way there was a default password there and and that caused us to you know rape
and pillage and and overrun your entire environment but you know work into it I learned this from my childhood as I said because I never got straight A's as a child and the closest I got one time I came home with like six A's and a b and the first thing my dad says was why'd you get a B in that course so I'm I'm I'm scarred from that but I've tried to take that as a life lesson into my Consulting career that's a real broad quick overview of techniques but you know the the the fundamentals there are uh good communication skills is really what we're talking about and getting the having the opportunity to practice them
um how do we move on uh who's ready for the red pill who wants the blue pill and everybody knows what this movie is the Matrix Space Balls Space Balls you fail the class um you know the message here is you know don't give up you know you've got to keep trying and even though Common Sense might tell you to walk away um you know those people are too stupid to ever understand you you know you got to keep going and in fact I I kind of think of the um the challenge of going into an environment where I need to convey and educate and teach and persuade and audience a group a company I consider it
to be more of a puzzle than a game security very often is described as a game but when you think of it as a puzzle there's a solution somewhere in there and very often there's more than one solution so keep that as a frame of reference and keep going and understand that sometimes especially if you're in a monolithic company a large company that's been setting their ways or they they they think that they've got limited budget and you know they're stretched thin and they can't invest one more thing in one more you know cool gwiz thing that you want them to do um you know keep in mind that it takes time so the analogy here is it takes time to
steer the Titanic from and this is the movie Titanic so um summarize again these are good communication skills the art of the Jedi mind trick I I believe if you have information that you need to convey to another person to another grp group you need to break it down in such a way that they understand because security is really reasonable at the end of the day in most cases and logical arguments logical rationale reasoning can be given to people and they should be able to draw the same logical conclusion that you have without the emotion without the excitement without the the pizzazz and the technical details just break it down into language that they can
understand get a lot of feed back from them in terms of listening to them and and and hearing you know what their challenges are and and being able to modify the solution I I my favorite thing was to always offer three solutions and there was the you know do nothing approach or the bare minimum there was the ultra high level you know you have all the money and the time and the resources in the world you could do this or there's some middle ground and of course where I wanted them was in the Middle Ground they'd obviously rule out the one end they'd obviously rule out the higher end and then we talk about that middle ground and there was usually
some negotiation there as well but when they walked away they felt like they'd made an informed decision I felt better CU I felt that like they'd made an informed decision they weren't blindly walking off exposing themsel they knew what the risks were but it was a calculated risk it was a risk that they were willing to take on and that also gave them direction for what they needed to do in terms of security moving forward which was maybe increased monitoring increased awareness aess you know if you've closed nine out of 10 holes but you can't close that 10th hole watch it really carefully to make sure nothing's coming through that hole at the end of the day
movie very good any questions comments push back feedback yes I was thinking about your talk some of it was like you were going in as a consultant to talk to y my reality in a right everybody knows everybody already know if you had special advice on that side uh go to get a new job where they don't know you yet no I realize that's a limitation because my experience has been you know I get to I get to come in as the consultant the expert and I used to joke with uh it was actually a technique I used to use to win over the security guys the it guys i' say hey guys what do
you need especially for the PCI CU you know your environment better you know what you need if I slap PCI on it guess what you'll get it and I'll be your friends I used to joke that I had this magic Cape that I could just get things I'm experiencing the challenges of working for a company now trying to educate and shift them into a different directions and it is a lot harder um I think and I've experienced the you know the looks of oh here he comes again and they turn the other way um I I think it's more slow more methodical you have to be more patient and and kind of pick your battles and and and and try to make
small wins and and again more it's I think it's more important than ever to try to give the information in such a way where that your management can kind of make the logical conclusion and try not to say and I saw this in an email just a couple days ago within table they they said it very FL in a flowery manner but it was basically I told you so try not to do that there's a question down here no was never it was a never mind I answer questions before they're even asked that is the art of the Jedi mind trick um if you're really super interested this is really a a um U um a
presentation that just try to peque your interest I'm going to be at Circle cityon in June giving a training course where we explore some of these things that I've talked about in the last 15 20 minutes but try to actually give you guys the opportunity to to practice them the opportunity to speak the opportunity to interact which I think sometimes we don't get and I'm hoping it's a theory that that'll help all of us do better in our jobs
yes all all of them um I mean really sometimes it's the more basic concepts like why you know why should everybody in the company have a strong password and change it and not use the same password that they're using on 20 Accounts at home you know just you know th those are the basics that we're still companies are still falling down over so I feel like we haven't tackled the fundamentals yet so I'd start there yes sir that's a b more from your experience how what's been your success rate or favor rate def quantitative or qualitative risk management wow um 100% failure no probably 5050 um but again some some organizations want the quantitative some organizations want the
qualitative to me it's more the trick of knowing what they want to hear and knowing what's you know what they're going to respond to what's what's the triggers um and you know that to me it takes practice it and it it's it's learning how to pick up on the cues which again is I think it's a technique that I've learned that I hope of I've tried to identify them but there's probably more out there as well yes I think if I put it just in terms of how can I best support business cheap they're much more receptive do this yeah that's very true I mean it's hard to push security as you know this is a way to increase profit
which is what they want hear or cut expenses which is what they want to hear um but to have a responsible um meaningful reasonable message for this is why it's NE a necessary investment and this is you know without doing too much fud this is the bad that could happen um but you know again there's a balance in there so to me it's all being reactionary yes I which activ hostile management actively hostile actively hostile management um probably regroup and just try to find uh a sympathetic ear somewhere else in management and sort of backd door them um you know build allies build build enough people that are getting the picture and find the influencers I used to walk into
companies and try to find out who is the person in charge very often the person really ran the organization was not the boss it was the boss's admin so I would like win win her over him him or her over sorry I don't mean to be sexist and uh it was often a woman frankly but you know they're the ones that that had the real power anyway do I have that long or are we done we're done sorry thank you very much everyone





