IPv6 IS a Security Defense - How not to get it wrong
Show transcript [en]
hi everybody in the room and you at home my name is Joe Klein I am a yes hacker and we're gonna talk about this because um people are getting confused about really what this means I've got lots of certifications I'm actually a fellow for the ipv6 forum have been for six years and have been a a into the ipv6 community now for 16 I think 16 years may be doing security research in this domain helping write standards designing products designing defenses and attacks just primarily looking at this from many different views this presentation oh yes I'm also CTO of disrupt six which would create ipv6 specific products and services security researcher and a trainer I have a new
set of training coming up in February which is a four day I only know networking to here's how to hack or do to defend ipv6 only environments which is pretty fun it's only taken an additional year for me to write it because I have a lot of laughs as someone to write and then there's my contact if you want to add me to your Twitter stream there's my Twitter by the way so I spoke at Bogota when ipv6 security a month ago and I became this was I consider now my blue period and they informed me that I was definitely a hacker so with that I like the 1960 version of hacker okay I explore the details of programmable
systems and how to stretch their capabilities okay and then this was also good I eat EF standards body you know intimate intimate understanding it's kind of interesting of internal workings of systems computers networks okay it was until 1985 where that definition of hacker changed from somebody that would be considered an inventor just someone's considered a criminal so I just want to mention that I usually preface this particular talk on that so sorry this is the high level stuff community computing has driven prices down for every generation we've actually brought on new protocols new systems new applications new concepts we have this growth curve that doesn't look like it's gonna stop at least maybe 2030 2040 based on that least current physics
current understanding current other things so this is gonna continue for a while which means if you're in the information security domain woohoo we're gonna still have jobs okay and yes there are now more devices then there are people okay how many devices do you have on you I have I have five okay at my home I have herds and herds of little things okay maybe I'm abnormal you know maybe I should be worrying about you know Arnold visit but this is an understanding that we still have a population increase but we're also seeing new systems they're actually supporting individuals in healthcare in building controls things that actually improve hopefully our lives so this is the whole plethora of Internet of Things
ok what we've been focusing on for information security kissed or eclis has only been the pink area okay we've kind of not done any of this and a lot of these are systems matter of fact I just in an assessment against a logistics company not patched for 12 years running out of date this no passwords RF was open blah-blah-blah-blah-blah okay is a company actually designs and builds this replicates this every month someplace in the country so crazy so there's an opportunity from a security standpoint to look at all this okay Internet the historic internet growth you notice 1970 there was actually a day where everybody had to go from the old protocol turn their computers off reboot them with the new
software and go to IP v4 guess what we couldn't do that with ipv6 something about six billion computers we just can't upload and patch them all at the same time if they anybody would actually allow us to patch okay so we saw a growth but during that growth because we started seeing extreme growth we had to find a whole bunch of new protocols and changes we had to add NAT NAT is bad it really is not a security product we'd have RFC 1918 to support NAT we had to have classless classless classful classless yes center blocks DHCP and then we had to actually add and I it was funny at one point web servers only ran
on a single IP address and after the study and from IETF internet Engineering Task Force who writes the protocols for the internet once they made their announcement and 2019 93 we started redesigning Apache which by the way you know how to patchy stood for it was a patch II configuration of the NCSA open-source code so that's where patchy came from you didn't know that which i think is funny so we helped design it to create virtual servers because at one point one server per IP address now with web services we have many devices using other techniques on one IP address which by the way adds confusion and makes it harder for us for security and that I
actually have an hour presentation on that don't have the time to talk about that so this is today's security environment okay these are like let's see Nats yeah okay and bridges and gateways and you know this is the Commons because it's all dirty and everything so security wasn't built into ipv4 and by the way helmet the addresses the address assignment based on Vint Cerf father of the Internet he said well you know we're gonna use a 32-bit number and the world's only gonna need because there's less than 200 countries let's say we're gonna have to in our countries and each country is going to have a network for their governments and a network for the
commercial side awesome now we know how big of an address space we had and that's how the ipv4 infrastructure was actually scoped okay and because of that a lot of changes had to take place that that at one point caused routers to have problems and things like that so we've been working since 94 to extend the life of ipv4 until we can come up with some kind of replacement sadly a lot of the aging infrastructure still sits out there I found a router that's 15 years old last week when I was looking at it that had a very very very old version of an operating system on it very bad we've also lost our end-to-end trust because
we have Nats and CD ends and we have all these other middle box technologies each of those middle boxes actually take us one one level away from being able to trust a specific machine or specific individual in your early IP before we had a book which you basically open up ago I need to go find this here's the data that's here and here's the IP address and here's the administrator awesome ok it was a text file that we would print but you know the other problem we have is negative externalities people are unwilling to fix their infrastructures if it doesn't help them directly they directly will not provide a certificate on their system unless they can see
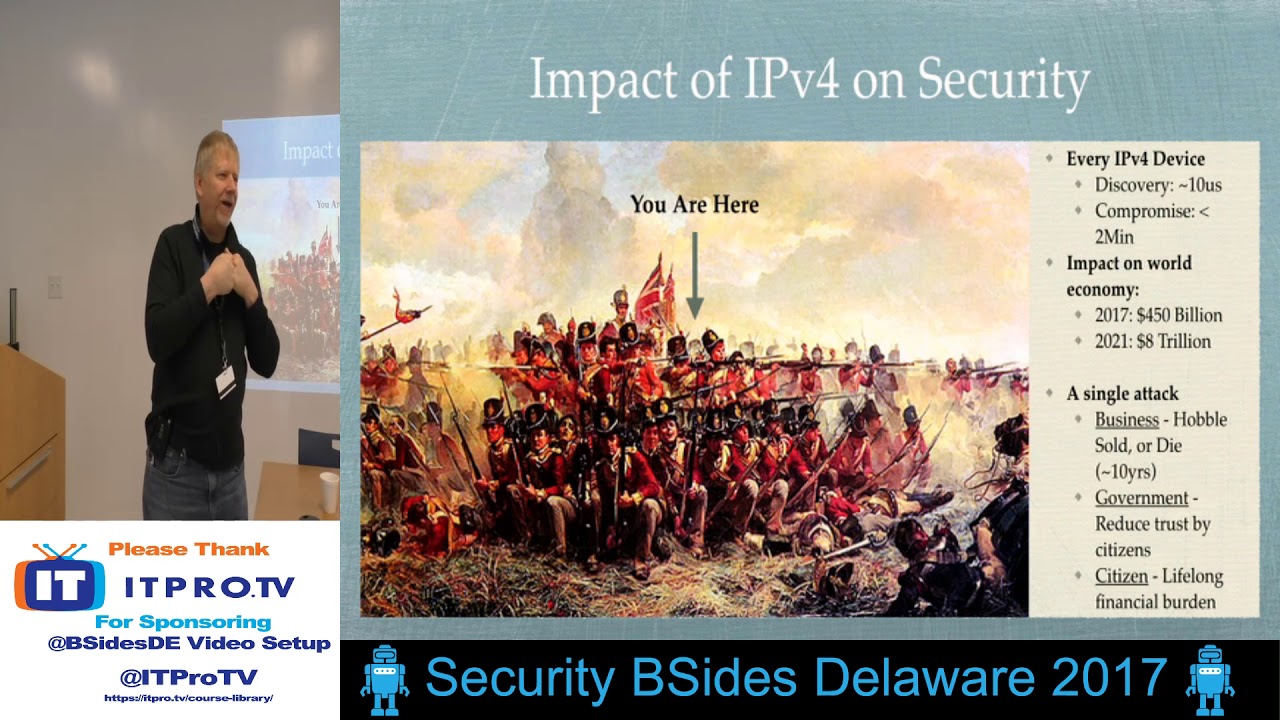
personal benefit not benefit to their customers they won't support DNS SEC because well it's gonna cost them time and effort therefore if anybody gets you know redirected to somebody else's system servers VPNs not a big deal same thing with proxy same thing with a lot of Technology so basically we have this mess on our hands with ipv4 we have a chance to change things ok this is the war we're in yeah they're coming from all directions and we're all standing in line we have to be close because there's so few ipv4 addresses so let's talk about how fast we can scan six minutes the whole internet do you feel comfortable now ok so if you put a
system on the Internet in the next six minutes somebody will scan you actually multiple peoples can you which means it's yet speed for discovery yeah microseconds compromises on systems that have been detected for a specific thing or about two minutes this is a study I did four years ago makes me feel really comfortable and warm and fuzzy plugging anything into the ipv4 infrastructure the impact of cyber crime on the industry on the world today is 2017 was about 450 billion dollars and the a single attack and I was talking to the group yesterday was that businesses here either hobbled sold or died within 10 years after a major compromise we discussed specific companies that in the last five
years have been found to be compromised and then we're sold off for pennies on the dollar okay or going out of business or close three-quarters of their stores or whatever governments if the government is hacked we lose their data that reduces our trust right and lastly we have lifelong burdens when our identities are stolen so that's a real problem so yes you are here yeah that right there so FRA pv6 everybody saying nobody uses ipv6 okay in the world and this date right here is interesting the 2012 is world internet day this is when we actually turned it on before this is when crazy people like me spend our time watching packets move back and forth and
doing both fun and evil things to it okay starting June 6 a 26-6 I anyway 2012 we started seeing growth if you noticed the world is already at almost 21% as of today and everybody says but what about the US what do you think could we call that 40% that's pretty significant so how many you're securing your ipv6 infrastructures 100% of your technology supports ipv6 at least your host based systems and your servers but not so much your security products and we will go into detail about that but it's a little bit disconcerting so you have one or two choices by the way I love this picture this just makes me laugh so comparison deployed in 1970 where we actually
turned all the stuff off and a return to back on it was experimental for ipv6 since 96 and actually gave a presentation in 96 about ipv6 which is pretty funny maximum devices are 2.4 time times tend to be well I didn't put that up there that's funny the term is 240 undecillion so for your interest you can look that up it was commercialized and 1990 ipv6 win world on 2012 you may not be aware of this but last year the internet Engineering Task Force has made a commitment not to make any changes to any protocol that runs across ipv4 only that's a risk to anybody running only ipv4 okay so if a change if they find a
major fall in something they can patch it but they it won't become a standard to ensure that we have consistency of communications that's that's an interesting thing the other thing is there's already an end-of-life chosen this is the initial 20 22 Wow we're gonna be really busy upgrading stuff are we and yes this makes me laugh one year at major conference I security conference I put together a bunch of these and printed them and I tested almost 200 companies yeah supposedly supported ipv6 and everyone except for for receive my sticker of support which is fun the other ones received that one a current estimated life shelf-life of ipv6 an underlying protocol is 2062 20100 so an depending on a bunch
of other things there's technology for the galactic internet and planetary internet right now there's protocols for that it's it's pretty interesting stuff so you need a unique addresses for to connect devices you really do sir yes
uh yeah I you can go to the NIST standard there's a NIST standard for testing ipv6 products I when I rent went around made sure the interfaces worked I made sure the administration worked and I made sure that if I gave it a few packets it could detect it and within 10 minutes I could find a product actually failed so it was it was pretty interesting so anyway so this came out from Ken gear if you haven't seen him he's a great presenter he I'm very impressed with the man as far as presentation skills someday I'll be that good he basically did while he was at in a research position he did an analysis against how do we fix cyber crime and
cyber threats so he approached it from the technical he approached it from the military the political military which we keep on hearing people talk about it and the political technical things like you know let's create cyber deterrence we keep on hearing that we have a cyber arms race we use art of war for us on sue please go out and pull this paper and read it it's fascinating based on both game theory and his particular process to show what's gonna work what's not gonna work and some of these things are gonna work or that aren't gonna work are gonna actually end up making the internet and operations using the Internet even worse so just want to mention that but he
actually had a call-out based on two years worth of studying on this dad ipv6 with good crypto provides end-to-end trust therefore there's a better way of providing a more trusted infrastructure so you guys have heard of the kill chain no Kay no kill chains here this is the survivability model for resilience I wouldn't mention this because I'm spending a lot of time if you see other presentations I've given over the last year I'm working on a survivability model called anti fragile but I'm trying to put this in context to the discussion we're gonna have on ipv6 the closer to this side that we can catch an attacker the least expensive it is on the organization the further we get to here
this is where the boom starts this is where the big money starts for a lot of people and that's why a lot of people a lot of organizations are focused on trying to fix this but if you can get ahead of the game it's very good the other side is that we're win Swart al who wrote a book called time-based security discuss is from an analogue standpoint that we have to basically have protection has to be greater than the ability for us to detect and respond today most of our technologies assume that we can detect and respond think about your your device that's gathering your logs how fast does it go from the sensor to the sim and somebody either
automatically or gets in the way to do a response to be able to fix that problem that could be seconds minutes or hours or days or weeks or months right maybe years depending on the company you're at so the faster we can respond here the more secure we have there is a new book coming out analog security which will discuss this including a whole set of mathematical formulas to actually start defining or creating a start to defining a mathematical model of what security and assurance looks like and I'm really excited I've been part of that project so if we're moving to ipv6 the first thing we have to do is we really have to move we'd love to save
move to ipv6-only right away you really can't every organisation it has things went bad real quickly mostly because you have a lot of hidden ipv4 Mis installed both in your architecture your applications the way we design our database our management systems our security systems our sock or NOC our management infrastructure funding everything else is is focused on it so we typically have a first step to go to dual-stack so the first thing you have to think about is the mindset okay these are only a couple if you're interested you can go to a website called ipv6 bingo and it will generate a bingo card for denial and then it then if you click on the link it'll actually
give you the science and all references to all the current issues one is that it won't have any impact on batteries there was a study from Nokia that we can reduce our battery or we can increase our battery life anywhere between six and 20-some percent by going to ipv6 only and getting away from ipv4 because for every application I have to make a connection I have to create a NAT open a firewall someplace I have to open on my side and I happen to have to open on their side and then for every CDN and everything else along the way I have to maintain state on all of that for every application I run so your phone is
running how many applications has to make so many connections it actually maintains state so that you can actually communicate so v6 data's sent there's no NAT there's no state required it comes back like is good okay because we're trying to take state away from the network infrastructure and put it on the hosts they're a little bit better for dealing with state but yeah this these are fun no business value want to mention this there's anybody in datacenters by do data centers I'll mention this LinkedIn and Facebook have said that they once they move to an ipv6 only environment they say anywhere from nine to twenty plus percent operational and staffing and now they've created new models
they've actually reduced programming costs and lots of other things so this is a big deal so that's just one example so I just want to mention that there's some interesting things the other thing is if you're gonna get people trained don't just train your network engineers make sure your helpdesk how are they gonna answer you know if they type you know NAT stat or whatever how are they gonna represent to the customer what that means and how to troubleshoot that stuff the defenders if you're doing defense you should actually have a real good handle in ipv6 because there's some really cool features I'm going to talk about a couple of them and your programmers have to know how to write it
because programmers we have today some of them are using old libraries that don't support ipv6 and have flaws in them one of the challenges that we have today is that because of that long build-up because we didn't want to restart the internet the we had four generations of ipv6 protocols and standards depending on the company that you've worked with to buy products and services even today you could have any of those generational issues in it the newest one actually has a lot of fixes for security and operational issues the older ones don't so you'll find code and products that have made your falls in it so I want to mention that because this is this is
what I've been trying to crusade for to get fixed for the last umpteen years the other thing is problems exist when you migrate at layer 2 through layer 7 we found Ethernet cards that don't support ipv6 so therefore if it runs data real fast and they offload it to the ethernet card it sees ipv6 it uses a seat for you there for now processing and everything else slows down and those are the kind of little tidbits that we found also the management layer because the management layer needs to know that you're trying to do something that's good for the business procurement I mentioned this yesterday something called the S dock basically a procurement document requiring organizations to buy products
that have security and specific sets of compliance if you go to nist ipv6 s dock you'll get all the definitions and references back to the ansi documents without paying for the ansi documents so that you can learn how to use this in your procurement policy interesting organizations that have used this process have improved security because every new procurement that says i have a processor in it and i have a network interface must follow this standard whether it's a there has to be a patch i have to be a to do real authentication there has to be encryption whatever it is that your standard requires has actually saved money over time for companies have done that and i'm going
to mention that because the ipv6 community started that four years ago when we've had some real successes on not only ipv6 compatibility and but also security of improvement of devices over time ok if we're running dual-stack we had this crazy problem it's early in the deployment of ipv6 we thought about wow we're gonna have a oceans of ipv6 and islands of IP v of ipv4 and islands of ipv6 and we had to create all these protocols so everything talked so we started creating lots of protocols I didn't include them all because it would go off and it would be too small and you would be to read it and not really useful on the other side now we have
protocols to deal with islands of ipv4 across ipv6 oceans ok so these things cause real havoc one specific item I want to mention so when do you say thank the first published vulnerability and attack using ipv6 was actually the first published because they had logging on was 2001 ok that's a long time ago ok if you go to some of my previous presentations over the last 12 years or whatever 15 years I keep a timeline of all those compromises and what caused what caused them what was the root cause what was could they detect it could they not detect it things like that so these are a real headache for us when we're in an ipv4 ipv6 environment the other thing
these layers can be deep we have found we found GRE with ipv4 the ipv6 embedded in it as ways of getting around IDS's intrusion detection systems okay so this impacts us from a security standpoint we have to be able to detect us and I've running dual-stack is expensive so the surface areas increase its doubled yes it the tunnels are a real headache to deal with a lot of applications and security controls are inconsistent and a bunch of products for about eight years I spent a lot of time trying to make sure that the firewalls worked and in some cases the firewalls for ipv4 would be turned on and it would turn off the ipv6 firewall hi Charlie
I've gave you six five the ipv4 firewall and some of those who are commercial products some of those were consumer products so you have to look at the secure the application security for anything that comes across your network also the increasing complexity of DNS because now if I'm doing passive DNS monitoring I can have a DNS go through TCP or UDP across ipv4 or ipv6 looking for a or quad a records C in complexity or concern here how are you going to monitor that and associate it with each request to see if it's a C and C or not a tunnel okay this this makes it rather complex also budget which is really the largest risk ipv6 when you're running
ipv4 and ipv6 together operationally and it increases it some people say it increases the operational cost by third a lot of organizations are trying to move to ipv6 very quickly anybody heard of LinkedIn they're completely internally 99% ipv6 only in their data centers and internally same thing with Facebook they love it it's it's reduced a lot of complexity they have which is pretty neat and the organizations that are using internal we'll talk about that our finally I PU six is pretty cold ok security analysis I still find applications don't log the address right you have 128 bits and a lot of applications go I only do 32 bits so I'm gonna whack out off the front or I'm gonna whack off the
back and this is what goes to your sim there are certain addresses that then look at like and map to specific nation states that aren't really attacking us via ipv6 so that's a concern the other thing is a lot of storage and analytics engines haven't upgraded their back-end so they're representing the ipv6 address as a string how fast is it how fast is a binary compared to a string very fast a lot of products haven't upgraded that therefore if you're doing threat intelligence you're doing sock work you're trying to look for some address that matches something or close to it this has become a real problem in socks also mapping ipv4 to ipv6 if I'm being
attacked by a p4 person and an ipv6 person are they the same are they different should you know that that's again that's some of the complexity that we have today in a dual stack environment so ENGO yes ipv6 and increase the pain make them cry make them painful make them have to work harder okay so I mentioned five items that we can use to make it painful I don't have the time to go into everyone because the complexity of it and the time would would basically be until tomorrow the next day depending on how much detail you want so I'm just going to go over five very quickly and I'm going to tell you why these are
important okay first denied apology enumeration when somebody does a traceroute and depending on the traceroute tool I can only define the routers but I can check for firewalls I can check for IPS is low balancers and other hidden networks depending on which version of of traceroute I use so that gives them context on which networks to go after what's available on the network in some cases somebody will have a firewall which is which they can trace route to and trace route through so the actions say oh this is the firewall okay I know where that is and oh by the way now that I do a reverse look-up on it I know it's a Cisco or I know it's a Juniper or I
know it's a whatever box it is so this basically bleeds so much information excuse me for information and yes I think that's a funny picture with the kid here and the ones hiding in the stack so how do we implement that in ipv6 we have a separate set of addresses it's called a linked scoped address it means that if I'm on the same segment I have a unique address you'll see this when you pull up your computer's you'll see an fe80 and some additional bits here some additional characters here hexadecimal by having this we can take this interface when we're routing from point to point and say we're gonna use this is just an example you wouldn't use one or
two you would use a random number a large random number I'm gonna I'm gonna route from here to here this guy would actually have that address as a default route this guy would have that addresses default route now women attacker using trace route I would see this this disappears it's at layer two it's now not from a network standpoint it looks like it's at layer two so I can't get a decrement and then I would hit that if I do the same thing here I can again manage it so when I do a trace route to here all I get is that interface and that interface pretty neat huh here's the other thing the best choice
of managing these systems would be to be out of band okay the second choice is we have another special set of addresses called a unique local address unique local address allows you to assign some random set of bits here and it's part of the RFC and you can look this up and they actually educate you on how to use this so your internal administrators so I'm walking around a lot your internal administrators can have access from internal to each of the interfaces on an address that they can still connect to and do traces with okay and they can apply control here to make sure that there's no X fill of the EFI the unique local addresses external okay
so essentially this allows you to hide Recology and still provide management for each of these systems which is pretty cool okay and these are not global addresses so that's nice see next fun thing so make sense okay second thing let me tell you a story about attackers attackers will choose passive especially free services first and then paid for services and some of these paid for services are extremely expensive but you have to know they exist we identified over 100 so far that we can classify on v4 that are doing scans and then selling that information there's interesting they can do active but then they have a cut out which means they have their own VPNs they have their
own proxies they're using tours so they basically have a cut out network they can do it for free or there's paid service that have low medium and high anonymity okay pervy four so that's interesting and then the last thing they'll always choose is the direct connection that's we don't want to do that so based on a study that we performed we were able to classify these into the type of attacks and then we were able to figure out where that knowledge came from we found that inbound connections the DNS queries because we were running our own authority of DNS we're identifying that some of these people got this information from the DNS server which is
inbound services HTTP HTTP SSH SQL we said we had telnet we didn't we said we had a bunch of other things but we started seeing them show up over here we also have outbound this is an interesting one if you make a connection at one point last year to NTP another company that sells these products would have scanned your networks because you made a request to the public NTP creepy huh same thing with patched servers we're seeing patched servers actually scan you back after you make a connection within a few minutes we also have DNS servers depending on whose DNS servers pop and IMAP servers do the same thing we found we have a whole list of these it would
be little tiny characters also management servers if you're on the cloud how do you know if somebody's not trying to hack the management server which actually impacts you okay or are you using SSH when you're calling in or telnet to manage the server okay it's on the same addresses these day now the attacker can get contacts for for free or for pay we also have search engines search engines are running things all the time are they claimed to be search engines these guys are providing information out so I'm an attacker I have this choice and oh yeah and monitoring how do you monitor your system do you ping it you do a query against the system remotely
do you log into the system and have you send logs I mean those are all things you have to ask a question these also provide indication we we put up a server one place and we kept on transmitting data and these two except for regular scanning this other system wasn't known and we only allowed a certain type of connection we provided some false information we found that the connection between here and here somebody was listening on a tap and then started scanning our monitoring system - okay that's the reality of today so they can choose to do this the process is I scan this small address space in six minutes I can do a DNS lookup for it
which then provides that IP and I can scan for it or it can take this address do a reverse lookup get this information get other information and go through this loop a couple times to find everything for a company okay do you feel safe now so FRA pv6 let's talk about the address space that large enough 19 + 19 19 zeros it's a pretty large address space when you have more bits to work with in the address space there's ingeniously fun things you can do okay to brute force at address when I'm across the router years or tens of years or hundreds of years depending on how you talk - okay that's good there are several techniques that I teach is
actually several others there's a smart one which is which is pretty funny because people put people put web servers on on an address and they call it a : 80 and it doesn't like hide anything right or they call it dead beef or they call it something that they can remember easily because they don't want to put something in the DNS server that they have access to or their internal DNS server so that's pretty fun the other thing is we're seeing brute force of DNS do you run your own DNS you know somebody's not doing a DNS brute force against you you get reports from your DNS provider authoritative DNS server provider anybody anybody Bueller
and also reverse DNS your address space your your the address space that your internet service provider or cloud provider or service provider provides you is that being enumerated okay before these are all done and everybody ignores them for v6 these are strong indicators that somebody's interested in either something on your network or they're going after your domain okay the more interesting part is they have to scan from here to here in this large field and I have one nugget of gold in several different locations let me show you where they are okay this confuses the heck out of people because to get service from these things I would have to tell you where they are and again that's what we do
through DNS let's talk about how we recommend mitigating it for ipv6 has anybody heard of a privacy address for ipv6 okay that's an address that will change the actual address the last 64 bits of the address on a regular basis and you can schedule that on a regular basis so is an example say that you're going out and doing an NTP once an hour what if you were to change it so that the address changes every half-hour that looks like two addresses are coming to them right so from a signaling standpoint when you change the address space you've changed your address what happens if they come at you you're no longer at that address for scanning awesome that's a signal
that somebody's actually looking at your site same thing with DNS pop IMAP patching anything that's actually outbound
service monitoring and performance guess what ipv6 allows us to take a single system and put depending on the operating system up to a thousand 24 dresses that's have fun with that why because the attacker today assumes that all services are on the same address so if I have 65 535 ports times that defined a single active device on that network how probable is it highly improbable yeah this actually changes the game so as an example I can change the IP address from the llao llao temporary address exists and throttle through I can take change a create a static address just for monitoring so I can check for up to updates I can have another one for managing ssh isn't that
what people do is a scan something they see a web server and they scan for ssh to see if they can prove for sit haha now you don't have to ever put SSH on a high port Wow search engines with DNS we could direct it to a specific IP address to see if it truly is the search engine from Google or whatever interesting albe out HTTP we have a load balancer read balancing it to that how about HTTP we can have it on a different address how about my SQL Server that we don't want anybody to enumerate and if we see somebody in numerating that's a high indication that something either was leaked or somebody's after your
organization pretty cool by the way this works real well I have servers that have been up for four years and except for the outbound initiation on the privacy address which I get pained all the time just letting it do patches and things like that I get no scanning on this okay so from the attackers view they're looking for the little gold they're in the wrong place it's pretty cool so because we have the non allocation space we can actually detect once we track that we can detect when I made that connection outbound and associate it with the IP address to figure out who I was communicating with to identify who's actually scanning me I mean does that make sense it's it's
really simple we now have new options because of it and by the way we do see bots from time to time trying to find something in here but again that gives us early indication that there's a bot running around we have different options that we can then make we can block the IP Blake block the cider block for them we can block the packet based on how the packets form oh we can entice them into a honeypot okay so again we have new new strategies to identify bad actors and BOTS yeah
yes that's why we're using a special set of packet identifier x' and cider blocks and a combination of two were allowing us to identify specific actors and that's been really fun thank you guys you're making it interesting okay something else everybody like malware you like it C and C's aren't they fun okay well so it's been a while since I moved a specific well-known client to an ipv6 only environment that was getting attacked all the time by different nation states some of the things that we learned is that one an ipv6 only ipv4 is an indication of a C&C or bad application implemented or a plug-in that's flawed or or or or actually a web RTC socket
that's miss configured but that's another issue this is a really strong indicator very quickly how fast can I see this well as soon as I see it go to my black hole my DNS black hole and I see a DNS and I'm walking at those logs I can make a determination based on the IP address of internally oh my god it doesn't like me anymore I just so I'll tell you the stories this way so very quickly if you're you're monitoring the DNS service from a logging standpoint if you see a quality or if you see a a record query or any type of ipv4 query very quickly can determine that somebody uses put now
we're on there they're doing C&C they're trying to do lateral movement or whatever this is sobbed the whole class a problem for most of the people trying to mitigate heavy attack oh and why is this what do the attackers in bed they primarily embed an ipv4 address or they do a DNS query across ipv4 to find the C&C that makes sense this has been very very successful with a bunch of my clients that we've moved for certain areas specifically to ipv4 oh by the way those have actually had p6 we turn we turn it off what we do is we go through and we do an assessment against that that particular air that particular group of networks we turn all the
services off we identify anything that's ipv4 or we turn it off we update it there's several other things we can do we can do code audits and stuff like that for it there's some tools for that that are quick so we can actually have it fixed if it's an internal if it's an external we can make recommendations for updating but once you have that it's a v6 clean environment any v4 shows tarnishment
as an example say that they're being fished there they're pulling ipv6-only traffic from the mail server so if they're being fished we're gonna see only an ipv4 connection okay that's typical they'll bill turn on the ipv6 oh by the way we do leave ipv4 on on purpose just to detect us we don't turn it off on the interface and the reason we do that is because people use some of those ipv4 to ipv6 transition techniques like Tara dough some of them will embed that code in their malware and that also gives us a strong indication so these are all just indicator which we've been able to find very successful and very quickly detection is a few milliseconds for the
log to process and for it to be shoved into something to detect it which is pretty fun pretty cool okay black cat find the black catch when you're setting up a new device on the Internet today how many people set up a new device and you get hammered and then all of a sudden you five it's you find that the system is compromised I'm so tired of that so what you do is is anybody heard of DNS or pcs think about it like it shares information based on the IP addresses that you allow to share with so if your internal addresses are a and the rest of the world is B through Z and lots of other characters you can create
a firewall then only allows when a source address within your organization makes a request this could even be just the engineering group makes a request they can only oh they're the only ones that can do the DNS query okay that's pretty cool what that does that provides logging with the sources the destination and it also gives you indicators that if you see that any of this information has been leaked besides from these sources dresses you very quickly can identify some kind of compromise or some kind of leak okay that's pretty cool so basically you base it on the source of who's making the dns query so you can block certain countries certain organizations things like that
v6 we had the ability to block whole continents okay pretty cool because there's a specific network block assigned to so different continents so if I have internal but not external all that stuff we talked about enumeration discovery gets kicked in play again this this works really well again I have servers that have been up for years for years I have really good time to see if anybody looks at them nobody scanning them it's awesome would you agree that these all call it increase the cost to the attacker okay yeah pretty quantifiably so yes this is this is what pace from my hotel room this is what we do basically a threat intelligence indicators compromised custom IDs and other weird things if
you're interested and then we do a bunch of services for readiness assessment testing security testing sock integration and attack of Defense and that's all I mentioned about that slide ok you have any questions did that did that make sense I try to make it as simple as possible to roll the different features like I said there's lots of other features that are a little bit more complex require some coding things like that things like moving networks for DDoS protection where we can integrate a signal that all the addresses on all your servers change addresses to a different address block so they're basically ddossing you here but now you're here
it's a DNS lookup it's a DNS lookup all the yeah all the bots don't do DNS lookups they use IP addresses the ones do DNS they usually pull it back once or you can actually identify the duck the bots doing that type of DNS query so but that's that's one of the fun things so any questions comments did you get enough swag okay have a great day