Josh Sokol: Measuring Cybersecurity Maturity with the NIST CSF
Show transcript [en]
[Music]
[Music] um so hey uh besides calgary i'm josh sokol i'm actually coming to you live from uh round rock texas just north of austin in the u.s um it's a pleasure to be here this is actually my second year presenting to besides calgary i started off last year and i was supposed to come there in person i was really looking forward to joining you all and then covet happened and now cove it's still happening so um my hope is that i can submit a talk and be accepted again next year and then i can actually be there in person um but in the meantime you know hopefully the the video will do um let's see here so our our talk today
is measuring cyber security maturity um i mentioned i'm josh i'm a cissp i've been running you know security teams for a long time actually retired from national instruments um about a year and a half ago something like that um in order to focus full-time on simple risk consume force is kind of my baby i've been working on since uh 2013 basically in march of 2013 i actually presented at the b-sides austin conference and i talked about risk management and everything that i learned and the thing that i figured out is that there wasn't really a good tool uh to do it out there certainly not a good free one that didn't cost me half a
million dollars and so i kind of created my own i've been involved with owasp for a very long time i was a former board member for the national foundation um i ran the oas austin chapter for a long time i even founded a conference uh here in austin called last con and yeah kind of areas of expertise there especially around uh grc as well as secure application development lifecycle um by the way so i have my kind of slides up here in front of me uh and i'm not able to see the stuff that you guys are are popping into chat um so i'll try and kind of flop back and forth so that i can read questions as we go but please
forgive me if i'm not answering them right away um in terms of what we're going to cover today uh what's organizational subsecurity maturity how to create an effective road map we'll talk about assessing current and desired maturity we'll talk about risk and then the road map piece you know how do we get from point a to point b so a little bit of background here uh i originally gave this talk with a coworker his name is alex bolamini and he ran the it compliance team at national instruments and uh this was the same time that i was wearing the security team at national instruments and we found out that we had a lot in common there were a lot of kind of
parallels between what he was doing and what i was doing um for me on the security side i was defying technical controls for the organization i and i was doing enforcement of these controls whereas for him he was really looking on the compliance side how do we define policies guidelines standards and procedures and how do we validate that we are in compliance with the defined requirements whatever those may be and so we were asked by our manager to assess our organization cyber security maturity and to create a roadmap for ni's uh information security program uh we had access to gartner and gartner is awesome it's really expensive um but they do have a really good
maturity assessment that you can take and it gives you this nice spider chart of where you sit uh but it's really high level advice it's like you should uh have somebody in charge of security well duh right and uh you'll say like you should have an information security policy you're like yeah i knew that um it doesn't really give you a road map of how do i get from point a to point b and so that's kind of where alex and i started on this journey um so before we get too far into here we have to kind of understand what organizational cyber security maturity is uh and organizational cybersecurity maturity really speaks to how effective the
people the processes and technology are at making cybersecurity risk regardless of what that might be and you have kind of two types of controls so you got lots of types of controls but you know controls kind of fall into one of two categories either you have mature controls or you have immature controls and sometimes you have stuff in between immature controls are things that uh management shouldn't be placing a lot of confidence in uh because they're immature whereas mature obviously because they're more mature controls you can place more confidence in them and whatnot so a quick example is if you had an immature control that might be an endpoint that has basic password protection there's not a lot there uh to
protect the the soft squishy stuff on the inside um but a more mature control example might be that same endpoint but now we're adding full disk encryption we're doing complex password requirements we're adding in multi-factor authentication you get the idea right we're adding in all these different things to mature this control and turning that from you know kind of a soft squishy center into more of like the m m model into more of a jawbreaker mod you know something a little bit more solid so how do we create the roadmap um well if you look at road map uh generally a road map says you start here uh you're gonna end up here and then the map is
just you know how do we get from point a to point b right how are we traversing this thing and there's lots of different paths as you go along but everything from point a to point b is essentially your road map so the first piece we said is we have to assess where we are and in order to do that we need to kind of identify the control framework then bias what is that we're looking to assess and there's tons of control frameworks out there talk a little bit about that on my next slide um but you know understand are we trying to protect our customers privacy data are we looking at securing credit cards are we
creating some super duper top secret system each one of these different things each one of these different kind of environments uh are going to have different requirements and so that's where we're going to start so in our case what we're doing is we're looking at frameworks that kind of center around um kind of i.t and cyber security and we looked at nist 853 800 171 and this csf had just come out at that point um so we were looking at that iso 27001 we all think of that as like the gold standard um truth is it's probably anything but it's pretty pretty slim pretty narrow um high trust is another one high trust is proprietary along with iso and so you
know we looked at all these different frameworks and when we started looking at all right what do we do here um we ended up selecting the cyber security framework and the main reasons were it was free right we're not dealing with proprietary things like iso or high trust or something like that um nist is fantastic when it comes to best practices there's a lot of controls a lot of kind of requirements that are spelled out in there and you look through them and you're like yeah we should do that yeah we should do that absolutely um it's relatively complete uh from a cyber security standpoint now if you're looking at data privacy or things like that uh not so much that's
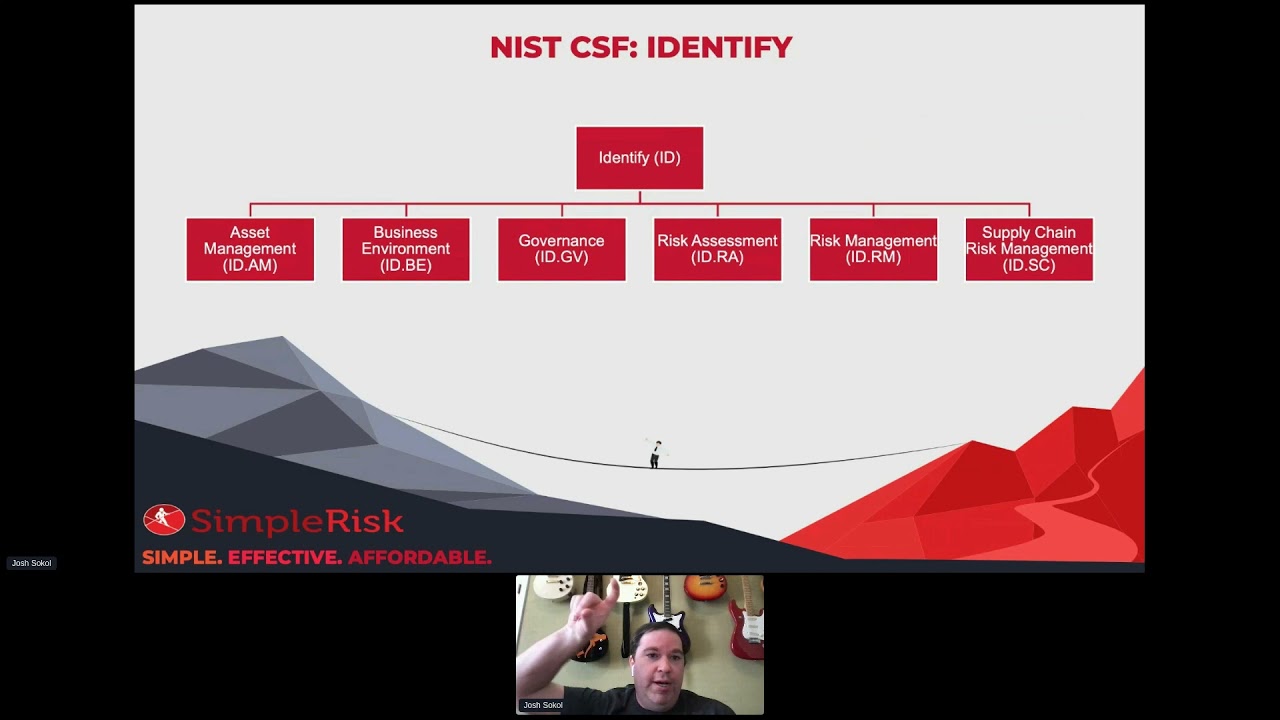
why this came out with the privacy framework shortly thereafter now csf breaks into five different functions that's that identify protect detect respond and recover that you see there and each of those functions has several categories resulting in 23 total categories so uh just as an example our identify function looks like this we have asset management business environment governance risk assessment risk management and supply chain risk management and so you can kind of see when you look at this you've got the higher level uh category there function as id identify and then you have asset management am and so in this csf speak that's going to be identify asset management is ida makes sense right um each of these categories is then
further split into subcategories so you know you'll have something like this asset management the one that we just looked at looking at and that as idm1 through idm six so idm1 says physical devices and systems within the organization are inventoried and idm six says cybersecurity roles and responsibilities for the entire workforce and third-party stakeholders are established so you've kind of got these varying degrees of asset management that are kind of baked into here and told there's 108 of these subcategories or i'd like to refer to them as controls in this case uh they're here so i'm going to flop back over and just see uh yeah no but nobody's asking questions i don't think no q a cool all
right so we'll keep on rocking this um so assessing your current maturity or at least how we do right there's lots of different ways to assess maturity but what alex and i did is we said all right there's this concept of a cmmi a cmmi is basically a maturity model that says you know we're going to go from we're not doing anything at all to man we're doing everything and we're really kicking butt at this um and we created ours based on a combination of miss csf and cobit we eventually kind of landed on these values that you see in front of you this is very similar to what you'll find in the nist capability maturity model or
cmmc that was released after alex and i did this so you know i like to think that we're on the forefront of uh nist csf csf-ness and cmmc um but i think the really important thing to note here is that most organizations won't ever have all or probably even most of their controls at levels four or five i mean level four if you look at the description it says not only have we done everything that is established or below it's saying that's either audited by management or third parties and you have consistent results right so you have like auditors that are coming in they're looking at all the the processes that you've created they're saying yes
this is working this is good you know and your your results are consistent that's a big thing right to get to that point um that's a big ass and then when you move on to step five you're taking even further these are automated processes with a closed feedback loop so when we uh make it some sort of an observation we're supposed to act against that observation and then take that and feed it back in to the process so that that thing doesn't happen again and this all has to be kind of an i made optimized process so you can kind of see how you know when we start we're at zero we're not doing anything all the way up to
five where man we're doing a lot of things um so uh current maturity for asset management so our next step here is that we're basically going to look at each of those subcategories uh and for each one of those subcategories we're going to look at our current capability what are we doing today with respect to the each of these things so you know according to this chart i'm doing really really well at asset management uh physical devices and systems being inventoried right but that's not hard to ask right we can have a an exposed tool we can have some sort of scanner maybe we look at network stuff and it's baked into our next gen
firewalls you know automating the process of inventorying the stuff in our organization that's probably not that difficult but when we start going down the list and we go oh well software has to be inventory too okay well you know we're not doing that in an automated fashion who knows what uh joe engineer installed on their laptop um then we have uh communication data flows being mapped well yeah we kind of do that it's a little bit more than ad hoc but not much right so it's an established process um you know external information systems are catalog you get the idea right all the way down to the last one we're saying man we just flat out are not doing this thing
now some advice for you guys based on lessons learned from alex nye the first piece is be honest with yourself right the understanding of the environment is a gut check at times um the you're gonna go through this and you're gonna go oh man that yeah we don't do that and that kind of sucks but what's gonna happen later on is management is also gonna do that they're gonna look at your results and they're going to go why did you make this decision and you're going to have to provide reasonable examples to support why you said that or refute it to others because they're going to be like well yeah we absolutely do do that and you go
no you know you may do that but as an organization we don't um stay consistent so make sure that as you're going through your you're kind of understanding what each of those levels mean and applying it in a consistent manner as consistent manner and err on the side of caution so being too optimistic can actually cause a lot of trouble from a compliance perspective so dial it back a little bit and if you're kind of on the fence about something you know go for the three instead of the four um because that's a lot easier to explain than why we said that you know we have a optimized process or something like that when we really don't
uh the second piece of advice i have here is consider your environment as a whole when we go through this exercise there are going to be outliers there's going to be areas of your organization where you're like wow that team really does have an optimized process but are they the exception or are they the rule right don't look at your environment as just individual users or teams how standard is this process being performed across our environment if you went to two different uh relevant managers would you get the same response if the answer is no then kind of like we said here err on the side of caution don't be too optimistic kind of go for the lower value
my third piece of advice here is be prepared to defend your responses in our case after alex and i did this exercise and this was not a a simple exercise this was not a one-day exercise was actually um it probably took us two weeks to go through all the different csf responses and kind of come up with that after we did that we sat back down with our manager and we said all right here's what we said and he went through one like well you know that's interesting i feel like we're doing better there and we go well not really because of this and so as you go through keep notes right that will help to kind of show
this is why we made this determination this is how we're judging where we're at today um and inaccuracies are going to lead people to to question the entire thing right so if you said if you came in super optimistic about a certain thing and then your manager comes in they start going well you know what about this what about this you know that no they don't do that there all of a sudden they start to question the whole thing just because of those one or two things that you may have overestimated all right let me check back and see [Music] four plus is expensive no matter how you swing it yeah absolutely so you know
adam brings up a really interesting point which is kind of as you go up that scale uh you're actually putting out more and more money and that's another reason why you know not everybody is going to be a four or five it sometimes it's just you know we don't want to sometimes it's we can't afford to and honestly that's perfectly acceptable um in the us with cmmc the requirement is level three for most of those organizations um i don't know if cmmi5 is ethereal but it's certainly a hard hard thing to reach and you're not going to do it across the board i don't think there's any organization that's ever going to be able to do it across the board and
that's probably what you meant by that curse let's see here so now we go and we assess our desired maturity so we've already figured out where we're at today now we have to figure out where we want to get to uh and to do this we really need to understand what our current risks are uh we have to understand regulatory and compliance requirements and management's risk appetites uh the regulatory requirements are gonna shape our minimum requirements right so how do we comply with all the mandatory uh regulations in the most efficient means possible our risk appetite is going to play a major part uh because it requires us to calibrate with management our overall goal here is to set our
desired state to the value that gives management comfort over the risk right we're not just doing this for our own benefit we're trying to figure out you know what like my boss asked me he said all right you know create a road map that gives us satisfaction right at what point are we done and you know the reality is we're never done we all know that as security practitioners but at least being able to point to a place and say yes if we have all this functionality then we're in good shape um so this is really hard for peop people that are being routinely audited um alex and nikon made the quote don't let perfection become the enemy of good here
uh you know we're not trying to be perfect as we're kind of going through and doing these estimates um that's not the point of this exercise uh the point of this is to to create a road map to come up with something that's decent that's usable that we can use to kind of move the ball forward so another little bit of advice for you guys um the first thing here is be reasonable and we kind of alluded to this earlier not all risks require optimized solutions uh so you know you don't have to be a five you don't have to be a four sometimes being a one or a two is okay right so going back to here
again another reminder here very few organizations will ever get to levels four or five uh for any of their controls um my advice to you is that having your controls at kind of that level three is probably a good target and that's why when nist came out with their baselines they basically said or cmmc rather said level three compliance is what they were looking for all right uh so now we have our kind of list of subcategories we've got our current capability and our desired capability and you can kind of see i've mapped them out here so we want to make sure that we add notes that we assign ownership so we're documenting why we
made these decisions we're documenting who's responsible for these controls and then once we have this now we can start looking at risk now risk in this scenario is really about gaps what we're looking at is where we sit today versus where we want to get to and if there's a difference in those that's a gap right that's a place on our roadmap where we need to kind of close that gap in order to get to where we want to be and so if we look here the bottom three the first one i've got manage process i want to be established the next one i have a perform process again i want to be established and the
last one i'm not doing it i want to at least be predictable and so we have these gaps here so now we have to create risks in this case you can see ida m5 i took as my example here uh we're performing it we want it to be established again performed means that individuals are doing it but it's defined mainly on tribal knowledge answers will vary between teammates whereas established is the owner's defined they're held accountable for the area uh you got formalized policies and procedures so our risk here is really the difference between those if you take like establish process minus perform process that equals risk right and so in this case it's it's that we don't have a
defined process we don't have ownership for the prioritization of resources based on classification criticality and business pretty simple um and that literally is the difference between the current capability and the desired capability now uh grc so grc is an acronym it means governance risk and compliance there's lots of grc tools that are out there that will help you to manage this there's not a lot of grc tools that are out there that will help you manage this for free um and so that kind of is why i got into the business i'm in um simplerisk is a free open source grc platform you can download today and everything that i'm going to show you you're going to be able to do
in simporas uh like by the end of the day today um so we're going to kind of walk through that but understand this isn't a talk about simple risk this is a talk about cyber security maturity and so these concepts would go with whatever grc platform you work with so the first piece is define controls and with define controls this is usually something that you're going to find in the governance side of your grc platform where you're basically saying here's my framework here's the list of all the controls that are part of this framework and you're basically going to spell out kind of the information behind this control so with respect to nist csf we can see that
this is ida m5 we can see the information about ida m5 what it encompasses uh we've got a phase we've got our family so that we can kind of search and filter through those later on and then we have our current level of maturity and our desired level of maturity and we're able to specify those within the platform so now that we've defined this on the government side now we can capture our risk so on the wrist side that's usually a separate module within the grc now we can basically go ahead and enter that risk and so i just took literally the subject that i gave you guys before and i copied and pasted into my grc tool
the next piece is to understand that risk values are going to be based on a few things it's basically the difference between the current and desired state so where we sit today where we will get to you your potential operational and financial impact given a complete failure of this process so how bad is it going to be if we can't identify our assets or our applications or things like that and then the likelihood of that event happening so we go through and if you did your cisp you know risk is likely at times impact there's lots of other formulas out there there's ways to wait them um but ultimately that's kind of what it is it's some sort of a vector
mapping between how likely it is that this event is going to happen and the impact of the event actually happening so then we go through and we populate all the other values we can define you know what teams are going to own this risk is there a person responsible for this we can define technologies we can set locations we're basically going to map this first back to our organization to our environment and all these values are essentially just pivot points they're different ways to search or report on the data so that we can say all right you know what's a list of all the risks that josh is responsible for we can pull that up
now uh your grc should automatically calculate the risk score for you so as you plug those values in we can see that my particular risk here came out with a score of a six um that's a six out of a ten point scale so it ends up being a medium level risk hence the orange color that you see there um if we had a red that would indicate higher yellow is usually lower um typically you'll see color scales like that so our next step would be to plan our mitigation once we have the risk out there we have to say how are we going to address this how are we going to fix this and this ends up kind of becoming
that road map piece right we have where we're at today we have where we want to get to we have the difference between them now that we've created the risk and to bridge that gap to get us to the point where we've actually uh you know closed that uh that problem uh we have to plan our mitigation so in this case i'm saying that currently this is being performed by individuals on ad hoc basis so people are just kind of doing it randomly you know when they feel like they need it and my requirement here is that we need to document the process for prioritization of resources based on classification criticality and business so we're basically saying that the only
thing that needs to happen here to mitigate this particular risk to close this control gap is to document the process well that's pretty easy right and we can assign this to a person and we can even set a date that we want them to fix this by all right let me flip back over here just make sure there's nobody talkie talkie no all right cool um so now let's talk about our road map our road map is all about prioritization it's how do we figure out what are the things that are the most important to us to kind of move that kneel forward and you know the first thing that we can look at here is the maturity gaps so we
can look at kind of where we said we are today versus where we want to get to that current and desired level of maturity and we can split that out by family uh so you know if i look at this chart here i'm doing pretty well at asset management but i really suck at student secure engineering and architecture right so maybe if i look at this you know i'm starting to tell management how we're doing i can say hey asset management yeah there's a few things that we're not excelling at but it's no big deal because our current level of maturity is far and away better than our desired state on average but when we look at secure engineering
and architecture we're coming out as a zero we have absolutely no capability in this area today and therefore that is an area that i think that we need to focus more time more attention more money uh more resources on in order to kind of advance the state of that and we can even talk in terms of you know these are the specific things that we're going to do and as a result of doing those specific things we're gonna move from a zero to a one next year not a huge change but that's better it's a step in the right direction i don't have that little dot in the middle that i absolutely hate every time i look at
this right so when we're assessing maturity gaps we can look at the things that are below maturity at maturity or above maturity obviously the things that are above maturity those are things that we're doing pretty well at we probably don't need to invest more time more money into but the things that show up in that below maturity uh area are things that we're not doing so hot at and we probably do want to uh invest further so this is really going to help us to kind of uh decide where do we invest our money now the next thing that we're going to want to do here is to look at burning fibers these are high priority items um so these are most
likely risks that are scored by a high impact and high likelihood so the things are going to end up being kind of up into the writing or a little thing with the high and the high um these are usually things that could cause serious business interruption or financial loss to the company uh and at least in simpforus we have what we call the high risk reports uh that can be used to identify this so this is literally just a report that's only going to show you the high level risk in your organization kind of the breakdown of those so these are the fires that you want to kind of put out because those are really bad now
obviously there's some kind of level of effort that you need to estimate in there just because something is really bad doesn't mean it's really easy to fix and so it might take days months years in order to fix that particular thing the next thing here is quick wins so these are low hanging fruits and we all have these things in our organization where we look at and we go yeah that would actually be really easy for us to fix you know we don't need a lot of additional assistance in order to fix that um we don't need financial uh you know we don't need to throw money at this problem we don't need a major
personnel investment we can do this with kind of the resources that we already have and so in simpforus we have what we call the risk advice report that you can use to identify this it's basically going to show you the level of effort that you specify for the mitigation mapped against the risk score and so in this particular case i've redacted the actual subjects but here we can see our level of effort as trivial and we can see at the top there are 3.6 risk score so that's our low hanging fruit that's our quick win in this case um to be able to kind of show that we're moving the ball forward and when i first
started the risk management program or i should say the vulnerability management program at uh national instruments this was an area that i focused very heavily on because i was able to show a very significant amount of progress in a very small amount of time and we all want to be able to show that to our management right because then they know that hey you're doing stuff all right uh let's see here so number four uh long-term work these are thematic issues so um as an example your company lacks formal documentation we saw that in my particular risk well maybe what we need is a project and that project is going to go through and make sure that we have formal
documentation for all of our policies all of our all of our processes that are out there um well in simplest uh for these kind of thematic issues you can create a project and you can kind of lump the risk together into a project and now you can manage those thematic issues kind of together and once that issue has been addressed kind of across the board now you can close it and it's going to close all the risks that are associated with that so that's kind of how we handle these things now the last one here is management goals and objectives and this is more about visibility right because what happens in your organization is your company or
your department are going to have ongoing ongoing goals or initiatives that everybody in the organization is kind of expected to support and you support them in different ways based on your role but to give you an example um before i left an eye there was kind of an active effort to try and reduce how much office space we had and if you think about that well you know if we're actively closing down offices and telling people work from home is okay well that brings up some other issues that we still need to address like remote access if these people are working from home or working from a coffee shop or you know wherever they feel like working
we probably have to have some sort of a policy that says here's how you do this safely here's the tools that you need on your system you need a ngav or an edr platform you know that's installed on your system in order to work from the coffee shop uh we do not allow split toning when you're working from the coffee shop things like that and this may be a quick win that actually supports leadership's initiatives right because they said hey we're going to try and reduce office space go great here's the things that security can do to help you with this initiative another example here is if your company is trying to make a push towards
increasing automation uh maybe you want to provide some guidance regarding the processes needed um so like uh integrating optimized controls things like that um so we say hey yes security is gonna help you we're gonna help build a pipeline uh we're going to help to kind of funnel code through this ci cd pipeline and we're going to make sure that security scanners happen within this we're doing stack analysis we're doing whatever and now all of a sudden we're kind of helping them to do this kind of automaty thing uh while at the same time accomplishing our security and compliance goals right so we've done both things kind of all together now in terms of ownership uh
i guess a couple of notes here um the first is that management owns the control environment and any necessary remediation and as security practitioners we sometimes have a hard time grasping on to this concept just like we have a very hard time grasping onto the concept that we don't own risk we our role as security practitioners is to assess risk our role as security practitioners is to convey risk but is not to accept risk and that's a really really important uh thing for us to recognize i oftentimes tell talk to people who say i feel like atlas with the weight of the world on my shoulders and if that thing happens you know i'm gonna get fired well if you put a proper
risk management program into place then you can document these things in advance you can make sure that proper people are signing off on them and then those aren't really your issues they're the organization's issues as they should be so management is going to own the control environment management owns the fixes that are going to happen they're going to be responsible for defining the course of action to direct the projects us as security we're trying to guide them we're trying to help them along management is going to consult with us and you can think of security in compliance as centers of excellence we're providing you know consultation of services but we're not actually engineering we're not actually
implementing the change there may be exceptions within organizations maybe security engineers are you know actually writing code and things like that but you know far far in a way the most common is that we see these guys you know it's not the security team that's making the change to the operating system it's the operating system team the unix guys the network guys the you know windows guys whatever and we're just telling them hey to fix this particular issue here's what you need to do now the last bullet here is that security and compliance validates that management has effectively mitigated the identified risks and communicates overall kind of status to i.t leadership so not only are we kind
of making these recommendations in terms of what we should do we're also validating that they've been done and that's really where kind of the audit piece the compliance piece comes in because we're basically able to say look you know um here's where we have a gap uh management is aware of this gap management decide that they're just going to accept the risk involved with that gap and so we decide that we're not going to negate that but from an overall enterprise perspective we need to be aware that this risk does exist and that's been signed off on so that's it uh that that's basically the talk a quick summary here for you guys um the first one is you can use this
technique for assessing the maturity of just about anything as long as you have some sort of standard to base it off of so you know if you want basis on iso 27001 or hipaa or high trust or you know the new as somebody mentioned talk earlier that there's a new uh privacy um thing coming out of quebec uh whatever you want to do you can base it off of that you just take the requirements that come out of that framework you apply that kind of where we sit today where we want to get to approach and there you have it there's your roadmap the second piece here is that leveraging this csf is really good for assessing
kind of an overall information security program it's a great baseline um you know i've worked some with uh some of the colleges there in canada and you know they're using this csf for you know a lot of the baseline that they're doing so you know if it's good enough for them it should be good enough for you it's good enough for the us government we did at ni uh and so on um the third thing here is it's all about determining where you are and where you need to get to um so think of this as that roadmap here's where we are today there's where we want to get to and how do we bridge that gap
and then you know the last thing is really risk management is an integral part of this process we need to make sure that we are you know properly managing our risk uh because when we're not you know bad things start to happen so with that uh i'll kind of open it up to questions i've kind of been looking in the chat as we went um but uh yeah uh let's see here so adam uh says do you see any point in calculating an overall aggregate score for i don't know executive reporting if so what's an ideal formula do you feel some section should be weighted higher than others or is it more often better to simply
prioritize due to roadmap output okay so big big question here um should we do aggregate reporting i guess is kind of the starting point kind of executive reports and things like that absolutely um there's kind of two types of risk management programs there's the um i.t or kind of the focus area risk management program and we see this a lot where in my organization risk management sprung out of my it group and that's where i was running it but there was another group that was doing risk management for trade compliance another group doing it for the legal department things like that and that's okay right everybody every organization can kind of have their own little pocket of risk management
but at some level you have executives who want to know what's our risk for the organization and when they ask that question they don't want to know oh we have x vulnerability on y server that's not the question that they're asking and this is a place where security practitioners often get hung up on what they want to know is kind of high level was that risk look like do we have issues with business continuity planning um do we have a pandemic plan uh you know they're looking at these business risks right uh what happens if our data center uh gets struck by a meteor and you know can't operate do we have a backup plan
for that those are the kind of things that they're considering and so from an enterprise level oftentimes what you're doing is you're kind of summarizing risks you're you're creating almost those projects and you're bubbling them up to them and they probably won't look anything like the risk that you had originally submitted into your system and that's okay because they care about kind different levels of things than you're going to interact with on a daily basis ideal formula i mean use the same formula right you're still looking at some likelihood of an event happening impact of that event happening um so one thing that you should keep in mind is whatever that scope looks like that
you're evaluating risk in you need to make sure that you're doing that across the entire kind of environment right so to give you an example if i'm a member of the unix team and i have a system that crashes every day at noon that might be a really high risk for me because my goal as member of unix team is to maintain high availability of our servers and i can't do that my servers keep crashing so if i'm that guy that's the member of the unix team i might mark that as a 10 out of 10 right because that's something i care about now if you move up a level and you're like i.t right we're looking at it now
one server crashing in an organization that has tens of thousands of servers that's probably not as big of a deal what if we have uh load balancing right well if we have kind of uh the ability to pull that server out and have another one that's operating in its place um what is the function of that server is it actually doing something that's mission critical is it supporting you know e-commerce transactions on a you know million-dollar minute website or is this just you know some server that's kind of uh we run a build on that once a week right so now we're looking at from a different perspective okay well you know that's gonna change our
risk score when we look at in that context now let's drive up another level right now we're looking at our executive team we're looking at kind of the overview of the whole organization totally different picture right they they don't care about that one server that's crashing one bit that's not even on their radar um but if you told them that that one server crashing is bringing down the website we're losing millions of dollars a day in business that's something that they're absolutely gonna care about so kind of understand what that scope looks like you know what uh what level of uh you know magnification you're looking at it under the microscope and that really is gonna affect what that score looks
like so keep that in mind baseline against that scope um so i guess that kind of goes to the weighting higher than others i mean it's not necessarily that you're weighting it higher than others um you're using the same formula you're just making sure that you take into account kind of the the scope when you're using that formula uh so hopefully that answers your question there adam uh aj agrees especially if that server provides an environment of minimal consequence absolutely i mean if if that system being down down doesn't really matter who cares if the system is down um and this is where we start kind of moving into kind of the business continuity playing realm where you know
we start to look at the servers and and you know what is the value of that server and how long does it take to bring it back up and you know things like that uh and debbie absolutely business context matters uh let's see have i considered delivering the same toolkit with the cis 18 instead of the csf um absolutely so uh we have the ability to do that when i say we i'm talking some horse at this point because i assume that's what the question is about um cis critical security controls uh so one thing that you have to recognize is cis is actually a proprietary framework uh and unfortunately what that means is that you can't
include the actual controls from the the ciscsc without actually paying cis a lot of money in our case with our sizes about 20 000 which kind of seems to me like a waste of money to be honest with you so what we do instead is we partner with an organization called compliance forge uh compliance forge has a control framework called the secure control framework or scf you can go to securecontrolframework.com uh to check it out and it's basically like almost a thousand controls that they've mapped across 177 different frameworks and so things like the the ciscsc nist csf iso 27001 um you name it it's kind of in that list of control frameworks and it's
pretty awesome having that ability because now not only can you specify you know where we're at with one framework you can actually flip that over and go okay well that's the picture that looks like for iso 27001 what if all of a sudden we had to be pci compliant well if all of a sudden we had to be hipaa compliant or whatever you're able to kind of just flip the pick and all of a sudden now you're seeing the controls that are part of that thing so it's pretty cool to be able to do that uh yes if the system is down nobody cares why bring it back up absolutely um you know it's kind of funny uh
kind of i.t approach to a lot of things uh and i came from an i.t background is if you don't have an owner for a system and something has to happen maybe um you're doing changes on the network and those changes are resulting in re-iping all the servers and you have a server you don't know who owns that thing well what you do you turn it off and you wait to hear who screams right and that that's just the reality of things uh yeah timothy you beat me to the the punchline they're screen testing um cool uh let's see um anything else guys i think we're getting close to time all right when it comes to risk compliance how do these
frameworks and systems account for irrationality we run into things like it crews shirking findings or management not taking ownership when it's not in their personal interests so that's a great question and i think it kind of goes along with what i said earlier the the realization needs to be that we as security practitioners i'm talking about all of us that are on here um we as security practitioners are our job is to assess risk and to convey risk and so you will accessorists you'll find issues and you will convey them to management and frankly management will throw their hands up and say we don't care right and at that point you need to ask yourself
all right they don't care how am i going to let that impact me and traditionally and i was in this role a long time ago too as security practitioners we feel like it's our job it's our duty to yell at them and tell them where they're wrong until they do care right that's just the reality of being a security person um unfortunately it doesn't ever get us anywhere you know talking about the problem until we're blue in the face really doesn't fix the problem and honestly it doesn't make them more likely to fix the problem uh so the end result of that is that we need to basically say look this is about risk management i've gone on record i've
told you here's a risk now we have to have some sort of a system to be able to track that that's where our grc comes in and we have to be able to say you know here's the risk you know so and so please go and sign off on this risk say that uh you know you approve this risk and you don't plan on doing anything about now you know if that thing happens we at least have some place to point and say look we assessed the risk we conveyed the risk so and so accepted that risk and it really is businesses job to assess those risks if you get into a situation where they're not willing to sign off on that
particular risk then you need to have kind of an introspective and start to go is this the organization that i want to be working for and i realize that that's a hard thing to say um especially coming from the guy who's now self-employed but at the end of the day you need to figure out you know am i a scapegoat in this organization or am i actively working with other people to make things better and any organization that you're a scapegoat in you might you know you might be there a long time you might have a golden parachute i you know but at the end of the day are you comfortable with that is it
going to help you career-wise is it going to you know give you when you finally leave that place or you have a soft landing someplace else those are the kind of things that you should be thinking about there so um jeffrey hopefully that gave you uh uh okay answer to your question there uh let's see last one i swear what's my thoughts on fair um okay so uh fair factored analysis of information risk um fair is what you refer to as quantitative risk analysis so most of what we've talked about here is qualitative we multiply a you know this is definitely going to happen against a it's really bad if it does and we get a score of a you know 10
or a high right that's qualitative um fair is basically going to give you dollar value so it's going to give you ranges of dollars um for that fair is useful there are certainly people out there that are going to you know tell you that i am completely wrong for advocating for anything that is qualitative um but at the end of the day the realization that i had is fair takes a lot of time um it takes a lot of resources and even the fair people will tell you don't use uh any sort of uh don't use quantive for everything that you're doing figure out where your biggest risks are and do quantitative analysis for that
um in terms of whether it maps with simple risk uh we have a customer who's um kind of out in the bay area and they use a customization piece of simporous to track every single one of the uh vectors that they put into a fair calculator uh and then they track kind of the results that come out of that thing so yes you you can kind of use them in tandem and then again if you're not doing all of your risk with the quantitative methodology and you're using qualitative as well then certainly having a system that's capable of both there's going to be value there uh let's see here um yeah kuro said very well the culture of an org doesn't
align with your values it's kind of time to ask that question right should i be here um steve why is there not a financial background what do you mean by that steve i'm curious
uh let's see well steve is doing that see a q a i don't see any q a stuff that came up here okay um well steve you got a minute or so to to tell me what you're thinking there um anybody else have any questions art thanks for uh thanks for joining me i appreciate it um awesome well uh thank you all for coming i really appreciate it i it definitely would have sucked if i was here all by myself but the fact that uh 40 something of you guys came and and listened to me i really do appreciate that um i'll be around the conference if you guys want to you know ping me send me a message um
if you want to find me on linkedin i'm linkedin i think i'm at joshua on twitter um i'm around and i'm a pretty social guy if you guys ever watch that so um thank you all so much really appreciate and i hope you have a great rest of the conference why is security not a function of finance um oh so um in some cases it is uh so in some cases we see uh cso reporting up to somebody like a cfo um in some cases we see security people reporting through i.t it really just depends on the organization and oftentimes it depends on where somebody in the organization finally decided that somebody should do something about security
in my organization it was you know 13 something years back 15 years ago that i went huh nobody's looking at security somebody should and i started doing something he eventually worked myself into a security job it just happened that i did that under it leadership um and that was really hard once i did that to kind of break out and be more of an enterprise security guy um but uh you know there's there's going to be benefits to working under finance or cfo there's going to be weaknesses as well obviously working for the person who has the money man that sounds awesome right if the cfo is willing to give me more and more money every year to keep things
secure cool um the other nice thing about kind of the the finance organization is that those guys uh in finance obviously not guys the people in finance um they do risk all the time they understand what fraud is and things like that uh and so you know generally speaking they have a good idea there um honestly legal is a great place for security or into as well right you we have a lot of requirements a lot of regulations things like that uh you know one can make the argument that we should reform to legal um should we report in thai tea i mean there's a lot of conflict of interest there there were a lot of times where you know we would say
hey you know here's a major issue actually um the there was a a very large data breach uh with a credit uh company here in the us and when they got breached the actual issue that they got breached with was something that we had recognized on our website uh many months before that and i ended up having to run that up three chains of management um saying this is really bad and it's literally the only time in my 13 years at ni uh where i went chicken little on them um and said you know the sky is falling if we don't fix this and people got mad at me for that but the end result is we didn't get hacked and they
did so you know i think there's going to be times there where like regardless of which organization you're in hopefully you have that chain management that when you say this is really bad they their ears perk up and they listen so cool all right well i'm out of time thank you all for uh for coming i appreciate it and uh yeah take care everybody have a good conference





