Characteristics of Emotet Infections
Show original YouTube description
Show transcript [en]
everybody to characteristics of emotech infections I am Brad Duncan I'm a threat intelligence analyst with Palo Alto networks unit 42 team uh I also volunteer for the internet Storm Center do some Diaries their infosec blogs for lack of a better term I tweet at malware underscore traffic on Twitter usually very dry boring technical tweets every once in a while I'll post a meme or something and then I'll post a lot of pcapp and malware samples to my blog at malware traffic Dash analysis.net foreign it's interesting when I submitted this proposal for this talk to the committee imotet was active and very much uh daily uh spammer where we would get various email examples for emotech on a daily basis
submitted to virus total and I would see it in my spam traps and now it's uh since about mid-july it's been quiet the botnet the infrastructure behind neemotet is still there it's still alive it's still occasionally doing things but it's not spamming so this emotec is uh what I would call dormant right now but we'll look at what emoted is um I'll describe how my lab environment is set up to look at some examples of emotec infection traffic which is uh we'll have two examples that we'll cover here and then other malware that is active that's kind of filling that hole that emotec left has left open since it's gone dormant so originally discovered in 2014
the emotech is uh was first a banking Trojan discovered as a banking Trojan and it's kind of morphed uh it's a what we call a modular malware which means that uh um it has functions that are sent as separate modules from the initial infection so for example you have a Spam bot module that will usually appear in my lab environment we'll see it uh spam bot activity happen on an infected Windows host approximately 30 to 45 minutes after the initial infection but uh it is back door it is a spam bot and it does uh provide follow-up malware usually Cobalt strike but we've uh we've seen other types of malware as well this the Cobalt strength ties in with the
emotec being an initial access broker which means the criminal group behind emotet likes to make extra money I guess by selling access to the hosts the infected Windows hosts that are part of its botnet and then these other criminals will use Cobalt strike to then map out the environment and uh see if there's anything of a high value Target and then usually it'll drop ransomware uh whoever the additional criminal is so uh when you hear stories about Conti ransomware uh attacks in the past year or so some of those can be directly attributed to an initial imhotet infection by someone who was tricked by a emoted Spam body email so there are currently two emoted
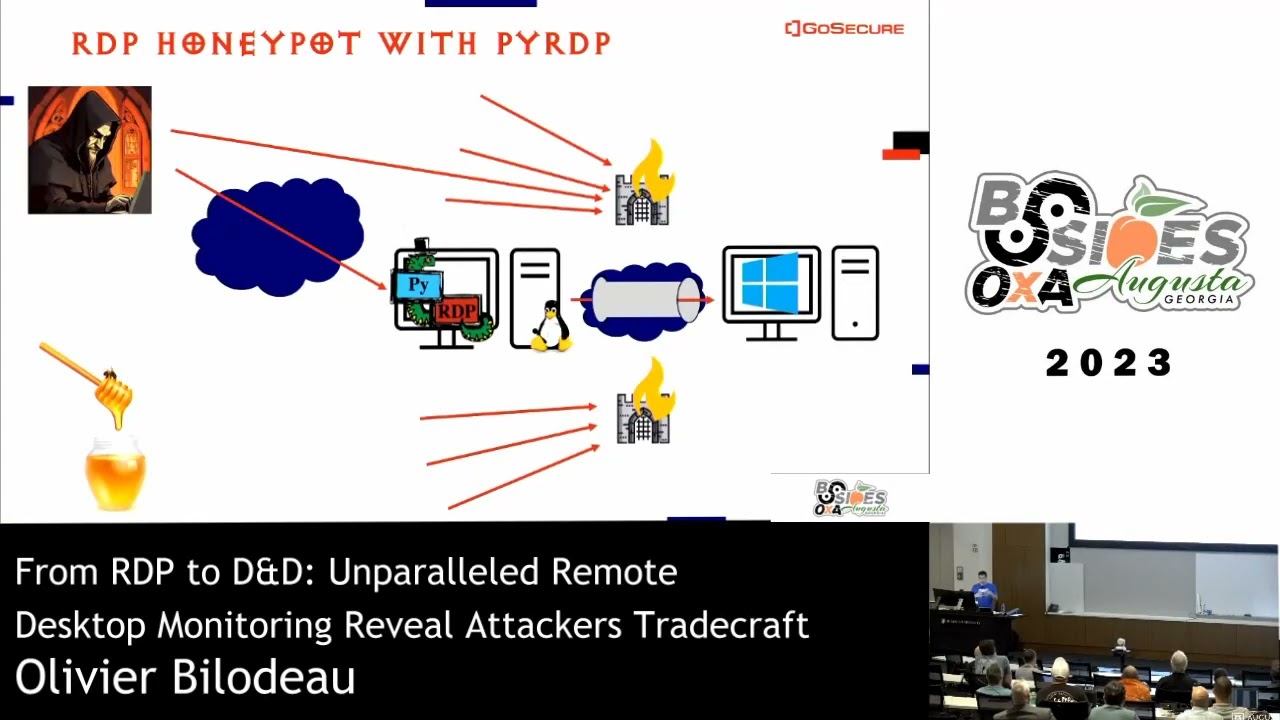
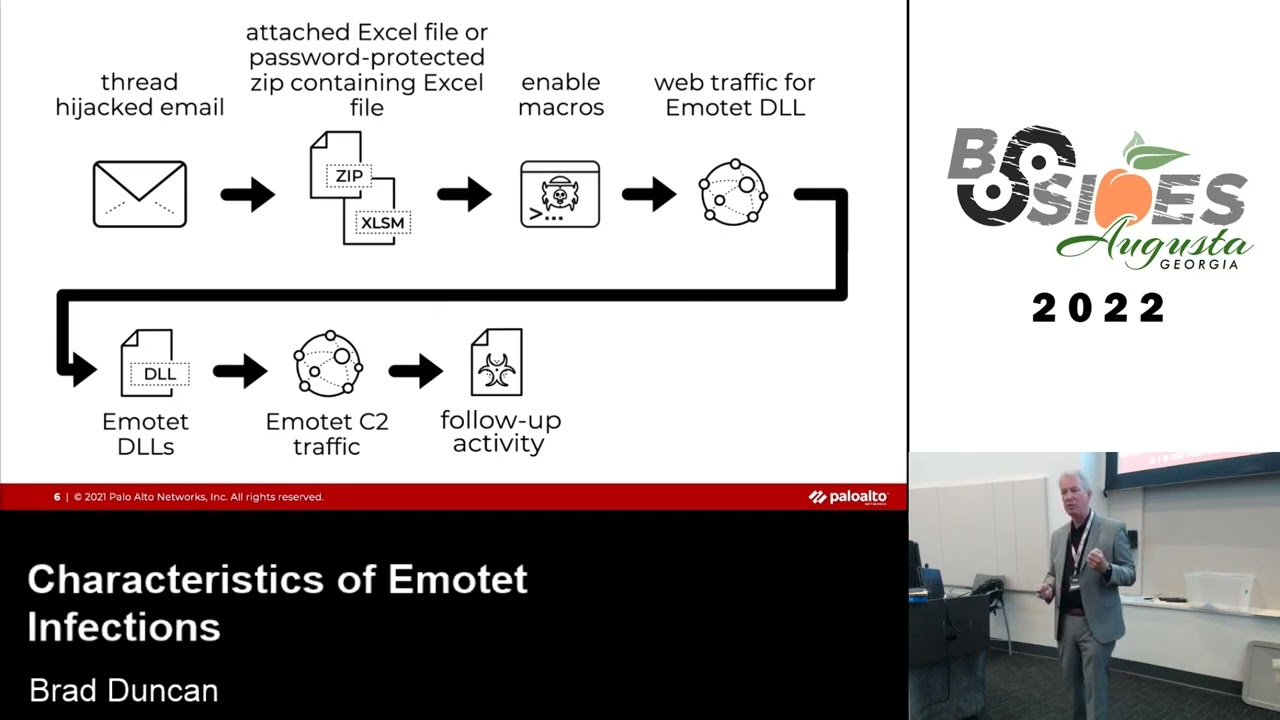
botnets they act exactly the same I'm not sure how certain people who track these things uh separate these two botnets out they call it epoch4 for one botnet Epoch five for the other botnet the reason they call it four and five is because before the 2021 takedown of emotech where it was gone for about 11 months came back in November of last year before that uh absence there were three botnets and they were called Epoch one Epoch II and Epoch three uh just nicknames by security researchers uh for the infrastructure behind emoted uh in recent years as I've said imotet infections have been publicly documented as leading to ransomware now here is the chain of events for atypical emotec
infection for the last few months last two or three months it was consistently something like this before it went quiet in mid-july 2022. so you would have a thread hijacked email and sometimes these emails wouldn't be threat hijacked but they're always impersonating somebody some stolen email address that was taken from a previously emotec infected host because part of what emotec does when it affects a Windows host is if you have a email client like Outlook or Thunderbird and you've got a bunch of emails in there it will take that information and we'll send it up to the botnet and then the uh emote botnet that infrastructure will regurgitate that information and use it for thread hijacked emails impersonating
a legitimate a sender and including those email chains but these emails um for the last two or three months before it went silent always contained attachments so it was either a password protected zip archive sometimes not password protected but mostly password protected that contain an Excel spreadsheet a Microsoft Excel spreadsheet specially crafted to with a macro with malicious code designed to infect a vulnerable computer with emotec a vulnerable computer and a victim would enable macros on a vulnerable Windows host and that would generate traffic to retrieve a Windows binary Windows dll File in this case for emotec and it would run it on the infected Windows host now you would see traffic wouldn't be just one
HTTP or HTTP request it'd usually be about three or four or five URLs that would retrieve emotec dlls and this would be a redundancy because these URLs will change frequently because they're easily detectable as hosting malware they'll get taken offline so therefore you have usually four or five different URLs that are all triggered to retrieve an emotec dll and hopefully one of them will still be active and then once the motet dll is run that's when we start seeing the command control traffic to servers on the IMO 10 botnet and then from there you see the follow-up activity like spam bot activity or Cobalt strike from what I've seen in my lab and then possibly in a
worst case scenario something like ransomware so here's an example of an email that has a password protected zip archive as an attachment and this is a thread hijacked email between it was stolen on a formerly infected Windows host that I infected with emotec my lab environment I'll populate my mail client with emails back and forth between email accounts that I control and one of them was a in this case it was Gmail account that I used uh named with a nickname Dom uh don Bertram and what we do here and Martin uh somebody I forget was the name of the recipient I've got everything shaded out here because I'm not going to share my honey pot email addresses with you guys
at least not publicly so if anybody's curious you can ask me about there is a couple I will share publicly here in this presentation but those are considered burned we have a uh you can't see it because I haven't scrolled down but we have uh the legitimate email chain between these two email accounts that I control that I've set up and uh it says hello Martin archive password 723 have a great day Don Bertram and then whatever you know great work on this morning's presentation whatever that email chain was now if you guys got an email like this from someone that you knew or at least that claimed to be some though from someone that you knew this would be uh
relatively easy to detect uh just because if you look at the from line of this it says Don Bertram as the name or the nickname but if you look at the email that is not Dom Bertram's Gmail account email it is uh something.it is an Italian email provider an Italian email address you open that password protected zip archive and then within that password protected zip archive there is an Excel spreadsheet that Excel spreadsheet for the last two or three months at emotech was actively spamming was sending out Excel spreadsheets that looked exactly like this um I think uh sometimes the the little gray shaded area with the warning would be yellow or to be pink but it it would
look exactly the same and you'll notice that there are seven spreadsheets tabs in this particular spreadsheet and if you look at the workbook properties you'll see a couple of uh consistent things like the author I think was always in this case dream and um last modified I don't know I think they were all RGS sgk but the thing with this is the work the sheets in the workbook were all protected so I can't go in and look at the macro code for this particular spreadsheet without knowing whatever password that was used to protect these particular sheets in this workbook so the only easy way quick and easy way for me to figure out what what those
URLs is is to detonate it in a environment or a sandbox So speaking of lab environments we'll look at my lab environment that I will use to um detonate emotent malware to check it in the environment now I will use active directory environments a lot of sandboxes especially the free ones or relatively cheap ones that are available even a lot of the Enterprise solutions for example Palo Alto networks has a live type of sandbox environment called Wildfire but that's a single Standalone Windows host right or maybe it's running them on two different ones you know one Windows 10 one maybe Windows 7 or something like that but it's not an active directory environment I like to use active directory
environments because that's how you see Cobalt strike so a malware like emotec or cacbot or iced ID is not going to send Cobalt strike to sell that access to that host to an initial access broker because a standalone Windows host is generally not part of a high value Target right you want an active directory environment with hundreds of clients and various interesting servers that could be uh that could be either exploited or targeted for ransomware but uh what I'll generally do in a virtualized environment in this MacBook that I have here for example I'm running either VMware Fusion or virtualbox those are two of them on a Linux host I can run the KVM system in qemu I've tried that
before with uh with the relatively good success and then those are generally it I do have a physical environment that I'll use for certain families of malware that are very resistant to running properly in a virtual environment so instead of uh I'm not I'm not as technically proficient as some people who can alter their virtual environments to disguise the fact that they're virtual right so I I just it's easier for me just to you know pick up a couple of laptops on eBay and an old Cisco switch and you know just set up an environment in my home lab and this is how I do it here plus the benefit of having a physical setup like this
is that you can add as many windows clients as you have ports in your switch and then I could usually just do a span port on a Cisco switch to any one of those clients if I'm detonating what's that on there I can just span that Port into another Port where I'm monitoring it on a computer that I'm using TCB dump or Wireshark to record the pcap I like to have fun with my virtual environments it's not all just uh monotonous although there is monotony and routine although it is routine uh stuff that I do every day I'd like to have a little fun so uh for example uh for a while there a short while I was
using an environment uh that was Batman and Robin right so um this is not the this is not the modern Batman right the the the guy that's facing the whispery deep voice this is the Adam West Batman of the late 1960s uh with uh Adam West and Bert Ward right so this is uh Batman would use aol.com right he's a little older generation uh and then Robin who's a little more young a little more hip he would use something relatively newer like Yahoo at least that's the way I see it um so I'll come up with these conversations off the top of my head uh this is uh this is one of the an example of the
emails that I'll send where um and I try and imitate the Adam West uh version of Batman uh vocally but it doesn't work out it sounds more like the Christopher Lloyd character uh Doc in Back to the Future it's like we gotta defeat the Joker it doesn't sound anything like Adam West but this is type of emails that uh that all Less in between these two accounts I'm using Thunderbird to uh to uh as the email client in my environment and you can see uh what I have up here uh I started near the end of June I had this going for a couple of weeks those accounts are still there though so feel free feel free to send anything you want
to any of these emails doubt I'll be I'll doubt I'll be using it much after today but uh you can see some of these emails have attachments and they're uh they're all reply based emails these are thread hijacked emails um I I shouldn't say thread hijacked emails uh sometimes that are not exactly thread hijacked like this one so yeah it's uh please open the attached document it's got a Excel spreadsheet and this is emotech right and uh but there is no uh email chain on this one the subject is r e and then the the uh recipient's email address and there uh there is no actual uh legitimate email chain that has gone back and forth here so we'll kind of see
that sometimes with emotec it will just uh put your email address to kind of pretend that there was a conversation anyway the attachment whether it's a within a zip archive that's password protected or whether it's directly attached to the email itself is the same type of Excel spreadsheet that we looked at earlier now this exact email from July 11th with this exact attachment I ran it earlier this week remember how I said there's uh usually four or five urls that are generated after by the macro code in that malicious document well we do have we do have https and HTTP based urls and one of those actually worked one of the HTTP URLs now what's
interesting here is uh when I ran this just through my home internet to check my internet service provider it was blocked so I tethered through my phone and my phone allowed this to that internet connection through my phone allowed this this Windows dll to come through right this is this is a URL that has been hosting malware since as early as July 11th and it's still active all right it took that URL that macro code from that malicious uh Microsoft Excel document and it saved it saves it to a under the infected users app data local directory it creates a new directory of random alphabetic characters and it saves it and it runs it and it
remains persistent through a Windows registry update through the most commonly used Windows registry update to keep malware persistent it's the hkey current user software Microsoft Windows current version run that particular you know under the HK CU registry hive and red server 32.exe is what is used to run it so it doesn't have an entry point like you would use if you were using run dll32 so with that in mind let's take a look at our first example now the Wireshark displays that are showing here that I'm showing here and there are some of you that I see that have uh participated in the workshop that I ran earlier this week it is my customized Wireshark column display all right and
you can find out how to set that up in the same way that I use it by looking at the Wireshark Workshop videos that I have posted through my employer Palo Alto networks if you Google Wireshark Workshop Duncan you should find that link to all that has a Palo Alto networks page that is on my blog posts and articles through the company that I've used to do that now this first infection example is from the 7th of June so I've posted the traffic online at my malware trafficanalysis.net blog I did a tweet about it through the unit 42 Intel handle on Twitter dumpsterfire though Twitter is it is it is very useful you may have
heard of the term infosec Twitter that's uh that is a thing figure about anywhere from 50 to 100 Twitter accounts that that are primarily geared towards tweeting or retweeting technical information now granted the unit 42 Intel handles uh specifically you know it's doing more than just these type of tweets it's a little promotional as well and promoting the unit 42 blog and everything but uh my particular uh you know I'll retweet this through my Twitter handle as well the at malware underscore traffic there's a lot of people on Twitter like I said about 50 to 100 that consistently tweet technical details but this particular pcap that is available on my blog site is an active directory environment
and I'm using crypto punch.data as a uh as a domain that is not registered by the way I'll go through I'll go through a domain registrar just to check to make sure that whatever domains I'm setting up for my active directory environments are not already registered because I have posted information before on stuff that I didn't realize was registered by somebody and have got an email saying hey uh you uh you you're posting this uh information that implies that our network is compromised and uh they asked me to take it down and I can only say yes but this is the active directory environment I want to infect my an active directory environment with the emotec because if I
don't I won't see Cobalt strike if they send it and it's about a 50 50 shot if they actually send it sometimes less than that depends on what time of the day U.S time wherever what time of the day that I am infecting a Windows host as to whether I might or might not see Cobalt strike foreign so I have this in Wireshark this particular P CAP from the 7th of June 2022 there are two https URLs and one HTTP URL that that were generated by the Excel Macro for that emotec dll and those are here now we don't know what those uh two first two URLs are unless you submit the uh the malware to
a Sandbox environment that has some sort of uh man in the middle set up to where you can uh decrypt that https traffic which is what I did in this case so the only one that we could look at that we could actually follow the TCP stream for and see if something was returned is uh visibly is that last HTTP URL so in Wireshark this is one of the first tricks that I learned as a analyst using Wireshark when I was first starting out was you follow the TCP Stream So you left click on that particular frame in your column display and you follow the TCP string bring up a menu and follow the TCP stream in this
case this particular URL did not return anything so the emotec dll or dlls would have been through the https traffic that's not going to be available in the pcap if you go to that blog entry on my site I retrieve the two dlls that were actually retrieved over https from the infected Windows host itself if we go back to our pcap and use the basic web filter you'll see that there is https activity to various IP addresses over TCP port 8080 and TCP Port 443 and that's just a list of everything right there all right you'll notice that there are a lot of IP addresses over those two various reports it's not limited to Port 443 or 8080 those are
just the most common ones sometimes they'll see it over https traffic over TCP port 7080. now um one of the things that you can trigger of an alert for on the network traffic is the certificate data from the certificates that are used to establish that TLS connection this is TLS version 1.2 so there is a certificate that is sent that we can actually see the data for if if this were TLS version 1.3 we could not do this so I would filter on tls.handshake.type equals 11 and in this case I'm just going anything with that particular data which I filter for that to look at the certificate data for any https traffic over TCP port 8080.
if I go to the frame details and I'll expand my way down to look at the certificate data so I'm going through transport layer security handshake protocol certificate handshake protocol certificate going all the way down until I see the certificate issuer data and there's a bunch of RDS sequence items and these are the sequence items uh illustrate they they have the values of the issuer data for this particular certificate and this is a self-signed certificate so uh when you set up an https server or web server that does https you need to have a certificate a public and a private in order to establish that TLS connection so this is the public certificate and you can actually you could have when
this was still active you could go you could have gone uh back in June on June 7th you could have uh plugged that IP address and Port into your web browser and it would go to the site now any uh web browsers any normal web browser is going to look at that and say hey this is this is a big security risk because this is a self-signed certificate it is not a recognized certificate Authority so Chrome Mozilla Firefox I'm sorry Chrome Firefox Microsoft Edge Safari they're not going to show it immediately but they'll let you accept the risk and continue now what we can do on this particular page that shows up we can click on that view certificate link
and we would find out that everything that we saw in Wireshark that we could find out in Wireshark we would find here thank you and you could use something like openssh to generate these types of certificates which is what I assume that the criminals do when they set these up because it's completely free now this traffic doesn't use a web browser to establish that connection for that https data to go back and forth right it's the malware itself that's doing that so it's not using a web browser so there is absolutely no problem whatsoever for malware to establish a command controls Channel over https traffic for a server that's using a self-signed certificate and we see that commonly
we commonly see that and they're I believe the emerging threats open rule Set uh has a at least an informational signature that triggers on certificate issuer data that comes over uh prior to that TLS connection being established where it's triggering on stuff like example.com or Global Security as an organization for this particular pcap this particular example you know we've seen emotec but the more interesting thing with an email infection is do we see Cobalt strike with uh emotec or any other malware because Cobalt strike is that precursor to other activity this is an initial access broker providing access to that infected Windows host to another criminal group so we see this uh because emotech always
uses IP addresses for its command control traffic without domains without any Associated domains if you start seeing a bunch of https entries as you were looking through Wireshark using this particular basic web filter and you see multiple https entries uh multiple entries per minute it's probably Cobalt strike and what we have here is uh I forget how many minutes this is after the initial infection what we see uh https traffic to lentgen.com now I already knew I already can look at this and know that yeah this is Cobalt strike traffic but uh and the certificate is a let's encrypt certificate for this uh particular web server but um it isn't uh just uh I who have uh you
know used the unit 42 Intel handle through Twitter to tweet that there were have been other accounts that have also discovered this as a Cobalt strike domain foreign
is it turns an infected Windows host into a Spam bot and if you're not already familiar with TCP ports 465 587 and 25. those are TCP ports associated with SMTP traffic
when I use my basic web filter and I start seeing entries that show TCP Port 465 and 587 and 25 then I know okay I've got some spam bot activity here especially if I'm not seeing any actual domains that are coming up here so I can filter an easy way to check and see if you have possible spam bot activity in a pcap on a traffic that you're investigating for a possibly infected Windows host is to filter on SMTP and we'll notice here that uh basically you'll see the SMTP commands that establish the TLs tunnel and then everything after that is encrypted so and you'll see more than one in this case I see three separate public IP
addresses to those SMTP based TCP ports using those TCP ports associated with SMTP now a Windows client on a normal basis even if it's set up to to get SMTP traffic from a single mail server for its mail client it's not going to go to different IP addresses for SMTP traffic you're not going to see three four five or normally with emotec you're seeing dozens of different IP addresses and dozens of DNS queries to various mail server domains every minute every minute or two and that's not normal that's spam bot activity now with the spambot activity regardless of the malware if there is any unencrypted SMTP traffic and there's an email that's sent over you can do a
quick check by filtering on smtp.data.fragment in this example we do not see that so every everything that was sent over SMTP for this particular example was all encrypted and uh quite literally I think if I would have waited long enough I would have found some unencrypted SMTP traffic but uh we're talking uh we're talking hundreds of megabytes or gigabytes of data depending on how long you have to wait it generates a lot of traffic emotec spambot activity generates a lot of traffic so for this particular example this first example of emotec uh we see https traffic for the emotec dll one unsuccessful https request we see command control traffic for emotech over https using that self-signed certificate and it's
always that specific self-signed certificate issuer right example.com it Department all that stuff right it's that that particular set of values for the certificate issuer is not unique to emotech but emotec always uses that particular set of values and then we saw https Cobalt strike traffic and you'll notice that that doesn't stay up very long before it stops in my particular environment because I'm generally just using one domain controller and one client right so it's not going to take somebody very long to quickly map out that environment and say oh you know good Lord this is nothing worth my time and then uh just quit and then we see encrypted SMTP traffic for uh spambot activity
so let's look at our second example of emotech traffic this one is from the fifth of July a little a little less than a month after the previous example in this one I've actually got uh 10 examples of emotec mouse spam from the uh from the days leading up to January I'm sorry July 5th and then we have this one this one does not contain Cobalt strike but it does contain spam bot activity and it does contain some emoted dlls that were sent over unencrypted HTTP which we can export from the pcapp and there is some unencrypted SMTP traffic that contains email examples spammed out by this host that is now or was then part of an
emotec botnet so if I load this in Wireshark with my special link crafted customized Wireshark column display and the filters that I use use my basic web filter and I can see three HTTP URLs and one https apparently a URL once again this is TLS encrypted traffic I can see the domain uh if it's TLS version 1.2 I can see the domain in the certificate issue but um if I follow the TCP stream for any one of those green lines up there those urls on July 5th I would uh I would see that there was a Windows executable file or Windows dll File that was returned from that server uh this particular one uh Zona information.es
which I believe es is uh Spain if I'm not mistaken right so this is a domain this is a legitimate domain these URLs that are hosting these emotec dll files are almost always legitimate websites that have been compromised and being used to host these uh these emoted dll files the command control servers are different those are specially established usually through fraud accounts through some sort of service provider somewhere but these you wouldn't want to block everything from this uh particular site then again maybe you would but uh this particular URL yes you could block it you could safely block it so you'll notice that a Windows executable file or a Windows dll File the first two bytes of either one of
those files shows up as the ASCII characters m z and then you'll usually see a line that says this program cannot be run in DOS mode maybe not that exact wording but something along those lines and then you may see some text strings that indicate some of the packed executable headers for this particular packed executable or uh p-e-d-l-l now again we can export these objects that were sent over unencrypted hddb traffic by using the export objects function in Wireshark all right so I could go to my file menu my export objects menu and then select HTTP objects and you'll notice when you do that with this particular pcap that all three of those unencrypted HTTP URLs
returned 525 kilobyte file um and what I can do with these is when I save these I can do a in a Linux environment for example I could do a file command to check to confirm that these are uh you know executable or dll files in this case it's a 64-bit Windows dll File I'll find that by using the file command I'll do a Shaw sum command to get that Shaw 256 hash and then I'll check that file hash and virus total or better yet I'll just do a Google search to see if that particular file has been submitted to any of the publicly available online sandboxes and then check and see if the information that they have matches the
indicators that I'm seeing in this pcap the Zenni know does anyone know why that I wouldn't just submit this Windows executable file or this Windows dll File to virus total directly
yeah tip your head he knows that you found his malware yeah exactly right that's what you were saying as well that yeah you don't want to do it because this uh you know if it is a targeted attack right this I don't care if you know what SEMA did submit that stuff to virus total because these things are generally have a different file hash every anyway each time you retrieve that dll from that URL uh there's some sort of hash busting or something going on there where it's uh generating a slightly different file every time but you're exactly right and that's another one of the things that we're taught early on when you're doing some you know near real-time analysis
and investigations of suspicious activity is yeah don't submit the file sample to virustotal or anything else online check that shot 256 hash first uh sir if you'd like to come up you can pick one of these three items here thank you
now in this particular example I have unencrypted SMTP traffic that contains emails that are the same type of thread hijacked emails that I was discussing earlier right I can filter on smtp.data.fragment and we can see that there are what are there 9 10 examples here eight examples nine I can follow the TCP stream for any one of those and I can see some of the SMTP traffic that led to this all right I can see that it is a um uh Japanese uh mail server that this is uh this is uh being used so what's happening here is that infected host that's acting as a Spam bot it's not sending it directly from itself it's
using this uh Japanese email account that's been compromised to relay the message to that address that email address that ends in Dot gov.cl and the beauty of this is and I've had this happen to me with the email accounts that I'll use uh uh you know as spambot traps so I'm infecting a Windows host and uh not only does it Steely email data it seals the username and password for that email account and then I'll uh I'll start seeing bounce back emails in these email accounts that uh from email addresses that are no longer active right I don't see these emails sent in my sent box in my sent queue because it's not being sent from
that account that account is being used as a relay so the only way I will know if my account has been compromised and is spamming is if I get these bounce back emails from email accounts that no longer exist or no longer work and I've had that I've had my uh the email the various email providers shut some of my email accounts down because they've been used as uh you know for spam activity and I wasn't aware of it and it's like oh I'm sorry change the password can I have it back you can export these emails from uh from the PCAT right we can go file export objects and this time select IMF IMF stands for internet mail format
this brings up your IMF object list it has all of those email files in the EML format and you can use an email client I use Thunderbird I don't think I think Outlook Outlook might open them I don't know if the windows based Outlook will I know the Mac based Outlook will but I'm not sure about the windows windows is kind of Windows based Outlook is kind of screwy I'm not saying that officially but anyway this is uh this is the type of thing that we uh for that uh Batman uh email that was spoof that I showed earlier this is the part that wasn't being shown right so uh this is obviously it's going
to a DOT CL email address I'm not uh certain does anybody know what country that is Chile okay so we're uh we're looking at uh I believe Spanish here right and this is not a thread hijacked email but this is pretending to be an email that was uh you know formally sent to that recipient from a you know whoever Patricia sochin is what that was uh that name was taken from a uh address book stolen from a previously infected emotech host so other malware that we see now that emoted is quiet once again ever since mid-july quite literally July 15th was the last evidence that I have of email that was sent from epoch4 or Epoch 5
either one of those botnets so the infrastructure that botnet infrastructure is still alive and still occasionally uh you know you get a heartbeat or something metaphorically speaking from it but uh it's not really doing anything the other malware that has also been active while emotec was active but seems to be even more active now is uh bumblebee iced ID and cackbot those three malware families yes sir how it was shut down I don't know how it was shut down and I wouldn't even say it was shut down it just stopped right it just kind of decided to go to sleep and we would see that occasionally right sometimes you'd see a week or two of a
break where there would be no spamming and like we're still seeing now the button and infrastructure would still be there those servers would still be online but uh the current theory amongst uh some people uh as we fellow security researchers as we kind of chatted is uh you know possibly the whole uh Ukraine conflict might be a reason that this is emotet has been attributed to some russia-based threat actor starting I don't know I don't know I mean it's uh at this point information uh emotec is an information stealer so but it's not specifically banking malware at this point in time so um I think it nobody knows the exact reason why emotech has now gone dormant
if he likes her you can pick one of the I neglected to mention this at the beginning but uh I gotta give away some prizes I figure anyone who's uh interested enough to pay attention through my drone of this highly technical information and uh is curious enough to ask a question they deserve a reward sir
yes sir
record for stuff in his videos do you ever use security hunting or elastic or so the question is do I ever use uh other security tools like security Union or elasticsearch or whatever the the short answer is no the longer answer is occasionally I have used security Union I before I joined Palo Alto networks I had gotten access to the emerging threats Pro rule set and I am a big big fan of security Union so um I have used security onion I don't do it so much anymore but I'll use that in conjunction with the emerging threat opens or the emerging threat Pro rule set if there's traffic that I don't know what it is right and I need to see if
there's any network-based signatures on the traffic to help me identify the malware but uh realistically what happens is uh now I've got access to uh restricted Channels with fellow security researchers where I can just reach out and grab somebody or poke somebody and say hey in poke who pokes people anymore online but uh metaphorically I can just reach out and say hey do you or you guys know what this is and usually somebody much smarter than me will be able to find that out and then I can I can share that information and nine times out of ten it's something that's already posted online but uh sometimes this stuff can be hard to find so if you'd like to come up uh
if you want to get the last prize and I see despite that being the last prize we still have some more questions yes ma'am thank you um
estimated emails yeah of uh you mean just like overall yes I don't have an esta an actual amount estimated but what I can tell you the volume of emotech emails that uh get sent out whenever the spam bot is active whenever the botnet is active telling the botnet post to start spamming all right so what will happen is on a single host when I'm doing it and this sounds kind of bad because what I'm doing is I'm detonating this malware in a live environment uh I'm doing something like tethering through my phone or going over a VPN but these emails are getting sent out now I comfort Myself by saying well if I'm not doing it somebody else is
doing it right but uh you know really that's just a kind of a cop-out but what happens is I can get an idea of what's Happening you know live in real time and what will be happening remember how I said there was a lot of you know hundreds of megabytes of gigabytes of traffic within an hour or two's uh worth of time so if you look at the traffic you're seeing quite literally uh you know dozens of emails sent every second from one single host dozens of emails sent almost every second you know up to that much so there's an ebb and flow to it but uh so you know if I don't shut these
off after a certain amount of time you know they'll be sending gigabytes of data out of spam bot traffic hundreds thousands of emails just from one single host now multiply that by how many hosts may be active at any given time on uh you know either one of those bot Nets and you've got uh you know you've got conceivably hundreds of thousands of messages that are going out every single day that these botnets are active spamming out and that's probably hundreds of thousands just as a general figures probably a conservative estimate in my personal opinion but you're not going to get a good number because uh from security vendors from security vendors because we're all
looking at different uh different uh different customer base right so there's no centralized Authority that's tabulating that information so we can only guess but I can I can give you that as a conservative estimate you said you had another question okay
gotcha gotcha yeah just uh anyone that isn't able to answer can grab me after that you sir with the glasses
how soon after I detonate the malware am I starting to see the spambot activity or the Cobalt strike spam bot activity almost always consistently whenever the spam bot uh span the botnets are active pushing out spam bot 30 to 45 minutes almost consistently within that time frame whenever the the it's actively sending out spam uh Cobalt strike can be anytime so uh sometimes it'll be you know within 10-15 minutes uh other times it could be hours and hours later and uh if I were to ever let these hosts run for like weeks at a time I may be able to give you a uh different answer but uh normally you know I can let these things run for you
know if it's not spamming I'll let it run just see okay when do I start seeing something interesting other than spam body I'm sorry command control traffic and for Cobalt strike I think what happens is when these criminals are selling access to the botnet to other criminals and using Cobalt strike for that it kind of all goes out at the same time so I've had two different hosts uh using two different public IPS that get hit you know all infect them about the same time or even different times of the day and when they get when they start getting the Cobalt strike for example it will be the same time regardless of when I started the infection so I think those
Cobalt strike deployments are going to multiple machines at the same time and it's just based on uh whatever the threat actor is doing to distribute that access to hosts in the botnet you sir in the green shirt okay anyone else yes
how often do I see tiered exploitation I see it quite frequently okay almost uh almost uh you know let's say uh 15 of the time at least yes sir
yes
Microsoft has disabled the macros by default and you are correct uh what we're seeing a lot of right now is uh uh attachments uh that are disk images ISO files and they will have a window shortcut and they'll have a hidden file somewhere on the image that is a Mount usually a malware dll you double click the Windows shortcut the only visible file it runs the malware whatever it is CAC bot bumblebee uh iced ID whatever but I think that's it I will take anybody else's question thank you guys very much [Applause]