Random Problems in IoT
Show transcript [en]
let's begin with a very short brief little demo [Music] so who has not seen that before who has who is not aware of that problem are quite a few who is a little bit worried that that's actually a thing who didn't spot what the point of that video was okay okay so what you saw there was a fully deterministic random number generator running on an Arduino so the Arduino has a very limited space it's an 8-bit microcontroller it's the 80 mega 3 2 AP chip for those of you who are interested and that is actually the constraint that they're trying to satisfy so this is what's going on this is why it's bad what you
have is I think of the linear congruential generator and LCG ok that's the five lines of code top left what that is doing is it's just generating numbers ok again and again and again feeding back into itself and they look kind of random the problem is it's fully deterministic whatever the seed is chosen the seed that's chosen by default one ok so every Arduino will generate the same random numbers in the same sequence if you change the seed you're not actually changing the random numbers you're just shifting it around this whole thing now on an AVR the AVR microcontrollers the AVR is the architecture it takes about two days to do a full cycle ok two days on my laptop
it takes 26 seconds that gives you the kind of power disparity that we're dealing with when we're trying to implement code on a microcontroller versus implementing code on say a laptop or a server or some other production environment now people have said why am i picking on arduino i'm not honestly it's just the arduino are well it's the cheapest that i could find is the most of readily available and also it's got a huge ecosystem with a kind of an ide that's really easy to use they get them out in schools for example so lots of people will you an Arduino because of that accessibility now I am NOT expecting Arduino x' to be perfect people said well what did you
expect it's a $2.00 chip what do you expect it well to be honest I could have been expecting that but the bigger problem is that there's nothing of the documentation anywhere that says this is a thing it just says you can get random numbers and no one gives a second thought as to what that actually means so what I'm gonna do today is take you through what a random number is mathematically I make every apology for my lack of apologies about the mathematics that makes sense think about it and I'm gonna talk a little bit about mathematics now so the LCG has this lovely property in the late 60s a paper was published by a
gentleman called mazzaglia he published a paper called random numbers for mainly in the plains but that's a joke by the way ok that's that's a funny you should tell tell yourselves so the idea was is that he did some analysis and he found that the random numbers generated by an LC G that code over there although you can change the parameters that particular bit of code spits out numbers that fall naturally in a plane or hyper plane as it should be called that cuts through some n-dimensional cube or that means is you can actually slice up this cube and go the random numbers are always going to be here all right and we've known this since the 60s we've
known this technically since before tcp/ip was a thing if you have Miko's talk earlier so let's take a little bit of a step back and let's think about what random numbers really are ok we use them in cryptography I'll come to that in the next slide but we also use them in other areas of life we use them in gaming and gambling ok you have a random number of dice though have you let's spin a deck shuffle you expect it to be random ok you don't expect to be able to guess the next sequence of cards because otherwise you'd be able to gain the system even digital systems have quite strict requirements a 4% win over a hundred million spins as a
requirement okay now to be able to justify that their games will fit in to the random numbers such that this is going to be true all right likewise we use it in science a lot ok statistical sampling for example relies on random numbers ok likewise control group selection if you are selecting a control group for a trial you shouldn't be able to predict who is or is not going to be in the control group versus the test group we also use it in things like Monte Carlo simulations if you run the Monte Carlos elimination twice an Arduino you'll get the same output and if that's what you think is science is probably not a very
good thing so we need random numbers to do Monte Carlo simulations on other statistical simulations in order to be effective we also use it in astronomy and things like where you have a very large data set a lot of it which will look very random so what you do is you generate something that really is random and then you do a comparison okay and that's how you find patterns that's how you find things out even in history and art we've used random numbers for a long time in ancient times back in ancient Greece for example or ancient cultures tend to have tend to have this kind of thing what they have is the idea that
randomness is in some way not humanly control configurable you can't control it if you're human so by casting dice or casting sticks you're in some way communicating with the gods or whatever you're particularly into likewise the ranging Greeks their democracy was actually a sort issue there's a device for the Claire Italian and that would take a colored dice in a tube or series of tubes they'd be dropped into a tray the color would tell you the office and then the numbers would tell you the person that's gonna occupy that office and that's how they did democracy likewise in art dadaism and Jackson Pollock paintings you know there's a real sort of move towards this kind of
random and this kind of feel that we have so this is where they fit into society but of course we don't really care about that kind of stuff what we care about is cryptography random numbers are really important in cryptography when I teach at the university local to me University Beckett University in Leeds I tend to tell them that there are five kind of pillars of man of cryptography one of them is random number generation other ones would be things like cipher suites and then cipher modes is another key management is a big one and trapdoor one way functions for hashing and that kind of thing but random numbers I emphasize they're really important don't mess them
up okay so look here's well how we use them we use them in key generation you should never be able to guess my key ok if you can guess my key I can't keep a secret the way I want to likewise IV or n once I say and once because nonce has a meaning in this country saying so I in n monster generation you shouldn't ever be able to predict the IV like if you were to have oh I don't know a hardware aetherium wallet which had a static IV that might be considered a bad thing if anyone's in the news last week that is a thing by the way if you're generating random salts you don't want the salts
themselves to be predictable so we use random numbers their cookies and session tokens if I can predict by say taking the time of day or the epoch time and some user artifacts and I can then predict your session token or your cookie or whatever then I can do at our account takeover and I can really mess with stuff so if you're generating random numbers they shouldn't be guessable for your tokens one-time paths theoretically perfect security relies very heavily on random numbers so how do we get them well some common methods are on the right here we say write to random number generation these are the things you find in is like TPMS and hsn's okay
little chips or causin chips that do a lot of cryptography for you or they do a lot of random number generation and other things for you so you include the silicon and then you can just talk to it they generate random numbers in a true sense they take an actual source of randomness but that's actually very slow compared to how a laptop might do it so for that we have pseudo-random number generators we've got quite a few actually the old ones of history or this they should be in my view are the LCDs in the lfsrs the linear feedback shift registers these are also referred to as deterministic RMG's DRN jeez that is they'll always be the same but we also
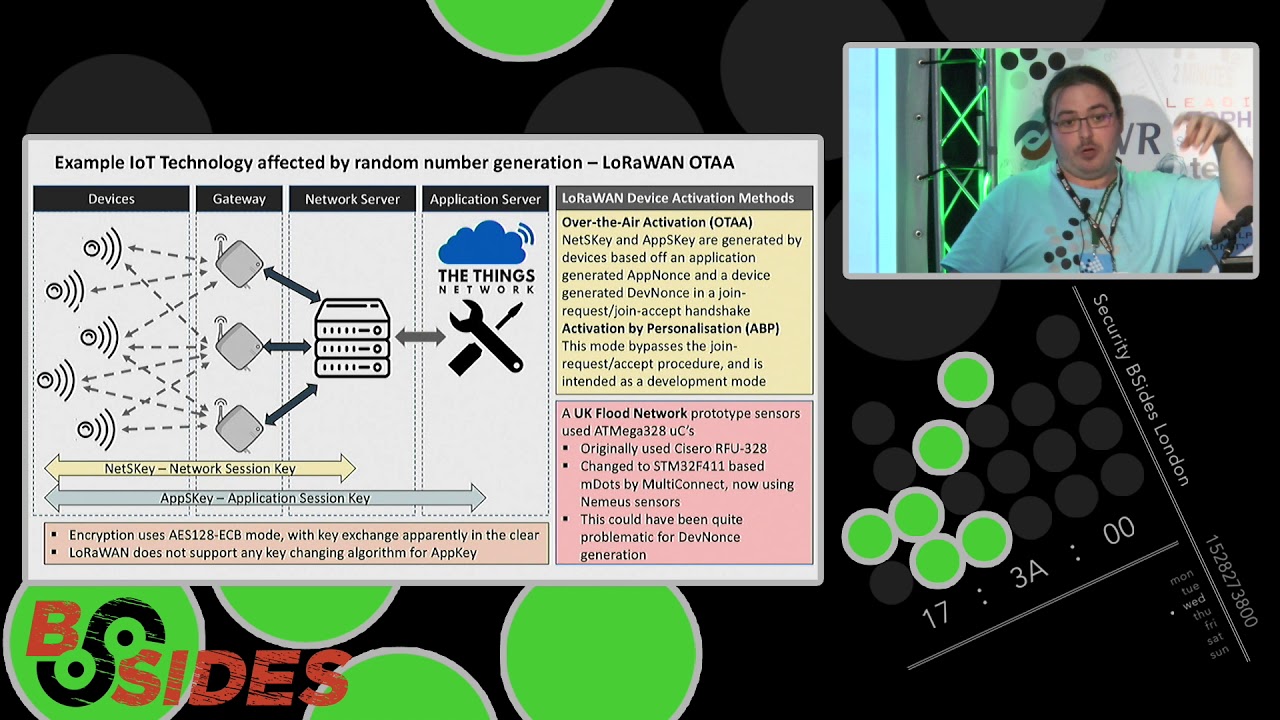
have another kind of subspecies of these PRNG is called the cryptographically secure PR MGS and these are ones where we go okay they have enough of an internal state to one being called cryptographically secure so that no one can ever kind of catch up with that so I mentioned IOT I mentioned this thing in the title why well here's one example here we have a kind of an overview of of the lower one stack using things network as your cloud service notice that you have here a net session key and an application session key what these do is these encrypt traffic from the devices yes the devices all the way to the network server and then that will
pass on the data encrypted with the app session key to the allowed service here you may think well what's wrong well the app session keys are not stored they're generated on the fly in a process called over-the-air activation so a device and once and an application and once are generated and swapped in the clear and they are then used to generate these keys so if I can predict the next random number I remove roughly 16 bits of entropy from that process okay it also relies on a thing called the app key the app key is interesting because things network only require that the app key be either default as in every device has it or they are perd
there's no requirement for them to be per device it's just if you feel like it the answer is you probably should do that so if I get your app key and I can predict your random numbers that might be a real problem there is a UK flood Network where their prototypes were built on 80 mega 3 to AP's the chip I showed you in the demo they've now moved on they use stm32f4 ones in some of them now the mute moved to numerous sensors but this could have been quite problematic okay this could have had some ramifications now others might say well you have a es12 8 in ECB mode that's the bad one but as a requirement
you have key exchange or artifact exchange in the clear and there's no support in laura1 for exchanging the app keys ok you have to do it through firmware update or some other mechanism assuming you've implemented it which of course you have to cut you good devs so this could've been problematic other examples top left you'll see an excerpt from the sprits implementation for arduino this is still the news by the way their best practice but Ino file has this as the entropy pool the first 64 characters of Pi mmm now for those of you who know a little bit of ASCII magic you're probably realizing are that means that half of the entropy pool is zero
zero one one guaranteed no house barred okay that is a problem I submitted a fix which is absolutely bare minimum because I didn't want to start messing with other people at other people's code too much and I got told though we're not going to push that we're going to put a warning instead that'll do it right sitting a bouncer loose young it's not a thing I'll do we know Laura now you'll see a lot of Laura in this in these slides I'm it's a thing that I look at quite a bit because I kind of liked the idea for those of you who don't know lor a Laura is a very long range ultra low
power radio frequency communication protocol so with only a few offer normal sign of battery you can get a range of up to 5 kilometers very easily yes it were it propagates that well through air so I looked at their implementation and I found this lovely little function look at that lower class random it just returns the RSSI for those of you who don't know that's the receives receives signal strength indicator it's just how loud is it the problem is IOT devices don't move the RSSI is going to be static what are you doing I start random ok you can make it random and I'll show you how but that isn't random alright so I mentioned at the start
there's going to be some mathematics to make a little bit easier I have a little visual cue that will tell you in the maths is running okay so when this changes you're safe ok because being a mathematician I get one of three responses the first one is kind of like oh he must be so clever no I'm really sorry I'm not you know when I make a cup of tea and how I had enough coffee then you know sort of its I put the teaspoon in the bin and the teabag in the sink and I put the milk on my head it's just not good it's not good or I get the other reaction of kind of oh I was
terrible at maths at school and the self-deprecation just keeps flowing or the last one and this is actually quite common is I hated maths at school and it's like well is the outpour of PTSD for mrs. Smith your maths teacher I'm really sorry for what you did / like if you saw mass the way I did you know you'd love it hopefully you'll love a little bit of this as well so I'm going to use some slightly unusual notation and definitions nothing too much I'm only going to define things no theorems no proofs nothing what you would call hard or difficult so first of all I'm going to use Greek letters that's what that is
that little weird-looking o is a Sigma just in case you didn't know that Sigma is what I'm going to use to represent strings now the straight lines either side they are actually taken from linear algebra so that does have a magnitude a length literally so this is the string length the next one is log base 2 of why we use that a lot okay because of this it answers the question what is the number the number X such that 2 to the power of X equals y ok and when we do that well we actually get out the number of bits needed to write the number why does that kind of make sense yeah ok cool to to the Omega
is shorthand for the set of 0 and 1 to the power n that is infinitely many from that set that is a thing called the infinite binary string space also called the contour space after some dead German guy so we also use this notation here 2 to the less than Omega that just means finite strings arbitrary length ok arbitrary length so it could be longer than the visible universe but it is only it is still finite in some sense so this is what I want to sort of show you we're gonna build up to a proper mathematical definition of randomness all right I'm gonna build up there quite quite steadily this won't take too long don't worry this battery
is finite so I have to you know keep up take this little game on the left ok the blocks can move up and down they can't go left and right they only move up and down the blocks moving up and down give you lots of possible situations that they can shift into how many situations are there how they I describe this accurately well I have 12 bits I have 9 ones and three zeroes so surely it's 12 bits the answer is no here's why I can take the blank space at the top or in the first position or in the second two bonds a position or in the last position so that's 0 0 0 1 1 0 1 1 2 bits 2 bits
per column DAF 6 bits make so if I have 12 bits in this sense I actually only have 6 free bits of entropy effectively and to be here being the tire state-space and the normally you apply some probability distribution that is there were some states that are more likely and some that are less likely so it's common when you speak to people entropy that's disorder right mm not really I refer you to the work of Lydia Glatt so in Chicago I think it's Chicago University and she's working on systems where the entropy tends towards order and she's growing what look a lot like crystals in simulations by manipulating the energy bear the entropy not the
energy of a system so this is quite important we actually have a name for this in information theory that's what this little equation is here it's called Shannon entropy and it's just probabilities multiplied by the number of bits needed to express it ok and then you sum all that up and you get some sort of measure which you can use all right we're going to play a little game okay there's anyone really not like bananas right your mum if I throw a banana with someone gonna catch it yeah okay one over there lovely can stand up for me I'm one over there okay I just pick up the banana and stand up I have pop-up
bananas if you'd like yes that nothing's gonna happen what I want to show you is this is a room full of 400 chairs okay and I've randomly chosen two people or random ish you know I don't ask first but I randomly chosen two people out of this distribution of people to stand up and those are getting my I my one bits and the rest of your all zeros all the other seats are zeros you can sit down thank you but what if I have n many people okay we're now playing random games can we enumerate some sort of information about this random game and the answer is yes okay what are we doing I'm taking some n the number of empty
buckets and I'm choosing two of them and we use this this is called the binomial coefficient and I can define very rigidly what how many possible games there are for a given n of game of two banana throwing okay and the answer is N squared minus n over 2 which is expressible here as I need this many bits to express this number and then I can address every single game in the space okay so although it looks very random it's actually a very small complexity compared to the overall space of n there are other things I can do I could measure for example the whole length and I could say to coordinates the white space on the left and then the
white space between the two bananas and then I can say well what's the biggest number I can have it's when one's in the middle and the other ones at the other end because then as this one moves this way this number gets bigger but this number like for light gets smaller give or take okay so actually I only need there to log to log base 2 of n over 2 which is basically twice times the number of bits that are caught to describe half the space notice how a random gain that have very little meaning and may or may not be a contrived example has given us some sort of information about a randomness which
we can then move forward with what I want to get to is this this is common go of complexity so we're going to deal with universal turing machines who's heard of those before anyone okö billion so the comma go of complexity formally is you say what is the shortest input to that search that the machine will run and it will halt and it will output the string I want okay that is the question you're asking it actually makes sense to say what is the Python comma go of complexity you'll notice it goes from C to K that's because there's a thing called prefix-free comig of complexity and that's actually minimal across all information content measures that's a
proof due to Chayton but I the reason you would want to have prefix-free says okay prefix-free set is the set of phone numbers what they've got prefixes and not quite what it means you can't take two phone numbers put them together and get another one as in no phone number is a prefix of another so the set of phone numbers is prefix free that's all that means easy easy easy so let's ask ourselves some questions then these are three strings okay how do they end Oh 100 100 100 100 100 101 exactly Oh 1 100 1 100 1 101 exactly okay easy how about this one 100 100 100 0 100 101 101 oh 1 100 100
101 1 you don't know this this song oh no no it's not it's oh oh but good try so here we actually have three strings I'm gonna call the third one random will imagine it keeps on going forever that's required and I can write these very short little programs and will reproduce the first two strings but I can't algorithmically reproduce the third string with ease the easiest way to do it is to just write it out and that's the intuition behind comig of of complexity the shortest program to produce a string if the string is complicated enough the only way to do it is to print the thing okay and we have a name for that it's called C income
possibility these are all things you can go in Google later it's absolutely fine I will answer questions with beer for hours about this kind of thing if that's your bag come and speak to me but if we take any finite string Sigma we can ask well is there a string C is a number C sorry which will keep the length of the string under its complexity is asking the opposite question okay but if it can I claim that the string is long enough that whenever you process it the only way to generate that string is just to print it out so intuitively we can't do better than producing the string with a print function of some kind
all right so comic incompressibility leads to this this is a mathematical definition of randomness okay a string is one random the one refers to the cheering jump of it so two random is above the double jump aside below the double jump and then three unknowns below the triple jump and all that sort of stuff it's one random if I can take any initial segment and that doesn't give me a clue as to the next bit it's always gonna be seeing compressible okay the whole infinite string there was a finite number see that minimizes at below its complexity okay and that string can effectively be zero if you want this is where we're going okay this is actually used the owl's
next bits test is based on exactly this idea and it's equivalent a lot to another very important notion of randomness called Martin loaf and of us but ultimately that's all I wanted to do there's a little summary entropy the measure of a number of arrangements with a probability distribution complexity is basically the shortest string that we need to reproduce some other strength and randomness is a string that doesn't have that can't be squashed into an algorithm okay it can only just be reproduced and that's as good as well as good as you can do if you're interested in this stuff and you want to keep reading there is a handy one thousand-page book called algorithmic
randomness and complexity by Downey and Hersh fault that I can thoroughly recommend if it's not your thing we'll leave it there okay you're now safe so if you didn't understand that you probably shouldn't be talking about random numbers if I'm honest with you but this is the kind of stuff that's going on relatively sequential definitions nothing that I think is particularly hard maybe a little bit mind-bending at the start but this is actually stuff that we can understand so what are we doing what I mentioned Arduino and that's bad well what's good what is good look like I claim this is what good looks like okay who thinks this looks relatively uncomplicated good I think it's very complicated I
think that's a good thing this is the Linux random number generator this is how you get random numbers out of slash dev slash random or slash dev slash you random if you're not fussy about blocking okay notice it has a lovely little bit of stuff to measure the entropy so we're now calculating entropy okay I feel like a weatherman doing this when are calculating entropy now when it falls below a value were to pull some out of the entropy pool that we've been managing with this little bit of circuitry here which is going to then make sure that the probabilities are as unbiased as possible okay I won't bore you with why I think you had enough of
that but this is what good works out now remember those five short lines of code took two days to fully cycle on an AVR compared to 26 seconds that gives you an idea of the order of magnitude of lost power by moving from a laptop to a microcontroller you're never gonna get this I claimed on an an Arduino well you can but you won't be able to do anything else with it and it might get a little bit too steep okay so what are we gonna do what can we do well we can do this we know the fundamental idea is take some entropy pull it do something with it to make sure it's there and then seed a
pseudo-random number generator that's a lot faster usually and use that as our random number source on a micro controller now do we have better candidates yes we do sue demanded number generators that are could do currently secure things like salsa 20 that has some acceleration if I remember I've seen support for cha-cha 20 okay someone really likes their Latin American dance ISM the Gimli permutation engine named because it's really short that's using live hydrogen that was developed by Bernstein that Al and that is optimized for use on embedded systems so we have better permutation engines for generating these numbers but what we don't have is a thorough treatment of entropy sources and therefore that are
usually kind of fingered as being very good priority the first one is the watchdog timer jitter thermal noise from an ADC and analog/digital converter RSSI noise okay so the noise that you can get out of a signal strength value and thermistor jitter there's always a little thermistor on a CPU in our inside every microcontroller and that one is there for making sure that if the chip gets a little bit toasty like I mentioned it shuts off and saves itself it doesn't set fire to the building okay so we can use these sources but I couldn't find when I was looking and I did try maybe I was looking in the wrong language or something if someone knows I mean I
don't please do let me know but I tried to find a thorough treatment of this and I couldn't really find it so I decided to say why what do we need so we have these things reference the top left here's what we need I think a simple testbed for assessing entropy sources all right if we can do that we can get a like-for-like comparison across lots of different sources and we can do it between microcontrollers as well okay that I think is a useful activity some code will get as reasonably good random number sources and others will give us very bad what we should be able to see that I always want to look at things
like speed okay I'm memory is cheap so I'm not too worried about size but it tends to be small anyway I'm worried about speed okay if you have to wait half an hour to get entropy that's probably not practical okay hence you know using a four-year-old with a big button isn't really gonna work and I also want to measure like how many components you need to add what's the expected cost not just in code but actually in the Bill of Materials okay how much is it going to cost you to implement this so we set up some sort of test rig and to be gathering some sort of pooling some processing the functions called extractors what these do is they
do a little bit of what's called whitening it just sort of flattens out the probabilities a little bit such that you can get better and rupee out so an entropy sauce that you're reading might sink two zeros or two ones every now and again and you don't want that you want to do something to make sure that you've got a better likelihood of having a decent or what we've got a fair random bit and the output of this is gonna be we can just plug these things into random number generators and then we get proper random numbers and for a set amount of time then we receive okay they've honest with me so far you can
probably hopefully see that the output will be quite useful we can say this is good and this is bad and here's why because it did this in this test and it did this thing that this in this test and this one doesn't have any components but it's faster this one's really slow requires you know sort of a supercomputer we can make informed decisions and make informed assessments about what's going on so this is what I came up with this is code that is more or less lifted from POC or gtfo oxo one is fully due to Dan Kaminsky gets full credit for all of this he was looking at clock jitter on JavaScript as a
randomness source and it was found that actually it isn't very it isn't reliably good there's very in Firefox there were various phase locks where the clocks would get reset and at that point you would kind of either be able to predict or would be able to guess reliably what the random numbers are going to be but this is actually a very good test ring so here's what you've got you got what we call the coin flip so we're gonna get a bit okay a 0 or a 1 get magic is just something that's going to give us a bite and I only care about the LSB okay I can also change it to only care about
some bit in the middle or the MSB or whatever okay but it should be extensible enough that we can actually extract out what we want it's a test that is I want to get a fair bit now this is interesting this is called a von Neumann extractor so we take a is a coin flip and if a is not equal to another coin flip we return a that is if we get 0 0 or 1 1 we ignore it if we get 0 1 we accept it return 0 if we get 1 0 we accept it we return 1 and it might look like well what's the point in that there's nice work on the perimeter and
the extractor by von Neumann where it shows that it kind of it tries to get as close as it can that the probability of 1 and probability of 0 is as close to 0.5 as possible by minimizing the bias okay and that's what we're that's what we're after and then the last bit is just to make a bite out of these coin flips okay so this is the kind of setup that I used very very simple it will install and compile on pretty much anything we want and it gives us a reasonable sense of what's going on in an entropy source this is what I did ok first thing don't ask why this is soldered the wrong way around that's a
very long story likewise you know sort of don't ask where the paperclip came from I don't remember that's why but yeah so here I'm just using a capacitor and a resistor I'm charging this little circuit up on a pin a digital right of Wang to the pin that I'm reading it on a 6 which is what that code is saying and then I'm just passing this output into my basic burst Kaminsky basic generator now this gives you reasonably good random numbers and it's very slow compared to the others okay when I first did it I was quite pleased I was getting what looked like decent entropy however it was taking 4 vertook button all right so it's very
slow now that could be because I was using you know through-hole components maybe if I tried it again with surface mount components that might be faster because that's where you know thermal properties are propagating less maybe that's involved ultimately I decided you can use it but here's the real problem you have to add traces to ground you have to remove the use of at least one pin for reading one ADC pin and those are valuable that are gold when you're building a device and then you also have to you know if either power it in a controlled way or have something that will actually allow you to send a signal and then cut it off and all that other
stuff so overall it does work the people who are saying it works they are right but I don't think this is the best option okay so a DC jitter not that good the next one was watchdog timer so there is a a load of forums and indeed an Arduino library on github which will get entropy from the watchdog timer jitter okay so as the water timer runs the copper generates a lovely little bit of jitter for you and that is random okay because jitter generally is a random thing however I found a problem as you can see here this was my fourth attempt it is and this is the start of my second attempt at it okay so I've seeded a
random number generator the LCG in this case and I've just fed it and pulled these numbers out and in case you haven't seen it they're exactly the same this is on this is on device reset okay this is the problem when you reset the device and it makes sense when you think about it when you reset the device the clocks reset so the jitter you built up the jitter a lovely wonderful excellent jitter that you found has disappeared it's evaporated okay you've basically done away with it so I wouldn't recommend this because it's very very easy to trigger a device reset in fact ironically one of the ways of doing it is by invoking the watchdog timer
but nevermind alright but yeah so this is actually a lot is said about watchdog timer jitter and when I first put this out on Twitter saying I want some entropy sources from people I got recommended this I think more than any other and it does work not the fastest but it does work but it takes about a second or two seconds which in microcontroller times Andy Fox is an absolute eternity if I remember rightly I think it's automotive that has a requirement of like 400 milliseconds from like sort of power up to being ready to go like it's quick okay and you have to solve that problem now maybe you could take this one and the previous
example and say well what if we store the entropy and then on reboot we recover it and do some permutation and that's fine you can do that okay that would work and that's what's done on other microcontroller systems however I found that the next two were significantly better so I want to sort of have a look at those so the mister noise on an Arduino you have eight pins for doing a DC a zero through a seven there's actually a hidden pin inside that is the ADC for the thermistor and you can read it this is the code to enable it this is then passed into the basic kaminsky generator and I did my assessment the code will be available
after the talk so everyone I want people to sort of go home and either tell me I'm wrong or something oh my god everything's broken but yeah so you read the thermistor and what I did was I take the LSB of that okay because I'm looking at the tiny fluctuations in temperature okay the point one or point two degree changes because that is going to tell me I said they give me better noise it's not going to tell me what the temperature is I don't care it's gonna give me better noise source than looking at the most significant byte which in most cases again will change but very slowly as the device slowly wore up or cools down so I took this and run
it in and it's quick okay it really does work got a big advantage as well every CPU more or less has a thermistor in it although I'm yet to find one that doesn't okay and in that sense it's very easy to find the code to access that value and then you can use that in your entropy pooling and that's a good thing and it's quick and yes if you breathe on it the numbers come out faster okay that's usually a good sign my neighbors already think I'm weird so the sight of me breathing on microcontrollers in a window was probably not that unusual for them but anyway I digress so this is actually I think a thing that we should
use okay we should recommend this as one of our one of our sources of entropy I didn't have any problems implementing this but I did for the next one because I'm looking at RSSI annoyance so receive strengths a signal indicator so I receive signal strength indicator sorry is common it's in the I Triple E standard every I Triple E 802 11 device has to have some sort of RSS I output okay so again if you have a radio and that's the big if if you have a radio then you can ask it for the RSS hi for those of you who don't know maybe not fully afraid you can have radio cause on a chip actually built into the silicon
or you can actually get a core which what I did I actually use the nee SP 32 based hand tech louver device sorry wrong one I know but I use one of these devices and I programmed it to give me the output through SP is this is now similar sort of code running on an ASP 32 this time modulo clock speed and modular few other things the code is comparable it speaks SPI to the chip it asks for the RSSI value by saying read me the address and the address translates to a register that is the RSSI value that the chip is updating all the time and I pull that back using the lower dot random
function and then I use the LSB of that why the LSB well it's accurate to a 10 point one of a decibel okay so even in a very static context where you're your signal strength isn't gonna vary okay it's not going to really change your IOT device unless it's on a train I know there are devices on trains but unless it's not on something like a train or a ship or somewhere the context changes then it's going to be relatively static but the LSB will change because the signal strength will move as someone walks past with Wi-Fi on their phone or someone sort of knocks it to the floor will probably have an effect for various
reasons I don't know why but yeah you can see that actually this is a very good source it's very very fast only if you keep asking it for RSSI values some chips just fall over they just go nah too much mate Donna you know it doesn't return than ever it just stops responding you know so that's not probably the best the best source but I think that if you took this particular example and the previous example I think you'd actually have a very good kind of metric and matrix of potential energy resources so this is an overview get slab github whatever link is gonna follow I'll decide on one or whatever depending on what people are saying and
I've done some articles about this on medium and here's a link also to the NIST specifications on this yes NIST have a specification for their entropy sources and these are the results okay hopefully this is now kind of fairly obvious okay so I managed to split them in two well this'll be fast I'm relatively slow which was one of the metrics I had if it's slow for me that's worse if it's faster for me that's better also I prefer not to have components okay I would prefer to have no impact on my bill of materials for a device because that's the first question I get asked whenever I do security for an IOT company right what's the cost and I have
to give them a physical cost as well as all the development costs well if you have to add an HSN that's expensive when you multiply it up by a million devices okay that's a big effect on the bottom line reading thermistor noise that's fine that's that's built-in anyway likewise if you have a radio call and if your radio core is either built-in or if it's not built-in then it is gonna be kind of associated to the chip strongly or it comes on a little bore little module then you can ask that for information and then feed that into your mantle number generation so I kind of color-coded it to make it sort of obvious mainly for me because you know
I'm something here giving a talk and didn't want to get it wrong but but ultimately this is this table of results so far so far I'd like to continue so these are kind of more closing remarks I didn't want to keep boring you with lots of mathematics I'm a long haired Scout so it's bad enough as it is but what I wanted to do is just give you some kind of idea of what I want to do next okay so the conclusions are fairly straightforward the problem is not limited to AVR okay this is a tweet from under taenia pentas partners where we found a device which on factory reset would generate a key within a thousand
resets there was a key collision this is real this is happening that shouldn't be happening okay we need microcontrollers to be comparable than unlike for like manner I would hope that this is moving some way towards that goal we also need to look towards improving random number generation across the board there were some very good valid number generations I want to call out for example the ESP 32 chips the ESP IDF integrated developer something whether they're basically their SDK includes by default lib sodium yeah Lib sodium and it also has by default a built-in HSM with native AAS 1 to 8 support in a chip that is marginally more expensive than the esp8266 which is very very popular
I actually challenged the guy I said well what if I can get a key out off the hsm and he said on Twitter and I think is on the website now he said he put it there tell you what I'll give you three and a half thousand dollars if you do it straight up putting your money where your mouth is you know that is unfortunately an exception to the rule if I could have something tomorrow I can have my Christmas early okay what I would want is simple I'm not expecting Atmel or microchip here on them to change the silicon on a device that is a big ask I'm not asking for that I'm not
asking for things to change in the SDK even if I can have something tomorrow I would just want a warning I would like the words not cryptographically secure to be in the documentation because if you read it you would think it was secure unless you were thinking in a more adversarial manner which of course every developer does as we all know that was a joke as well anyway so manufactures need to be held to account this we need to start asking them questions why are you not doing this or why are you doing it in this way and developers also need to be more aware in security we talk so much about the who and the what and the how we very rarely
talk about the when of security if you have a long rapport with lots of things in it if you're a consultant hopefully you break it down and say these things these things first these need doing by Tuesday idea okay fact they need doing by last Tuesday but will give you a week and then you and then other things can wait right but that's that's not necessarily all that common I'm sure everyone in this room does it but I've had situations where it isn't it isn't manageable because there's no when when do I do security when do I make these decisions okay we need to be more honest about that kind of thing with IOT your
cryptographic decisions need to be made when you choose the integrated circuit you're going to be developing for because cryptography is very hard to do backwards on a microcontroller if your chip doesn't have native support for aes-128 adding it in yeah you can add the code but you saw what five lines did okay how long compared to a laptop you're just gonna make it harder IES was chosen our rijndael cipher was chosen because it had good optimization in hardware ok so if you need cartography identify it early and then make your integrated circuit choice then based off that decision amongst all the other things you're looking at because you can't do it backwards you can't do
it later on it way you can but that's expensive and very very difficult so future work what else do I want to do how do I want to take this kind of project forward well I want to keep analyzing random number generators I have one of these infinite noise dongles if anyone wants to have a look at it that's a very nice design using operational amplifiers and compressors and or audio circuitry analog circuitry to generate random numbers into a USB dongle I want to see if I was good enough I would look at other potential sources of randomness and noise that can be fed into either IOT like if you really want really good and to be sauce
here's a really fast little circuit you can add and it adds this much to your Bill of Materials but I also want to start saying well can we extend the test rig to include entropy estimation an interesting point about the NIST such a set up their specification is doing things that the von Neumann extractor isn't required but doing things like entropy estimation is that is necessary that's actually required part ok so if we are being honest with ourselves we should also think what can we add some entropy estimation in is there a fast way of doing that if anyone's got any ideas do let me know I'd love to hear and then use this information get gather
a body of information put it in a public place and then go you know what here is what is what you have here are the tools that seem to work and then developers for things like live hydrogen another really good project that works does have a lightweight version of live sodium they've already spoken to me very briefly but I've been really busy so I haven't been able to talk to them I will honest but we can use this to inform our development of co-development of libraries to make things a little bit less well crap okay that's it I hope it wasn't too much mathematics thank you very much for your time eyes ears and patience thank you
[Applause]





