Don't Google 'PowerShell Hunting'
Show original YouTube description
Show transcript [en]
[Applause] all right so thanks for the wall walking we really appreciate it both myself and the Shawn I are here so at the or you can see top of our talk is called don't Google powerful hunting there's a little bit of background talk about that in the the actual presentation next slide please so this is our general talk about the soul one really why are you here and spending your time with us for the next hour or so stay tuned thieves in a response for PowerShell and then really kind of the Bullock he's collecting artifacts and what we're trying to get at where potentially someone else and take it forward as well next slide please so who are we so
myself my name is Rick I'm also a retro technologist right so so forget about the future and that's what really kind of you know drives me keeps by by PacSun when I'm not doing computer stuff I'm working on ancient technology in in terms of what we look up today so be looking for his cameo role as a Gunter in the upcoming
[Music]
[Music]
[Music]
[Music]
[Music]
[Music]
all right so here's one of our of our top couple of things we found in our current job is you know Marshall that's what come through the knee right so we start we start my go-to move is let me go straight to Google and just drop some terms in there and see what comes up and so Google PowerShell hunting with PowerShell and so it's a lot of different but what we're really looking at is how do we of what our cell was one on the host to kind of say okay this is maybe patient zero in response how to determine you know what Power Cell was used to exploit that system and it was not a difficult
for us if I find out says we got a probe the name of the toxin you know Google powerful hunting because it means you may not want is hard right so power kills the goats you language burger for the adversary colossal mantissa don't want to live final asleep and they want to make sure nothing touch of the disk as much as possible so we see that our funding part is it's also but the next piece like I said is we really want to get to that the silhouette of our body is going to determine what Power Cell was wrong on top of my system and that the next has the you know we were able
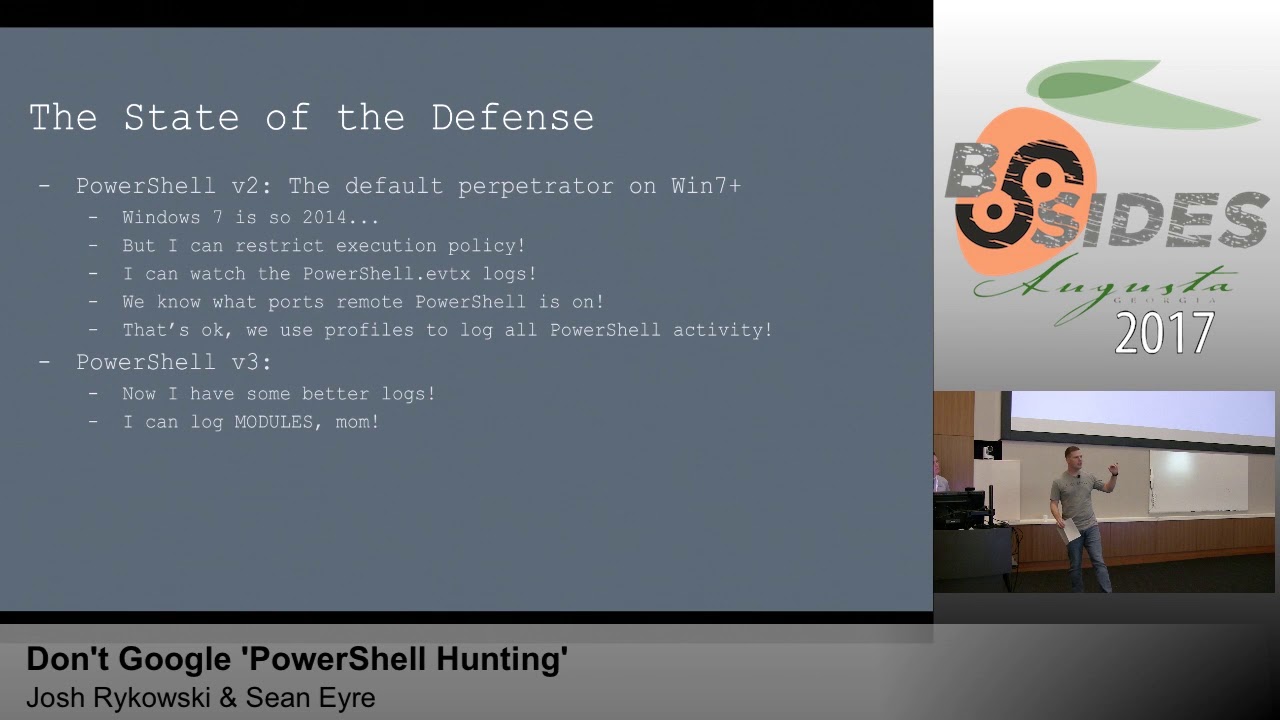
to do that and hopefully we can take the picture that we gonna do that in this level we wanted to make it scalable right so happy want to see if we can go ahead and take this and build for our talk here for a research overall is to find a reliable method to locate post execution artifacts and including ourselves script text itself because that's really I'm looking for that'll tell them what was actually what occurred on the system with PowerShell exactly so I'm not the Sean Chris the state of the defense alright so obviously
so system management automation is the dll that does absolutely all of the heavy lifting for even so the defense who has been in an environment where PowerShell is active for all of its users that's you yeah a bunch of fans right who's been in an environment where command hompless disabled for all the users the power shows completely demonstrate so as we actually see this a lot on top and we typically here where we camp walking is their identity which is also typically true it's the important reality of it work but worth fitting in is power so these attacks is it's a management automation framework not simply a shell so we can't just turn it off but there's a lot of things that
we can do to begin to harden against it so powering through the slides attack like you did is available to everybody you've heard of power sploit for and they allow you to use power shelves the basics to launch attacks and in precision on citizens BIOS Lee as well as using traditional running through if you really want to learn some cool stuff about this for free jump online go to call security weekly on YouTube or look for the text segment that Carlos Perez talks about the basics of infusing W my MS and you'll see just how dangerous the final point on there when we said skip DT is just call out these again they're in the platforms so whether they so
starting with PowerShell version two were to walk away off the verge of five what you do so we all know that Windows 7 has been running since 2014 and now they wanna cry so is that nothing else did right excuse
so a lot of what we see is people going to the first Google hit how can I decide our dough your first day is probably always going to be execution policy right so there's like five different ways to restrict education policies and the probably most common one is to straight go straight to where you can't run any surpluses on the machine whatsoever with about ps1 files this is so often times user controls are not set up properly and in literally typing command execution policy buybacks are started the argument execution falsified us when they're running in particle threads like PowerShell da/dx attack execution policy space bypass straight down right in this you set it to co-sign
boldly or no execution all five different settings whether is that I'm a brute policy with a local computer policy to bypass offense man if your users if they are so turning-point notes we have a ton of different anything what happened running through Scientology [Music] but the art you know that weekís profiles to the established transcription with PowerShell v2 and ah but the problem is profiles are just PowerShell scripts and they're editable on the computer so if you're alive attacker you're gonna go in Danya control de and look for the command start back transcript you're good see it's there you can do this on all four the basic profiles really fast and again anything we can do for the two
most of the admin privileges are gonna allow you to bypass it now some of you were thinking what about things like app Locker and cisco on other stuff like that to help out of it we're gonna cover that in a couple of slides b3 gives us some better forensic logs that we can actually use so we're actually starting to move forward there's not a whole lot to say and counterpoint to what the advances v3 made it's just that they're not quiet the logs we need to do well x Leptis then we get to be five and we get really excited because we finally did it right so now the windows audits scripts for us and stripped blocks for us too so
with the introduction of the anti-malware scanning interface ante third bullet slide there you're actually gonna see when power tools run it if you run three entity they look for something that might be suspicious than anything that windows finds suspicious and can't be tuned on top of that is going to be log in to your event on top of that you're basically more of it is going into it as well as the fair tax code and this is all stored in your panels we can also turn on system-wide transcription and the enterprise is where your admins use this a lot it's going to roll really fast right but at least you might be able to catch something but
the a kind of point all of this is the way that dot networks so this is the kind of depressing point when you install the new the old version is not
so the long story short the most three different top screws is this is a really hard thing to the bed defense in the devil is hard to create a defense based on the automation framework though this is the key point here so anything you do is gonna create other artifacts so if they're precision for W my object creation and we just talked about some ways 5s reinvent laws but there are other things you can rely on yes operational logs for win RM so anything that a powerful building is going to produce is going to write up a winner and that's been produced when our an operational loss
No I can use a public blog pious ones for you Brian okay that's not gonna stop someone from using the interactive mode I can blog show that ABC that way and I can also go ahead and uses a DLL that it was a feather collection and that third one is actually we're gonna watch a movie if you want to use a lot apartment defenses be cut again specifically wanna beta so there's block okay wrist decision regarding the price but by authoring and you'll see any time to explode on top of that if it gets side loaded into a different extra cubicle that's not sign up over notice you look actually generated for basically start in there because it will actually based
on the this is how your surface tablets actually lock this down to power so it's not as strong constraint language both raw power shovel about half its power and you can go in so then we pass it off to looking at all right so like I said when we first started looking for that's we need to system stores if we should sell anyone else you know [Music]
[Music]
okay so from the now we're gonna go into what normal looks like another anomaly in the entire experience really we would into winter honest memory space so you can actually parse when are into memory space for you've been in graduating scribble and it will return you don't you know it's cripples life because if you go straight to that within that memory space um so our garment that we did experiments on so we want 64-bit we were running with PowerShell version 2 that's reasonably good bad power sellers in juice most common denominator comes on default was Windows 7 so a lot of enterprises still running Windows 7 hours of version 2 is the most likely to
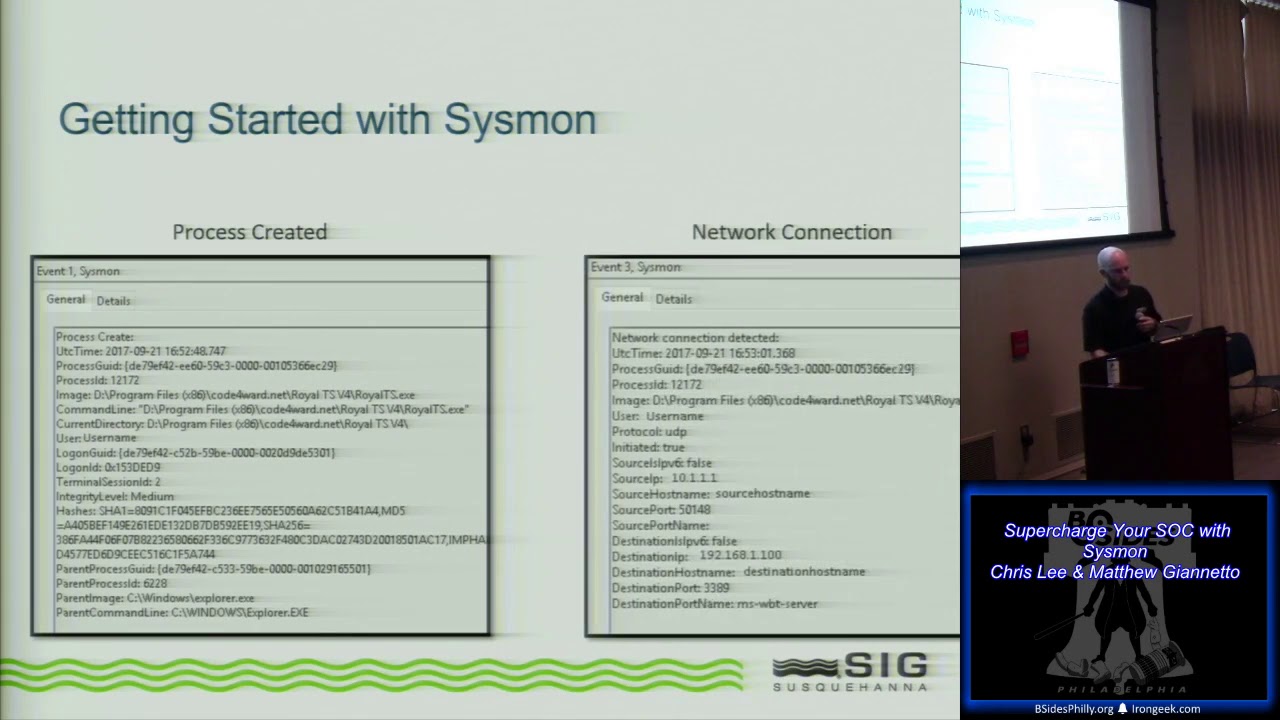
be encountered in a while it's the same reason why you never looking at a 32-bit know when you first started studying reverse engineering because that can still run on Scooby 4-bit systems and then a lot of versions first and foremost user clicks power agility achievement that part and it popped open shell I started without then you look at one we also look at that from them running a ps1 from within a shell and finally we built a deputy my object it actually used a so all the ways we build our persistence were injected in biomass and also the next slide please so now we're going to process readings but you know like someone asked a
question you know you need to know what normal looks like so go grab a Sam's poster the information on it I definitely recommend that so this is the same name so when you use your excuse me I'll have ABC from the desktop just opening the interpreter Explorer is going to spawn power jello taxi and it's gonna spawn zone this is on Windows 7 specifically on Windows 10 these mean take a little bit but overall the process freeze apparently very consistent mostly what's going to change on Windows 10 is where compost is going to spawn a PowerShell WT and click inner and so Explorer is correspond command obviously the commands going and you'll see this is pretty consistent across all
different contexts so will spawn command WC which will then run see you another to say you can just double click on I'm going to reintroduce see me into that and because that context has Omaha suppose you'll see Carlos spawn and under due process one from the PowerShell command line in next like this so we went into is going to call the actual specific so then Wow basically true run this evil infinite loop exam instead of that so if you were innocent as Connor can you find me as a right front of a screen and use arrested respond this task every 20 minutes and this is where actually kills the previous version you want to see what's service house
looks like what services everything's ready a minute so we trusted all you guys to find that on Google and on other sorts of information so services that would actually want PowerShell C and then C is our assessment spawn when execution starts in creating constables this is assuming that you even window visible obviously these are very simple cases of recovery and attackers we do a lot to make yourself a lot more discreet one obvious they can hide it with us they can make it non interactive all
running out of the registry this is my
explorer.exe powershell CS RSS spawn spawn host is pretty cut-and-dry this is what you guys see I never knew we didn't notice if you're not experiencing tarshell the strings would kill you so in streams and single quotes for all strands that's above your esculent SK key or by your safety so to get this running properly at the strings to stop kicking my butt since I all basic bird started tuk E&C for him in
this sliding after you know a fifty twenty eight twenty nine articles bear hunting embarrassing arm it's and they talked about twenty twenty nine things in this specifically so fancy very cozy bear funny but so women then it spawns this its spawn services XE which service those things now w mine PRT SC is gonna do all your heavy lifting for your WS and PowerShell running out of the WMI context is actually going to spawn right there and then console votes is still going to spawn even if the window doesn't printer so what we end up doing is crushing a command line event consumer into disseminated movies which is how this all works on the background and even though we didn't say to hide
the window that when they're never rendered but it still spawns out this will in the processor so here gonna mom is for our last question if there's that wait till uniform I'm case we're gonna come back and it's but giving up this really alright next slide this myself yep memory artifacts so there are some first thing we discovered doing some some googling we actually found that which is a big fun because what if you can find the entire process you can read exactly what the attacker or the administrator did however scripts are not reliably starters do energy to read it so look across all memory and pull every single powershell script out even though you know the powers have a man is
a typically burp now in structure that doesn't mean that you can just be like Oh everything's going to be you know a verb of three words long attack whatever if you try these records on this trust being a lot of faults so we found two things as we started verifying this really versatile if you run a base64 encoded command that command is going to be a memory and then you interpret a command basically the unpack script will be a memory as well and then you're gonna have other copies of it in any in format where it started interpreting is running you're gonna have to plain text strings that are always there and we're using I'm gonna say always even though
it's not necessarily true for the second point system management of automation because it's going to be imported rest table will always be in a process that string and link extreme will always be the process this is the basic concept that makes using strings to analyze processes but it's also going to be mentioned everywhere within that process style powershell will be there if powershell is used to run it and probably be there for most context where it's not because when the console will be imploded there's always help information in the background that could be referenced and it's kind of similar to Free Willy so the silicon memory most of the time but we don't have enough
confidence to say with you all the time but even saltier is what if this script is actually terminated so even if it's been hidden from the process execution block we know that our forensics tools never live to find ones that are still allocated and we also know that the factors can completely gonna alligator attacks from running memory because then it will get overwritten no crash so we wanted to look at post exploitation and say what if the script is completed what if the process is terminated can we still reliably pick up these artifacts from memory next slide please so this leads to semi reliable collection so as we already said you can't you can't target descriptors know
nothing about if you want a little for PowerPoint or PowerShell Empire and no more you can collect all the module names all the commands and you can search across dynamic memory for all those strings and it's not gonna be plated it's not really giving memorize where the one machine is gonna take you forever today so those are pictures no you know no you know something about but if you know nothing about what the attacker did you can't reliably target a spirit off it's just no information is there so we go that's a case that we've got to go after the stuff we know so here the me here so we examine randoms and we look for
those two strings we've talked about in previous life and basically we just kind of pulled samples out of memory we'll be in the area surrounded so we paginated the RAM and then we you know pulled out the artifacts and we looked at in a rather naive order to see what we could learn from so we see is basically if you pull out the artifact system management automation well we found it that we didn't always find the script we pulled out based on PowerShell we always found the script and then we could use an overlap the two x divided by discredit and restage it together again in a 94 de we just kind of swapped it now so you'll be fine so you're using
those two artifacts actually enables you to once execution has terminated you can go and still use those two artifacts to grab enough memory to find the scripts that were running however this is not super reliable primarily because you're stitching the process blocks back together in the wrong word or possible which is what the last poll is talking about target on the order in all right so to kind of pick up so that's that's where we kind of you're starting from the top down right so we're looking at the process the process behind the process and you can dump the memory of that process monitor processor and then total Constance about process currently whatever other we just didn't have
chance to finish overcome by advantage from life and want to work and whatnot is the tool that will work from the bottom up so basically looking for some of those standard you know looking at the so we're trying to work up we're trying to find it in memory and then use that to work up again we're trying to be trying to get to the point where it's a easily reproducible process and then it's a scalable process because right now you try to go out and do this for so the VM we're working in had two gigs of memory and so even then it was kind of cumbersome we go and do that search in the memory but if we have a system
that's there - tell me a lesson waiting for that to happen so we're trying to you know again not going all that all the chat essentially and get down to what we won and then essentially volatility or develop a third workflow exactly not sure how to proceed yet on that once we get the tool finish then we'll work on getting it embedded into volatility or recall taking it to the next step right now we're trying to be awesome some words in there the next step is products are not volatility but PowerShell carved out someone spaces you don't want that you use PowerShell speech there's some triggers off of that we can look at first time here for
PowerShell so that point this concludes our presentation we wanted to see if there any questions or any comments you map for us as we move or like I said we're not they're not quite done working the tool yet so any feedback is definitely good feedback programmer so I haven't actually gotten into books what I'm doing right now I'm actually going to Carlos Perez's dark for news class for the dirty thong next week the slides that he does for that box as wells for the DEF CON gives you the DEF CON of blackhat one orbital online there's about a hundred and fifty slides in the desert and anymore and there's a lot of really good detail in
there about the basics of how it works even if you can't hear they're pretty close to you so we go there honest github go check it out I think it's good huh past dark underscore operator it's one of the two and past that he's got a couple good talks that are out there for getting familiar with it I would also check out I think it's magic braver my big mispronouncing his name he's got a lot of good work out there on it and then she's a guy let's read this guy's name I can I can look it up for you afterwards there's another guy that I follow on Twitter it is a lot of work with power sploit
empire so a lot of how I've been learning this is looking at attacker methods and then finally reproduce them without framework to do it for me so that's I I need to double check but I believe the answer is yes I think especially with the higher versions of PowerShell there's there should be an event blog that actually keeps track of that getting changed and I think on the lower versions of my text that's actually tracked by the registry so it should be track as the numbers escaping the event log for registry document
i Sean that caps the third name I was looking for he said yes sir so we ran out of time that was gonna be our sixties case and we got bogged down memory forensics and honestly like we realized we didn't know as much about memory forensics as we thought we didn't have to relearn some t6 so we kind of dove into the tool of designing a framework for actually building the tool it did not go to that risk it's so important I'm not qualified to be gone in detail in our questions Wow awesome so we've got one more giveaway here and the question is mine to ask and so I said
the original levels are there
[Music]
[Applause]