PG - How to Escalate Privileges to Administrator in Latest Windows - Soya Aoyama
Show transcript [en]
and now we have sama with how to escalate privileges to administrator in latest windows today I will give a presentation about how to escalate privileges to administrator in latest windows first let me introduce myself I'm sorry Aoyama I'm security researcher at who did the integration food system integration laboratory limited I'll be working for little more than 20 years a software developer of Windows I wrote a nice dry but Brutus profile with Jacque application and more I've studied security research about three years ago I am very happy to make my presentation today my first presentation was at Abbey Tokyo last year it's famous civility conference in Japan it's Rex DEFCON it password is no drink no hug at
that time I gave a presentation quite drinking so I hope to enjoy drinking today - all right let's get started I think that there are three typical method to get administrative privileges first it's a method to still administrator accounts there are many tools mimikatz period app cache nap and more next it's a missile to attack system vulnerabilities many series it's reported this year as well who in total is C vulnerable OS finally it's a method to use Windows 10 weakness today's talk wait focus here ya go - to pour abilities and submit to Microsoft bounty program I claimed it Bonneville but Microsoft claimed it was not Microsoft security is a center applied they have decided my finding is not
vulnerabilities after the investigation so I decided to make it in public I
explained in fact I found from now calm management Rancho Rosa SOT Pat et al welcome management Ranch is planted the process is escalating administrator it's Lord third-party Darrell this is problem therefore if you can depress the third party deal you can get administrator privilege but the third party deal has requirement it must be registered in the following registry
I will show you the source code before that demonstration this is only land command prompt create process shiridi else
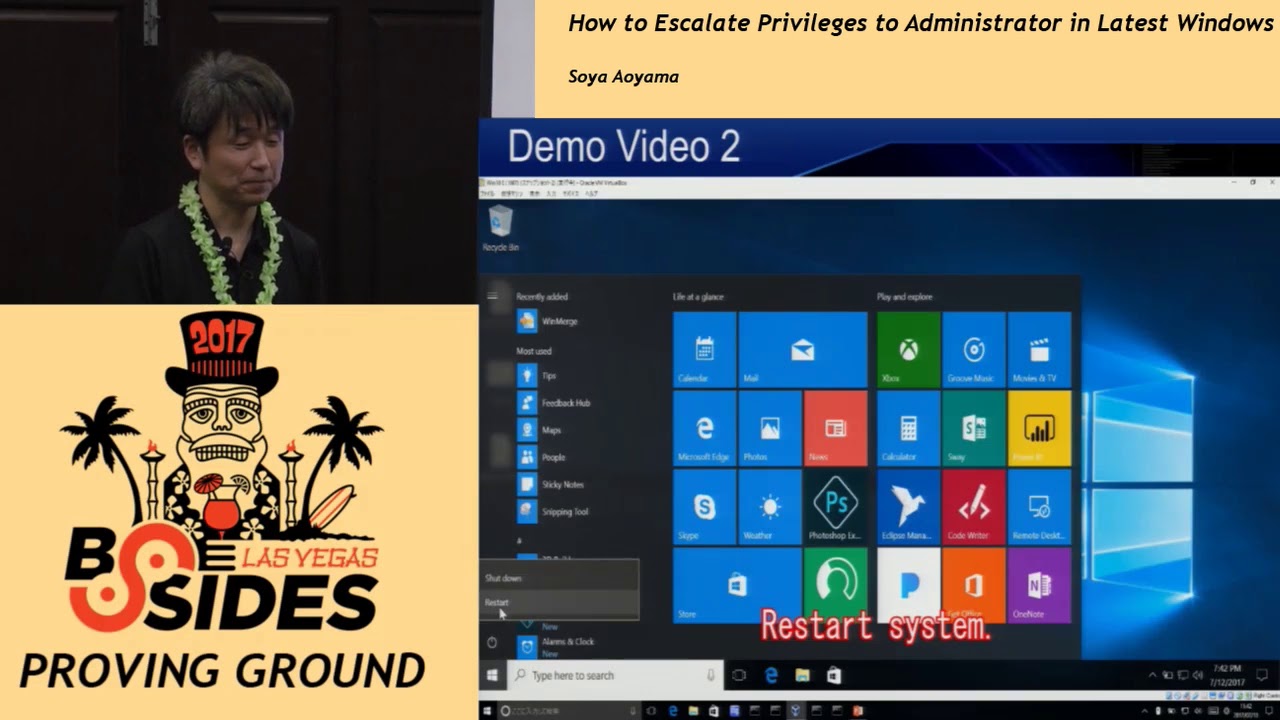
let me show you this demonstration we merges in salt in butter machine first is normal state type co-management rancher in search bar and select nothing harpus
next find the target the type regedit in such a bar and set
open at your local machine software grasses asterisks sherry X context many hundreds and we merge its gid of target tal open the hot copy DUID
this GID and find next open the key and improv Sabha 32 it's tired tiara
next we press the time dear open default and copy directory path of Tong et al
start Explorer this the past in address bar and enter select shell extension x64 dot the area and the name and add underscore copy besides every dot DL to here it's much as deal
rename the file to sell extension x64 dot DL okay it's ready finally start home management launcher again command prompt o is started and display administrator in title bar well this theorem was displayed during the demonstration you need administrator previous to access the file don't worry I found mean to solve this issue
onedrive help to solve plural when the system is started explorer start and load one right gear the wondered program is located in the forum
this is problem because it's under users folder so you can replace one drive year with user privilege and inject Explorer and use the I file operation the API Explorer therefore you can access the administrator's own files I saw the source code of next demonstration I implement the content of documentation demonstration one by program we press the arrow and start combine item Atlanta let me show you next demonstration
there's much as much fire check the contents of abate the to command Li name and copy I will get administrative privilege now
click right button and open one drug deal was replaced already restart system ok yesterday I received one question in the hostel that this account need to be administrative privilege answer is yes if this account is user privilege this attack will not successed
the star takes time so keep
a it's same result the previous demonstration but US attorney was not displayed in conclusion all I could recognize that even if individual weakness are small but it will be very dangerous depending on combination when the bad files check clicked one drive the air file is depressed rushes Wow when the system is started Explorer load meshes do the moistures process repress we much DL by marshes Wow and start con management lunch the CIM management ranchers process give you administrator privilege by loading mices DL if you can make that user click the batch file you can get administrator
it and persistent it means apt attacks it's very easy you can use it the target email attacks or watering hole attacks if you can get administrative privilege you can do a lot access to any loans files registry system setting and more
this is bad news you not use the method animal or my Microsoft fix this problem in Windows 10 build one five or six three home management Rancher Steve loader third-party da but doesn't escalate to administrator privileges I'm sure most of Microsoft doesn't want to pay me our users maybe finally thank you very much other he is my mentor I appreciate your support and feedback for presentation and everyone's attention thank you very much [Applause] and if anybody has any questions raise your hand so we can get it on the feed I was wondering with her he could be perhaps you could change the registry values instead of changing the dll's with her that would be an easier option
you were showing the you were showing at a certain point of time the the dll that was referred to by GUI d if you just changed its registry entry no change but I registered it I found tank D I want to I want to find GUI type GU ID and Tiger deal path so I if you can no turn at the pass so I don't you you don't access you don't need access to necessary hmm okay but okay you could just point point that goe to a different DLL ah yeah so perhaps that would be another option
okay registery yeah okay
under registry no any application now there is many application so today I use image but another application is okay and I try to Dropbox and yeah any other questions thank you for coming we'll have another talk here in 10 minutes [Applause]





