2017 - Cracking The Lens: Targetting HTTP's Hidden Attack Surface
Show transcript [en]
good morning and welcome to cracking the lens exploiting HTTPS hidden attack surface can everyone hear me okay yep good good have you ever seen a tempting target but had to ignore it because it wasn't quite within the scope of your test or maybe you've seen something that wasn't scoped but it was just really quite boring looking and not worth wasting much time on load balances and analytic systems are everywhere but they're just not very interesting they form a lens in front of websites that we're used to looking through rather than app in this session I'll share with you proven techniques to hunt these systems down crack them open and use them as gateways into our
targets infrastructure some of these techniques involve requests so malformed that they break certain security tools and may exploit systems that you never even realized existed like at the start of this research I wrote a simple payload designed to make vulnerable servers send a ping back to my server and I sent this payload to a couple of thousand sites and got quite a few pingbacks but there was something slightly strange about a couple of them I noticed when I sent a payload to cloud dámelo I got a ping back from the same location as when I send the payload to Inga comm which are two quite different sites and so I did a reverse DNS lookup
on this IP address and I found out it was hoped in my own ISP which is pretty strange you wouldn't think that a Russian mail server would be hosted on a UK ISP like BT and so I took the request that caused that ping back and sent it to the repeater i we sent it a few times and noticed something else strange the response was coming back to me in about 52 milliseconds which is ridiculously fast for a request that supposedly heading from me in England all the way to the server in Russia and in all the way to the ping back serve in Ireland and then all the way back again and so I did a
couple of trace routes one simulating a haste P connection that's the one on the left and one simulating a HTTP s connection and as you can see the one simulating an unencrypted unauthenticated connection is getting terminated in the middle of BT's infrastructure hi bTW is pretending to be cloud doc mailed on me whereas the encrypted connection goes all the way to the server's actual location and that is really quite suspicious because it implies the the person doing this interception doesn't have the authority or the keys to do so because if they did they could intercept HTTPS as well so also there was something else suspicious the host name of the server you seen the trace view on the left where the
connection is suspiciously terminated was predator dot alien PT code at UK which you can probably agree is a little bit Shady now I investigated this further and I found out what the true purpose of this system was and I found out that I could potentially abuse the system to hijack a decent portion of the Internet traffic of all BT users which was cool but that's just a distraction from the question that we should be asking which is given that I and many other English pen testers have been testing through an exploitable proxy system like this I never even realized that it existed what else have we missed so first I'll talk about how to build a speculative attack
pipeline to efficiently hunt these systems down and initiate a conversation with them after that I'll talk about two key types of attacks on these systems one focused on targeting fun in system by making the miss route requests to give us access to internal stuff that's meant to be private and one focused on exploiting back-end systems where we have to be a little bit more creative after that I'll do a brief demo of one of the tools I'll be releasing and then I'll answer five minutes of questions so this systems that we're going to be targeting are designed to mein invisible and as such the process that we use to interact with them is incredibly important for the purpose of
this research I found them by sending payloads designed to make them send a ping back to my system I either either a DNS request or HTTP request or hopefully but this approach to finding vulnerabilities by causing pingbacks has been so effective in recent years that my boss made up an acronym for it uh-oh asked so if I say Oh aster I'm talking about trying to find vulnerabilities by making vulnerable systems trigger pingbacks two systems we control at the start of this research I had no idea whether anything was actually going to work so I injected my payloads in the laziest way possible I simply used the hard-coded Berk match in the place rule to inject a request a
payload into every request that went through the proxy and then I just browse some sites and I got me a lot of pingbacks but it didn't get me much useful information because it was incredibly difficult to correlate the pingbacks from the time I wished it was really hard to correlate the requests with the corresponding pingbacks because they didn't reliably occur at the same time for example here we've got one system that due to some payload that I sent to some server I don't I don't know which server it's decided to ping me every 24 hours and it kept doing this for about one week and I never figured out what the cause of this was and I haven't been
able to replicate it since so this strategy will get you information it may be entertaining but it won't get you much useful information to resolve this I wrote collaborator everywhere which is an open-source extension for for burp suite that injects a unique payload into every request and it uses the uniqueness to automatically correlate the payload with the pingback and using that extension I got roughly half of the bounties that I'm going to mention in its presentation however I found one server where the vulnerability was only being found intermittently and that was because this target was using round robin DNS for load balancing and only one of their five front end servers was actually vulnerable because we're targeting
front-end service like load balancers we need to be particularly aware of that kind of infrastructure level stuff and as such you really want to hit every single public facing IP that the target has to do that I started using masscan and eventually switch to using zed grab because it has more useful features for web stuff so if you want to do a focus toward it on a particular application then a collaborator everywhere is the best tool for the job but if you want to spray payloads over a huge amount of infrastructure zed grab is what i recommend who did i target for the purpose of this research i just targeted everyone that i could legally
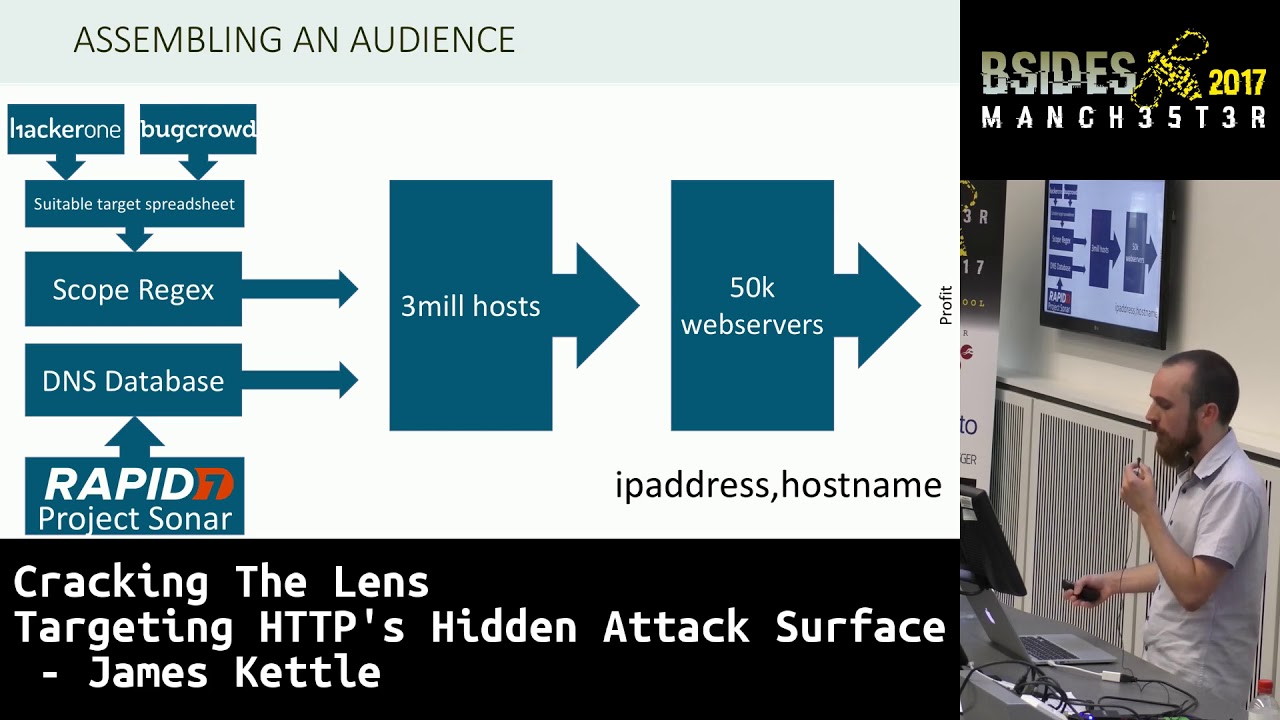
target which means everyone who has a bug bounty program and to identify that I manually reviewed every every bug bounty profile on hacker 1 and bug route and made sure that they didn't forbid automated testing and use that to build a spreadsheet of domains that I could target which gave me a regular expression of domains I could target which I then ran against rapid sevens projects owner database which has a list of every known host name so without sending any network traffic I was able to generate a list of 3 million hosts that i could legally try and hack which which contained about 50,000 web servers now i initially also populated this list of targets using reverse dns but i went
into a little bit of a problem there the problem is that google has got a bug bounty program and certain web sites out there like to spoof google's reverse dns which means that you will end up packing into websites that have got nothing to do with google whatsoever they don't have a bug bounty program they're just claiming to be Google which is not good I mean you could say that they're asking for it but it's still not go down you're definitely not gonna get paid for it now if you're gonna send a request to 50,000 service right you might as well make sure it's a pretty nice it's a well optimized request and you want to hear as much
attack surface as possible one way of doing that is using the max for words header which can trick trick load balances into saying thinking they can't forward a request and have to generate her reply immediately another useful thing is the no transform directive for the cache control header this tells load balancers please don't rewrite this request in any way before you pass it down the chain you can also use exported proto to pretend that you're using a protocol that you're not really using which can also confuse servers a bit and just hit some interesting pieces of attack surface the end result of this pipeline is that whenever I whenever I had an idea during this research I could spend about 30
seconds manually writing a HTTP request and then in the space of five minutes send that 50,000 web servers and get the results that capability to quickly try out ideas and therefore make make iterative improvements to my payload is a large part of the reason that this research was so successful and aren't so much money so first of all we're going to look at targeting things like reverse proxies that sit in front of web applications and we're going to trick them into routing our requests to internal websites that are not meant to be private that are not meant to be public this is quite like if this is a type of server scientific quest forgery but it's a lot more powerful than normal
server-side request forgery quiz because we have a lot of control over the requests that gets sent to the internal service and sometimes that comes in extremely useful as we'll see shortly the simplest technique to make a load balancer send a request to the wrong location is simply to change the host header to the location that you want the request to be sent to this is almost exploiting intended functionality and this technique has been publicly known in some small circles for a while but it's been hugely underappreciated I can say that with confidence because using my zero line with this one payload I was able to exploit a huge number of servers including but not limited to 27
US Department of Defense service Oh - Yahoo - Yahoo load balancers in about seven other weird Yahoo servers that I didn't figure out what it were for my own ISP by accident as mentioned earlier and also a Colombian ISP thought through itself into the firing line by doing DNS poisoning to impersonate one of my targets so when we've got this vulnerability what can we do with it well here as you can see I found a yahoo load Hey ahoo load balancer and I'm using it to route the request to port 8080 - on a nearby IP so the service you can see the sponding can't be accessed directly and as you can see you've got
this repeater to unload command line which suggests that this is this service is not speaking HTTP it's probably interpreting every each of the HTTP headers that that it's receiving as a separate command other than that at this point I had pretty much no idea what the service was however I had an idea I thought I know I'll change the HTTP method from get to help it's a bit of a long shot but I've got no idea what I'm doing so hey and it actually worked it said hi there I'm an Apache traffic server overseer which means I'm responsible for handling the configuration of probably a large number of Yahoo's load balancers also this is how you can change configuration
settings on me so now know that if this was normal server site request forgery thought I'd found I wouldn't actually be able to get and set variables on this server because the syntax requires a space which you can't get with normal service five request forgery but because this is not that setting variables and getting them is actually quite easy so here we can see I've fetched the value of proxy conflict on email and it's set to nobody at Yahoo Inc com great using the ability to set variables one thing that I could do was whitelist my own IP to give it the permission to push items into all of Yahoo's load balance caches which could
get me quite a lot of defacements on quite a few yahoo websites potentially something else that I could do that would be even more fun is in is enable Sox foxing on all of their load balances the only issue with that is that that wouldn't be limited to my utter my IP so effectively pretty much everyone would have access to it Yahoo's internal network so will probably get shot down quite fast so I Eve aborted that to Yahoo and got fifteen thousand dollar bounty for it so that was cool and I found that issue using collaborate everywhere and they fix that pretty fast but a couple of weeks later my pipeline found a different server that had the
same vulnerability getting me another five thousand for a total of twenty thousand which was really solid start to this research now as mentioned the same technique also worked on my ISP and it could be used to access the administration panel for the pool of proxies that they were routing traffic through but they don't have a bug bounty program so I didn't attempt to actually break into this administration panel but what I did want to know is what the point of this of this industry of this interception was and to do that I did a trace through of the whole ipv4 space to work out which IPS they were targeting and that showed me the rough
five percent of website IPS were on the blacklist which could which meant all traffic to them to TCP port 80 was being routed into these proxies and that affected yeah a large number of sites an interesting side effect of that is that if your if your website so IP is blacklisted for example just because you're using cloud hosting then all BT traffic appears to come from a pool of about five different IPS so if you're doing any based any IP based access control or you blacklist any of those IPS then you might actually blacklist most of the UK so be careful about that looking at what these IPS hosted I found that I found this behavior if you try
and access one of these IPS with a host header which they blacklisted then you get this message which I'm sure none of you've ever seen before which says access to the websites listed on this page has been blocked pursuant to orders of the High Court ie as copyrighted content on there although I of course it's pretty easy to bypass that sort of thing now so it seemed like the purpose of this system was just for copyright enforcement but when I reported this issue to BT I actually learned a little bit of backstory this system was originally built as part of the as part of the clean feed government initiative to block access to images of child abuse
it's just that as soon as it was built they couldn't argue that it shouldn't be repurposed to block copyright abuse as I mentioned I also exploited a Colombian ISP so here this happened after the BT incident so it took me much less time to figure out what on earth was going on here I try to send a payload to a different Russian web site and I got a ping back funk Columbia and I knew that had to be done by DNS poisoning and I was using rapid Evans DNS database so I contacted rapid7 and they found the responsible DNS server which is there so that server if you try and access a blacklisted hostname will will route you
through its proxy both of these systems a live at the moment you can take a look at them if you like this system seemed to be targeting image hosts and social networks and once again it would block access to these and say you can't access this because it may host images of child abuse and it would have this logo but that's not all this system was for because they were also poisoning the DNS for BBC decoder UK and all of his subdomains unfortunately I wasn't able to figure out why they were doing this I think they're probably targeting specific articles on there and perhaps changing the content or it's blocking access to them but I wasn't able to find
out which articles they were targeting also maybe they're not altering any content and they're just interested in knowing what you're reading now thinking that the paler of thinking that you know what's gonna happen when you send one of these payloads is always a mistake so for example I found 17 Yahoo servers with the following behavior when I send the payload like this they do miss through the request but they lose the request to outage doc the supplied hostname and they also put the hostname in the path twice I've got no idea what the cause of a is but my job is only to exploit it luckily now here as it is presented there that's not much use
because for server-side request forgery because you're limited to hitting a very specific path fortunately this service was incredibly tolerant about what characters you could put in the host header so you could put a directory traversal sequence in the host header and that would result in the requests that you see on on the right which normalize us into a request to the web loop which means it is useful so have a site request forgery so I reported that to Yahoo and got 5,000 for that now the key thing to know here is that if you didn't have wildcard DNS setup on your ping back server you would have just missed this issue entirely
now this payload we finally on to some different payloads might look familiar I used it back in 2013 to poison Django's Password Reset emails featured in my first ever presentation here but why found here was a particular US military server which looks at the host header and it whitelisted the hosts setter but it routed the request to whatever was spent and specified in the top line which I had control over however I had a little bit of a problem when I found this I wanted to prove I could access an internal service to prove this that this was a serious issue but I just been told off by Yahoo for doing an internal port scan of their
network and i was a bit twitchy about doing the same thing on a US military network especially when i was about to catch a flight to the USA to give a presentation so instead of doing a poor scan i googled a bit and i found an amazing forum post on defense of CARICOM it says if you're looking at this and not on the military or DoD this won't mean anything to you nor will you be able to access it and then it listed a couple of internal military websites which I could access using this vulnerability so that meant that without actually doing any I have any internal scanning I prove the severity of this issue my advice is if you don't need to
do an internal port scan especially with the bug bounty I don't bother it's just cleaner if you don't do that or also the larger the target company they're less likely is that you actually need to because there's more people posting stuff on random internet forums okay now Oh although the network diagram that I showed for the section only showed one proxy server it's possible to have chains of proxies and if you want to exploit a proxy in the middle of a chain that can make life difficult because the proxy at the start of the chain might just chuck out your request for example in caps Allah use the host header to work out which of the ex-fiancé to vote
to route requests to so if you change the host header as per the normal attacked like I've done here you'll just get a response that says unrecognized host or something like that however I found that they're quite tolerant about what they allow in the port of the Hostetter so if you send the following requests they will route that to the to the correct client because they basically ignore everything after the colon however the backend one specific back-end that I found that was using in caps Allah use this host center to build a URL and if you put the host header in a URL the URL looks like that and it gets interpreted by the client as
a username and password or authentication attempt to a host name of my choice so that gave me server side request forgery on that in capsule of client and it also revealed the location of their back-end server meaning that I could talk to it directly and bypass in capsular entirely encapsulated fixed this since I gave the presentation in blackhat a couple of weeks ago but I'm sure this technique works on plenty of other servers these vulnerabilities aren't just caused by poor configurations what we've got here is some code that the new velak was running or on their main live web site on their load balancer and it looks absolutely fine they take the user supplied gyro and
they overwrite the host portion of that Yogo to to the hard-coded value pointing to their back-end server and and they for the request it seems fine but unfortunately for them they were using the server component apache HTTP components and that library failed to require that the path of the HTTP request starts with a forward slash so that meant if I send a malformed illegal HTTP request like this then they rewrite it like that and they try to log on to my server with the username of the server that they were actually trying to connect to so that gave me access to new Alex internal network which some amazing stuff on it it had some awesome developing jokes this was
playing music and everything and they also had some administration panels that had no authentication on them whatsoever so that was cool now unfortunately New Relic don't have a don't pay cash bounties but to their credit they did patch this issue very quickly on a public holiday and they also reported this issue back to apache HTTP components where it's now been fixed so if if you're using that library you don't need to panic as long as you've kept it fully up to date fortunately for me this technique also worked on seven different Yahoo servers earning me another eight thousand dollars for a total of thirty three thousand which is the full amount that I earned during this research now you
might be wondering what happened to that money so the deal that I had with my company was that with any bounties that I earned by accident during the course of my research would get spent on beer unfortunately uh these bounties raised a little bit of a challenge so we decided to give the majority to charity and spend a small amount on beer instead now the strangest behavior that I saw I turned this research was courtesy of a whistleblowing website called called globalinx now this is a bit like WikiLeaks except it's actually legitimate and and here when I send the following request which is malformed because it does not start with a forward slash I received about fifteen DNS
requests to my server all in mixed case or coming from different IP addresses Oh which was pretty puzzling I mean what would cause that eventually due to the nature of the website I had an idea which is because this is a whistleblowing website they want to hide the physical location of the back-end server to protect it to protect it from government raids and that kind of stuff so actually the back end is accessed by the front end as a tor hidden service so I've got a server side request forgery through tor which raises some quite interesting challenges when it comes to expert exploitation because my request being sent food tour I don't actually have access to any internal services
what I can do though is if I've got an exploit for the tour client then I can make them connect to my server and then gain control of their front-end through that and also because it's a whistleblowing site and it's using tor I could potentially use it to quite heavily obfuscate an attack on someone that I didn't like because even if they were to trace the attack through tor the trail would end at a whistleblowing website which is probably guilty it's oh right yeah that's now be fixed oh okay
so now we're gonna look at exploiting helper systems which are generally located more or less behind the server behind application now here unlike that in the previous section making these systems cause a ping back is actually really easy generally and the hard part is actually exploiting that for something useful the main thing that makes exploiting these systems so difficult is that when we get a server-side request forgery it's blind server side request forgery meaning that we can't read the response from the internal services and we can't adapt our attack based on what we're seeing so we have to be a bit more creative this section of the research was sparked by a really old looking website that
contained a really exciting sentence it said the ex rap flow file header should contain a URL pointing to an XML document specifying the features of a mobile device so you can access any website and you can specify a URL in this HTTP header and they will in theory fetch that euro and then pause the result as XML so we've got two really dangerous pieces of behavior there and when I found this I got very excited and immediately all of my targets and within a couple of hours I'd got exactly no pingbacks so I was very sad and I tweeted it and then about 20 hours later I got a ping back from Facebook so Facebook does support
this header but they fetch it about 26 hours after you use this header fortunately for Facebook there X there set up their their XML parsing seems to be fairly solid so I wasn't able to exploit it but the fact that there's a 26 hour gap in between trying each stack and getting the result made it quite awkward so maybe I missed something maybe you can exploit them and get a decent bounty for it fortunately there are many other useful headers out there that are widely supported the most commonly supported useful header for causing pingbacks is the referer header this really surprised me a shocking number of websites will fetch whatever URL you specify in the referer header I
think they must be doing this some kind of analytics or SEO purposes but yeah that works on the shocking number of sites as I'll show you shortly also the x-forwarded-for header I'm sure you're familiar with using this to spoof your your your IP address you can also put a domain name in there and then if they resolve that in that domain name that will cause a ping back to your server and that tells you they are using this header they trust this header and therefore it means maybe it's worthwhile spending more time trying I'd be spoofing attacks and similarly that also works for the true client IP header and the ex VIP header which in
which are less well-known but there's no cost to adding extra headers basically also I found in capsula for some reason if you specify a parameter with the same name twice with the same value then they fetch that with the HTTP request I've got no idea why they do it and I only found it because a bug in my code led that led to parameters being specified twice but there you have it okay so we've got someone connecting to the euro that we specify in them afirma header so what well one thing that we can try and do is trick their client into handing UPS some credentials to our server I try this technique and it
didn't work on any of my targets but while I was trying it some random vulnerability scanner happened to hit my server and did get exploited by it and hand over its credentials so I still count that as a as a win also you can try the client-side heartbleed you can you can try the client heartbeat attack which did work on one of my targets so I was able to take blind server side request forgery and use that to read memory from the vulnerable server you can also use various other off the shelf tools to get more of a feeling for what the target is actually running and what are they and what are the exploits you might be able to do but
off-the-shelf exploits are kind of boring what else can we do well one thing we can do is use more OS so we found this behavior using the pingback technique but we can also then take say the latest struts to remote code execution of the week and use that to make a payload that makes vulnerable service send I think that to us so then we can make this thing that's crawling the referer header and tell that to spray our payload for struts across its internal network and maybe find some shots also some of these things that fetch the referer header render the webpage that they visit as and they they rendered the page in a browser
environment they even execute JavaScript on that page and that means that we can make them spray cross-site scripting payloads across their own intranet and if they find a vulnerability we can inject a beef hook and effectively gain full access to that internal site I think the correct technical name for this is blind reflected server-side XSS also depending on how they limit cross protocol what cross protocol access we can get cross-site scripting in local files like prop self invite one which might give us access to their entire file system just once again pretty nice in fact if they're rendering there's a huge number of things that can go wrong tons and tons of things and to answer
all of these questions my colleague Gareth ace who's presenting later on vote at all called hack ability this is a website that you can point someone at and it will probe their browser environment and observe interesting things about that environment like what plugins they support and whether there's any interesting JavaScript variables that aren't that normal browsers don't have for example here I've I've taken the parity ethelia wallet which is most notable because it got horribly happy a couple of weeks ago and pointed it at this website and and and hack ability has identified that this wallet is injecting some extra variables and using those using those objects I can get the wallet ID of the person who's visiting
my website and even initiate transactions and that is actually intended functionality but hack ability will point it out to you in a very obvious way and it was using something very similar that we've got remote code execution on Jake's browser which is basically a Java version of phantom J's earlier this year these environments are often really out of date and not well configured and this will tell you really easy ways of hacking them okay looks like we've got time for one final exploit I've saved my favorite one till last so here this application is not sending my request to the wrong location it's I I'm getting the correct response from the server I from this request but
when I trigger that request I also get requests to my server like ping backs for random files this is another US military web of course and just to confirm exactly what's happening I've an on wises slightly to I loaded a history of blimps page and the server and the server tried to fetch a picture of a blimp for my server we're we which was quite mysterious so the only plausible explanation here is that I'm accessing this application through a reverse proxy and the reverse proxy is scanning the responses and it's looking for resource imports and then when it sees one of those it fetches it presumably so it can cache it so that the page will load
faster now I wonder if I can exploit this maybe I can send a request to the application to the backend that will trick the reverse proxy into fetching us and sent some sensitive internal content and caching it and then I can grab that out the cache so to trigger this I had to find some cross site scripting which was surprisingly difficult but I found some in the end so here I send a request using a reflected cross-site scripting vulnerability for triggers that makes the server send the following text back to me which has an image import statement which from the server's from the proxies point of view this is fetching any image right it starts with
image source equals and the file name ends in dot jpg but from the so it will see that and try and grab that image from that internal server but from the server's point of view because it's running the PHP that's just fetching the index the index of that site ISO the proxy when it saw that would catch that content and that meant that I could just grab hold of that sensitive internal page from the proxies cache so what we've done here is we've escalated a reflected cross-site scripting vulnerability into a service hide request forgery vulnerability I think the key problem here is that the proxy is caching resources on external sites not a good idea okay time for a brief
live demo of collaborate everywhere okie Dok right so here we've got but sweet and I'm just gonna turn on calibrate it everywhere and as you can see here it's works out what my IP czar for DNS and TCP and that's because sometimes my system will cause interactions and it will otherwise report these is highly exciting vulnerabilities when they're just been caused by my own system and they're not very interesting so now I'm just going to load Firefox which is proxying through but and this is loading a bunch of websites like stripe Foursquare or earlex Starbucks a Facebook and Netflix now what I'm showing you here are not vulnerabilities in these websites these are interesting pieces of behavior in
these websites so if we look at the proxy history we can see if you pick a random thing here that's not a good one this is the request that the browser sent and collaborate it everywhere it has rewritten it and it's injected loads of payloads right it just puts them everywhere and so that may have caused an interaction and if we look this kind of results we can see we've got a bunch of pingbacks so here for example you can see that stripe has fetched for the URL specified in the referer header and they fetched it with a user of Ruby so presumably they're using Ruby to do that and it says that happened after - two seconds which means the time
on this system is slightly wrong ah hey some other systems I sinned ping back ascend pingbacks after quite a long time gap so here Netflix fetched us after nine hours of 30 minutes and if we look at this interestingly they claim to be using an iPhone but they also claim to be using an x86 CPU and so yeah simile here we can see that Facebook have fetched the WAP file specified in expat profile and we also get DNS lookups for the true client IP header from Starbucks so we know me we can maybe spoof our IP on Starbucks perhaps and X VIP from stripe and exported for from loads of people okay
great that's the demo now how do you educate these issues well you can replicate them using burp suite of course as of the latest update the scanner will find most of these vulnerabilities automatically unfortunately you can't let placate all of these issues using SAP because of a known bug but I have it on good authority that this is going to be fixed soon so soon you will be able to use up to find these issues and my Tim MIT M proxy is a good open source alternative that can handle this stuff if you want to help clients replicate it they might not have any of these tools so you can do most of them with show commands you
can do the basic attacks using Co like this for the more advanced ones that require malformed tasty HTTP requests you will need to use echo and then just pipe it into n cat or open SSL as appropriate also you might need to use the server name or option for open SSL to set that s ni feels depending on if the target is using doubt fat or they're like okay how do you defend against these attacks well as far as reverse proxies go and load balances and the like I think the important thing is to understand these systems are designed to proxy they're meant to send requests to internal servers so it only takes a tiny
tiny bug in these to make them send the request to the wrong internal server as a result the best approach is to put these in a demilitarized zone to put them in a network environment in which they do not have Network level access to any stuff that's intended to be private don't put them on a system with unauthenticated admin panels on the same network as for things that fetch the referer header and the like it may help to think of them as employees that have really really whole web browsers that never get updated who click on every link that you give them fortunately unlike employees they won't plain if you put them in a sandbox so
that's why I would recommend do it also if you've got a bug bounty program well if you don't have one I recommend having one if you've got one and you don't forbid automated testing I've probably already tried these payloads on your site so you can have a degree of confidence so you're not so vulnerable please don't forbid automated testing with with with custom tools because you will miss out on some really good fun on some really good vulnerabilities if you want to stop people flooding you with traffic you could always just forbid testing with off-the-shelf tools okay the three key things to take away I have a bug bounties that enable white hat research at scale load balancers our
VPNs for the public and coolers our employees who click I'll take five minutes of questions now and then if you've got any any more after that I feel free to come and talk to me at the back or send me an email don't forget to follow me on Twitter thank you for listening [Applause]
[Applause]
yep it was fixed a few months ago it didn't I pretty sure it didn't get a CVE because I mean they would argue that's not a vulnerability it's only a vulnerability when it's combined with new LX coat yes they it was patched a few months ago okay thank you thank you very much James





