Operation Tripoli - Aseel Kayal
Show transcript [en]
hello hi thank you everyone for attending thank you for having me thank you for not falling asleep after lunch so good to see you all just to briefly introduce myself before I start talking about the talk my name is Seale I work at the threat intelligence analysis group at checkpoint I've been there for three years and I mainly well most of my work focuses on Middle East stuff and this talk is no different actually this talk has a lot to do with Libya and if you don't know where the country of Libya is it's actually right in the middle of this math I made it a bit easy it's North Africa but Libya has a very interesting history because back
in the day it was ruled by a king and in 1969 that King was abroad in Turkey and Greece supposedly to receive some medical treatment and there was a revolution against him and that revolution succeeded quite easily there wasn't a lot of resistance to it and then someone else rose to power someone by the name of Qaddafi and Qaddafi became a bit of an internet celebrity for the recent years but before that he was really the voice of change in Libya he wanted to get rid of the corrupt Kingdom he wanted to overthrow the tyrant he turned the country into a republic and because he was such an advocate of change he only ruled for 40
years and by the end of that he didn't even go willingly because in 2011 that was actually the peak of the Arab Spring so all over countries in the Middle East there were protests asking the rulers and the dictators to step down and to improve the living circumstances within those countries and the political chaos started from Tunisia that's where the protests first began and then spread most notably to Egypt and Syria but the it also reached Libya as well and eventually Qaddafi was overthrown and killed and the situation didn't improve much after that there was even a council that was supposed to choose a replacement for Qaddafi but they failed and they also failed to prevent a second civil war
that happened in Libya in 2017 and since that day or nowadays there are two major people in power in Libya there is a prime minister which leads the government that the UN approves of and there is a general marshal of the Libyan National Army so he leads the rebel powers against that prime minister and I gave you that kind of Borak historic and boring historic introduction in talib in Libya because this dude the general marshal or by his real name afta appeared in an interesting context a Facebook page that was using his name and that page was created I think in march and it was sharing posts like this one and there are a lot of things that
we can tell from this post first off we see that it had 5,000 reactions so a lot of people were exposed to this post a lot of people saw it and engaged with it it was promising mobile applications that word that could could have been downloaded by the link that it offers and they were supposedly providing the users with the latest news from Libya but in truth that they of course had malware and they were malicious so I was really curious just coming across this post randomly going through stuff on Facebook and I wanted to dig a bit deeper into this and find out more about this attack and this page all of the posts that were shared by it were like
this one so they were sharing malicious links to malicious files and so one of the first questions I asked myself coming across this post and trying to investigate this further was are the attacker is using other ways to spread the smell where is this the only page did the malicious activity start just now or has this been going on for a while and to answer that one of the first ways that I've used was the Facebook search part so I used that to look up some of the links that were downloaded the militia that we're downloading the malicious files and that in the posts by this page and doing that I got back nothing and if you're if
you're familiar with the Facebook search bar you have extensive stalking experience you would know that not a lot of the times it doesn't really give back the most accurate results even when you know a post is there you don't always get it back and that wasn't probably the most effective way to check this but then I realized that the posts included something else besides the links downloading the files they included text and that text was an Arabic and I speak Arabic and I can tell you that text was so shitty that I even created a version of the post with all of the grammatical mistakes and wrong syntax and weird phrasing highlighted you can see it's
kind of like very high percentage of the post and I roughly translated that into English with the mistakes you can kind of feel or see how I felt reading this and seeing this text in the post itself but this can tell me two things first off I can tell that whoever wrote this text is an Arabic speaker because they didn't really use translating engine or Google Translate or whatever to generate this because even though that might sometimes mess up the message you're trying to convey Google Translate will give you back the word army with double a or two with you etc and second of all I can use that in my advantage so if I
can find those uniquely wrong mistakes again being repeated elsewhere I can probably say that it was the same person who made that mistake and so I did that and this time around when I looked up some of the Arabic phrases that I saw in the posts I got back results and I actually got back many many many results using this technique and you can see that all of the results here also follow the same patterns as just a small caption and then a link leading to a malicious file and soon enough I realized that each link was shared by more than one page so we can really see the same text here the same caption of the post and the
same link copied in multiple places on the same day so I soon realized that each such link had the potential of exposing multiple related pages and then those pages as I was going through them revealed more links and the links connected me to more pages and then those pages connected back to the same links so again I realize that could kind of create a network here of URLs and Facebook pages and I did that and this is the full version of it all and it's very ugly it's zoomed out you can't tell anything about it but this is kind of the full melty go graph of the graph of the whole thing connecting all of the
pages and the URLs but we can really see how interconnected this is and looking at the connections we can tell that each link was most of the links were shared more more than once by the different pages that were involved in this attack and again just by mapping the whole thing I was able to tell that the activity goes back to at least 2014 that's the earliest instance I have seen relating to this activity so it has been going on for quite awhile when I came across this I was also able to tell that there are approximately 40 pages that were involved in this operation and that were being used to share the malicious posts and I saw that this had a very
wide outreach because eventually some of the pages that I came across and I was able to connect this had tens of thousands of followers and even two of them had more than 100,000 followers so you can imagine that each post that was prompting victims to download a malicious file had the potential of reaching thousands or tens of thousands of people each time through one individual page and we can ask ourselves well who is this after who are the attackers trying to target using this and you might have wild guess but we were able to get more solid evidence about the victims because actually all of the posts or most of them were using link shortening services so a lot of
Google short links and bitly and tiny URL and what's great about those links is that they story statistics so I can see how many times they were clicked where from and more information about that so in the link I'm showing here for example we can see that it was create around the time it was great it was clicked around 7,000 times and that was also around the time it was shared and that's a very high number as well but we can also see that most the time the victims or the people that click this link were referred to it by Facebook so we know that this is the major attack vector for this campaign and out of the
seven thousand clicks five thousand clicks came from surprise surprise Libya and there were some victims supposedly or some other clicks from different countries but we can really see the focus on this country by this attack and again disclaimer a click does not mean successful infection so these are just the numbers of clicks we don't know that they were victims eventually but we can really see the focus on Libya even in terms of links here and the same pages that were involved in the malicious activity shared other posts as well so we also saw them sharing updates about things that were going on in Libya and news and that kind of followed the same pattern so that the same post with the
same caption and picture was copied across multiple pages and seeing this I was very surprised I first off I thought it was trying to push kind of hidden propaganda or agenda and maybe trying to influence some people but in reality these were just news updates that were trying to keep the followers of the pages engaged and trying to keep them following the pages themselves and just to eventually click the malicious links and increase the pages legitimacy this wasn't really trying to politically affect anyone's opinion I would say and another question I was asking myself and you might be is why why were the attacker is using Facebook why this social network so in Libya but also in
other countries where there is a lot of political conflict I would say sometimes your mainstream media or your main media outlets the official news channels and the official newspapers are not the best source to get your news so a lot of the times you would be thinking you're seeing what's really going on when in fact what you're following great the channel is really giving you kind of a biased idea of what is going on and they're taking just one side and because of that a lot of people in the Middle East region but also in different places have turned to other sources for news and it involves obviously online websites and online blogs but also
Facebook so Facebook has become kind of a very reliable way for people to get their news from and as soon as the victims realize they're in sins that people realize that threat actors were very quick to follow so we also see that in a lot of the misinformation campaigns that have been exposed recently Facebook has played a very major role and actually such a campaign that was exposed by Facebook's themselves by the Facebook company that was affecting countries such as Sudan and Libya it was they discovered that the attackers behind this attack invested nearly one hundred thousand dollars in advertising trying to reach the people or the citizens of Libya and other countries and affect them we're trying to kind of
humiliate one later and promote another so again we really see how important Facebook is in the landscape in the Middle East also in terms of misinformation campaigns but also in terms of malware so we've seen some of the more advanced players like if you know of the dark caracal threat group but also oh no okay sorry if you know of the dark caracal threat group and apt c-23 for example so we have also seen them spreading their malicious samples using Facebook so these are just two examples of groups that they have used or pages that they've used to reach a wide audience of victims and even in our case like although the posts or the
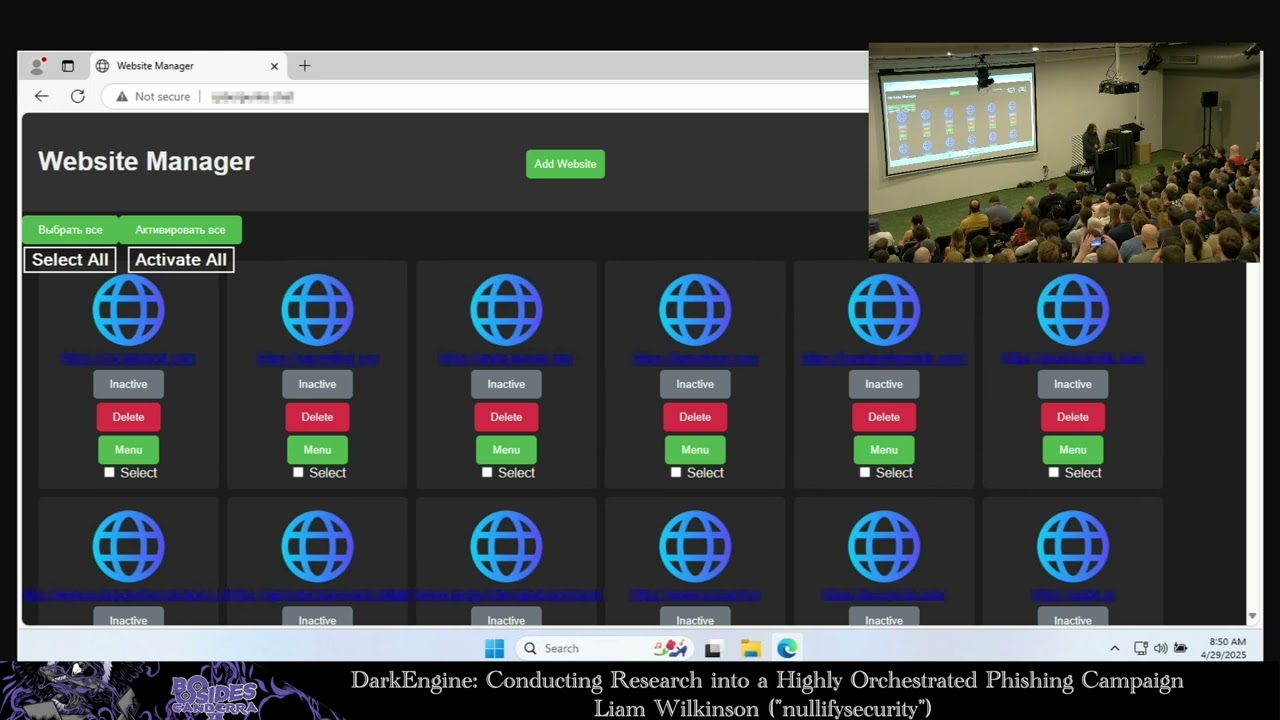
news headlines that the pages share it weren't really trying to do something like behind the stage or affect people but we can still see that updating and sharing those news about Libya and those pages did keep the users engaged and it was kind of a nice way to keep them following the pages and since we've mentioned malware here and malicious files you might again also be wondering what was the malware that was used in this campaign so it wasn't very very impressive I would say the attackers in this case we're using kind of off the shelf tools so known remote administration tools for both mobile and desktop that they were attacking the two vectors in the case of mobile we saw
that a lot of the times they were using spine out which again kind of provides the attacker with with a nice panel that can let them control basically anything on the infected device and exfiltrate all the information like contacts calls and more sensitive stuff as well and in terms of desktop so it was a lot of NJ rat and other things that the attackers didn't really develop themselves so they again didn't waste a lot of time on developing their own malware and in case of desktop they did add some protective layers before delivering the payload eventually so we can see that when the victims would download the filer when they would click the link they at first
would be or would receive a VBS file or at wsf file and you can even see that the name the file itself looks like a news headline so just to keep the theme of the posts going on and to convince the victims that oh this is okay you should click this should run this on your machine and then opening up the VBS file again we can see that it has this sort of random blob it's first but it's not really you can tell that this is just a comment it's not really part of the code and it's just used to hide the beginning of the VBS code which is down at the bottom so it's just meant to confuse any
victim who attempts to open this file and the purpose of the VBS it just basically take an array of decimal values and turn it into the corresponding ASCII characters and eventually reverse that string and now we can see that we get a more readable code in this case and we still have an encoded bit at the end and that is basics t4 encoded and which is in this case the payload the executable fails the purpose of the VBS is to kind of prepare for the payload to be executed on the machine and the payload itself was a dotnet executable again also something open-source of the shelf not something the attacker developed and it was supposed to gather information from
the infected device so again like the IP address the installed antivirus products etc and upload all of that to a C&C address and that since the address helped me answer the question of who is behind this attack because basically the this website or this CNC used duck DNS or a dynamic DNS so it resolved to a lot of IP addresses and then going over the going over those IP addresses I saw that one of them was associated with another domain and that domain was used by this campaign back in 2017 so it was the C&C 4 other files that were spread by the Facebook pages and that other domain unlike the drtc dns it had Whois information and the
Whois information showed me a name that I couldn't really get a lot of information on online but it also had an email address which again repeated the D RPC that we see in the hotter website and looking up this email address I also saw that it was used to register to other addresses dexter ly comm and dexter ly dot space and searching for dexter ly actually led me to a facebook profile operated by the attacker so dexter ly was the current avatar of the attacker behind this campaign and the prehistory vs avatar as it turns out was dr. pc which we've seen in the new web site address and in the gmail email that was used for registering them and
this Facebook profile I mean if you've looked at similar attacks it kind of follows the pattern of attackers of the sort he was basically flexing about all of the achievements and everything that he did and all of the systems he managed to infiltrate and basically sharing panels of showing successful infections and victims that he managed to get to run the application and what was a bit weird for me at least observing a lot of similar threats in the regions that usually those kind of threat actors would be like oh look look at the credit cards they managed to steal er look at the PayPal account and got into and it's more it's more about bragging in that
sense but this guy was actually sharing a lot more sensitive information so over the years I think he managed to infect thousands of people mostly from Libya and apparently he also got his hands on a lot of sensitive information by doing that so we saw that using this Facebook profile he also used to share a lot of financial documents that were shared by the Libyan embassies and Libyan government and internal information that wasn't supposed to reach his hands or anyone else and he can even see him kind of getting his hands on communications between international companies and the Libyan government as well so this was really kind of surprising to see that despite the basic tools he was using
this was very very successful and did a lot of harm actually and he even shared some official documents and on his facebook profile so we can even see that he got his hands and a couple of copies of diplomatic passports which is funny because this the one on the right actually belongs to the general Marshall to the guy from the initial Facebook page somehow by infecting some guys in device he got a copy of the diplomatic passport of this guy and that was crazy and seeing just the scope of this attack was again also crazy and we've reported all of this activity to Facebook so luckily the dexstar ly profile is down nowadays all of the pages that were involved are
down and again this guy some of his activity even back in the day and I realized since later on was also uncovered by Trend Micro I think back in 2017 but he that didn't deter him they still kept at it and this time we took more strict means in terms of trying to stop him from doing what he's doing and they really hope he doesn't go back to doing that eventually because he he was also sharing the fact that he received emails by the FBI letting him know that they're aware of his malicious activity but I think as long as he stays within Libya he's gonna be off the hook but just hopefully not doing anything
malicious anymore so to conclude this activity has been going on for years I think even more than 2004 theme this goes back to way before that and in the previous profiles that I've seen also operated by him he was kind of also active in 2013 and all different in different hacking activities and he was using off-the-shelf tools and I think if you're kind of working in threat intelligence or in malware analysis and whatever that makes our job in terms of attribution a bit harder because if he's using his own unique code that's kind of better for us to track his tools and to know what is going on there and to be able to tell when he releases new
samples for example but just knowing that he is using things like spy note or engineer at mix it makes it a bit harder and I think looking at the alternative of identifying this guy simply by his grammar mistakes and seeing tracking this activity by his typos was a nice alternative in this case that would have been harder if we were just doing this simply by looking at the malicious samples so in terms of threat intelligence techniques this also kind of provided me at least with a new way of looking at things and not just looking at the malicious code but also sometimes it's more simple than that you don't only have to rely on the sample
itself and despite the low sophistication of those things and the fact that he was using those open-source tools we can really see the high impact of these attacks and I think this really applies to a lot of threats in the Middle East the fact that they are not a very sophisticated man there are very sophisticated ones don't get me wrong but despite the fact that they're not very complex we can really still see them doing very very high like a lot of damage simply because they know how to socially engineer their samples they know how to reach their victims and they know how to design the bait for the people that they are targeting so in
this case we really see the investment of this guy in the usage of those Facebook pages with thousands of followers and trying to keep them as legitimate as possible and succeeding throughout all of that into reaching those people and not really by investing a lot of effort on the technical side so I would say that and this may be repeats what Brian said earlier in the day that you don't really have to have the most advanced tools for you to have the severe impact that this campaign had and that'd be all for me thank you