How I Met Your Password

Show original YouTube description
Show transcript [en]
okay hello everybody it's pretty quiet in here so my talk today is how I made your password basically covering a few things around password cracking primarily from the offensive side of things why it's sometimes becoming more difficult mistakes that we can be making before sorry before I continue can you can everyone hear me working around okay thanks and also some attacks that some of them are not new they just haven't which haven't seen them for a while but they're still very good they can work very well especially if you new to to cracking passwords it's a few things that have evolved since they were first made then also what to do for the the slow algorithms the ones
are taking more that are more difficult to crack and then finally some new information about wpa2 attacks that I'm sure you've recently heard of that was released by Adam and hashcode so we'll have a look at that as well and how it's going to help us a lot with cracking those Wi-Fi passwords of course everything shown here is for you to use in your work I assume no one would ever want to use it for anything bad that thought would never cross your minds so nothing mentioned here would would be should be used for that the key is to try and make things stronger and more secure by finding what's wrong with them and trying to fix those holes that's
where these approaches are coming from how we'll do the questions because it's going to be pretty close to lunchtime when I finish and so what I'm gonna do is if you have any questions when I'm finished then you can come up and we can discuss it then because I don't wanna keep those of you who don't have any questions and may be hungry and will want to get to lunch so just having a quick look at the outline then why you're failing just having a brief look at at why it's getting more difficult to crack passwords leaks based friend or worst foe so it's quite a bit of leaks out there and we're gonna just have a brief discussion
on whether or not they're actually working for us or they're not working for us as somebody who does password audits does it make your life easier does it make it more difficult some people may feel that with leaks becoming some more apparent there's no it's harder for them to crack passwords because companies are securing pretty well against the ones out they will have a look at that as well then some attack methods Markov tmesis and prints some of these those of you who've been cracking passwords for a while may recognize they've still very much capable of increasing the amount of passwords that you can crack if you use them properly attacking phrases and other languages so
we often just seem to default to cracking passwords in English but if you come from different countries different places these different kinds of passwords you can crack emoji may land up in a in a hash summary and you want to be able to crack that so we'll have a look at that as well cracking heavy-duty algorithms and they new wpa2 attacks without client interaction and then questions finally okay so why are you why you're failing so what's been happening a lot recently I'm sure you've seen it out there in the news is that well we're seeing two things increasing a lot we're seeing real time password black lists finding themselves into applications into third-party tools
major leaks like have I been poned releasing the sha-1 hashes that companies can in query in real time and say well the password you trying to say it is not secure try and use something else then the user education side of things so there's always these an increase in the amount of education that's been given to users every year unfortunately passwords are still relatively secured and I think they're always going to be but the level does increase as time goes by as a new generation starts using the internet they they're a bit more prickly to those attacks that can happen they're a bit more aware of what insecure passwords couldn't be and so they up the level a
bit more as I started using systems out there and then of course beta hashing algorithms also have come to the fore and so that also makes it more difficult to crack passwords sometimes as well okay salts increased use of salts so from a developer point of view a lot more salting of passwords is being done and stronger and longer salts as well unfortunately sometimes the salts being used when hashes are created but they're so small and so weak that they may as well not be there at all on the other hand you have some people who are building very robust very good applications that are salting those hashes very well making them very difficult for somebody to be able to
crack and then increased computing power resulting a better uptake of slower or intensive hashes so certain hashing algorithms that were once considered too difficult to use because of the fact that they would have been too slow the processing power to be able to do multiple transactions or multiple events in hashing a password that was an issue in the past that's becoming less of an issue now of course the more difficult algorithms that have been introduced may still also be causing systems to slow down but the fact is that processing power is getting faster and faster and faster and so more advanced hashing algorithms can be used just the node at the bottom there of course that the
inverse is true so the more processing power that we have to crew to use stronger algorithms we have also stronger processing power to crack pass passwords as well so the two tend to rise together but the fact is that we are seeing a lot more use of better hashes or better hashing algorithms out there than we did five years ago maybe even four years ago will less people also moving away from the easy hashes mostly moving away from the Eastleigh hashes easy hashes unfortunately we still see some people trying to do authentication with md5 in in databases or sha-1 if you're doing that then I would highly recommend you well don't change change it now cause if
you get up and go well no but as soon as possible you need to you need to get over hashes like that they're they're pretty true trivial to to crack and even if they're salted this little pretty trivial to crack these days as well so md5 basically belongs in the history books or maybe for the odd check of a file that you've got matches a different father G of God that's about as far as as I would use it these days when it comes to any form of authentication you want MV v out the window faster you want sha-1 out the window fast as well okay leaks so leaks are creating awareness for better password security basically
every time they go in the news people see these this tariff leak has happened and the passwords that came out of it were horrible also related to our previous slide because often those leaks are easy to crack and just one point I'd like to make here too also is that there's no point moving to a stronger algorithm you can go all the way up to be crypt if you want to and then your security and the rest of your system and application infrastructure is so bad that it's it's pretty easy to get a hold of the hashes and start working on them so you know you need to look at both sides because I've seen for example on a
paint is you can get hold of hashes pretty quickly in an application so yes the box was ticked to say we're not using md5 and sha-1 or anything that's insecure like that all fast to crack like that but the downside is that they weren't kept securely there weren't the application had nowhere protecting them everything else that should have holistically protected those hashes was not there back to the leaks they can be queried to prevent password reuse I'm sure many of you have seen those lists going out there that you can query these api's you can download the Shaw ones and other forms of the hashes and what this is doing is that it's um it's allowing
websites and applications to actually say to user well the password that you've entered if you please don't choose this while it's been leaked somewhere okay now that's very good but it's not very effective if you haven't switched to a stronger hashing algorithm and it's not possible to attack the application and get the hashes anyway because otherwise you're just telling users to pick a new password when the rest of the system is insecure as well so leaks best friend or worst foe so leaks give us good word lists for for cracking right because they're real pass passwords they're not once we've guessed maybe someone's chosen it maybe they didn't chose it it's real-world passwords that people
have used we can get statistics from those we can look up and do all sorts of fancy analysis and see well for this particular side these are what the users are doing when it comes to HR sites this is what they're doing when it comes to social sites or or the dating sites this is how users are choosing their passwords common words used here and there and then we can also block or ban these leaked passwords as I mentioned using the various api's so what is the downside well the downside is that many of our word lists when we're cracking passwords now become and negated because if you've got a few billion passwords that users
have chosen chances are all that's not worthless you've got worth 10 or 15 gigs at least 80 percent or more are going to be in that list so it's kind of bringing down what you used to have to work with when it comes to cracking passwords in your in your word in your word lists the user experience in entry so I don't know if any of you have used any sites that are using these these banned lists to block certain passwords that you can use okay there can be a bit frustrating because you're tapping and it's saying no you're trying something else and it's saying no there's leaks are pretty big so the chances of getting or choosing a
password that it's gonna that's going to be in that list is is pretty good okay so what you have is two things are happening either your usability of the site is affected because users are like well I just don't know what to choose you know keeping in mind that users don't sit all day planning what's the strongest password that they're gonna pick so it becomes frustrating for them and then the other problem that happens with them with that is that some sites have a little limit so by the fifth or sixth time that it doesn't accept something it'll give in and say okay you know because we don't want to frustrate you anymore so we'll exceed what you've got
but you need to work on it or change it at some other time so now what's happened is the weaker password Sabina has been allowed in into the system again it also does not re-educate the user so telling a user that password one two three should not be used cuz it's in a leak doesn't provide them with any kind of education of how to choose a stronger password it just tells them that while you can't use this one try again so they try password four five six and they get the same thing the trial password seven eight nine okay by the time they're up to ten thousand or so they still haven't been taught anything
about how to construct a secure password so yes these leaks have pros that that they're making them useful on both sides for those cracking passwords for those who need to have secure passwords on these sites at the same time though there's certain things that need to be addressed simply clearing those api's and blocking users is not sufficient to get this thing to work it's gonna it's going to become frustrating business is going to ultimately force you to put some kind of a compromise in there and then of course the fact is that and as I'm sure you some of you know the case of the sha-1 lists that are out there I think nineteen nine was a 99.5 percent
or correct I think more by now 99 point something hi so already people wanting to crack passwords will have those in the dictionaries they'll be able to work with and we'll touch on that a bit later on so those are not going to be affecting them they're not going to be trying them as false as false positives when they're looking to create a word list to attack hashes and if finally the user education is is a problem as well so to make password or its effective than your word list need to be efficient and I think that's a given but even if you've got the processing power you don't want to just throw a word list at
a wasting time so if you know that a particular site or system is already using a query a certain number of leaks to check if the passwords in there get them out of the word list that you're using because otherwise you're just sending stuff that you know there's not going to be in there one way to do that is the the RLI tool from hash codes utilities very simple you give it a a word list and then you give it a second word list it'll then give you the output of the difference between the two right so what is not in the one what in your word list was not in the other one in this case
what in my word list wasn't in the parent passwords what you may want to do there is remove special characters drop the case down because you're gonna use rules also ultimately to attack the passwords later on so there's no point trying to compare those at this point in time what you want to do it's get a nice streamline word list that hasn't got the leaks that you know that particular target was excluding from allowing users to use when you want to audit it understand how users will bypass these pwned password chicks and then also try and make your password attacks using your rules and your hybrid attacks and and that what we'll touch on just now
get them to try and follow these types of patterns that the users are using right so for example in this example June at 2018 July 2018 and JUnit 2019 but the user may have tried to set those as a password in the site setting up it's in a leak you can't use it now it's being leaked you can't use it all right so what are you gonna do is gonna try JUnit 2019 2019 and maybe that one is not in the list I'm not saying this is not it's an example but if it's not in the list now the site will accept it but is that any more secure than the other two right there's very simple rules in
both John and hash cat when cracking that would give you the output of June at 2019 2019 having just the one password candidate of June at 2019 there so think about how users are gonna think and how they're going to work around this because ultimately that's what users are pretty good at the ones who stick around long enough I remember us are saying oh you're some are just going to be frustrated and go somewhere else but those who stick it out will find a way to find a word that a password that isn't in that legal and then they will continue it it's not necessarily meaning it's going to be a secure password it just means it may not
be in a word list that is floating around on the internet some way or that has been leaked okay common password attacks so we're not going to go into detail on the very common common stuff so I assume most of you know that you're using the word list very easy you run your particular tool of choice and you give it a big dictionary list the brute force well that's not a dictionary but trying different characters different sets of characters built-in attack tops like the hybrid attacks the combination attacks okay these are basically using word lists and rules or word lists and brute force or combining word lists together these are been around for very long they
still work very well we're not going to go into detail on them and in rules and rules files so these things are still out there they're still being used very much but it's a look at some of the other ones that aren't as as simple as as these ones and some of them being around as I said for for a while some of them are quite good we're gonna do going to look at mark of team ASIS and prints so the layout I'm going to use the blue box tells you what it does the green box tells you what an example of what the output would be and then the yellow box is basically just the the commands that
you can be using now the mark of attack a few years ago you used to need quite a bit quite a few tools to get to work or certain tools to plug into your output to your hash cracking for it to work these days it's built into maths of the hash cracker so for example hash ket automatically does a mark off when you're trying to brute force so what is mom what is mark over it's a statistical prediction or selection of the next character based on the previous character and or including the position of that character okay so for those of you who haven't heard of mark of before it's about he's he's a mathematician
came up with these very interesting algorithms and and Markov chains are basically tables that try to predict some kind of certainty sometimes very good certainty what is going to be next in the chain okay so I'll give you an example if I if I use the sentence Humpty Dumpty sat on a light okay your brain knows because it seen it before they're statistically the next word is wool right you're not gonna suddenly your brains not gonna just pull out car or bus or something okay because it's been trained you've seen that sentence many times in your life and you know what comes after it so Markov works in a similar way we can take certain words
sentences phrases from books from publications from anything really and we can work out that if I have one or two words what comes next statistically right if I have one word what's after it if I have two words what's after that and you can group them it can become quite complex as it goes on but the fact is that it gives you a pretty strong prediction that you can use when cracking partial words so that you're not trying things that would have a low chance of working so if you look at the green box there if you had the characters hgl in the english dictionary that's a 90% chance that there's an ell 80% chance of an oh I left out the P but
that would have been in there as well there's only a 5% chance that the next character would have been a being a W so if you were trying to crack a password and using these as candidates to see if it matches the hash that you're trying to to crack W would be the very last thing you would be trying h GL W does that saying you won't try it but statistically you want that to be at the bottom to increase your chances of cracking a password closer to the top t missus searching mixes takes a word list and provides insertion rules to insert the word into appreciate positions of each word right so team aces what it
basically does is it will take a it'll take a word list it'll take create rules to insert if you look on the right day and output box right I've given it the word hello now what team aces outputs is that it's it's outputting if you don't know what that is you're looking at it some it's the rules for hash cat right so when house cat sees this it knows to apply certain rules so here it's telling it that in position zero of whatever input word I'm getting put an H in position one put an e in position L and so on and so forth when you when it's done that it moves on the next one so
now in position one put the H in position to put the e in position three put the L and so on and so forth so it'll carry on doing that all the way down inserting this particular word into every character that you can find in the target word all right and then you will be left with a bunch of rules that you can use it as output and you can feed it to hash cat as a rule fell on a dictionary it can work very well it can insert things that you may not have thought about obviously you can also get pretty big depending what you're feeding it and have them how big the rules are
that come out it's up to you to see what your appetite is if you've got quite a few GPUs and you want to keep them quite busy well give it a good word list and give it quality rules it'll be happy to go on with that okay then the prints attack the prints attack is stands for probability infinite chained elements so what does what does is it takes one word list and it creates and chains and returns words right that can fit into certain positions there so for example we input a word list and we're outputting assuming a length of six right so if we are putting assuming a length of six what the princess attack
will do is it'll output three plus three character words to give us a length of six okay so it builds a table of of all the words indexes them knows what the lengths are and the unit starts outputting based on their table so to give us a six links word it'll also output a four plus two character would it'll output a five plus one character word and so on and so forth it'll keep doing this so that gives you a good way to generate quite a nice word list that you can use for that so the command line they're also pretty simple once you've compiled the prints binary it's pp 64 you give it a word list or you can give it
constraints about where it should start and stop generating these passwords for you so if we go to the next slide looking at prints so there's an example right I've got a word stuff takes file and I'll just put three words in there hello Bob and aeroplane now I'm gonna ask Prince to generate words on this now I'm not gonna give it constraints I'm gonna let it start from the minimum which is three characters and work its way up and if you look at the output you can see what it's doing here so for three characters that output it Bob because Bob is a three character word then it went to four well hello if it's
that then it put airplane then it started adding now if you notice as it goes on I'm not sure you can see it in this in this example but one thing you need to keep in mind that you may land up with some dupe duplicates here that you'll need to filter out before you go on because it's going to keep on adding and it may switch them around and then you're going to have these duplicate words coming in here too so it's outputting a whole lot of possible words that you can use for that as well just some other tools to mention there's the Combinator attack this is done by most tools by default but if you
want to create combined word lists for yourself there's a Combinator binary it's it's also part of the hash CAD tools and it's very simple you give it two files it joins them you give it three files it joins all the words in those files and gives you output it's a very nice way to do that so you know for example if you've got a if you've got a word list with a bunch of nouns in it and a word list with a bunch of verbs you want to join them all together you can use Combinator to do that and then who resort is a tool I wrote I think in 2015 or so basically just to help manage
the word list that you have to make them more efficient to make them easier for you to work with sometimes we have we tend to add to our word list to such a degree without cleaning them that we're sitting with quite big word lists that are actually ineffective and one very sure where the world is becoming an effective is if it's got entries that it should be doing with rules instead of just the base word itself right so for example if your wordless contains at hello okay you don't need to have the at in your wordless because there are rules and rules files that then are going to tell the cracking software to and added
before every word and so on and so forth so you want to get those out to keep the word list nice and and and small and as lean as possible these various options I've just shown two there one of them is to take away the the sentences say if you've got a word list with a bunch of sentences and you don't want them indeed you can say no sentence which basically compact everything into one line without one string without any spaces the word defy option will do the opposite it'll basically break each word up each word in the sentence up into a new word on a new line they send various other options you can look at using there as well it
is a Python script so feel free to change it or do whatever you want to it to make it work for what you need it's not the only tool that can do that out there so if you if you want to look on Google as well something else that fits your needs then you should do that the key here is to make sure that your word lists are very well maintained and very efficient when you're cracking passwords otherwise you're wasting resources with things things that it doesn't need to be doing okay so having a look at the next example is attacking phrases and other languages so looking at phrases is various ways that we can create phrases
there's some simple ways for example just taking books taking information from sites grabbing the ticks from them and basically cutting out sentences from there that's one way you can do it as well some other ways or using the Combinator tool so basically combining certain elements right so for example what you can do is have a a pronoun word list and then have a noun word list right and then you combine the two with Combinator so that you start making some kind of sentence or have a sorcerers like I like I hate I do I won't etc combine those with a whole bunch of other standard words like I won't stand I won't sit I don't like this etc etc to
get those those phrases out to you missus the tool we discussed also very good for creating various kinds of phrases as well remember what you can do in your word list too when you're combining them or using any of the tools is at a space either on the left or the right side of what you're combining if you want a sentence with a space in it instead of just everything on one line generally users will either just enter one phrase in one go some of the mains or a space but certain sites wouldn't want allow that in which case we don't need to worry about doing that but then you can also use the Combinator attack
with the space as well to create sentences there and then the mark of attack is also very handy for doing that as well how to use the mark of attack for creating sentences I'll leave it up to you to look at what tools you want to use or if you want to develop your your own what we have here are the engrams for the from the corpus of contemporary American English okay so top noun + noun Markov chains so basically what this tells us is that if we look at the word health right that's a very high frequency that the next word is going to be care after the word health right looking at low very high frequency that
the next world will be enforcement now if you go to the website and you scroll down you will find the word law quite a few times right but what's going to change is the frequency or in the chain what statistically would be the next word after the word law so you can then use this as you want customize your own tools to basically output sentences from these Markov chains then attacking other languages so often you may find yourself faced with certain hashes that need to be cracked that aren't in the English language now if it's the English character set or the English alphabet that's not too difficult but you might find that you're getting ones that are in in Arabic for
example maybe in emoji maybe in Chinese etc and so on so you want to be able to try and attack these as well now obviously first prize is to look forward lists that you can use along with the rules but you can do it you can also get hash get to brute force certain of these characters for you if you want to as well and to do that we use an option in hash cat that is called - - hex - Cara set so that's basically telling hash code that instead of giving it just characters I'm giving them in hex and the reason we do that is because because in utf-8 certain characters are the
non-standard characters these are represented in in hexadecimal values as the Unicode so if you click on that link there at that at the table it's a very nice website that that that person has set up there you can basically look up all the characters that that you want to tells you what the the values are for for those so the example if we look at generating or brute-forcing Arabic output we can say okay the obscure an example of hash Kadesh m0 which is to attack md5 my hashes and then what we're doing is remember we need the two characters for the hex so we're going to say their character 1 or - 1 is either
d8 d9 da or DB now remember we've told hash cat that it's its hexadecimal so it's looking at that in pairs it's not looking at it in characters remember to always add that switch because if you don't hatch that's going to assume that you mean a D or an 8 or a D or a 9 what you don't want it to do in this case so that's the base theme - - is telling us to add the next or the following hexadecimal characters and these are the ones that will basically change or that it'll brute-force through to give us the various outputs and then we have the mask at the end which is combining them
one and two one-and-two one-and-two to output these the same thing with emoji with emoji just one difference is that it's actually four of these hex characters that you need to put so for example if we look at just switch out here
which side is the Sun such might be a bit small let's see alright so if we are just putting in in a script to make it easier to run so here watch what what I've done is let me first show you that file okay I'm I don't know if you can read it it's a bit small on the top there is it burner but a bit better I don't wanna go too big it's gonna start cutting it off you can ignore the parts in the beginning what's interesting now what do you want to focus on is that I've got there's four preset characters I've given to hash get if 0 9 F + 3 8 right which tell us which
are the hex for the the emoji - 4 is the one that's actually going to change now I didn't include everything in there you can get that from the website if you want to include it all and I've told it to generate a that it must view those as a hexadecimal character set and then I've told it to output there so if you look I'm going to output - emerges at a time which is basically two sets of four so if we run that we get the output that's shown there how many how many did I have to have more than four yeah sorry I had three so then you get that I put there so that's one example of what you
can do with that if you look at that at that table you can basically output all sorts of characters all sorts of of languages Greek Chinese Arabic as I mentioned you move on from there just keep in mind that this is more last resort after a word list or use it with a hybrid attack and add certain characters to word list okay because it force you'd really want to be at the very end of I ran out of all ideas and now I'm gonna try and bridge for something
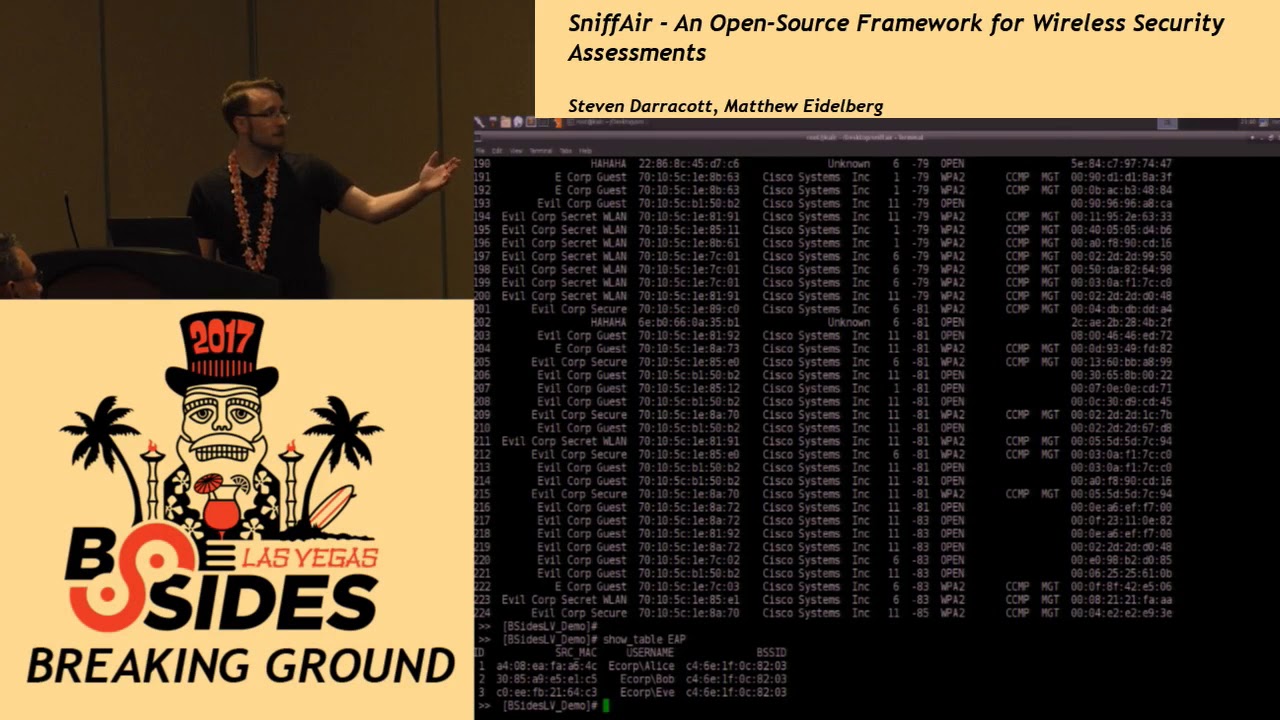
yeah so that's how we can do that and then also just keep in mind that when you're outputting this just check that your hexadecimal values are correct because you may if you make a mistake you you're not gonna pick it up and they said you won't be seeing what's coming out and what is not cracking so my recommendation would be try and put into a file scripted do something like that with it so that you've always got the same amount of data there okay the next one is the new wpa2 attack that you may have heard about and it's very interesting it's very helpful it's very nice courtesy of Adam at hash code and also
zero B for that so what we have here is an it is a new way to attack wpa2 which is doesn't require us to have visibility of the clients handshake to the access point so I'm sure many of you who've tried it it's always a frustrating thing because you need to be in a range of both if you're not you'll end up having to walk around and these antennas facing all sorts of places and you know in the end you start looking quite conspicuous about what you're doing with this new attack you only need to have visibility of the of the access point and how it works is that it looks at certain packet in the a in the a pool frame called RNs
ie or robust security network information element its users looks at the pairwise master key right and in there what was found was that it's a it's an H max sha-1 hash using the the pairwise master key as the key and in the following data that it it does the rendered hash on which is the pmk name the AP's MAC address and the station's Mac MAC address with all of that it then creates these I'm just go back sorry and then creates these frames now from these frames we can get everything we need to be able to attack the network without having to actually go and get any clients or get any handshakes from that so Adam very kindly put a new attack
and zerah be very kindly created or updated his tool hcx dump tool and it works very well I'll try and run it but I was trying to do it just now but with all the Karma devices running around the attacks are not looking very good because it is messing up everything so this is the screenshots are sufficient so what's happening here is you basically run it we give it the output of a pcap file you give it an adapter okay and then you give it a enable status one is basically just to show us when it has found a PM krd that controls what kind of output comes out of there so when I ran this it it found certain
handshakes and in some of them you'll notice that it found the PM k ID and that's the key of what we're looking for in order to be able to crack that wpa2 so the next one the HC XP cap tool what that does is it reads the pcap file and it dumps these PM k ids for us in a format that hash cat can use so if you look at the bottom there three of them were found I'm just coming back to this one it may take a while also the tool does have options to filter on certain MAC addresses so you're not just targeting everything inside if you don't want to do that you can target specific
MAC addresses specific APs and specific channel numbers as well it'll then dump these PM key IDs that are written down I've used a very descriptive file name of blah and you simply then have a look inside there and what you have in bla is this hash that's comprised of certain elements you'll notice that the AP's MAC addresses in there as well as as the station and then also a hex representation of the SSID and the attack is pretty simple after that it's like you would have done with your wpa2 hashes in the past except the new mode is 16800 that you'll give hash cat you'll feed it the file that you just generated from their tool and then the
w3 is just to control the workload and in your word list or whatever attack you're going to do and what's going to happen in its it's going to output now I've got it running on these I don't think it finished yet but I'll show you what it's doing Thanks
as if you have a look at this one it's a little busy it's a little busy we were running the ones that I was trying to attack um with certain access points it may not work okay so the one that I had that I was testing with it didn't get it it managed to get the DMK IDs of other access points so you just need to give it some time play around with it until you get the output that you're looking for but in this case I've given hash cat that file and it's busy trying to crack those those passwords over they if I do a state is pronounced you'll see it changing and going on so that's mode
16800 and painfully easy to do you just need to run the tool have a Wi-Fi adapter of course that that's in monitor mode get the pmk ids when they're dumped convert them into a format hash cat can use run hash code with a particular word list or whatever your attack is going to be and then it will give you the passwords once they are there they're cracked so it doesn't just keep in mind that if you I mean if you're new to wpa2 you cracking it doesn't it's not magically going to just spit out passwords you still need to have wordless that that are good you still need to have a text that are good at
cracking these hashes what it does it's very good now is that you don't need to be inside of the client capturing that handshake you don't need to do is and try and get those handshakes to come in you just need to have your machine with your Wi-Fi adapter and visibility of the access points that you want to it to attack tracking the heavy duty al algorithms so just a brief discussion on how we can approach these algorithms that are very strong that are very slow especially salted ones especially ones that are you're just finding that you're you're that you're not getting anywhere with him okay optimize word lists or or must I think anybody speak to who cracks
passwords will tell you that if your word lists are not good you're gonna go running circles for a very long time so you need to have word lists which are very precise very scaled-down right remember to take away special characters because your rules are gonna do that for you you don't need them in there you're just gonna keep GPUs idling if you don't any work to do what you want to do with with the rules keep brute-forcing for the end especially with slow algorithms okay it was some of them you're just wasting your time even trying to do a brute-force because it's actually not gonna kind of gonna go anywhere profile the target as well so you know if you're
assuming that you're doing this as as in order to you know think about what the person is doing are they filtering out leaked passwords like we discussed earlier are they what's happens with what the users use is there a company name that I can I can use in a pattern or that I can feed it into Team aces to start adding into my dictionary for example why would they pick certain past passwords and what enforcement does the company have on character size or the website have on character size the the password length how short can it be how long can it be and so forth shaky the GPU or CPU is being optimized right so if you notice
that John or hash card is showing you that not much is happening okay you've got six GPUs and ones doing the work that isn't optimized so you're doing something wrong you need to change that especially on the slow algorithms because you want to give as much power you want to have everything working as hard as it can so that you you get good use out of it and then you use rules as well to create a workload right so that brings me to the end of my part for today I hope it answers some questions I do some interesting new attacks for the WPA that you can try I just want to quickly show you where you can get those
tools from assume in the Internet's working it looks like all the Karma devices have been turned off for a few seconds okay so here's Derby's website which with hcx dump tool so you'll need this one to do the WPA attack you're going to also need to get hcx tools which is right next to it okay and compile these of course as well then you will need hash get the latest version of hash get top it correctly okay it's a very simple just go to the site there and I'll recommend perhaps fetching it from from github and compiling it and then lastly if you need the steps to be read or reiterated and quite a good
explanation of it as well as when I bring that up for you
okay so there's um atoms it's an article he's got links to the tools as well that you'll need to do that you can use that as well and he also gives a very good description of how of what it's doing along with the actual packet capture and then also the steps that you need to do that so how to defend against this is as it was with WPA with the other attack acts actually as well was to have Wi-Fi passwords that are secure that along there are complex that are difficult to crack or switch to a different authentication mechanism like and manager authentication instead of appreciate key on the clients but if you can't do that you need to make sure that
it's it's quite that it's quite a secure password just also note that you need certain adapters for this to work right it's not just going to work on like a like a max Wi-Fi adapter almost Wi-Fi adapters out there so on I think on their B's website there he did show which adapters it's known to work with or if you do have one that you had been using to capture handshakes try it anyway on on that for example the tp-link I've got was not listed as being supported but it does work on there too so I'm sure he will just keep on adding these supported adapters as time goes on
okay that's the end of the show so if you have any any questions afterwards you're welcome to come up here I don't want to keep everybody from those who need to go to lunch so you welcome to come to the front and all answer any questions that you may have thank you [Applause]